Linux+ Guide to Linux Certification Chapter Nine System Initialization
... • Guidelines/limitations to using FIPS: – Version 2.0 of FIPS supports the FAT16 and FAT32 filesystems only – FIPS will only work with primary Windows partition and will not resize logical drives within extended partitions – FIPS works by splitting the Windows partition into two primary partition – ...
... • Guidelines/limitations to using FIPS: – Version 2.0 of FIPS supports the FAT16 and FAT32 filesystems only – FIPS will only work with primary Windows partition and will not resize logical drives within extended partitions – FIPS works by splitting the Windows partition into two primary partition – ...
PowerPoint
... FTP install directories, floppy images, and ISO images for CDROMs with one command. • “make release” is used by many large companies to produce special versions of FreeBSD with special patches or additional software installed by default. • It is also the well documented way in which the release engi ...
... FTP install directories, floppy images, and ISO images for CDROMs with one command. • “make release” is used by many large companies to produce special versions of FreeBSD with special patches or additional software installed by default. • It is also the well documented way in which the release engi ...
Threading
... kernel threads can exist within a process, then they share the same memory and file resources. Kernel threads are preemptively multitasked if the operating system's process scheduler is preemptive. Kernel threads do not own resources except for a stack, a copy of the registers including the program ...
... kernel threads can exist within a process, then they share the same memory and file resources. Kernel threads are preemptively multitasked if the operating system's process scheduler is preemptive. Kernel threads do not own resources except for a stack, a copy of the registers including the program ...
slides.02.pdf
... • Associated with each I/O device is a memory location where execution continues when that device generates an interrupt (interrupt vector). • The interrupt vector contains the start address of an operating-system provided procedure (interrupt handler). Execution continues with that procedure. ...
... • Associated with each I/O device is a memory location where execution continues when that device generates an interrupt (interrupt vector). • The interrupt vector contains the start address of an operating-system provided procedure (interrupt handler). Execution continues with that procedure. ...
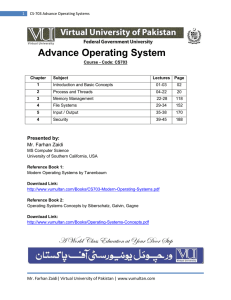
CS-703 Advance Operating Systems
... • C/C++ programming. This is an essential pre-requisite since without this; you won‘t be able to do the assignments. • An undergraduate first course on data structures. This should include implementation of elementary data structures e.g. lists, stack, queues, trees etc. in a high level language lik ...
... • C/C++ programming. This is an essential pre-requisite since without this; you won‘t be able to do the assignments. • An undergraduate first course on data structures. This should include implementation of elementary data structures e.g. lists, stack, queues, trees etc. in a high level language lik ...
FreeBSD for the Linux user
... FTP install directories, floppy images, and ISO images for CDROMs with one command. • “make release” is used by many large companies to produce special versions of FreeBSD with special patches or additional software installed by default. • It is also the well documented way in which the release engi ...
... FTP install directories, floppy images, and ISO images for CDROMs with one command. • “make release” is used by many large companies to produce special versions of FreeBSD with special patches or additional software installed by default. • It is also the well documented way in which the release engi ...
Operating System
... frequently that the users may interact with each program while it is running. Time-sharing systems were developed to provide interactive use of a computer system at a reasonable cost. A time-shared operating system uses CPU scheduling and multiprogramming to provide each user with a small portion of ...
... frequently that the users may interact with each program while it is running. Time-sharing systems were developed to provide interactive use of a computer system at a reasonable cost. A time-shared operating system uses CPU scheduling and multiprogramming to provide each user with a small portion of ...
Xen and the Art of Virtualization
... Notwithstanding the intricacies of the x86, there are other arguments against full virtualization. In particular, there are situations in which it is desirable for the hosted operating systems to see real as well as virtual resources: providing both real and virtual time allows a guest OS to better ...
... Notwithstanding the intricacies of the x86, there are other arguments against full virtualization. In particular, there are situations in which it is desirable for the hosted operating systems to see real as well as virtual resources: providing both real and virtual time allows a guest OS to better ...
Xen and the Art of Virtualization
... Notwithstanding the intricacies of the x86, there are other arguments against full virtualization. In particular, there are situations in which it is desirable for the hosted operating systems to see real as well as virtual resources: providing both real and virtual time allows a guest OS to better ...
... Notwithstanding the intricacies of the x86, there are other arguments against full virtualization. In particular, there are situations in which it is desirable for the hosted operating systems to see real as well as virtual resources: providing both real and virtual time allows a guest OS to better ...
Networks and Operating Systems (252-0062
... and everything will be done for you without your ever having to know, so just shut up. ...
... and everything will be done for you without your ever having to know, so just shut up. ...
Week_3 Operating system File
... A thread is a basic unit of CPU utilization; it comprises a thread ID, a program counter, a register set, and a stack. If a process has multiple threads of control, it can perform more than one task at a time. In certain situations, a single application may be required to perform several simil ...
... A thread is a basic unit of CPU utilization; it comprises a thread ID, a program counter, a register set, and a stack. If a process has multiple threads of control, it can perform more than one task at a time. In certain situations, a single application may be required to perform several simil ...
Porting OSE Systems to Linux
... and customisations, which has given birth to countless of tools and utilities to ease both development and management. Just like the Linux kernel itself most of the tools are available free of charge. The large user base also means that there are many developers on the employment market who knows th ...
... and customisations, which has given birth to countless of tools and utilities to ease both development and management. Just like the Linux kernel itself most of the tools are available free of charge. The large user base also means that there are many developers on the employment market who knows th ...
Figure 5.01
... application may allow a program to continue running even if part of it is blocked or is performing a length operation, thereby increasing responsiveness to the user. For example, a multithreaded Web browser could allow user interaction in one thread while an image was being loaded in another thread. ...
... application may allow a program to continue running even if part of it is blocked or is performing a length operation, thereby increasing responsiveness to the user. For example, a multithreaded Web browser could allow user interaction in one thread while an image was being loaded in another thread. ...
operating system concepts
... 2.6 Some computer systems do not provide a privileged mode of operation in hardware. Consider whether it is possible to construct a secure operating system for these computers. Give arguments both that it is and that it is not possible. Answer: An operating system for a machine of this type would ne ...
... 2.6 Some computer systems do not provide a privileged mode of operation in hardware. Consider whether it is possible to construct a secure operating system for these computers. Give arguments both that it is and that it is not possible. Answer: An operating system for a machine of this type would ne ...
Exception Handling in the Choices Operating System
... C++ exception handling support in the object oriented Choices operating system [13]. Exceptions can be thrown for any detected error that can be attributed to a process. This paper specifically addresses errors signaled by the processor. Processor exceptions generated by errant code or faulty hardwa ...
... C++ exception handling support in the object oriented Choices operating system [13]. Exceptions can be thrown for any detected error that can be attributed to a process. This paper specifically addresses errors signaled by the processor. Processor exceptions generated by errant code or faulty hardwa ...
ch4-v2
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the parent ...
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the parent ...
ppt
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the parent ...
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the parent ...
Chapter 10: Multiprocessor and Real
... Peer architecture • Kernel can execute on any processor • Each processor does self-scheduling • Complicates the operating system – Make sure two processors do not choose the same process ...
... Peer architecture • Kernel can execute on any processor • Each processor does self-scheduling • Complicates the operating system – Make sure two processors do not choose the same process ...
Operating Systems
... Peer architecture • Kernel can execute on any processor • Each processor does self-scheduling • Complicates the operating system – Make sure two processors do not choose the same process ...
... Peer architecture • Kernel can execute on any processor • Each processor does self-scheduling • Complicates the operating system – Make sure two processors do not choose the same process ...
Proceedings of the General Track: 2003 USENIX Annual Technical Conference
... called UMLinux [Buchacker01]. UMLinux was developed by researchers at the University of Erlangen-Nürnberg for use in fault-injection experiments. UMLinux is a Type II VMM: the guest operating system and all guest applications run as a single process (the guestmachine process) on a host Linux operati ...
... called UMLinux [Buchacker01]. UMLinux was developed by researchers at the University of Erlangen-Nürnberg for use in fault-injection experiments. UMLinux is a Type II VMM: the guest operating system and all guest applications run as a single process (the guestmachine process) on a host Linux operati ...
DEGREE PROGRAM IN ELECTRICAL ENGINEERING LINUX
... implement a network layer without an operating system. Hence, Linux implements network layer functionality very well, research scenarios are much easier to implement, because there is no need to concentrate on an unrelevant low level functionality. It is possible to control all layers of the OSI mod ...
... implement a network layer without an operating system. Hence, Linux implements network layer functionality very well, research scenarios are much easier to implement, because there is no need to concentrate on an unrelevant low level functionality. It is possible to control all layers of the OSI mod ...
Notes on Operating Systems
... When a user application is running, the operating system loses its control over the machine. It regains control if the user application performs a system call, or if there is a hardware interrupt. Exercise 1 How can the operating system guarantee that there will be a system call or interrupt, so tha ...
... When a user application is running, the operating system loses its control over the machine. It regains control if the user application performs a system call, or if there is a hardware interrupt. Exercise 1 How can the operating system guarantee that there will be a system call or interrupt, so tha ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.