1.01 - UCSB Computer Science
... C program invoking printf() library call, which calls write() system call ...
... C program invoking printf() library call, which calls write() system call ...
2.01 - SEJONG
... Operating System Services User Operating System Interface System Calls Types of System Calls System Programs Operating System Design and Implementation Operating System Structure ...
... Operating System Services User Operating System Interface System Calls Types of System Calls System Programs Operating System Design and Implementation Operating System Structure ...
CS533 Concepts of Operating Systems
... The “Fault” operation is an example of extensibility – measures the time to resolve a page fault by a user-defined pager in a separate address space. “Trap” – Latency between a write operation to a protected page, and the invocation of related exception handler. “Appel1” – Time to access a random pr ...
... The “Fault” operation is an example of extensibility – measures the time to resolve a page fault by a user-defined pager in a separate address space. “Trap” – Latency between a write operation to a protected page, and the invocation of related exception handler. “Appel1” – Time to access a random pr ...
Lecture 3
... Microkernel System Structure Developed at Carnegie Mellon University in the mid 1980th Modularizes the kernel Moves as much from the kernel into “user” space: all nonessential ...
... Microkernel System Structure Developed at Carnegie Mellon University in the mid 1980th Modularizes the kernel Moves as much from the kernel into “user” space: all nonessential ...
Minor Thesis presentation
... • All these developments are having master/slave relationship, where microprocessor based desktop or PC running Linux, Unix or Windows acts as a master is connected with single or multiple FPGA boards which acts as slave. This master/slave relationship has some bandwidth limitations which does not a ...
... • All these developments are having master/slave relationship, where microprocessor based desktop or PC running Linux, Unix or Windows acts as a master is connected with single or multiple FPGA boards which acts as slave. This master/slave relationship has some bandwidth limitations which does not a ...
Kernel (computer science)
... of protection it is not possible to assign different privileges to processes that are at the same privileged level, and therefore is not possible to satisfy Denning's four principles for fault tolerance[15][16] (particularly the Principle of least privilege). Hierarchical protection domains also hav ...
... of protection it is not possible to assign different privileges to processes that are at the same privileged level, and therefore is not possible to satisfy Denning's four principles for fault tolerance[15][16] (particularly the Principle of least privilege). Hierarchical protection domains also hav ...
The Macintosh File System (continued)
... • chkdsk utility – much more robust than in other Windows operating systems Guide to Operating Systems, Third Edition ...
... • chkdsk utility – much more robust than in other Windows operating systems Guide to Operating Systems, Third Edition ...
summary of subject matter/topics and course requirements
... techniques in security and protection of an operating system ...
... techniques in security and protection of an operating system ...
Monolithic kernel vs. Microkernel
... Monolithic kernels (and most of the first generation µ-kernels) run device drivers inside the kernel space. Hardware interrupts are directly handled by kernel processes. To add or change features provided by the hardware, all layers above the changed layer in the monolithic kernel also have to be ch ...
... Monolithic kernels (and most of the first generation µ-kernels) run device drivers inside the kernel space. Hardware interrupts are directly handled by kernel processes. To add or change features provided by the hardware, all layers above the changed layer in the monolithic kernel also have to be ch ...
slides
... permanently, the computer system must provide secondary storage to back up main memory. • Most modern computer systems use disks as the principal on-line storage medium, for both programs and data. • The operating system is responsible for the following activities in connection with disk management: ...
... permanently, the computer system must provide secondary storage to back up main memory. • Most modern computer systems use disks as the principal on-line storage medium, for both programs and data. • The operating system is responsible for the following activities in connection with disk management: ...
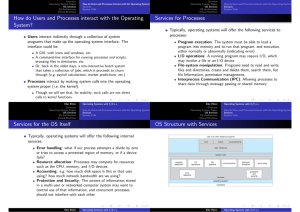
Module 3: Operating
... Accounting – keep track of and record which users use how much and what kinds of computer resources for account billing or for accumulating usage statistics. Protection – ensuring that all access to system resources is controlled, ex: firewalls, passwords, file permissions, etc. ...
... Accounting – keep track of and record which users use how much and what kinds of computer resources for account billing or for accumulating usage statistics. Protection – ensuring that all access to system resources is controlled, ex: firewalls, passwords, file permissions, etc. ...
Linux+ Guide to Linux Certification Chapter One Introduction to Linux
... • Linux is an operating system (OS) whose kernel and many additional software packages are freely developed and improved upon by a large community of software developers in ...
... • Linux is an operating system (OS) whose kernel and many additional software packages are freely developed and improved upon by a large community of software developers in ...
Chapter 2: Operating-System Structures
... Apple Mac OS X as “Aqua” GUI interface with UNIX kernel underneath and shells available ...
... Apple Mac OS X as “Aqua” GUI interface with UNIX kernel underneath and shells available ...
Intro to Linux Slides - Raspberry PI Summer Camp at IPFW
... existence as a server OS and Has become useful as a desktop OS, It can also be used on all of these devices. “From wristwatches to supercomputers,” is the popular description of Linux' capabilities. ...
... existence as a server OS and Has become useful as a desktop OS, It can also be used on all of these devices. “From wristwatches to supercomputers,” is the popular description of Linux' capabilities. ...
Discovering Computers
... or apps to memory, turns off all unneeded functions, and then places the computer in a ...
... or apps to memory, turns off all unneeded functions, and then places the computer in a ...
ppt
... common PC hardware, but also runs on a variety of other platforms The core Linux operating system kernel is entirely original, but it can run much existing free UNIX software, resulting in an entire UNIX-compatible operating system free from proprietary code Linux system has many, varying Linux ...
... common PC hardware, but also runs on a variety of other platforms The core Linux operating system kernel is entirely original, but it can run much existing free UNIX software, resulting in an entire UNIX-compatible operating system free from proprietary code Linux system has many, varying Linux ...
PPT - UNL CSE
... Tom is deploying a new server program for his client. During the field test, he notices that its performance is below his expectation. How would he identify the main causes? A company is planning to upgrade the server systems. You are asked to analyze which systems and which configurations will ...
... Tom is deploying a new server program for his client. During the field test, he notices that its performance is below his expectation. How would he identify the main causes? A company is planning to upgrade the server systems. You are asked to analyze which systems and which configurations will ...
Module 3: Operating
... host id, process name or process id). Use get process id or get host id. open connection, close connection recipient uses accept connection The initiator is the client. The recipient of the request is the server. ...
... host id, process name or process id). Use get process id or get host id. open connection, close connection recipient uses accept connection The initiator is the client. The recipient of the request is the server. ...
Linux+ Guide to Linux Certification
... – Accepts and runs batch programs in the background when the interactive load is light ...
... – Accepts and runs batch programs in the background when the interactive load is light ...
How do Users and Processes interact with the Operating System
... Traditional UNIX UNIX - one big kernel Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a large number of functions for one level Limited to hardware support compi ...
... Traditional UNIX UNIX - one big kernel Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a large number of functions for one level Limited to hardware support compi ...
Basic Unix - University of Arizona
... lists the files in a directory one screenful at a time How this works: • ls writes its output to its stdout • more’s input stream defaults to its stdin • the pipe connects ls’s stdout to more’s stdin • the piped commands run “in parallel” ...
... lists the files in a directory one screenful at a time How this works: • ls writes its output to its stdout • more’s input stream defaults to its stdin • the pipe connects ls’s stdout to more’s stdin • the piped commands run “in parallel” ...
Blue Background
... Unlike the official Unix operating system, Linux is distributed freely under GNU General Public Licence (GPL) as specified by the Free Software Foundation. Linux is copyrighted and it is not public domain. However, a GNU Public Licence has much the same effect as being in the public domain. The lice ...
... Unlike the official Unix operating system, Linux is distributed freely under GNU General Public Licence (GPL) as specified by the Free Software Foundation. Linux is copyrighted and it is not public domain. However, a GNU Public Licence has much the same effect as being in the public domain. The lice ...
Are Virtual-Machine Monitors Microkernels Done Right?
... Here Hand et al. argue that, while microkernel designers have spent considerable effort on optimising inter-process communication (IPC) mechanisms, this is irrelevant as it is “not a critical design concern in the construction of high-performance VMMs.” They further argue that IPC between virtual ma ...
... Here Hand et al. argue that, while microkernel designers have spent considerable effort on optimising inter-process communication (IPC) mechanisms, this is irrelevant as it is “not a critical design concern in the construction of high-performance VMMs.” They further argue that IPC between virtual ma ...
Berkeley Software Distribution
Berkeley Software Distribution (BSD) is a Unix operating system derivative developed and distributed by the Computer Systems Research Group (CSRG) of the University of California, Berkeley, from 1977 to 1995. Today the term ""BSD"" is often used non-specifically to refer to any of the BSD descendants which together form a branch of the family of Unix-like operating systems. Operating systems derived from the original BSD code remain actively developed and widely used.Historically, BSD has been considered a branch of Unix, Berkeley Unix, because it shared the initial codebase and design with the original AT&T Unix operating system. In the 1980s, BSD was widely adopted by vendors of workstation-class systems in the form of proprietary Unix variants such as DEC ULTRIX and Sun Microsystems SunOS. This can be attributed to the ease with which it could be licensed, and the familiarity the founders of many technology companies of the time had with it.Although these proprietary BSD derivatives were largely superseded by the UNIX System V Release 4 and OSF/1 systems in the 1990s (both of which incorporated BSD code and are the basis of other modern Unix systems), later BSD releases provided a basis for several open source development projects, e.g. FreeBSD, OpenBSD, NetBSD, Darwin or PC-BSD, that are ongoing. These, in turn, have been incorporated in whole or in part in modern proprietary operating systems, e.g. the TCP/IP networking code in Windows NT 3.1 and most of the foundation of Apple's OS X and iOS.