Joshua White - Everis Inc.
... Joshua White Director of CyOON Research and Development “Cyber Operations for Optical Networks” [email protected] Everis Inc http://www.EverisInc.com ...
... Joshua White Director of CyOON Research and Development “Cyber Operations for Optical Networks” [email protected] Everis Inc http://www.EverisInc.com ...
Web Service 101
... • Build – wrap existing artifacts as SOAP and HTTP service and describe them in WSDL. ...
... • Build – wrap existing artifacts as SOAP and HTTP service and describe them in WSDL. ...
SOAP
... PortType - Defines the abstract interface to the Service. Associated with one or more operations. Message - Defines the information exchanged at the time an operation is executed (input and output). Made of one or more parts. Part – Elemental piece of information in a message (an individual paramete ...
... PortType - Defines the abstract interface to the Service. Associated with one or more operations. Message - Defines the information exchanged at the time an operation is executed (input and output). Made of one or more parts. Part – Elemental piece of information in a message (an individual paramete ...
Estimating Impact and Frequency of Risks to
... Figure 2 shows the risk level estimation model BBN. The frequency part is on the left side of the figure. The frequency estimate is derived by inserting the values for the base metrics sub variables first and from those derive the initial frequency. As can be seen in Figure 2, there is a dependency ...
... Figure 2 shows the risk level estimation model BBN. The frequency part is on the left side of the figure. The frequency estimate is derived by inserting the values for the base metrics sub variables first and from those derive the initial frequency. As can be seen in Figure 2, there is a dependency ...
Internet Security
... encrypted traffic between firewall and external host host authenticates and then is "inside" the firewall ...
... encrypted traffic between firewall and external host host authenticates and then is "inside" the firewall ...
Internet Vulnerabilities & Criminal Activity
... Two different malwares using the same C&C site may belong to the same attacker Why not go after the author? Prosecution requires: Knowledge Intent Damages & monetary loss ...
... Two different malwares using the same C&C site may belong to the same attacker Why not go after the author? Prosecution requires: Knowledge Intent Damages & monetary loss ...
Teaching Computer Security using Minix
... The base system is always functioning Each project adds a new functionality to the base system or replaces a functionality It is NOT a toy system, and it is NOT so complicated (some of the instructional OS has been used in some embedded systems) ...
... The base system is always functioning Each project adds a new functionality to the base system or replaces a functionality It is NOT a toy system, and it is NOT so complicated (some of the instructional OS has been used in some embedded systems) ...
Permissions
... • Users do not have to remember multiple user names and passwords • Logins are controlled by Windows password policies • Logins can be mapped to a single user, or Windows group account • Non-Windows users (i.e. MAC) cannot log in to SQL Server © Wiley Inc. 2006. All Rights Reserved. ...
... • Users do not have to remember multiple user names and passwords • Logins are controlled by Windows password policies • Logins can be mapped to a single user, or Windows group account • Non-Windows users (i.e. MAC) cannot log in to SQL Server © Wiley Inc. 2006. All Rights Reserved. ...
DNS - FSU Computer Science Department
... learn a lot about you • you may supply name and e-mail to sites • search engines use redirection & cookies to learn yet more • advertising companies obtain info across sites ...
... learn a lot about you • you may supply name and e-mail to sites • search engines use redirection & cookies to learn yet more • advertising companies obtain info across sites ...
Chapter 1
... Transmission Control Protocol/ Internet Protocol (TCP/IP) • Allows different types of computers to communicate at a low level ;it is up to applications, however to determine how client/server talk • Uses IP Addresses to communicate between computers • The destination computer may have many different ...
... Transmission Control Protocol/ Internet Protocol (TCP/IP) • Allows different types of computers to communicate at a low level ;it is up to applications, however to determine how client/server talk • Uses IP Addresses to communicate between computers • The destination computer may have many different ...
Network Hacking: Exploits, Intrusions and Defenses
... A secure / trusted machine Placed on the communication path from a protected network to the Internet Controls, inspects and filters the communication Attempts to prevent attacks from outside Read RFC 2979, Behavior of and Requirements for Internet Firewalls ...
... A secure / trusted machine Placed on the communication path from a protected network to the Internet Controls, inspects and filters the communication Attempts to prevent attacks from outside Read RFC 2979, Behavior of and Requirements for Internet Firewalls ...
darkhadoop - TutorialsPoint
... Say a malicious hacker has a target of 192.168.2.113, as shown in the figure above. The target is part of a network block 192.168.2.0/254. When the hacker unleashes his DDOS attack, he is not only disrupting the business operations of the target organization, but also crippling the network besides i ...
... Say a malicious hacker has a target of 192.168.2.113, as shown in the figure above. The target is part of a network block 192.168.2.0/254. When the hacker unleashes his DDOS attack, he is not only disrupting the business operations of the target organization, but also crippling the network besides i ...
Online Booking System-Client Server Technology
... In this module a sales agent searches for a movie .and book a ticket for a movie in a particular theatre using the user interfaces that are developed. Not only booking tickets but also cancellation of tickets can also be done using this system. The system can only gives access to the authorised user ...
... In this module a sales agent searches for a movie .and book a ticket for a movie in a particular theatre using the user interfaces that are developed. Not only booking tickets but also cancellation of tickets can also be done using this system. The system can only gives access to the authorised user ...
the transitivity of trust problem in the interaction of android
... End users are used to accepting permission requests with every installation of applications, thus tempted tojust acknowledge the shown list; Many applications require rather broad permissions, for example, Internet access for update checks; The dangerous permissions may be “hidden” between less crit ...
... End users are used to accepting permission requests with every installation of applications, thus tempted tojust acknowledge the shown list; Many applications require rather broad permissions, for example, Internet access for update checks; The dangerous permissions may be “hidden” between less crit ...
Java – Secure Application Manager How-to
... When the IVE installs J-SAM on a user’s machine, J-SAM listens on the loopback addresses (on the corresponding client port specified for the application server) for clientrequests to network application servers. J-SAM encapsulates the requested data and forwards the encrypted data to the IVE as SSL ...
... When the IVE installs J-SAM on a user’s machine, J-SAM listens on the loopback addresses (on the corresponding client port specified for the application server) for clientrequests to network application servers. J-SAM encapsulates the requested data and forwards the encrypted data to the IVE as SSL ...
Effective Database Security Database Top 10 Threats
... #6 - Weak Audit • Definition: Audit policies that rely on built-in database mechanisms suffer a number of weaknesses – Usually due to: ...
... #6 - Weak Audit • Definition: Audit policies that rely on built-in database mechanisms suffer a number of weaknesses – Usually due to: ...
TroyTech INet+ Certi..
... administration of IP addresses by dynamically issuing them to clients, and not requiring them to be hardcoded by an administrator. DHCP is built on BOOTP (Boot Protocol) and leases addresses from a scope. When the leases expire, the IP addresses are placed back in the scope for use by another client ...
... administration of IP addresses by dynamically issuing them to clients, and not requiring them to be hardcoded by an administrator. DHCP is built on BOOTP (Boot Protocol) and leases addresses from a scope. When the leases expire, the IP addresses are placed back in the scope for use by another client ...
Presentation
... Universal remote control with 802.11 wireless Other compromised robots with IR transmitters ...
... Universal remote control with 802.11 wireless Other compromised robots with IR transmitters ...
security
... • The encrypted information exchanged at the beginning of the SSL handshake is actually encrypted with the malicious program's public key or private key, rather than the client's or server's real keys. • The malicious program ends up establishing one set of session keys for use with the real server, ...
... • The encrypted information exchanged at the beginning of the SSL handshake is actually encrypted with the malicious program's public key or private key, rather than the client's or server's real keys. • The malicious program ends up establishing one set of session keys for use with the real server, ...
Secure Solutions for Wireless, VPN and Perimeter
... Application-layer firewalls are required to stop these attacks Enable deep content inspection Requirement for network security today to internal ...
... Application-layer firewalls are required to stop these attacks Enable deep content inspection Requirement for network security today to internal ...
Networked Applications (sockets)
... – E.g., Web browser on your laptop or cell phone – Doesn’t communicate directly with other clients – Needs to know the server’s address ...
... – E.g., Web browser on your laptop or cell phone – Doesn’t communicate directly with other clients – Needs to know the server’s address ...
FAKEM RAT: Malware Disguised as Windows Messenger and
... The perpetrators of targeted attacks aim to maintain persistent presence in a target network in order to extract sensitive data when needed. To maintain persistent presence, attackers seek to blend in with normal network traffic and use ports that are typically allowed by firewalls. As a result, man ...
... The perpetrators of targeted attacks aim to maintain persistent presence in a target network in order to extract sensitive data when needed. To maintain persistent presence, attackers seek to blend in with normal network traffic and use ports that are typically allowed by firewalls. As a result, man ...
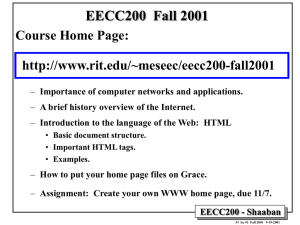
CECS470 - Rochester Institute of Technology
... server and a crude text-based browser (Web client) were developed. • Marc Andreeseen, who helped to develop the popular GUI browser Mosaic for X at The National Center for Supercomputing Applications (NCSA), released an alpha version of his browser in 1993, and in 1994 ...
... server and a crude text-based browser (Web client) were developed. • Marc Andreeseen, who helped to develop the popular GUI browser Mosaic for X at The National Center for Supercomputing Applications (NCSA), released an alpha version of his browser in 1993, and in 1994 ...
Citrix Application Firewall
... Web sites from unauthorized access and misuse by hackers and malicious programs, such as viruses and trojans (or malware). It provides protection against security vulnerabilities in legacy CGI code or scripts, Web server software, and the underlying operating system. ...
... Web sites from unauthorized access and misuse by hackers and malicious programs, such as viruses and trojans (or malware). It provides protection against security vulnerabilities in legacy CGI code or scripts, Web server software, and the underlying operating system. ...