Lecture 18: Internet Protocol
... » destination unreachable » fragmentation required: MTU too small. » parameter problem: header invalid – for information messages: » echo request/reply » timestamp request/reply – Two programs that use the ICMP protocol: » ping and traceroute – IP invokes ICMP to report errors, ICMP encapsulates mes ...
... » destination unreachable » fragmentation required: MTU too small. » parameter problem: header invalid – for information messages: » echo request/reply » timestamp request/reply – Two programs that use the ICMP protocol: » ping and traceroute – IP invokes ICMP to report errors, ICMP encapsulates mes ...
Visualisation and Analysis of Real Time Application Behaviour in a
... • Network simulation is the most efficient means of developing and testing new protocols and network schemes • Evaluation of the behaviour of real time applications would benefit from an ability to assess the “quality of reproduction” when subjected to a particular network scheme ...
... • Network simulation is the most efficient means of developing and testing new protocols and network schemes • Evaluation of the behaviour of real time applications would benefit from an ability to assess the “quality of reproduction” when subjected to a particular network scheme ...
JOB DESCRIPTION NETWORK ADMINISTRATOR
... • Completion of a four year degree in Computer Science, or a related field with coursework in networking and two years of network experience including wide area networks, and supervisory training or experience; or an associate’s degree in Computer Science or related field, two years’ experience in a ...
... • Completion of a four year degree in Computer Science, or a related field with coursework in networking and two years of network experience including wide area networks, and supervisory training or experience; or an associate’s degree in Computer Science or related field, two years’ experience in a ...
nexosTroubleshooting..
... routers, and possible troubleshooting steps for problems that might occur in the process. Explain the extended setup: The laboratory for NEXOS will be realized using the Embedded XINU model developed by PI Brylow [5, 6]. Brylow has produced the first translation of the XINU operating system to a mod ...
... routers, and possible troubleshooting steps for problems that might occur in the process. Explain the extended setup: The laboratory for NEXOS will be realized using the Embedded XINU model developed by PI Brylow [5, 6]. Brylow has produced the first translation of the XINU operating system to a mod ...
ppt
... - Incorrectly setup Access Points - Encryption - Access control - Wi-Fi not included in security policies in many institutions - Weak encryption standards used - Rogue Access Points - War-driving ...
... - Incorrectly setup Access Points - Encryption - Access control - Wi-Fi not included in security policies in many institutions - Weak encryption standards used - Rogue Access Points - War-driving ...
Helicomm Hypercompetes in M2M
... globally for human use. In that same year, over 8 billion embedded microcontrollers shipped for machine use. Machine-to-machine communication relies upon collecting and communicating data with embedded systems, (embedded systems are computer chips within machine devices.) In many remote monitoring a ...
... globally for human use. In that same year, over 8 billion embedded microcontrollers shipped for machine use. Machine-to-machine communication relies upon collecting and communicating data with embedded systems, (embedded systems are computer chips within machine devices.) In many remote monitoring a ...
Known issue when using Novatel Wireless V620, V640 USB720
... (Network Driver Interface Specification) mode with the Microsoft Windows VistaTM operating system On the new Windows VistaTM OS, there is an issue with the connection stability when using the NDIS mode on the Novatel Wireless V620, V640 and the USB720. In order to maintain the 3G connection, the Net ...
... (Network Driver Interface Specification) mode with the Microsoft Windows VistaTM operating system On the new Windows VistaTM OS, there is an issue with the connection stability when using the NDIS mode on the Novatel Wireless V620, V640 and the USB720. In order to maintain the 3G connection, the Net ...
3 - Computer Network - Basic Concepts
... The Internet consists of a worldwide interconnection of governmental, academic, public, and private networks based upon the networking technologies of the Internet Protocol Suite. It is the successor of the Advanced Research Projects Agency Network (ARPANET) developed by DARPA of the U.S. Department ...
... The Internet consists of a worldwide interconnection of governmental, academic, public, and private networks based upon the networking technologies of the Internet Protocol Suite. It is the successor of the Advanced Research Projects Agency Network (ARPANET) developed by DARPA of the U.S. Department ...
Chapter 2 Networking Overview
... applications at the socket layer. Allows an application to have authenticated, encrypted communications across a network Uses digital certificates to authenticate systems and distribute encryption keys Supports one-way authentication of server to client and two-way authentication Used by web ...
... applications at the socket layer. Allows an application to have authenticated, encrypted communications across a network Uses digital certificates to authenticate systems and distribute encryption keys Supports one-way authentication of server to client and two-way authentication Used by web ...
Business to Business Wireless E
... automatically updates databases back in a data center whenever a package is delivered and signed for. Another market sector that is starting to implement B2B M-Commerce is the home utility sector (electricity, water, phone, etc.). Such that, every house that is connected to a public water supply or ...
... automatically updates databases back in a data center whenever a package is delivered and signed for. Another market sector that is starting to implement B2B M-Commerce is the home utility sector (electricity, water, phone, etc.). Such that, every house that is connected to a public water supply or ...
Active Networks
... possibly a security database and an enforcement engine. The programming model that an EE supports must also be restricted to ensure network security. No broad consensus on the division of responsibility for policy enforcement between the NodeOS and the EE. ...
... possibly a security database and an enforcement engine. The programming model that an EE supports must also be restricted to ensure network security. No broad consensus on the division of responsibility for policy enforcement between the NodeOS and the EE. ...
CIT 016 Review for Final
... secure network perimeter Outside users can access the DMZ, but cannot enter the secure network For extra security, some networks use a DMZ with two firewalls The types of servers that should be located in the DMZ include: ...
... secure network perimeter Outside users can access the DMZ, but cannot enter the secure network For extra security, some networks use a DMZ with two firewalls The types of servers that should be located in the DMZ include: ...
A Big Test Result - Knowledge Systems Institute
... This lesson we examine the role of network interface cards (NICs) and how they are installed. ...
... This lesson we examine the role of network interface cards (NICs) and how they are installed. ...
Networking Basics - Henry County Schools
... the next and if a computer does not have information to transmit, it simply passes the token on to the next workstation › If a computer wishes to transmit and receives an empty token, it attaches data to the token and the token then proceeds around the ring until it comes to the computer for which t ...
... the next and if a computer does not have information to transmit, it simply passes the token on to the next workstation › If a computer wishes to transmit and receives an empty token, it attaches data to the token and the token then proceeds around the ring until it comes to the computer for which t ...
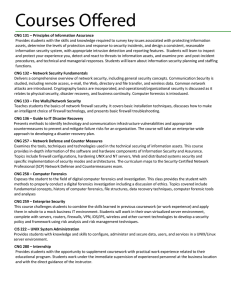
CNG 131 – Principles of Information Assurance Provides students
... Teaches students the basics of network firewall security. It covers basic installation techniques, discusses how to make an intelligent choice of firewall technology, and presents basic firewall troubleshooting. CNG 136 – Guide to IT Disaster Recovery Presents methods to identify technology and comm ...
... Teaches students the basics of network firewall security. It covers basic installation techniques, discusses how to make an intelligent choice of firewall technology, and presents basic firewall troubleshooting. CNG 136 – Guide to IT Disaster Recovery Presents methods to identify technology and comm ...
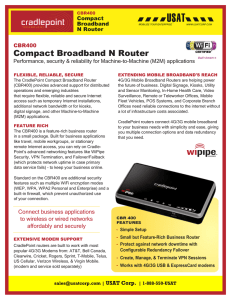
CBR400 Compact Broadband N Router
... - Enables wireless Internet access through 4G/3G mobile broadband networks, existing WiFi, or Ethernet-based data services ( Cable / DSL / Satellite ) - Supports most wireless data modems (sold separately) Range / Connection - Wireless “N” WiFi (802.11n + legacy 802.11b/g, 2x2 MIMO, 300 Mbps) - Up t ...
... - Enables wireless Internet access through 4G/3G mobile broadband networks, existing WiFi, or Ethernet-based data services ( Cable / DSL / Satellite ) - Supports most wireless data modems (sold separately) Range / Connection - Wireless “N” WiFi (802.11n + legacy 802.11b/g, 2x2 MIMO, 300 Mbps) - Up t ...
Gr11IT2013-2_1-Networks
... can operate at speeds of up to 100 Mbps? 18. 4G (also known as LTE). 19. Arrange the following types of network in ascending order with regard to their size: LAN, PAN, WAN and HAN 19. PAN, HAN, LAN and WAN 20. What type of network does one typically set up and use to exchange files wirelessly betwee ...
... can operate at speeds of up to 100 Mbps? 18. 4G (also known as LTE). 19. Arrange the following types of network in ascending order with regard to their size: LAN, PAN, WAN and HAN 19. PAN, HAN, LAN and WAN 20. What type of network does one typically set up and use to exchange files wirelessly betwee ...
Tuesday, February 7, 2007 (Intro to the Network
... At the spec’d 10Mbps, this makes for a 500 bit minimum frame size. Add a bit of padding for safety and round up to a power-oftwo and get a minimum frame size of 512 bits. So the minimum frame time is 51.2 microseconds. This is a slot time. Obviously, this increases as the speed of the underlying net ...
... At the spec’d 10Mbps, this makes for a 500 bit minimum frame size. Add a bit of padding for safety and round up to a power-oftwo and get a minimum frame size of 512 bits. So the minimum frame time is 51.2 microseconds. This is a slot time. Obviously, this increases as the speed of the underlying net ...
Wireless LAN Security
... Using MAC filters is considered to be very weak security because with many Wi-Fi client implementations it is possible to change the MAC address by reconfiguring the card. An attacker could sniff a valid MAC address from the wireless network traffic . ...
... Using MAC filters is considered to be very weak security because with many Wi-Fi client implementations it is possible to change the MAC address by reconfiguring the card. An attacker could sniff a valid MAC address from the wireless network traffic . ...
Wells Public Library`s
... A. You should be able to connect anywhere in the building, and also directly outside the building. Usually, within a minute of turning on your computer, the wireless card senses a signal and your computer will connect to our wireless network. If it does not automatically connect, you may have to hel ...
... A. You should be able to connect anywhere in the building, and also directly outside the building. Usually, within a minute of turning on your computer, the wireless card senses a signal and your computer will connect to our wireless network. If it does not automatically connect, you may have to hel ...
Router/Switch Security
... Community strings are passwords that are applied to an IOS device to restrict access. • Default community string for read−only “public” • Default community string for read-write “private” ...
... Community strings are passwords that are applied to an IOS device to restrict access. • Default community string for read−only “public” • Default community string for read-write “private” ...
The Basics of HOME NETWORKS
... Wired Equivalent Privacy (WEP) is a protocol used for encrypting packets on a wireless network. It uses a 64-bit (or 256bit, depending on the vendor) shared key algorithm. Using WEP will increase the protection on your data, but doing so will reduce the effective data rates. Truly secure? Nope! www. ...
... Wired Equivalent Privacy (WEP) is a protocol used for encrypting packets on a wireless network. It uses a 64-bit (or 256bit, depending on the vendor) shared key algorithm. Using WEP will increase the protection on your data, but doing so will reduce the effective data rates. Truly secure? Nope! www. ...
MAN Metropolitan Area Network = A metropolitan
... which all of the various devices in the network are connected to a single cable or line. RING TOPOLOGY A ring network is a network topology in which each node connects to exactly two other nodes, forming a single continuous pathway for signals through each node - a ring MESH TOPOLOGY A wireless mesh ...
... which all of the various devices in the network are connected to a single cable or line. RING TOPOLOGY A ring network is a network topology in which each node connects to exactly two other nodes, forming a single continuous pathway for signals through each node - a ring MESH TOPOLOGY A wireless mesh ...