Chapter 2
... Purpose is to prevent receiver from being overwhelmed with segments, preventing effective processing of each received segment Some error correction techniques have built-in flow control Dominant technique is sliding window protocol, which provides mechanism by which receiver can specify number ...
... Purpose is to prevent receiver from being overwhelmed with segments, preventing effective processing of each received segment Some error correction techniques have built-in flow control Dominant technique is sliding window protocol, which provides mechanism by which receiver can specify number ...
When Failure is NOT an Option
... Today, serial devices still play a major role in many applications worldwide to collect or report process data. No matter the industry, from Power/Utility, Water Wastewater or Treatment, Oil/Gas or Mining, Transportation, Factory or Process Control Automation, Medical, to Security, many applications ...
... Today, serial devices still play a major role in many applications worldwide to collect or report process data. No matter the industry, from Power/Utility, Water Wastewater or Treatment, Oil/Gas or Mining, Transportation, Factory or Process Control Automation, Medical, to Security, many applications ...
Hands-on Networking Fundamentals
... Privacy (WEP) • Employs Wired Equivalent Privacy (WEP) • WEP encryption key – Consists of key, checksum, initialization information – Total key length is 64- or 128-bits • 128-bit key supports superior 128-bit encryption ...
... Privacy (WEP) • Employs Wired Equivalent Privacy (WEP) • WEP encryption key – Consists of key, checksum, initialization information – Total key length is 64- or 128-bits • 128-bit key supports superior 128-bit encryption ...
Weighted fair queuing
... • Flow-based WFQ differs from priority and custom queuing in several ways. • On serial interfaces, WFQ is enabled by default, and the user must enable priority and custom queuing. • WFQ does not use queue lists to determine the preferred traffic on a serial interface. • Instead, the fair queue algor ...
... • Flow-based WFQ differs from priority and custom queuing in several ways. • On serial interfaces, WFQ is enabled by default, and the user must enable priority and custom queuing. • WFQ does not use queue lists to determine the preferred traffic on a serial interface. • Instead, the fair queue algor ...
Preparation of Papers in Two-Column Format
... a result of a new resource management policy and higher attainable throughput. However, this new technology has not been broadly studied empirically in a displayed commercial network setting to understand how network resources are being utilized across different protocol layers for real users. It is ...
... a result of a new resource management policy and higher attainable throughput. However, this new technology has not been broadly studied empirically in a displayed commercial network setting to understand how network resources are being utilized across different protocol layers for real users. It is ...
cellular - D
... Enables operators to offer high performance, massmarket mobile broadband services – high bit-rates, high system throughput (uplink and downlink), low latency. Designed to be simple to deploy and operate, through flexible technology that can be deployed in a wide variety of ...
... Enables operators to offer high performance, massmarket mobile broadband services – high bit-rates, high system throughput (uplink and downlink), low latency. Designed to be simple to deploy and operate, through flexible technology that can be deployed in a wide variety of ...
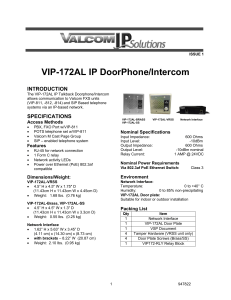
VIP-172AL IP DoorPhone/Intercom
... When requesting assistance, you should include all available information. General information and troubleshooting procedures are available on the Valcom website at www.valcom.com.Valcom equipment is not field repairable. Valcom, Inc. maintains service facilities in Roanoke, VA. Should repairs be nec ...
... When requesting assistance, you should include all available information. General information and troubleshooting procedures are available on the Valcom website at www.valcom.com.Valcom equipment is not field repairable. Valcom, Inc. maintains service facilities in Roanoke, VA. Should repairs be nec ...
Chapter 1 Communication Networks and Services
... 1960s: Dumb terminals access shared host computer z SABRE airline reservation system 1970s: Computers connect directly to each other z ARPANET packet switching network z TCP/IP internet protocols z Ethernet local area network 1980s & 1990s: New applications and Internet growth z Commercialization of ...
... 1960s: Dumb terminals access shared host computer z SABRE airline reservation system 1970s: Computers connect directly to each other z ARPANET packet switching network z TCP/IP internet protocols z Ethernet local area network 1980s & 1990s: New applications and Internet growth z Commercialization of ...
What is a communication network?
... NICs listen to medium for frames with their address Transmitting NICs listen for collisions with other stations, and abort and reschedule retransmissions Transceivers ...
... NICs listen to medium for frames with their address Transmitting NICs listen for collisions with other stations, and abort and reschedule retransmissions Transceivers ...
Chapter 1 - UniMAP Portal
... NICs listen to medium for frames with their address Transmitting NICs listen for collisions with other stations, and abort and reschedule retransmissions Transceivers ...
... NICs listen to medium for frames with their address Transmitting NICs listen for collisions with other stations, and abort and reschedule retransmissions Transceivers ...
New Methods of Telephony Service
... obviously required to propagate the actual voice or video signal to the destination. The need to service the identity or privacy of a calling or called party is still a necessity. This concept, when integrating into a server based IP network architecture, brings on a whole new meaning for identity. ...
... obviously required to propagate the actual voice or video signal to the destination. The need to service the identity or privacy of a calling or called party is still a necessity. This concept, when integrating into a server based IP network architecture, brings on a whole new meaning for identity. ...
Communication Networks
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
... Low cost, high-speed communications with low error rate possible using coaxial cable Ethernet is the standard for high-speed wired access to computer networks ...
Technical Report
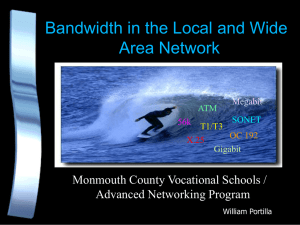
... ATM- Asynchronous Transfer Mode. A method of communications in which information is transmitted in "cells". Transmission rates from 150 megabits per second to 600 mbps. ...
... ATM- Asynchronous Transfer Mode. A method of communications in which information is transmitted in "cells". Transmission rates from 150 megabits per second to 600 mbps. ...
Week 01 Lecture
... Fig below shows the contents of payload pointer for normal operation. Assuming that the input is running slower than the frame, show the contents of the H1,H2, H3 bytes and the location of the start of payload after the transmitter performs frequency justification. N D F I D I D I D I D I D ...
... Fig below shows the contents of payload pointer for normal operation. Assuming that the input is running slower than the frame, show the contents of the H1,H2, H3 bytes and the location of the start of payload after the transmitter performs frequency justification. N D F I D I D I D I D I D ...
DwB Standard Presentation
... • The POC was designed in a collaborative way with several NSI and data archives involved. • Currently the POC does not include management tools for RDC’s staff and data-producers but it is possible to implement them (question of time). • The consortium contract for managing the network with differe ...
... • The POC was designed in a collaborative way with several NSI and data archives involved. • Currently the POC does not include management tools for RDC’s staff and data-producers but it is possible to implement them (question of time). • The consortium contract for managing the network with differe ...
PPT
... – Large body of wireless (and wired) network theory that is ad-hoc, lacks a basis in fundamentals, and lacks an objective success criteria. ...
... – Large body of wireless (and wired) network theory that is ad-hoc, lacks a basis in fundamentals, and lacks an objective success criteria. ...
View
... component that interfaces the wireless communications signals traveling through the air medium to a wired network—often referred to as a distribution system. • Base station enables users to access a wide range of network services, such as web browsing, email access, and database applications. • A ba ...
... component that interfaces the wireless communications signals traveling through the air medium to a wired network—often referred to as a distribution system. • Base station enables users to access a wide range of network services, such as web browsing, email access, and database applications. • A ba ...
Internetworking
... – all nodes along the path from a node’s home link to its current home link must be provided with host-specific routes --> increase dramatically, as the distance grows (#Fig. 3-2 in Solomon) – mobile nodes frequently change links --> a lot of deletion and addition in the routing tables – if only min ...
... – all nodes along the path from a node’s home link to its current home link must be provided with host-specific routes --> increase dramatically, as the distance grows (#Fig. 3-2 in Solomon) – mobile nodes frequently change links --> a lot of deletion and addition in the routing tables – if only min ...
IP Routing
... source to destination. IP layer in each host and router maintains a routing table, which is used to route the packets based on IP address. If a destination host is directly connected to the originating host by a link or by a LAN, then the packet is sent directly to destination host using appropr ...
... source to destination. IP layer in each host and router maintains a routing table, which is used to route the packets based on IP address. If a destination host is directly connected to the originating host by a link or by a LAN, then the packet is sent directly to destination host using appropr ...
Demonstrating the Optimal Placement of Virtualized Cellular
... is shown. Ann and Ben are living in a so-called home area and are subscribers to an LTE network. Together with many others, Ann is traveling to the event area, a stadium. Ben stays in the home area. This is indicated by the locations of the icons representing Ann and Ben in Figure 1. Figure 3 illust ...
... is shown. Ann and Ben are living in a so-called home area and are subscribers to an LTE network. Together with many others, Ann is traveling to the event area, a stadium. Ben stays in the home area. This is indicated by the locations of the icons representing Ann and Ben in Figure 1. Figure 3 illust ...
Wireless Communications
... significant percentage of this bandwidth is used for communications overhead; in practice the maximum throughput is about 5.5 Mbit/s. Metal, water, and thick walls absorb 802.11b signals and decrease the range drastically. 802.11 runs in the 2.4 GHz spectrum and uses Carrier Sense Multiple Access wi ...
... significant percentage of this bandwidth is used for communications overhead; in practice the maximum throughput is about 5.5 Mbit/s. Metal, water, and thick walls absorb 802.11b signals and decrease the range drastically. 802.11 runs in the 2.4 GHz spectrum and uses Carrier Sense Multiple Access wi ...
Slide 1
... that had thus far characterized the mobile market. This approval meant that for the first time, full interoperability and interworking of mobile systems could be achieved. IMT-2000 offers the capability of providing value-added services and applications on the basis of a single standard. The system ...
... that had thus far characterized the mobile market. This approval meant that for the first time, full interoperability and interworking of mobile systems could be achieved. IMT-2000 offers the capability of providing value-added services and applications on the basis of a single standard. The system ...
Business Data Communications 4e
... A new, extended version of NetBIOS, the program that lets computers communicate within a local area network. Formalizes the frame format (or arrangement of information in a data transmission) that was not specified as part of NetBIOS. Business Data Communications ...
... A new, extended version of NetBIOS, the program that lets computers communicate within a local area network. Formalizes the frame format (or arrangement of information in a data transmission) that was not specified as part of NetBIOS. Business Data Communications ...
here
... much larger; (b) long-distance circuits are needed; (c) there are possibly multiple routes from one host to another host When the network is much larger, using MAC address based forwarding tables will make the network so slow because the forwarding table will be so large. To solve this problem, hier ...
... much larger; (b) long-distance circuits are needed; (c) there are possibly multiple routes from one host to another host When the network is much larger, using MAC address based forwarding tables will make the network so slow because the forwarding table will be so large. To solve this problem, hier ...
William Stallings Data and Computer Communications
... • A layer model • Each layer performs a subset of the required communication functions • Each layer relies on the next lower layer to perform more primitive functions • Each layer provides services to the next higher layer • Changes in one layer should not require changes in other layers ...
... • A layer model • Each layer performs a subset of the required communication functions • Each layer relies on the next lower layer to perform more primitive functions • Each layer provides services to the next higher layer • Changes in one layer should not require changes in other layers ...
Windows Vista networking technologies
In computing, Microsoft's Windows Vista and Windows Server 2008 introduced in 2007/2008 a new networking stack named Next Generation TCP/IP stack,to improve on the previous stack in several ways.The stack includes native implementation of IPv6, as well as a complete overhaul of IPv4. The new TCP/IP stack uses a new method to store configuration settings that enables more dynamic control and does not require a computer restart after a change in settings. The new stack, implemented as a dual-stack model, depends on a strong host-model and features an infrastructure to enable more modular components that one can dynamically insert and remove.