Unit 3 Networks
... Networks can be classified in many ways; as a network user, you’ll want to keep in mind the idea of control and how it affects your privacy and security ...
... Networks can be classified in many ways; as a network user, you’ll want to keep in mind the idea of control and how it affects your privacy and security ...
Week 3 Topical Lecture
... Chapter 1: roadmap 1.1 What is the Internet? 1.2 Network edge 1.3 Network core 1.4 Network access and physical media 1.5 Internet structure and ISPs 1.6 Delay & loss in packet-switched networks 1.7 Protocol layers, service models 1.8 History Introduction ...
... Chapter 1: roadmap 1.1 What is the Internet? 1.2 Network edge 1.3 Network core 1.4 Network access and physical media 1.5 Internet structure and ISPs 1.6 Delay & loss in packet-switched networks 1.7 Protocol layers, service models 1.8 History Introduction ...
5.3 System-High Interconnections and Virtual Private Networks
... telecommunications services connecting the various entities. The number of techniques for providing communications between facilities has increased dramatically. While leasing telecommunications lines is still an option for those with specialized communications environments, there are many more cost ...
... telecommunications services connecting the various entities. The number of techniques for providing communications between facilities has increased dramatically. While leasing telecommunications lines is still an option for those with specialized communications environments, there are many more cost ...
ppt
... 9. Why might you use client IP affinity instead of no affinity for load balancing? What is the trade off? If you have resources which are cached at the server (e.g. an SSL session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the ...
... 9. Why might you use client IP affinity instead of no affinity for load balancing? What is the trade off? If you have resources which are cached at the server (e.g. an SSL session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the ...
IOSR Journal of Computer Engineering (IOSRJCE)
... which is majorly because of the open nature of the internet.[20] .People always want to feel secured in everything they do and voice communication is not exceptional. Security in VoIP is now a major concern with news headlines like “Venezuelan VoIP hacker imprisoned for 10 years after stealing over ...
... which is majorly because of the open nature of the internet.[20] .People always want to feel secured in everything they do and voice communication is not exceptional. Security in VoIP is now a major concern with news headlines like “Venezuelan VoIP hacker imprisoned for 10 years after stealing over ...
Cloud Traceability Working Group Face to Face Report
... logstash, kibana) stack – particular reference to UK but widely seen elsewhere too • RAL have ELK infrastructure (on back of castor work), migration to new hardware longer than planned. In place now. Next step to send logs from cloud into that. • RAL have done low level work to tune ELK to better sc ...
... logstash, kibana) stack – particular reference to UK but widely seen elsewhere too • RAL have ELK infrastructure (on back of castor work), migration to new hardware longer than planned. In place now. Next step to send logs from cloud into that. • RAL have done low level work to tune ELK to better sc ...
Appendix B - Roaming
... Perhaps it would help you to understand the difference between layer 2 and layer 3 if we have a typical real world example? Imagine an ftp server running on a PC connected by a lan cable to your office switch. The server wants to send a stream of data to a wireless client (let's say a laptop) which ...
... Perhaps it would help you to understand the difference between layer 2 and layer 3 if we have a typical real world example? Imagine an ftp server running on a PC connected by a lan cable to your office switch. The server wants to send a stream of data to a wireless client (let's say a laptop) which ...
security
... issued by a certificate authority (CA) listed in the server's list of trusted CAs. • An encrypted SSL connection requires all information sent between a client and a server to be encrypted by the sending software and decrypted by the receiving software, thus providing a high degree of confidentialit ...
... issued by a certificate authority (CA) listed in the server's list of trusted CAs. • An encrypted SSL connection requires all information sent between a client and a server to be encrypted by the sending software and decrypted by the receiving software, thus providing a high degree of confidentialit ...
Security 2 - Eastern Illinois University
... Include Heading fields that might hide false identity ...
... Include Heading fields that might hide false identity ...
O A RIGINAL RTICLES
... fast handover. Author mainly addresses on re-authentication difficulty while handover in WLAN. Authenticated server send a handover tickets to the mobile station as an evidence of authorization and it produces the equivalent tickets when connecting with a new access point. In proposed system re-auth ...
... fast handover. Author mainly addresses on re-authentication difficulty while handover in WLAN. Authenticated server send a handover tickets to the mobile station as an evidence of authorization and it produces the equivalent tickets when connecting with a new access point. In proposed system re-auth ...
4th Edition: Chapter 1 - Computer Science & Engineering
... Optical links from central office to the home Two competing optical technologies: Passive Optical network (PON) Active Optical Network (PAN) Much higher Internet rates; fiber also carries ...
... Optical links from central office to the home Two competing optical technologies: Passive Optical network (PON) Active Optical Network (PAN) Much higher Internet rates; fiber also carries ...
Basic Concepts
... Figure 1-11: Internets • Packets are carried within frames – One packet is transmitted from the source host to the destination host • Its IP destination address is that of the destination host – In each network, the packet is carried in (encapsulated in) a frame (Figure 1-12) – If there are N netwo ...
... Figure 1-11: Internets • Packets are carried within frames – One packet is transmitted from the source host to the destination host • Its IP destination address is that of the destination host – In each network, the packet is carried in (encapsulated in) a frame (Figure 1-12) – If there are N netwo ...
Economics, Policy and a little MPLS
... Mobile 3 - Resources • Some QoS approaches are based on the netwrk running largely underloaded • e.g. EF and AF may only work for IP telephony if it constitutes a small part of traffic • This is not the case on many wireless links today. • Need to look at hard QoS schemes - particularly for low lat ...
... Mobile 3 - Resources • Some QoS approaches are based on the netwrk running largely underloaded • e.g. EF and AF may only work for IP telephony if it constitutes a small part of traffic • This is not the case on many wireless links today. • Need to look at hard QoS schemes - particularly for low lat ...
Bluetooth - School of Information Technology, IIT kharagpur
... Conclusion Bluetooth technology encompasses several key points that facilitate its widespread adoption: • Its specification is publicly available and free . ...
... Conclusion Bluetooth technology encompasses several key points that facilitate its widespread adoption: • Its specification is publicly available and free . ...
9781435420168_PPT_CH01
... data traveling over a network; can be used for both legitimate network management and for stealing information from a network Social engineering: within the context of information security, the process of using social skills to convince people to reveal access credentials or other valuable informa ...
... data traveling over a network; can be used for both legitimate network management and for stealing information from a network Social engineering: within the context of information security, the process of using social skills to convince people to reveal access credentials or other valuable informa ...
Adaptive QoS Framework for Multimedia in Wireless Networks and
... for reservation [8]. The frames consists of two phases control phase which consists of mini-slots and a information phase used to transmit data. During the control phase the nodes running real-time applications reserve required number of information phase slots. Other information required for routin ...
... for reservation [8]. The frames consists of two phases control phase which consists of mini-slots and a information phase used to transmit data. During the control phase the nodes running real-time applications reserve required number of information phase slots. Other information required for routin ...
Downlaod File
... each conductor to handle a certain amount of information. Think of it like an automotive transmission. The more gears you have, the great control you have over the speed of the automobile. On the negative side, wired connections are not always realistic. Some rural areas HSBC Bank are still not wire ...
... each conductor to handle a certain amount of information. Think of it like an automotive transmission. The more gears you have, the great control you have over the speed of the automobile. On the negative side, wired connections are not always realistic. Some rural areas HSBC Bank are still not wire ...
Slides on Security
... from the outside world into a private network. • Firewalls can be implemented in a router. • A firewall can restrict certain types of traffic activity on a network based on: – Source or destination IP address – Port number – Protocol – data contents (virus scanning) ...
... from the outside world into a private network. • Firewalls can be implemented in a router. • A firewall can restrict certain types of traffic activity on a network based on: – Source or destination IP address – Port number – Protocol – data contents (virus scanning) ...
Proceedings of the 2007 IEEE Workshop on Information Assurance
... state visualization is promising. As networks become more dynamic, the need to stay on top of these changes in real time and to address immediate security needs presents a continuing challenge. We believe Panemoto addresses these concerns and will continue to do so with a flexible architecture suppo ...
... state visualization is promising. As networks become more dynamic, the need to stay on top of these changes in real time and to address immediate security needs presents a continuing challenge. We believe Panemoto addresses these concerns and will continue to do so with a flexible architecture suppo ...
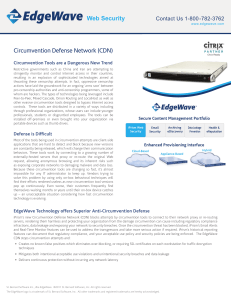
Circumvention Defense Network (CDN)
... Peer-to-Peer, Mixed Cascade, Onion Routing and LocalHost as well as other evasive circumvention tools designed to bypass Internet access controls. These tools are distributed in a variety of ways including through professional organizations, whose users can include younger professionals, students or ...
... Peer-to-Peer, Mixed Cascade, Onion Routing and LocalHost as well as other evasive circumvention tools designed to bypass Internet access controls. These tools are distributed in a variety of ways including through professional organizations, whose users can include younger professionals, students or ...
e-Security extra notes
... Virtual private networks (VPNs)—use public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
... Virtual private networks (VPNs)—use public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
PDF - International Journal of Recent Scientific Research
... Line-of-Sight (NLOS) typically up to 6 - 10 km (4 - 6 miles) for fixed customer premises equipment (CPE). It is based on IEEE 802.16 standard and also called Broadband Wireless Access [8]. ...
... Line-of-Sight (NLOS) typically up to 6 - 10 km (4 - 6 miles) for fixed customer premises equipment (CPE). It is based on IEEE 802.16 standard and also called Broadband Wireless Access [8]. ...
Working Group Outcomes
... Smartcard IC’s designers use rules & tools, and wafers are made on fabrication lines as per ITRS roadmap. Smart card IC market still < 1% of total semi market Five Laws paradigm applies now to smart cards. ...
... Smartcard IC’s designers use rules & tools, and wafers are made on fabrication lines as per ITRS roadmap. Smart card IC market still < 1% of total semi market Five Laws paradigm applies now to smart cards. ...
Windows Server 2008 - St. Mary's Ryken High School
... for Standardization (ISO) has become a key part of networking because it provides a common framework for developers and students of networking to work with and learn from • OSI model is not specific to any protocol suite and can be applied to most networking protocols • OSI model is a seven-layer or ...
... for Standardization (ISO) has become a key part of networking because it provides a common framework for developers and students of networking to work with and learn from • OSI model is not specific to any protocol suite and can be applied to most networking protocols • OSI model is a seven-layer or ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.