The TELNET Protocol
... Telnet date back to late 1960s is generally consider the first network application. – There are several RFCs are listed at the end of the lecture. ...
... Telnet date back to late 1960s is generally consider the first network application. – There are several RFCs are listed at the end of the lecture. ...
Lec9-telnet
... Telnet date back to late 1960s is generally consider the first network application. – There are several RFCs are listed at the end of the lecture. ...
... Telnet date back to late 1960s is generally consider the first network application. – There are several RFCs are listed at the end of the lecture. ...
BASrouters — BACnet Routing Examples
... This application is a variant of Application #8 except that the PC is located remotely but attached to the Internet as is the IP router. Both the PC and the WAN-side of the IP Router have public IP addresses (1.2.3.4 and 2.3.4.5 for example). On the LAN-side of the IP Router is the building’s automa ...
... This application is a variant of Application #8 except that the PC is located remotely but attached to the Internet as is the IP router. Both the PC and the WAN-side of the IP Router have public IP addresses (1.2.3.4 and 2.3.4.5 for example). On the LAN-side of the IP Router is the building’s automa ...
Access Control Lists Lecture 1
... Controlling traffic can increase network performance Distribution of routing updates can be controlled Security can be added at the network boundary Specific types of traffic can be permitted or blocked An administrator controls what areas a client can access Screen certain hosts to eith ...
... Controlling traffic can increase network performance Distribution of routing updates can be controlled Security can be added at the network boundary Specific types of traffic can be permitted or blocked An administrator controls what areas a client can access Screen certain hosts to eith ...
Universal WiFi Range Extender WN3000RP
... 1. The Extender connects to a wireless network that is up and running. When the Extender connects wirelessly to a network, it acts as a network client. This is similar to how a computer connects to a network. 2. The Extender acts as an access point for computers. The Extender has its own wireless ne ...
... 1. The Extender connects to a wireless network that is up and running. When the Extender connects wirelessly to a network, it acts as a network client. This is similar to how a computer connects to a network. 2. The Extender acts as an access point for computers. The Extender has its own wireless ne ...
Diapositiva 1 - Gaming Standards Association
... the protocol to participate in the slot network • Event and Meter subscriptions allow a host to subscribe to specific information • Operators can “try out” new products to see if they like them • Products can compete using the same data – e.g. two data mining packages can be connected to the network ...
... the protocol to participate in the slot network • Event and Meter subscriptions allow a host to subscribe to specific information • Operators can “try out” new products to see if they like them • Products can compete using the same data – e.g. two data mining packages can be connected to the network ...
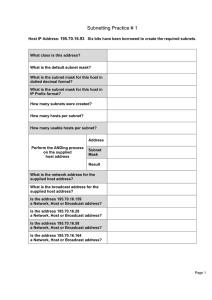
Subnetting Practice # 1
... You are the network administrator for Bunch-A-Hosts Limited in Windsor and are required to subnet the network according to the diagram. You have decided to use the network 172.16.0.0. There are multiple subnets at each site but you are only responsible for providing usable subnetworks with enough IP ...
... You are the network administrator for Bunch-A-Hosts Limited in Windsor and are required to subnet the network according to the diagram. You have decided to use the network 172.16.0.0. There are multiple subnets at each site but you are only responsible for providing usable subnetworks with enough IP ...
Chapter 7 - SaigonTech
... • Errors can occur when data is altered in medium – Usually caused by noise or faulty media connections – When the destination computer receives a frame, the CRC is recalculated and compared against the CRC value in the FCS – If values match, the data is assumed to be okay – If values don’t match, t ...
... • Errors can occur when data is altered in medium – Usually caused by noise or faulty media connections – When the destination computer receives a frame, the CRC is recalculated and compared against the CRC value in the FCS – If values match, the data is assumed to be okay – If values don’t match, t ...
IPv6 Security Threats and Mitigations
... Note: use of DHCP is announced in Router Advertisements Rogue devices on the network giving misleading information or consuming resources (DoS) Rogue DHCPv6 client and servers on the link-local multicast address (FF02::1:2): same threat as IPv4 Rogue DHCPv6 servers on the site-local multicast ad ...
... Note: use of DHCP is announced in Router Advertisements Rogue devices on the network giving misleading information or consuming resources (DoS) Rogue DHCPv6 client and servers on the link-local multicast address (FF02::1:2): same threat as IPv4 Rogue DHCPv6 servers on the site-local multicast ad ...
Ethernet - Computer Science Technology
... • Errors can occur when data is altered in medium – Usually caused by noise or faulty media connections – When the destination computer receives a frame, the CRC is recalculated and compared against the CRC value in the FCS – If values match, the data is assumed to be okay – If values don’t match, t ...
... • Errors can occur when data is altered in medium – Usually caused by noise or faulty media connections – When the destination computer receives a frame, the CRC is recalculated and compared against the CRC value in the FCS – If values match, the data is assumed to be okay – If values don’t match, t ...
TNS07%20PPP
... In reality, it is often the case that serial links can be clocked considerably faster than parallel links, and they achieve a higher data rate. ...
... In reality, it is often the case that serial links can be clocked considerably faster than parallel links, and they achieve a higher data rate. ...
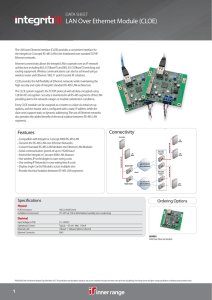
LAN Over Ethernet Module (CLOE)
... The LAN over Ethernet Interface (CLOE) provides a convenient interface for the Integriti (or Concept) RS-485 LAN to be distributed over standard TCP/IP Ethernet networks. Ethernet connectivity allows the Integriti LAN to operate over an IP network architecture including 802.3i (10baseT) and 802.3U ( ...
... The LAN over Ethernet Interface (CLOE) provides a convenient interface for the Integriti (or Concept) RS-485 LAN to be distributed over standard TCP/IP Ethernet networks. Ethernet connectivity allows the Integriti LAN to operate over an IP network architecture including 802.3i (10baseT) and 802.3U ( ...
ITE PC v4.0 Chapter 1
... Chapter 7: Summary In this chapter, you learned: The role of the transport layer is to provide three main services: multiplexing, segmentation and reassembly, and error checking. It does this by: • Dividing data received from an application into segments. • Adding a header to identify and manage ...
... Chapter 7: Summary In this chapter, you learned: The role of the transport layer is to provide three main services: multiplexing, segmentation and reassembly, and error checking. It does this by: • Dividing data received from an application into segments. • Adding a header to identify and manage ...
4100ES, 4190, 4010ES and 4010 Network
... connections only, or as a modular design allowing selection of either wired or fiber optic media modules Fiber optic communications are available with fiber media modules on the Network interface modules or when using the higher performance multiple signal fiber optic modems Fiber optic links ar ...
... connections only, or as a modular design allowing selection of either wired or fiber optic media modules Fiber optic communications are available with fiber media modules on the Network interface modules or when using the higher performance multiple signal fiber optic modems Fiber optic links ar ...
Packet Optical Networking for LTE Cell Tower Backhaul
... Enable 3G/LTE high growth data services to be efficiently backhauled over existing SONET infrastructure While facilitating migration to packet-centric infrastructure May 18, 2011 ...
... Enable 3G/LTE high growth data services to be efficiently backhauled over existing SONET infrastructure While facilitating migration to packet-centric infrastructure May 18, 2011 ...
Network Reference Model for cdma2000 Spread Spectrum
... This may be incorporated into selective routers (also known as Routing, Bridging, and Transfer Switches), public safety answering ports, emergency response agencies, and Automatic Location Information (ALI) database engines. The structure of the Emergency Service Network is beyond the scope of this ...
... This may be incorporated into selective routers (also known as Routing, Bridging, and Transfer Switches), public safety answering ports, emergency response agencies, and Automatic Location Information (ALI) database engines. The structure of the Emergency Service Network is beyond the scope of this ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... A MANET (Mobile Adhoc Network) is a collection of two or more devices equipped with wireless communications and networking capability and can communicate with another node that is immediately within their radio range or one that is outside their radio range (using intermediate node). The application ...
... A MANET (Mobile Adhoc Network) is a collection of two or more devices equipped with wireless communications and networking capability and can communicate with another node that is immediately within their radio range or one that is outside their radio range (using intermediate node). The application ...
ITE PC v4.0 Chapter 1 - Система е
... communication session between two applications and delivering data between them. TCP/IP uses two protocols to achieve this: Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Primary Responsibilities of Transport layer Protocols Tracking the individual communication between appli ...
... communication session between two applications and delivering data between them. TCP/IP uses two protocols to achieve this: Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Primary Responsibilities of Transport layer Protocols Tracking the individual communication between appli ...
ITE PC v4.0 Chapter 1
... communication session between two applications and delivering data between them. TCP/IP uses two protocols to achieve this: Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Primary Responsibilities of Transport layer Protocols Tracking the individual communication between appli ...
... communication session between two applications and delivering data between them. TCP/IP uses two protocols to achieve this: Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Primary Responsibilities of Transport layer Protocols Tracking the individual communication between appli ...
CORD Fabric, Overlay Virtualization, and Service Composition
... Finally, SR is sourcerouting, where we can change the path traffic takes through the network, by simply changing the label assignment at the source (leaf) switch there is only one switch to ‘touch’ instead of the entire ‘path’ of switches. This is how we have performed elephantflow trafficen ...
... Finally, SR is sourcerouting, where we can change the path traffic takes through the network, by simply changing the label assignment at the source (leaf) switch there is only one switch to ‘touch’ instead of the entire ‘path’ of switches. This is how we have performed elephantflow trafficen ...
William Stallings Data and Computer Communications
... Addressing level Level in architecture at which entity is named Unique address for each end system (computer) and router Network level address IP or internet address (TCP/IP) Network service access point or NSAP (OSI) ...
... Addressing level Level in architecture at which entity is named Unique address for each end system (computer) and router Network level address IP or internet address (TCP/IP) Network service access point or NSAP (OSI) ...
True-False Questions
... c. network topology linking a number of computers by a single circuit with all messages broadcast to the entire network. d. network architecture that gives equal power to all computers on the network. e. telecommunications network that spans a large geographical distance. Answer: a ...
... c. network topology linking a number of computers by a single circuit with all messages broadcast to the entire network. d. network architecture that gives equal power to all computers on the network. e. telecommunications network that spans a large geographical distance. Answer: a ...
Wire 1
... Captures (“sniffs”) messages send/received by your computer – Also stores A passive application (does not send data itself) – Contrast that to active measurements – Gets a copy of all data send/received ...
... Captures (“sniffs”) messages send/received by your computer – Also stores A passive application (does not send data itself) – Contrast that to active measurements – Gets a copy of all data send/received ...
Windows Vista networking technologies
In computing, Microsoft's Windows Vista and Windows Server 2008 introduced in 2007/2008 a new networking stack named Next Generation TCP/IP stack,to improve on the previous stack in several ways.The stack includes native implementation of IPv6, as well as a complete overhaul of IPv4. The new TCP/IP stack uses a new method to store configuration settings that enables more dynamic control and does not require a computer restart after a change in settings. The new stack, implemented as a dual-stack model, depends on a strong host-model and features an infrastructure to enable more modular components that one can dynamically insert and remove.