mac os - WordPress.com
... installations tend to be much less demanding on system resources. In many cases, the old family computer that can barely run Windows is more than sufficient to run the latest version of Linux. Internet Development - Much of the backbone of the Internet is run by UNIX servers. Many of the more gene ...
... installations tend to be much less demanding on system resources. In many cases, the old family computer that can barely run Windows is more than sufficient to run the latest version of Linux. Internet Development - Much of the backbone of the Internet is run by UNIX servers. Many of the more gene ...
Operating Systems History
... • The programs can access directly to some function in superivor mode throught a System ...
... • The programs can access directly to some function in superivor mode throught a System ...
Chapter 2: System Structures
... 4 Many types of resources - Some (such as CPU cycles, main memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code l Accounting - To keep track of which users use how much and what kinds of computer resources l Protection and ...
... 4 Many types of resources - Some (such as CPU cycles, main memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code l Accounting - To keep track of which users use how much and what kinds of computer resources l Protection and ...
Operating Systems Operating Systems Operating Systems
... – It is the first software we see when we turn on the computer, and the last software we see when the computer is turned off. – It's the software that enables all the programs we use. The operating system organizes and controls the hardware on our desks and in our hands, – yet most users can't say w ...
... – It is the first software we see when we turn on the computer, and the last software we see when the computer is turned off. – It's the software that enables all the programs we use. The operating system organizes and controls the hardware on our desks and in our hands, – yet most users can't say w ...
Chapter 2 Operating
... 2.5 Operating-System Design and Implementation The first problem in designing a system is to define goals and specifications. At the highest level, the design of the system will be affected by the choice of hardware and the type of system. Once an operating system is designed, it must be implemented ...
... 2.5 Operating-System Design and Implementation The first problem in designing a system is to define goals and specifications. At the highest level, the design of the system will be affected by the choice of hardware and the type of system. Once an operating system is designed, it must be implemented ...
Operating Systems
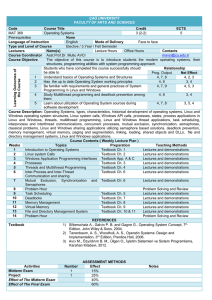
... Office Hours Course Coordinator Asst.Prof.Dr. Mutlu AVCI [email protected] Course Objective The objective of this course is to introduce students the modern operating systems, their structures, programming abilities with system programming approach. Relationship Students who have completed the course ...
... Office Hours Course Coordinator Asst.Prof.Dr. Mutlu AVCI [email protected] Course Objective The objective of this course is to introduce students the modern operating systems, their structures, programming abilities with system programming approach. Relationship Students who have completed the course ...
Slides
... – fetches a command from user and executes it • Command may be built-in, • Command may be another program • GUI: User-friendly desktop interface – Icons represent files, programs, actions, etc. Many operating systems now include both CLI and GUI interfaces Linux: command shells available (CLI); KDE ...
... – fetches a command from user and executes it • Command may be built-in, • Command may be another program • GUI: User-friendly desktop interface – Icons represent files, programs, actions, etc. Many operating systems now include both CLI and GUI interfaces Linux: command shells available (CLI); KDE ...
(OS) license terms do not permit multiple users to access
... What if a Volume Licensing customer purchases new devices that do not have an operating system preinstalled (“naked” PCs)? Customers’ options for acquiring full licenses for the Windows operating system are through the OEM channel, the retail/FPP channel or through Volume Licensing (upgrade). If a c ...
... What if a Volume Licensing customer purchases new devices that do not have an operating system preinstalled (“naked” PCs)? Customers’ options for acquiring full licenses for the Windows operating system are through the OEM channel, the retail/FPP channel or through Volume Licensing (upgrade). If a c ...
System Software - California State University, Fresno
... Mac OS – First introduced in 1984 – One of the 1st GUI’s, making it easy even for a novice – Designed to run with Apple – Not as widely used; not as many application programs – Considered to be one of the innovative operating systems – Popular with professional graphics artists – Latest Release: Mac ...
... Mac OS – First introduced in 1984 – One of the 1st GUI’s, making it easy even for a novice – Designed to run with Apple – Not as widely used; not as many application programs – Considered to be one of the innovative operating systems – Popular with professional graphics artists – Latest Release: Mac ...
chapter4
... • Command-driven DOS—short for Disk Operating System—was very popular in the 1980s and early 1990s and runs primarily on PCs (IBM and IBMcompatible). IBM's version of DOS is called PCDOS and Microsoft's version of DOS is called MS-DOS. Both were developed by Microsoft, and they are essentially the s ...
... • Command-driven DOS—short for Disk Operating System—was very popular in the 1980s and early 1990s and runs primarily on PCs (IBM and IBMcompatible). IBM's version of DOS is called PCDOS and Microsoft's version of DOS is called MS-DOS. Both were developed by Microsoft, and they are essentially the s ...
OPERATING SYSTEMS:
... and others from malicious or ignorant users. The User/Supervisor Mode and privileged instructions. Concurrent threads might interfere with others. This leads to protection of resources by user/supervisor mode. These resources include: I/O Define I/O instructions as privileged; they can be executed o ...
... and others from malicious or ignorant users. The User/Supervisor Mode and privileged instructions. Concurrent threads might interfere with others. This leads to protection of resources by user/supervisor mode. These resources include: I/O Define I/O instructions as privileged; they can be executed o ...
Multitasking (Time sharing)
... sharing systems, the CPU executes multiple jobs by switching among them, but the switches occur so frequently that the users can interact with each program while its running. Time sharing requires an interactive or (hands on) computer system, which provides direct communication between the user and ...
... sharing systems, the CPU executes multiple jobs by switching among them, but the switches occur so frequently that the users can interact with each program while its running. Time sharing requires an interactive or (hands on) computer system, which provides direct communication between the user and ...
lec01
... Approached Bill Gates to see if he can build one Gates approached Seattle computer products, bought 86DOS and created MS-DOS Goal: finish quickly and run existing CP/M software OS becomes subroutine library and command executive ...
... Approached Bill Gates to see if he can build one Gates approached Seattle computer products, bought 86DOS and created MS-DOS Goal: finish quickly and run existing CP/M software OS becomes subroutine library and command executive ...
Introduction
... 1.1 What is an operating system 1.2 History of operating systems 1.3 The operating system zoo 1.4 Computer hardware review 1.5 Operating system concepts 1.6 System calls 1.7 Operating system structure ...
... 1.1 What is an operating system 1.2 History of operating systems 1.3 The operating system zoo 1.4 Computer hardware review 1.5 Operating system concepts 1.6 System calls 1.7 Operating system structure ...
Operating System Structures
... The system call interface invokes intended system call in OS kernel and returns status of the system call and any return values • The caller need know nothing about how the system call is implemented ...
... The system call interface invokes intended system call in OS kernel and returns status of the system call and any return values • The caller need know nothing about how the system call is implemented ...
lec01 - CSE @ UCR
... In the unix paper, they are defending this decision! However, this is a new and important advance: portable operating systems! ...
... In the unix paper, they are defending this decision! However, this is a new and important advance: portable operating systems! ...
CS 153 Design of Operating Systems
... In the unix paper, they are defending this decision! However, this is a new and important advance: portable operating systems! ...
... In the unix paper, they are defending this decision! However, this is a new and important advance: portable operating systems! ...
AutoPod: Unscheduled System Updates with Zero Data Loss
... attacks commonplace in today’s networks. Security problems can wreak havoc on an organization’s computing infrastructure. To prevent this, software vendors frequently release patches that can be applied to address security and maintenance issues that have been discovered. This provides a management ...
... attacks commonplace in today’s networks. Security problems can wreak havoc on an organization’s computing infrastructure. To prevent this, software vendors frequently release patches that can be applied to address security and maintenance issues that have been discovered. This provides a management ...
Introduction to OS - faculty.cs.tamu.edu
... Time Sharing (mid 1960s on)! •! OS interleaves execution of multiple user programs with time quantum! –! CTSS (1961): time quantum 0.2 sec! •! User returns to own the machine! •! New aspects and issues:! –! On-line file systems! –! resource protection! –! virtual memory! –! sophisticated process sch ...
... Time Sharing (mid 1960s on)! •! OS interleaves execution of multiple user programs with time quantum! –! CTSS (1961): time quantum 0.2 sec! •! User returns to own the machine! •! New aspects and issues:! –! On-line file systems! –! resource protection! –! virtual memory! –! sophisticated process sch ...
Lect03
... OS for time-sharing o To accommodate multiple real-time users, the OS rotates its various jobs in and out of execution via time-sharing o Each job gets a predetermined “time slice” o At end of time slice current job is set aside and a new one starts o By rapidly shuffling jobs, illusion of several j ...
... OS for time-sharing o To accommodate multiple real-time users, the OS rotates its various jobs in and out of execution via time-sharing o Each job gets a predetermined “time slice” o At end of time slice current job is set aside and a new one starts o By rapidly shuffling jobs, illusion of several j ...
Summary for chapter 2 OPERATING SYSTEM nAJWA kNEFATI
... The first GUI appeared on the Xerox Alto computer in 1973. The advent of Apple Macintosh computers in the 1980s. the Aqua interface that appeared with Mac OS X. Microsoft’s first version of Windows—Version 1.0—was based on the addition of a GUI interface to the MS-DOS OS. Cosmetic changes ...
... The first GUI appeared on the Xerox Alto computer in 1973. The advent of Apple Macintosh computers in the 1980s. the Aqua interface that appeared with Mac OS X. Microsoft’s first version of Windows—Version 1.0—was based on the addition of a GUI interface to the MS-DOS OS. Cosmetic changes ...
Chapter 04 - Regis University: Academic Web Server for Faculty
... Each piece can have its own access rights. A segment has a name and an offset value. Usually one OS segment address table per ...
... Each piece can have its own access rights. A segment has a name and an offset value. Usually one OS segment address table per ...
File
... layer (layer 0), is the hardware; the highest (layer N) is the user interface. With modularity, layers are selected such that each uses functions (operations) and services of only lower-level ...
... layer (layer 0), is the hardware; the highest (layer N) is the user interface. With modularity, layers are selected such that each uses functions (operations) and services of only lower-level ...
Web-Based Operating Systems
... Adobe Flash and Asynchronous JavaScript and XML (AJAX). AJAX- Highly touted by Google (Calendar & Gmail services) Flash – More than 98% of all machines connected to internet have a flash player installed. -Jonathan Strickland The widespread familiarity with these technologies is one of the primary r ...
... Adobe Flash and Asynchronous JavaScript and XML (AJAX). AJAX- Highly touted by Google (Calendar & Gmail services) Flash – More than 98% of all machines connected to internet have a flash player installed. -Jonathan Strickland The widespread familiarity with these technologies is one of the primary r ...