ch3
... between a running program and the operating system: Pass parameters in registers Store the parameters in a table in memory, and the table address is passed as a parameter in a register III. Push (store) the parameters onto the stack by the program, and pop off the stack by operating system ...
... between a running program and the operating system: Pass parameters in registers Store the parameters in a table in memory, and the table address is passed as a parameter in a register III. Push (store) the parameters onto the stack by the program, and pop off the stack by operating system ...
Section A: Operating Systems Basics
... The conceptual model of folders and files does not reflect the physical reality of the way in which files are stored on a disk. Students may confuse this statement with the explanation of fragmentation discussed later in the section. Remind students that randomaccess storage allows files to become p ...
... The conceptual model of folders and files does not reflect the physical reality of the way in which files are stored on a disk. Students may confuse this statement with the explanation of fragmentation discussed later in the section. Remind students that randomaccess storage allows files to become p ...
Comparative Operating Systems Fall 2001 An Examination of
... sophisticated, highly reputable operating system for desktop PC's and servers. Since Linux is so well accepted, and free with open source code, it is no wonder that embedded developers have begun to look for ways to incorporate it into their devices. ...
... sophisticated, highly reputable operating system for desktop PC's and servers. Since Linux is so well accepted, and free with open source code, it is no wonder that embedded developers have begun to look for ways to incorporate it into their devices. ...
Slides - CSE, IIT Bombay
... – Prompt service can be provided through exclusive use of a computer; however, efficient use requires sharing of a computer’s resources among many users – An OS designer decides which of the two goals is more important under what conditions * That is why we have so many operating systems! ...
... – Prompt service can be provided through exclusive use of a computer; however, efficient use requires sharing of a computer’s resources among many users – An OS designer decides which of the two goals is more important under what conditions * That is why we have so many operating systems! ...
Lecture 1
... 2. Operating system – controls and coordinates the use of the hardware among the various application programs for the various users. 3. Applications programs – define the ways in which the system resources are used to solve the computing problems of the users (compilers, database systems, ...
... 2. Operating system – controls and coordinates the use of the hardware among the various application programs for the various users. 3. Applications programs – define the ways in which the system resources are used to solve the computing problems of the users (compilers, database systems, ...
Abstract View of System Components
... Transferring information between computers via networks became more economical and practical ...
... Transferring information between computers via networks became more economical and practical ...
A Pattern Language for Secure Operating System Architectures
... • Systems that use explicit message passing have the possibility of checking each message to see if it complies with system policies. • For example, a security feature that can be applied when calling another process is protected ...
... • Systems that use explicit message passing have the possibility of checking each message to see if it complies with system policies. • For example, a security feature that can be applied when calling another process is protected ...
Module 4: Processes
... The context (or image) of a process can be described by – contents of main memory – contents of CPU registers – other info (open files, I/O in progress, etc.) Main memory -- three logically distinct regions of memory: – code region: contains executable code (typically read-only) ...
... The context (or image) of a process can be described by – contents of main memory – contents of CPU registers – other info (open files, I/O in progress, etc.) Main memory -- three logically distinct regions of memory: – code region: contains executable code (typically read-only) ...
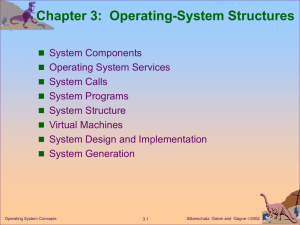
Operating-System Structures
... Two common approaches for users to interface with OS. Command line interface (CLI) or command interpreter Shell: program that is executed automatically when a job is initiated or a user logs on. Get and execute the next user-specified command ...
... Two common approaches for users to interface with OS. Command line interface (CLI) or command interpreter Shell: program that is executed automatically when a job is initiated or a user logs on. Get and execute the next user-specified command ...
PPT Chapter 09
... Message Passing in Unix: Pipes • FIFO mechanism for data transfer between processes called reader and writer processes • Usually implemented in file system – But, data put into a pipe can be read only once • Removed from pipe when it is read by a process ...
... Message Passing in Unix: Pipes • FIFO mechanism for data transfer between processes called reader and writer processes • Usually implemented in file system – But, data put into a pipe can be read only once • Removed from pipe when it is read by a process ...
PPT - Defcon
... Make the Owner of the Token Any User Make Any Actions Taken by the Process Appear to be Someone else such as System ...
... Make the Owner of the Token Any User Make Any Actions Taken by the Process Appear to be Someone else such as System ...
Chapter 2: Operating-System Structures
... kernel as though they were all hardware ■ A virtual machine provides an interface identical to the ...
... kernel as though they were all hardware ■ A virtual machine provides an interface identical to the ...
Microkernels
... Exokernel web server performance features: – Transmits data directly from page cache w/o copying. – Colocates hyperlinked files within filesystem. – Network stack tuned to reduce packets by 20%. ...
... Exokernel web server performance features: – Transmits data directly from page cache w/o copying. – Colocates hyperlinked files within filesystem. – Network stack tuned to reduce packets by 20%. ...
LEC6-FileSystem
... ° OS provide a way to map files into the address space of a running process; map() and unmap() • No read or write system calls are needed thereafter ...
... ° OS provide a way to map files into the address space of a running process; map() and unmap() • No read or write system calls are needed thereafter ...
Operating System - Chap1: An Introduction to Operating System
... 1.1 INTRODUCTION In the early days of computer use, computers were huge machines, which were expensive to buy, run, and maintain. The user at that time interacted directly with the hardware through machine language. A software was required which could perform basic tasks, such as recognizing input f ...
... 1.1 INTRODUCTION In the early days of computer use, computers were huge machines, which were expensive to buy, run, and maintain. The user at that time interacted directly with the hardware through machine language. A software was required which could perform basic tasks, such as recognizing input f ...
Document
... each built on top of lower layers. The bottom layer (layer 0), is the hardware; the highest (layer N) is the user interface. With modularity, layers are ...
... each built on top of lower layers. The bottom layer (layer 0), is the hardware; the highest (layer N) is the user interface. With modularity, layers are ...
Chapter 1: Introduction What is an Operating System? Computer
... ) once finished, it seeks next job from user ...
... ) once finished, it seeks next job from user ...
pdf book chapter - LIRA-Lab
... Multiprocessor Operating Systems An important, but often not entirely obvious extension to uniprocessor operating systems, is support for multiple processors having access to a shared memory. Conceptually, the extension is simple in that all data structures needed by the operating system to manage t ...
... Multiprocessor Operating Systems An important, but often not entirely obvious extension to uniprocessor operating systems, is support for multiple processors having access to a shared memory. Conceptually, the extension is simple in that all data structures needed by the operating system to manage t ...
OS Lab Manual
... why an operating is called a resource manager. Some of important tasks, which a typical modern operating system has to perform, are given below: ...
... why an operating is called a resource manager. Some of important tasks, which a typical modern operating system has to perform, are given below: ...
CS533 Concepts of Operating Systems
... User-level exception handler (trampoline) emulates the native system call ‘trap’ instruction for binary compatibility ...
... User-level exception handler (trampoline) emulates the native system call ‘trap’ instruction for binary compatibility ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.