Manual D-Link AirPlus DI-614+
... adapter cards used on laptop and desktop systems, support the same protocols as Ethernet adapter cards. Under many circumstances, it may be desirable for mobile network devices to link to a conventional Ethernet LAN in order to use servers, printers or an Internet connection supplied through the wir ...
... adapter cards used on laptop and desktop systems, support the same protocols as Ethernet adapter cards. Under many circumstances, it may be desirable for mobile network devices to link to a conventional Ethernet LAN in order to use servers, printers or an Internet connection supplied through the wir ...
UNIX Networking
... • Server is a process that is waiting to be contacted by a client process so that server can do something for the client. – Server is started, sleeps waiting for a service request from a client – Client processes started on same system or another system within a network. – Client process sends a req ...
... • Server is a process that is waiting to be contacted by a client process so that server can do something for the client. – Server is started, sleeps waiting for a service request from a client – Client processes started on same system or another system within a network. – Client process sends a req ...
CHAPTER 1 THE INTRUSION DETECTION SYSTEM
... they allow network administrators to detect policy violations. These policy violations range from external attackers trying to gain unauthorized access to insiders abusing their access. ...
... they allow network administrators to detect policy violations. These policy violations range from external attackers trying to gain unauthorized access to insiders abusing their access. ...
Harshita Deshpande - Computer Science
... that it can run at various points in the network to exploit, for example, locality, available computation, and/or available bandwidth. The principal contribution of Active Naming is a unified framework for extensible and application-specific naming, location, and transformation of wide-area resource ...
... that it can run at various points in the network to exploit, for example, locality, available computation, and/or available bandwidth. The principal contribution of Active Naming is a unified framework for extensible and application-specific naming, location, and transformation of wide-area resource ...
Mobile IPv6 to manage Multiple Interfaces
... Users are becoming mobile World-wide availability of popular wireless communication technologies ...
... Users are becoming mobile World-wide availability of popular wireless communication technologies ...
EVVBU Marketing Strategy Development Session
... protocol • 802.1x builds on an existing protocol called Extensible Authentication Protocol (EAP [RFC 2284]) • By tying EAP into the bigger picture, so to speak. EAP conducts the authentication process. It ties Point-to-Point Protocol (PPP) to the physical layer, OSI Layer 1. • EAP over LAN (EAPOL) i ...
... protocol • 802.1x builds on an existing protocol called Extensible Authentication Protocol (EAP [RFC 2284]) • By tying EAP into the bigger picture, so to speak. EAP conducts the authentication process. It ties Point-to-Point Protocol (PPP) to the physical layer, OSI Layer 1. • EAP over LAN (EAPOL) i ...
version with answers - Computer Science at Princeton University
... (2f) Suppose two directly-connected routers A and B have a BGP session between them, running over a TCP connection with port 179 on both ends. A third party C, several hops away, could conceivably launch a denial-of-service attack on router B by sending unwanted packets to router B on port 179. To ...
... (2f) Suppose two directly-connected routers A and B have a BGP session between them, running over a TCP connection with port 179 on both ends. A third party C, several hops away, could conceivably launch a denial-of-service attack on router B by sending unwanted packets to router B on port 179. To ...
Active directory
... features are invisible to end users; therefore, migrating users to an Active Directory network will require little re-training. Active Directory offers a means of easily promoting and demoting domain controllers and member servers. Systems can be managed and secured via Group Policies. It is a flexi ...
... features are invisible to end users; therefore, migrating users to an Active Directory network will require little re-training. Active Directory offers a means of easily promoting and demoting domain controllers and member servers. Systems can be managed and secured via Group Policies. It is a flexi ...
Netronics Wireless Solution for Video Surveillance
... • Real Time - Focused alerts, maximum information for manned patrols • Mission-critical - No tolerance for system downtime or quality degradation Requires higher capacity for video streaming, and higher robustness and reliability of the wireless transport infrastructure ...
... • Real Time - Focused alerts, maximum information for manned patrols • Mission-critical - No tolerance for system downtime or quality degradation Requires higher capacity for video streaming, and higher robustness and reliability of the wireless transport infrastructure ...
BD01416451651.98
... and battery-powered devices that can be used in virtually any environment. With this data simple computations are carried out and communicate with other sensor nodes or controlling authorities in the network [21]. Wireless communication is a major source of energy consumption in WSNs. WSN have latel ...
... and battery-powered devices that can be used in virtually any environment. With this data simple computations are carried out and communicate with other sensor nodes or controlling authorities in the network [21]. Wireless communication is a major source of energy consumption in WSNs. WSN have latel ...
Oracle EBS R12 - Security
... In today’s environment, a properly secured computing infrastructure is critical. When securing the infrastructure, a balance must be struck between risk of exposure, cost of security and value of the information protected. ...
... In today’s environment, a properly secured computing infrastructure is critical. When securing the infrastructure, a balance must be struck between risk of exposure, cost of security and value of the information protected. ...
DHCP snooping
... Rogue DHCP Server Set up a rogue DHCP server serving clients with false details E.g. giving them its own IP as default router Result in all the traffic passing through the attacker’s computer ...
... Rogue DHCP Server Set up a rogue DHCP server serving clients with false details E.g. giving them its own IP as default router Result in all the traffic passing through the attacker’s computer ...
1 Chapter 7: Testbank Questions 1. A computer ______ is two or
... accomplish specific tasks and make specific requests/c. two or more computers connected together via software and hardware so they can communicate/d. unauthorized connection to a wireless network/e. a computer, peripheral, or communication device on a network ...
... accomplish specific tasks and make specific requests/c. two or more computers connected together via software and hardware so they can communicate/d. unauthorized connection to a wireless network/e. a computer, peripheral, or communication device on a network ...
Chapter 9
... – deterring measures Actions that will make criminals abandon their idea of attacking a specific system (e.g., the possibility of losing a job for insiders). – prevention measures Ways to help stop unauthorized users (also known as “intruders”) from accessing any part of the EC system. Ex: requiring ...
... – deterring measures Actions that will make criminals abandon their idea of attacking a specific system (e.g., the possibility of losing a job for insiders). – prevention measures Ways to help stop unauthorized users (also known as “intruders”) from accessing any part of the EC system. Ex: requiring ...
슬라이드 1
... supports peer-to-peer connectivity implemented quickly and easily no need for special tools or skills, no network administration in business meeting or in the setting up of temporary workgroups limited coverage area => all stations must be within the airwave distance of other stations with whic ...
... supports peer-to-peer connectivity implemented quickly and easily no need for special tools or skills, no network administration in business meeting or in the setting up of temporary workgroups limited coverage area => all stations must be within the airwave distance of other stations with whic ...
ppt
... [1] M. A. Khalighi and M. Uysal, "Survey on Free Space Optical Communication: A Communication Theory ...
... [1] M. A. Khalighi and M. Uysal, "Survey on Free Space Optical Communication: A Communication Theory ...
C08
... almost impossible to find a mobile system, DNS updates take to long time TCP connections break, security problems ...
... almost impossible to find a mobile system, DNS updates take to long time TCP connections break, security problems ...
Security policy design with IPSec
... Network security design can be compared to the design of software, and many of the principles that have been developed and used over the years can be used (Porto and De Geus 2003:1). It is unfortunate that many software products are developed using what might be termed a ‘build and fix’ model. This ...
... Network security design can be compared to the design of software, and many of the principles that have been developed and used over the years can be used (Porto and De Geus 2003:1). It is unfortunate that many software products are developed using what might be termed a ‘build and fix’ model. This ...
mpls network faq (frequently asked questions)
... The agency will control the assignment of the remaining addresses. ISP recommends that the IP addresses below 10.x.y.11 be used for network components such as hubs, switches, routers or Firewalls. The first device would be assigned 10.x.y.11 when following this recommendation. Q12. What is NAT? A. N ...
... The agency will control the assignment of the remaining addresses. ISP recommends that the IP addresses below 10.x.y.11 be used for network components such as hubs, switches, routers or Firewalls. The first device would be assigned 10.x.y.11 when following this recommendation. Q12. What is NAT? A. N ...
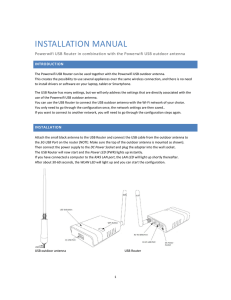
installation manual
... This creates the possibility to use several appliances over the same wireless connection, and there is no need to install drivers or software on your laptop, tablet or Smartphone. The USB Router has many settings, but we will only address the settings that are directly associated with the use of the ...
... This creates the possibility to use several appliances over the same wireless connection, and there is no need to install drivers or software on your laptop, tablet or Smartphone. The USB Router has many settings, but we will only address the settings that are directly associated with the use of the ...
Acceptable use Policy
... strictly maintaining the confidentiality of your Service login and password. In all cases, you are solely responsible for the security of any device you choose to connect to the Service, including any data stored or shared on that device. Cibola Wireless recommends against enabling file or printer s ...
... strictly maintaining the confidentiality of your Service login and password. In all cases, you are solely responsible for the security of any device you choose to connect to the Service, including any data stored or shared on that device. Cibola Wireless recommends against enabling file or printer s ...
Lecture 7
... Optical links from central office to the home Two competing optical technologies: Passive Optical network (PON) Active Optical Network (PAN) Much higher Internet rates; fiber also carries ...
... Optical links from central office to the home Two competing optical technologies: Passive Optical network (PON) Active Optical Network (PAN) Much higher Internet rates; fiber also carries ...
Does the IEEE 802.11 MAC Protocol Work Well in Multihop Wireless
... IEEE 802.11 MAC Protocol – (5) The serious problems encountered in an IEEE 802.11-based multihop ad hoc networks: The TCP Instability Problem. The Serious Unfairness Problem. ...
... IEEE 802.11 MAC Protocol – (5) The serious problems encountered in an IEEE 802.11-based multihop ad hoc networks: The TCP Instability Problem. The Serious Unfairness Problem. ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.