glossary - Cengage
... in which the data in the database is in compliance with all entity and referential integrity constraints. data management—A process that focuses on data collection, storage, and retrieval. Common data management functions include addition, deletion, modification, and listing. data manager (DM)—See d ...
... in which the data in the database is in compliance with all entity and referential integrity constraints. data management—A process that focuses on data collection, storage, and retrieval. Common data management functions include addition, deletion, modification, and listing. data manager (DM)—See d ...
Chapter 5 Preliminaries on Semiparametric Theory and Missing Data Problem
... variates, V , are available, then, they can be used as a surrogate variables in order to gain efficiency. The methodology is also developed for longitudinal data and is presented under a monotone missing data pattern. However, some extensions to arbitrary missing data patterns are also studied. In p ...
... variates, V , are available, then, they can be used as a surrogate variables in order to gain efficiency. The methodology is also developed for longitudinal data and is presented under a monotone missing data pattern. However, some extensions to arbitrary missing data patterns are also studied. In p ...
Search for Scalar Top Quark Partners and Parton Shower Tuning in
... To start with, I would like to express my gratitude towards Prof. Dirk Ryckbosch for his efforts into bringing me towards the point where I finalise my studies. Five years ago, when I was unsure whether physics was a good fit for me, he told me that all it takes is a decent dose of enthusiasm and mo ...
... To start with, I would like to express my gratitude towards Prof. Dirk Ryckbosch for his efforts into bringing me towards the point where I finalise my studies. Five years ago, when I was unsure whether physics was a good fit for me, he told me that all it takes is a decent dose of enthusiasm and mo ...
seislog_manual_8.44.pdf
... hard disk and the type of recording you want to do, you may specify a number of files of a specified size to make up the total ringbuffer scheme. Each file in the ringbuffer has the same format as an ordinary event and can then be treated as such except that is does not have a detection number. This ...
... hard disk and the type of recording you want to do, you may specify a number of files of a specified size to make up the total ringbuffer scheme. Each file in the ringbuffer has the same format as an ordinary event and can then be treated as such except that is does not have a detection number. This ...
IDM Workshop Template
... The central goal of this project is to assist researchers and developers in building query optimizers that are "provably correct". Specifically, this research group is building a framework which accepts specifications of optimizer components and their interactions, and generates optimizers that can ...
... The central goal of this project is to assist researchers and developers in building query optimizers that are "provably correct". Specifically, this research group is building a framework which accepts specifications of optimizer components and their interactions, and generates optimizers that can ...
Measurement of lifetime for muons captured inside nuclei
... 1. Analyze the ADC VS. TDC profile. 2. Comparing the probability of compatibility between two ADC distribution. 3. Making different ADC cut and analyze the TDC data for each ADC cut. ...
... 1. Analyze the ADC VS. TDC profile. 2. Comparing the probability of compatibility between two ADC distribution. 3. Making different ADC cut and analyze the TDC data for each ADC cut. ...
PPTX - ARIN
... • Uses a URL containing 3 parts: – The address (you’re used to this one) – The method (a basic instruction to the server that tells it what you want to do) – A resource identifier (basic information about the record (resource) you want to affect ...
... • Uses a URL containing 3 parts: – The address (you’re used to this one) – The method (a basic instruction to the server that tells it what you want to do) – A resource identifier (basic information about the record (resource) you want to affect ...
Materialized View
... use a dynamic lookup cache, you can only use the equality operator in the lookup condition. NewLookupRow port will enable automatically. Best example where we need to use dynamic If we use static lookup first record it will go to cache is if suppose first record and last record lookup and check in t ...
... use a dynamic lookup cache, you can only use the equality operator in the lookup condition. NewLookupRow port will enable automatically. Best example where we need to use dynamic If we use static lookup first record it will go to cache is if suppose first record and last record lookup and check in t ...
annual report - Center for Experimental Nuclear Physics and
... with the slow controls system. With the delivery by our colleagues at Karlsruhe Institute of Technology (KIT) of the complete analog readout electronics, commissioning of the electronics system and characterization of the detectors are almost complete. This work was carried out using the latest Mark ...
... with the slow controls system. With the delivery by our colleagues at Karlsruhe Institute of Technology (KIT) of the complete analog readout electronics, commissioning of the electronics system and characterization of the detectors are almost complete. This work was carried out using the latest Mark ...
Lec. notes
... • ER design is subjective. There are often many ways to model a given scenario! Analyzing alternatives can be tricky, especially for a large enterprise. Common choices include: • Entity vs. attribute, entity vs. relationship, binary or nary relationship, whether or not to use ISA hierarchies • Ensur ...
... • ER design is subjective. There are often many ways to model a given scenario! Analyzing alternatives can be tricky, especially for a large enterprise. Common choices include: • Entity vs. attribute, entity vs. relationship, binary or nary relationship, whether or not to use ISA hierarchies • Ensur ...
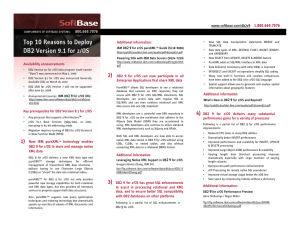
Top 10 Reasons to Deploy DB2 Version 9.1 for z/OS
... privileges by roles rather than groups or users simplifies DB2 9 for z/OS security administration. DB2 9 for z/OS also adds a trusted security feature that lets you define trusted connections (DDF, RRS, and DSN) to the DBMS. By regulating authorized connections to DB2 for z/OS, overall enterprise se ...
... privileges by roles rather than groups or users simplifies DB2 9 for z/OS security administration. DB2 9 for z/OS also adds a trusted security feature that lets you define trusted connections (DDF, RRS, and DSN) to the DBMS. By regulating authorized connections to DB2 for z/OS, overall enterprise se ...
SAND CDBMS
... SAND CDBMS does this without imposing the usual price of administrative complexity. The benefits of this simplified administration are manifest in a number of areas. First, SAND CDBMS takes responsibility for the details of storage out of the hands of the user, allowing completely free-form data man ...
... SAND CDBMS does this without imposing the usual price of administrative complexity. The benefits of this simplified administration are manifest in a number of areas. First, SAND CDBMS takes responsibility for the details of storage out of the hands of the user, allowing completely free-form data man ...
Selecting the Best Curve Fit in SoftMax Pro 7 Software | Molecular
... number of parameter describing the curve. As sample size increases, the last term of the AICc approaches zero and the AICc tends to yield the same conclusions as the AIC5. The AIC and AICc take into account both the statistical goodness of the fit and the number of parameters that have to be estimat ...
... number of parameter describing the curve. As sample size increases, the last term of the AICc approaches zero and the AICc tends to yield the same conclusions as the AIC5. The AIC and AICc take into account both the statistical goodness of the fit and the number of parameters that have to be estimat ...
figure 6-2 - JSNE Group
... • Many problems solved using recursive algorithms • Choosing between recursion and iteration – Nature of solution; efficiency requirements ...
... • Many problems solved using recursive algorithms • Choosing between recursion and iteration – Nature of solution; efficiency requirements ...
DEVQ101-06 - Atlanta.mdf
... A future release of Microsoft® SQL Server™ may modify the behavior of the Transact-SQL timestamp data type to align it with the behavior defined in the standard. At that time, the current timestamp data type will be replaced with a rowversion data type. Microsoft® SQL Server™ 2000 introduces a rowve ...
... A future release of Microsoft® SQL Server™ may modify the behavior of the Transact-SQL timestamp data type to align it with the behavior defined in the standard. At that time, the current timestamp data type will be replaced with a rowversion data type. Microsoft® SQL Server™ 2000 introduces a rowve ...
Presentation - College of Engineering
... • Best “k” servers are chosen as the source servers. Similarly best destination server is chosen • All selections are subjected to reliability constraints. E.g. chunks of the same stripe should be in separate failure domains/update domains. ...
... • Best “k” servers are chosen as the source servers. Similarly best destination server is chosen • All selections are subjected to reliability constraints. E.g. chunks of the same stripe should be in separate failure domains/update domains. ...
SC PE
... Files • Files are the common containers for user data, application code, and operating system executables and parameters. • A file includes data and control information – Data is information that has been converted to a machine-readable, digital binary format. – Control information indicates how da ...
... Files • Files are the common containers for user data, application code, and operating system executables and parameters. • A file includes data and control information – Data is information that has been converted to a machine-readable, digital binary format. – Control information indicates how da ...
cdc epilepsy quality of care study
... 17.1 How old was patient at diagnosis? 17.2 What is the date when the patient was diagnosed? 17.3 How long ago was diagnosis made? 17.4 What is the date of patient’s enrollment at BMC? ...
... 17.1 How old was patient at diagnosis? 17.2 What is the date when the patient was diagnosed? 17.3 How long ago was diagnosis made? 17.4 What is the date of patient’s enrollment at BMC? ...
ACC - Access Denied!
... various intervals throughout COI lifecycle activities to ensure user requirements are adequately addressed. The chartering process may be a mechanism to solicit the appropriate membership at all levels, as needed. COIs can exhibit a diverse range of characteristics depending on the community’s missi ...
... various intervals throughout COI lifecycle activities to ensure user requirements are adequately addressed. The chartering process may be a mechanism to solicit the appropriate membership at all levels, as needed. COIs can exhibit a diverse range of characteristics depending on the community’s missi ...
Applied Statistics : Practical 11
... > spplot(meuse,'zinc',do.log=TRUE) > bubble(meuse,'zinc',do.log=TRUE) Can you interpret the output of this plot? (Check the help if needed) In these plots, each data point is associated to an interval of zinc quantity and the coding is based either on color (spplot) ...
... > spplot(meuse,'zinc',do.log=TRUE) > bubble(meuse,'zinc',do.log=TRUE) Can you interpret the output of this plot? (Check the help if needed) In these plots, each data point is associated to an interval of zinc quantity and the coding is based either on color (spplot) ...
lin - Carnegie Mellon School of Computer Science
... of a chord overlap with the composition notes of another chord. So, it is sometimes difficult to discern what the correct chord is. This problem is different than the problems that other researchers over the years have challenged. Here, we are trying to find the general sounding chord in polyphonic ...
... of a chord overlap with the composition notes of another chord. So, it is sometimes difficult to discern what the correct chord is. This problem is different than the problems that other researchers over the years have challenged. Here, we are trying to find the general sounding chord in polyphonic ...
Data analysis

Analysis of data is a process of inspecting, cleaning, transforming, and modeling data with the goal of discovering useful information, suggesting conclusions, and supporting decision-making. Data analysis has multiple facets and approaches, encompassing diverse techniques under a variety of names, in different business, science, and social science domains.Data mining is a particular data analysis technique that focuses on modeling and knowledge discovery for predictive rather than purely descriptive purposes. Business intelligence covers data analysis that relies heavily on aggregation, focusing on business information. In statistical applications, some people divide data analysis into descriptive statistics, exploratory data analysis (EDA), and confirmatory data analysis (CDA). EDA focuses on discovering new features in the data and CDA on confirming or falsifying existing hypotheses. Predictive analytics focuses on application of statistical models for predictive forecasting or classification, while text analytics applies statistical, linguistic, and structural techniques to extract and classify information from textual sources, a species of unstructured data. All are varieties of data analysis.Data integration is a precursor to data analysis, and data analysis is closely linked to data visualization and data dissemination. The term data analysis is sometimes used as a synonym for data modeling.