Chapter 7A Functions of Operating Systems Types of Operating
... – 32-bit OS – Very stable – Windows NT Workstation • Single user multi tasking OS ...
... – 32-bit OS – Very stable – Windows NT Workstation • Single user multi tasking OS ...
linux: a product of the internet
... takes advantage of available hardware power. Because Linux was written almost entirely in a machine-independent language (C) ,It can be adapted to different machines and can meet special requirements. The file structure takes full advantage of large, fast hard disks. Equally important, it was origin ...
... takes advantage of available hardware power. Because Linux was written almost entirely in a machine-independent language (C) ,It can be adapted to different machines and can meet special requirements. The file structure takes full advantage of large, fast hard disks. Equally important, it was origin ...
Proceedings of The National Conference
... As a starting point, an initial default installation of Red Hat Linux 7.3 served to reveal and even answer some of the problems associated with the project’s requirements and design. Red Hat 7.3 was readily available at the USMA Information and Technology Operations Center (ITOC) and seemed to be a ...
... As a starting point, an initial default installation of Red Hat Linux 7.3 served to reveal and even answer some of the problems associated with the project’s requirements and design. Red Hat 7.3 was readily available at the USMA Information and Technology Operations Center (ITOC) and seemed to be a ...
Linux+ Guide to Linux Certification
... They believe in open and distributed computing amongst the IT industry With free IT industry communication in open peer-to-peer exchanges. They believe in open & available sourcecode. They place some or all of their products under the GPL license making them opensource products. They believe in the ...
... They believe in open and distributed computing amongst the IT industry With free IT industry communication in open peer-to-peer exchanges. They believe in open & available sourcecode. They place some or all of their products under the GPL license making them opensource products. They believe in the ...
Shin Liu 2/26/2015 Chapter 4 Power Point Answers and Questions 1
... utilities, device drivers, operating systems, and language translators. The “utilities” are specializeprograms that make computing easier; like antivirus programs use to clean/protect the user’s computer, or backup programs in case the user’s computer crash and data is lost. “Device drivers” allow c ...
... utilities, device drivers, operating systems, and language translators. The “utilities” are specializeprograms that make computing easier; like antivirus programs use to clean/protect the user’s computer, or backup programs in case the user’s computer crash and data is lost. “Device drivers” allow c ...
Installing guest operating systems on VMWare and Linux Kernel
... Installing guest operating systems on Linux Kernel-based Virtual Machine (KVM) virtual servers To install a quest operating system on a KVM virtual server, follow the steps in the Installing guest operating systems on Linux Kernel-based Virtual Machine (KVM) virtual servers quick start guide, which ...
... Installing guest operating systems on Linux Kernel-based Virtual Machine (KVM) virtual servers To install a quest operating system on a KVM virtual server, follow the steps in the Installing guest operating systems on Linux Kernel-based Virtual Machine (KVM) virtual servers quick start guide, which ...
Server Installation - gozips.uakron.edu
... Identify a computer on the network Windows communicates the computer name to other computers on the subnet so it should be unique Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than one computer ...
... Identify a computer on the network Windows communicates the computer name to other computers on the subnet so it should be unique Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than one computer ...
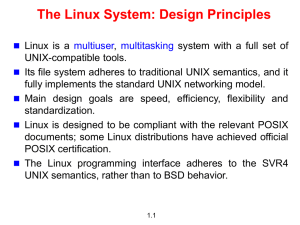
The Linux System
... /etc All the configuration files for the various software are stored here. Don't play with this directory. /home All users will have their 'My Documents' under this directory. If your id is rossi, your 'My Documents' (called home-directory) is /home/rossi. /lib The libraries required by system-appli ...
... /etc All the configuration files for the various software are stored here. Don't play with this directory. /home All users will have their 'My Documents' under this directory. If your id is rossi, your 'My Documents' (called home-directory) is /home/rossi. /lib The libraries required by system-appli ...
Document
... – CPU begins executing commands in BIOS – BIOS passes control to boot loader – Boot loader passes control to Linux kernel ...
... – CPU begins executing commands in BIOS – BIOS passes control to boot loader – Boot loader passes control to Linux kernel ...
Department of Computer Science and Engineering
... Linux ( i/ˈlɪnəks/ LIN-uks[5][6] or, less frequently used, /ˈlaɪnəks/ LYN-uks)[6][7] is a Unixlike and mostly POSIX-compliant[8] computer operating system assembled under the model of free and open-source software development and distribution. The defining component of Linux is the Linux kernel,[9] ...
... Linux ( i/ˈlɪnəks/ LIN-uks[5][6] or, less frequently used, /ˈlaɪnəks/ LYN-uks)[6][7] is a Unixlike and mostly POSIX-compliant[8] computer operating system assembled under the model of free and open-source software development and distribution. The defining component of Linux is the Linux kernel,[9] ...
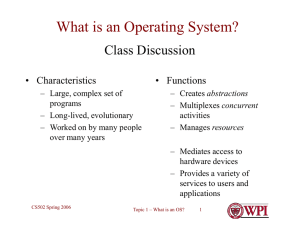
What is an Operating System
... sharing: how are resources shared across users? naming: how are resources named (by users or programs)? security: how is the integrity of the OS and its resources ensured? protection: how is one user/program protected from another? performance: how do we make it all go fast? reliability: what happen ...
... sharing: how are resources shared across users? naming: how are resources named (by users or programs)? security: how is the integrity of the OS and its resources ensured? protection: how is one user/program protected from another? performance: how do we make it all go fast? reliability: what happen ...
PPT - RAMP - University of California, Berkeley
... Previous PPC RAMP-White design used multiple independent operating system images • Pseudo-SMP support in Linux kernel was nontrivial to implement ...
... Previous PPC RAMP-White design used multiple independent operating system images • Pseudo-SMP support in Linux kernel was nontrivial to implement ...
embedded Operating Systems
... “Consumer electronics is a major category where developers are looking to use Linux,” said Stephen Balacco, a Venture Development analyst. The area is high volume and cost-sensitive, so “if you can reduce licensing costs by reducing run-time royalties, you will be more competitive.” A huge coup for ...
... “Consumer electronics is a major category where developers are looking to use Linux,” said Stephen Balacco, a Venture Development analyst. The area is high volume and cost-sensitive, so “if you can reduce licensing costs by reducing run-time royalties, you will be more competitive.” A huge coup for ...
Chapter 2
... mechanism to support program development (1969) • Thompson’s B language (interpreted) used as a language for development (1970) • Ritchie evolved B into C, a compiled language (1971) • UNIX rewritten in C (1973) ...
... mechanism to support program development (1969) • Thompson’s B language (interpreted) used as a language for development (1970) • Ritchie evolved B into C, a compiled language (1971) • UNIX rewritten in C (1973) ...
DOS (“Disk Operating System”)
... • When we type ‘ls’, how does the system know where that command is? – ‘PATH’ variable ...
... • When we type ‘ls’, how does the system know where that command is? – ‘PATH’ variable ...
Heading Goes Here
... verification. The major difficulty with layered approach is careful definition of layers, because a layer can only use the layers below it Less efficient than other approaches ...
... verification. The major difficulty with layered approach is careful definition of layers, because a layer can only use the layers below it Less efficient than other approaches ...
Peter Sirokman
... Since L4Linux is a “complete” operating system, it is representative of microkernel operating systems ...
... Since L4Linux is a “complete” operating system, it is representative of microkernel operating systems ...
Unix History, and Background
... programs to run on different Unix variants. • As long as the operating system uses POSIX compliant mechanisms, it can run software regardless of the actual variant used. • POSIX standard (1003) is administered by IEEE (Institute of Electrical and Electronics Engineers) • The standard is also recogni ...
... programs to run on different Unix variants. • As long as the operating system uses POSIX compliant mechanisms, it can run software regardless of the actual variant used. • POSIX standard (1003) is administered by IEEE (Institute of Electrical and Electronics Engineers) • The standard is also recogni ...
Unit 3 Operation System
... long way from version 1.0 all the way up to the new Vista and soon to be released Windows 7. Although Windows has made strides in regard to security, it has a reputation for being one of the most vulnerable systems. ...
... long way from version 1.0 all the way up to the new Vista and soon to be released Windows 7. Although Windows has made strides in regard to security, it has a reputation for being one of the most vulnerable systems. ...
Linux-Spr-2001-sect-1-group
... •Printers are still very difficult to configure in Linux because they must use generic drivers. Hp sells it’s own distribution of UNIX and does not provide driver support for it’s own printers. •Dell has recently begun selling a computer that comes preconfigured with Linux installed. This is the fir ...
... •Printers are still very difficult to configure in Linux because they must use generic drivers. Hp sells it’s own distribution of UNIX and does not provide driver support for it’s own printers. •Dell has recently begun selling a computer that comes preconfigured with Linux installed. This is the fir ...
Blue Background
... Unlike the official Unix operating system, Linux is distributed freely under GNU General Public Licence (GPL) as specified by the Free Software Foundation. Linux is copyrighted and it is not public domain. However, a GNU Public Licence has much the same effect as being in the public domain. The lice ...
... Unlike the official Unix operating system, Linux is distributed freely under GNU General Public Licence (GPL) as specified by the Free Software Foundation. Linux is copyrighted and it is not public domain. However, a GNU Public Licence has much the same effect as being in the public domain. The lice ...
L03 - UMBC
... (e.g., /afs/umbc.edu/users/j/d/jdoe28/home/). The current directory is where you are located at any time while you are using the system. The / (pronounced “slash”) is the root directory in Linux. Files within the same directory must be given unique ...
... (e.g., /afs/umbc.edu/users/j/d/jdoe28/home/). The current directory is where you are located at any time while you are using the system. The / (pronounced “slash”) is the root directory in Linux. Files within the same directory must be given unique ...
system programs
... based on Unix standards. First developed as a small but self-contained kernel in 1991 by Linus Torvalds, with the major design goal of Unix compatibility. Its history has been one of collaboration by many users from all around the world. ...
... based on Unix standards. First developed as a small but self-contained kernel in 1991 by Linus Torvalds, with the major design goal of Unix compatibility. Its history has been one of collaboration by many users from all around the world. ...
Syllabus - Marwadi University
... Write a shell script to display the digits which are in odd position in a given 5 digit number in Unix / Linux / Ubuntu Write a shell script to read n numbers as command arguments and sort them in descending/ascending order. Write a shell script to check entered string is palindrome or not. Write an ...
... Write a shell script to display the digits which are in odd position in a given 5 digit number in Unix / Linux / Ubuntu Write a shell script to read n numbers as command arguments and sort them in descending/ascending order. Write a shell script to check entered string is palindrome or not. Write an ...
LINUX Virtualization
... execution of special instructions. This allows a virtual machine (and its associated guest operating system) to run until the VMM regains control. Pacifica also amends address translation with host and guest memory management unit (MMU) tables. ...
... execution of special instructions. This allows a virtual machine (and its associated guest operating system) to run until the VMM regains control. Pacifica also amends address translation with host and guest memory management unit (MMU) tables. ...