lecture.9
... • Sometimes, you want several threads to work together in a group, and not to proceed past some point in a critical section (the Barrier) before all threads in the group have arrived at the same point • A Barrier is created by setting its value to the number of threads in the group • A Barrier can b ...
... • Sometimes, you want several threads to work together in a group, and not to proceed past some point in a critical section (the Barrier) before all threads in the group have arrived at the same point • A Barrier is created by setting its value to the number of threads in the group • A Barrier can b ...
threads
... • Sometimes, you want several threads to work together in a group, and not to proceed past some point in a critical section (the Barrier) before all threads in the group have arrived at the same point • A Barrier is created by setting its value to the number of threads in the group • A Barrier can b ...
... • Sometimes, you want several threads to work together in a group, and not to proceed past some point in a critical section (the Barrier) before all threads in the group have arrived at the same point • A Barrier is created by setting its value to the number of threads in the group • A Barrier can b ...
The Architecture of a Worldwide Distributed System
... period of learning as much as you can in as many different subjects that are interesting. In this respect I took full advantage of my Ph.D.: I did work ranging from programming my own EEPROMs, to secure network objects, digital video on demand, and a full blown new operating system with its own TCP/ ...
... period of learning as much as you can in as many different subjects that are interesting. In this respect I took full advantage of my Ph.D.: I did work ranging from programming my own EEPROMs, to secure network objects, digital video on demand, and a full blown new operating system with its own TCP/ ...
Operating Systems Concepts with Java
... • I/O systems: Chapters 13 and 14 describe the devices that attach to a computer and the multiple dimensions on which they vary. Because these devices differ so widely, the operating system needs to provide a wide range of functionality to applications to allow them to control all aspects of the de ...
... • I/O systems: Chapters 13 and 14 describe the devices that attach to a computer and the multiple dimensions on which they vary. Because these devices differ so widely, the operating system needs to provide a wide range of functionality to applications to allow them to control all aspects of the de ...
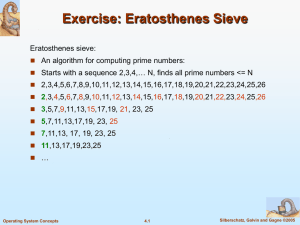
ch4
... Goal: Write multithreaded matrix multiplication algorithm, in order to make use of several CPUs. Single threaded algorithm for multiplying n x n matrices A and B : for(i=0; i
... Goal: Write multithreaded matrix multiplication algorithm, in order to make use of several CPUs. Single threaded algorithm for multiplying n x n matrices A and B : for(i=0; i
OperatingSystems_FA15_4_Threads
... Speed of execution: Multi-threaded process can read and block for data, while another thread can process the data. Modularity: Processes that has separate activities or variety of sources and destinations can implement these activities as threads. SILICON VALLEY UNIVERSITY CONFIDENTIAL ...
... Speed of execution: Multi-threaded process can read and block for data, while another thread can process the data. Modularity: Processes that has separate activities or variety of sources and destinations can implement these activities as threads. SILICON VALLEY UNIVERSITY CONFIDENTIAL ...
Linux+ Guide to Linux Certification
... • Bus: Pathway information takes from one hardware device to another via a mainboard • Mainboard (also called a motherboard): Circuit board that connects all other hardware components together via slots or ports on the circuit board • Peripheral components: Attach to the mainboard of a computer – e. ...
... • Bus: Pathway information takes from one hardware device to another via a mainboard • Mainboard (also called a motherboard): Circuit board that connects all other hardware components together via slots or ports on the circuit board • Peripheral components: Attach to the mainboard of a computer – e. ...
Chaps_1-13_v5.0
... The system administrators have privileges on all the UNIX systems beyond that of any user. They can do anything to any of the systems or the network. Setting up a complex UNIX networking environment requires more technical knowledge and sophistication than an equivalent Windows environment (which is ...
... The system administrators have privileges on all the UNIX systems beyond that of any user. They can do anything to any of the systems or the network. Setting up a complex UNIX networking environment requires more technical knowledge and sophistication than an equivalent Windows environment (which is ...
ch4
... For speed, implement threads at the user level A user-level thread is managed by the run-time system user-level code that is linked with your program Each thread is represented simply by: PC Registers Stack Small control block All thread operations are at the user-level: Creating a new t ...
... For speed, implement threads at the user level A user-level thread is managed by the run-time system user-level code that is linked with your program Each thread is represented simply by: PC Registers Stack Small control block All thread operations are at the user-level: Creating a new t ...
etc/rc.boot
... When the kernel has started itself (has been loaded into memory, has started running, and has initialised all device drivers and data structures and such), it finishes its own part of the boot process by starting a user level program, init. Thus, init is always the first process (its process number ...
... When the kernel has started itself (has been loaded into memory, has started running, and has initialised all device drivers and data structures and such), it finishes its own part of the boot process by starting a user level program, init. Thus, init is always the first process (its process number ...
Dancing with Giants: Wimpy Kernels for On-demand Isolated I/O
... Central to on-demand isolation of I/O channels is the notion of the wimpy kernel, which constructs these channels without affecting the underlying TCB; i.e., without modifying its security properties and increasing the verification effort [39, 66]. The wimpy kernel is an add-on trustworthy service t ...
... Central to on-demand isolation of I/O channels is the notion of the wimpy kernel, which constructs these channels without affecting the underlying TCB; i.e., without modifying its security properties and increasing the verification effort [39, 66]. The wimpy kernel is an add-on trustworthy service t ...
Multics
... the eventual GE 645. Bell Labs joined the software development in 1965. The Multics project had very ambitious and revolutionary goals, so it is not surprising that the project had its moments of intrigue. The project called for delivery of the project in two and a half years, but delivery of the GE ...
... the eventual GE 645. Bell Labs joined the software development in 1965. The Multics project had very ambitious and revolutionary goals, so it is not surprising that the project had its moments of intrigue. The project called for delivery of the project in two and a half years, but delivery of the GE ...
Threads
... – an address space (defining all the code and data pages) – OS resources and accounting information – a “thread of control”, • defines where the process is currently executing • That is the PC and registers ...
... – an address space (defining all the code and data pages) – OS resources and accounting information – a “thread of control”, • defines where the process is currently executing • That is the PC and registers ...
Operating systems
... b. Interactive. Composed of many short transactions where the results of the next transaction may be unpredictable. Response time needs to be short (seconds) since the user submits and waits for the result. c. Time sharing. Uses CPU scheduling and multiprogramming to provide economical interactive u ...
... b. Interactive. Composed of many short transactions where the results of the next transaction may be unpredictable. Response time needs to be short (seconds) since the user submits and waits for the result. c. Time sharing. Uses CPU scheduling and multiprogramming to provide economical interactive u ...
Developing Interfaces and Interactivity for DSpace with
... – No, but.... – Basic understanding will help diagnose problems – Many skill levels represented here • Some really NEED this knowledge (and may already have it) • Will help others UNDERSTAND their tech people ...
... – No, but.... – Basic understanding will help diagnose problems – Many skill levels represented here • Some really NEED this knowledge (and may already have it) • Will help others UNDERSTAND their tech people ...
Word - Center for Sustainable Energy
... equipment). 11. For grid-connected systems, inverter is marked “utility interactive.” 12. For ungrounded inverters, installation complies with CEC 690.35 requirements. 13. Conductors, cables and conduit types, sizes and markings according to the approved plan. 14. Overcurrent devices are the type an ...
... equipment). 11. For grid-connected systems, inverter is marked “utility interactive.” 12. For ungrounded inverters, installation complies with CEC 690.35 requirements. 13. Conductors, cables and conduit types, sizes and markings according to the approved plan. 14. Overcurrent devices are the type an ...
Red Hat Enterprise Linux 4 Update 1 EAL4 High Level Design
... of International Business Machines Corporation in the United States, other countries, or both. Linux is a registered trademark of Linus Torvalds. UNIX is a registered trademark of The Open Group in the United States and other countries. Intel and Pentium are trademarks of Intel Corporation in the Un ...
... of International Business Machines Corporation in the United States, other countries, or both. Linux is a registered trademark of Linus Torvalds. UNIX is a registered trademark of The Open Group in the United States and other countries. Intel and Pentium are trademarks of Intel Corporation in the Un ...
Eliminating Receive Livelock in an Interrupt-Driven Kernel
... (The system design avoids lengthy periods at high IPL, in order to reduce latency for handling certain other events, such as lower-priority device interrupts.) The queues between steps executed at di erent IPLs provide some insulation against packet losses due to transient overloads, but typically t ...
... (The system design avoids lengthy periods at high IPL, in order to reduce latency for handling certain other events, such as lower-priority device interrupts.) The queues between steps executed at di erent IPLs provide some insulation against packet losses due to transient overloads, but typically t ...
Midterm study guide
... 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is ...
... 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is ...
Differences Between IBM eServer iSeries and pSeries Servers
... Linux on iSeries can be done via OS/400 operator commands if the Linux partition is hosted (described below in the Linux Integration section) or by Linux commands. I/O for a Linux Partition I/O support for Linux is very straightforward on partitioned pSeries systems. Each Linux partition is assigne ...
... Linux on iSeries can be done via OS/400 operator commands if the Linux partition is hosted (described below in the Linux Integration section) or by Linux commands. I/O for a Linux Partition I/O support for Linux is very straightforward on partitioned pSeries systems. Each Linux partition is assigne ...
Dell OpenManage Deployment Toolkit Version 5.2.1 User`s Guide
... script-based and RPM-based installation for deploying large number of systems on a pre-operating system environment in a reliable way, without changing their current deployment processes. Using DTK you can install operating systems on Dell systems in BIOS or Unified Extensible Firmware Interface (UE ...
... script-based and RPM-based installation for deploying large number of systems on a pre-operating system environment in a reliable way, without changing their current deployment processes. Using DTK you can install operating systems on Dell systems in BIOS or Unified Extensible Firmware Interface (UE ...
Operating system/IT0307
... statements is called variously: – control‐card interpreter – command‐line interpreter – shell (in UNIX) ...
... statements is called variously: – control‐card interpreter – command‐line interpreter – shell (in UNIX) ...
STUDY GUIDE FOR THE MIDTERM EXAM of Tuesday November 3
... 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is ...
... 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.