Learning Markov Networks With Arithmetic Circuits
... in general [25]. Learning MN parameters and structure is also intractable in the general case, since computing the gradient of the log-likelihood requires running inference in the model. As a result, most applications of MNs use approximate methods for learning and inference. For example, parameter ...
... in general [25]. Learning MN parameters and structure is also intractable in the general case, since computing the gradient of the log-likelihood requires running inference in the model. As a result, most applications of MNs use approximate methods for learning and inference. For example, parameter ...
Artificial Intelligence and Machine Learning: Policy
... amounts of data into information and services, based on certain instructions and rules. It’s an important concept to understand, because in machine learning, learning algorithms – not computer programmers– create the rules. Instead of programming the computer every step of the way, this approach giv ...
... amounts of data into information and services, based on certain instructions and rules. It’s an important concept to understand, because in machine learning, learning algorithms – not computer programmers– create the rules. Instead of programming the computer every step of the way, this approach giv ...
Professional identity as learning processes in life histories
... subjective development phenomena are mostly not accounted for - or if they are: then in entirely psychological concepts, which do not conceptually integrate societal contextual factors - here especially work. The basic theoretical problem is to establish a theoretical understanding of two separate y ...
... subjective development phenomena are mostly not accounted for - or if they are: then in entirely psychological concepts, which do not conceptually integrate societal contextual factors - here especially work. The basic theoretical problem is to establish a theoretical understanding of two separate y ...
21st Century Learning: Research, Innovation and Policy
... individual learners may be highly beneficial in order to find out such matters as whether a student really does comprehend certain material, or about their levels of motivation or anxiety. Used properly, this individual focus may add fundamentally powerful diagnostic tools to the process of formativ ...
... individual learners may be highly beneficial in order to find out such matters as whether a student really does comprehend certain material, or about their levels of motivation or anxiety. Used properly, this individual focus may add fundamentally powerful diagnostic tools to the process of formativ ...
Specific nonlinear models
... Applications of deep learning Lately, deep learning has lead to superior classification results in challenging areas The main scheme is as follows: 1. use unsupervised learning from many unlabeled examples to prepare the deep network in an initial state; 2. use back propagation only for the final t ...
... Applications of deep learning Lately, deep learning has lead to superior classification results in challenging areas The main scheme is as follows: 1. use unsupervised learning from many unlabeled examples to prepare the deep network in an initial state; 2. use back propagation only for the final t ...
LIONway-slides-chapter9
... Applications of deep learning Lately, deep learning has lead to superior classification results in challenging areas The main scheme is as follows: 1. use unsupervised learning from many unlabeled examples to prepare the deep network in an initial state; 2. use back propagation only for the final t ...
... Applications of deep learning Lately, deep learning has lead to superior classification results in challenging areas The main scheme is as follows: 1. use unsupervised learning from many unlabeled examples to prepare the deep network in an initial state; 2. use back propagation only for the final t ...
The cerebellum chip: an analog VLSI implementation of a
... threshold is reached. Thereby, the correct timing of CRs results from the adaptation of a pause in PU spiking following the CS. In summary, in the model the expression of a CR is triggered by DN rebound excitation upon release from PU inhibition. The precise timing of a CR is dependent on the durati ...
... threshold is reached. Thereby, the correct timing of CRs results from the adaptation of a pause in PU spiking following the CS. In summary, in the model the expression of a CR is triggered by DN rebound excitation upon release from PU inhibition. The precise timing of a CR is dependent on the durati ...
Suggested Readings
... approach to the dissertation and contributions towards the MSc dissertation itself. The dissertation style will be a technical scoping and proof of concept study and not involve human participants in experimentation. Appendix A summarises a study of relevant assessment methods and its conclusions. A ...
... approach to the dissertation and contributions towards the MSc dissertation itself. The dissertation style will be a technical scoping and proof of concept study and not involve human participants in experimentation. Appendix A summarises a study of relevant assessment methods and its conclusions. A ...
MindTools - IHMC Public Cmaps
... Expert Systems. Expert systems have evolved from research in the field of artificial intelligence. An expert system is a computer program that simulates the way human experts solve problems, tha is, an artificial decision maker. They are computer-based tools that are designed to function as intelli ...
... Expert Systems. Expert systems have evolved from research in the field of artificial intelligence. An expert system is a computer program that simulates the way human experts solve problems, tha is, an artificial decision maker. They are computer-based tools that are designed to function as intelli ...
ppt - Computer Science Department
... automatically detect patterns in data, and then to use the uncovered patterns to predict future data or other outcomes of interest. -- Kevin P. Murphy The field of pattern recognition is concerned with the automatic discovery of regularities in data through the use of computer algorithms and with th ...
... automatically detect patterns in data, and then to use the uncovered patterns to predict future data or other outcomes of interest. -- Kevin P. Murphy The field of pattern recognition is concerned with the automatic discovery of regularities in data through the use of computer algorithms and with th ...
Imants Freibergs, Serge-André Mahé, Alain Lacheny, Jean
... The new paradigm of "knowledge construction using experiential based and collaborative learning approaches" is an outstanding opportunity for interdisciplinary research. This document is an attempt to introduce and exemplify as much as possible using the lexicon of "social sciences", considerations ...
... The new paradigm of "knowledge construction using experiential based and collaborative learning approaches" is an outstanding opportunity for interdisciplinary research. This document is an attempt to introduce and exemplify as much as possible using the lexicon of "social sciences", considerations ...
Behavioral Learning Theory: Pavlov and Piaget - UHS-CD3
... salivary conditioning of Pavlov's dogs. During his research on the physiology of digestion in dogs, Pavlov noticed that, rather than simply salivating in the presence of meat powder, the dogs began to salivate in the presence of the lab technician who normally fed them. Pavlov called these psychic s ...
... salivary conditioning of Pavlov's dogs. During his research on the physiology of digestion in dogs, Pavlov noticed that, rather than simply salivating in the presence of meat powder, the dogs began to salivate in the presence of the lab technician who normally fed them. Pavlov called these psychic s ...
View PDF - Advances in Cognitive Systems
... Although such agents produce intelligent behavior with less human knowledge engineering than before, there remains a non-trivial element of knowledge engineering in the encoding of the prior domain knowledge. Such prior knowledge includes encoding how to extract a coefficient from an expression, how ...
... Although such agents produce intelligent behavior with less human knowledge engineering than before, there remains a non-trivial element of knowledge engineering in the encoding of the prior domain knowledge. Such prior knowledge includes encoding how to extract a coefficient from an expression, how ...
Learning multiple layers of representation
... Department of Computer Science, University of Toronto, 10 King’s College Road, Toronto, M5S 3G4, Canada ...
... Department of Computer Science, University of Toronto, 10 King’s College Road, Toronto, M5S 3G4, Canada ...
The Schizophrenic Brain: A Broken Hermeneutic
... Gallagher’s analysis implies: (i) Hermeneutics and cognitive science is in agreement on a number of things. An example is the way we know objects. The interpretation of objects needs ”schema theory” (a modern version is given by Michael Arbib [22]); (ii) Hermeneutics can contribute to cognitive scie ...
... Gallagher’s analysis implies: (i) Hermeneutics and cognitive science is in agreement on a number of things. An example is the way we know objects. The interpretation of objects needs ”schema theory” (a modern version is given by Michael Arbib [22]); (ii) Hermeneutics can contribute to cognitive scie ...
Hypernetworks: A Molecular Evolutionary Architecture for Cognitive
... learning methods are algorithms to search for similarities between objects. Supervised learning methods, especially classification algorithms, try to maximize the contrast between the classes. Contiguity, especially temporal contiguity, is not exploited in machine learning, except where some aspects ...
... learning methods are algorithms to search for similarities between objects. Supervised learning methods, especially classification algorithms, try to maximize the contrast between the classes. Contiguity, especially temporal contiguity, is not exploited in machine learning, except where some aspects ...
stairs 2012 - Shiwali Mohan
... monster from Mario, speed of the monster and its type as attributes. Mohan and Laird also used a similar representation in their solution for the Infinite Mario domain in [10]. However, including all objects in the visual scene as a part of the state will result in a large state table. As an extens ...
... monster from Mario, speed of the monster and its type as attributes. Mohan and Laird also used a similar representation in their solution for the Infinite Mario domain in [10]. However, including all objects in the visual scene as a part of the state will result in a large state table. As an extens ...
Introduction to Computational Intelligence Business
... The definition of what characterizes a business application is not entirely uniform throughout the CI literature. The root of the misconceptions are often in the interpretation of the concept of business, a word sometimes abused of and with many different singular translations from English depending o ...
... The definition of what characterizes a business application is not entirely uniform throughout the CI literature. The root of the misconceptions are often in the interpretation of the concept of business, a word sometimes abused of and with many different singular translations from English depending o ...
Q1 - shoaib ahmed jatoi
... is a document in which the information you require is represented as alphanumeric symbols printed on paper" we might just say "Here is the information you require". Quite a few other words can be used as synonyms for information. It is sometimes called content, substance, message, or even (with some ...
... is a document in which the information you require is represented as alphanumeric symbols printed on paper" we might just say "Here is the information you require". Quite a few other words can be used as synonyms for information. It is sometimes called content, substance, message, or even (with some ...
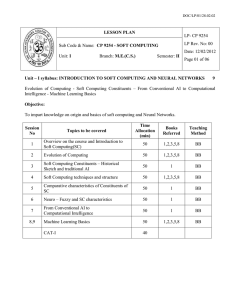
lesson plan
... Introduction to Genetic Algorithms (GA) – Applications of GA in Machine Learning – Machine Learning Approach to Knowledge Acquisition. Objective : To impart knowledge on genetic algorithms and their applications. ...
... Introduction to Genetic Algorithms (GA) – Applications of GA in Machine Learning – Machine Learning Approach to Knowledge Acquisition. Objective : To impart knowledge on genetic algorithms and their applications. ...
Theoretical Foundations for Intelligent Tutoring Systems
... entirely discursive and attempt no kind of formalisation of their content. The aim of this paper is to suggest that it is not premature for ITS research to begin an attempt to complement a short-term emphasis on pragmatic aspects (Kearsley, 1989) by seeking theoretical foundations for its implementa ...
... entirely discursive and attempt no kind of formalisation of their content. The aim of this paper is to suggest that it is not premature for ITS research to begin an attempt to complement a short-term emphasis on pragmatic aspects (Kearsley, 1989) by seeking theoretical foundations for its implementa ...
d - Fizyka UMK
... information compression, or algorithmic complexity. In computing: minimum length (message, description) encoding. Wolff (2006): all cognition and computation is information compression! Analysis and production of natural language, fuzzy pattern recognition, probabilistic reasoning and unsupervised i ...
... information compression, or algorithmic complexity. In computing: minimum length (message, description) encoding. Wolff (2006): all cognition and computation is information compression! Analysis and production of natural language, fuzzy pattern recognition, probabilistic reasoning and unsupervised i ...
Universal Design for Learning - MERLOT International Conference
... To find initial training for key individuals, go to • AccessIT: Introduction to Accessible Information Technology in Education (http://access-it-online.info/public/welcome.asp) • Bridging the Gap through Universal Design for Learning--A 6-week online course which will provide an introduction to the ...
... To find initial training for key individuals, go to • AccessIT: Introduction to Accessible Information Technology in Education (http://access-it-online.info/public/welcome.asp) • Bridging the Gap through Universal Design for Learning--A 6-week online course which will provide an introduction to the ...
Studiefiche - studiegids UGent
... 11 Compare and contrast basic search issues with game playing issues. [Familiarity] 12 Translate a natural language (e.g.,English) sentence into predicate logic statement. 1 [Usage] 13 Convert a logic statement into clause form. [Usage] 14 Apply resolution to a set of logic statements to answer ...
... 11 Compare and contrast basic search issues with game playing issues. [Familiarity] 12 Translate a natural language (e.g.,English) sentence into predicate logic statement. 1 [Usage] 13 Convert a logic statement into clause form. [Usage] 14 Apply resolution to a set of logic statements to answer ...
slides
... • The AER communication protocol emulates massive connectivity between cells by time-multiplexing many connections on the same data bus. • For a one-to-one connection topology, the required number of wires is reduced from N to ∼ log2 N . • Each spike is represented by: ◦ Its location: explicitly enc ...
... • The AER communication protocol emulates massive connectivity between cells by time-multiplexing many connections on the same data bus. • For a one-to-one connection topology, the required number of wires is reduced from N to ∼ log2 N . • Each spike is represented by: ◦ Its location: explicitly enc ...