integrated security in cloud computing environment
... Internet by hackers and cybercriminals needs to be addressed and cloud computing environment needs to secure and private for clients [10]. We will deal with few security factors that mainly affect clouds, such as data intrusion and data integrity. Cachin et al. [11] represents that when multiple res ...
... Internet by hackers and cybercriminals needs to be addressed and cloud computing environment needs to secure and private for clients [10]. We will deal with few security factors that mainly affect clouds, such as data intrusion and data integrity. Cachin et al. [11] represents that when multiple res ...
A Graph-based Approach to Vehicle Trajectory Analysis Diansheng
... distance (straight line) and following representative points. A Delaunay Triangulation (DT) is constructed for the extracted representative points. For each trajectory segment, let A and B be its starting and ending points (both are representative points), the interpolation algorithm will find the s ...
... distance (straight line) and following representative points. A Delaunay Triangulation (DT) is constructed for the extracted representative points. For each trajectory segment, let A and B be its starting and ending points (both are representative points), the interpolation algorithm will find the s ...
WFPC-2 Shutter-A Position Sensing Error Fault Isolation
... The message content of 0688066816 indicated that both shutter blades reported their position as "closed" during the pre-move check at Real-Time Interrupt (RTI) 1640i. The shutter's mechanical design makes it impossible for both blades to actually be in the closed position. The instrument recognized ...
... The message content of 0688066816 indicated that both shutter blades reported their position as "closed" during the pre-move check at Real-Time Interrupt (RTI) 1640i. The shutter's mechanical design makes it impossible for both blades to actually be in the closed position. The instrument recognized ...
CMG-DM24 - Ocean Networks Canada
... data immediately. You can now start configuring it for your own needs. There are two ways you can do this: ...
... data immediately. You can now start configuring it for your own needs. There are two ways you can do this: ...
BUSINESS ANALYTICS YEARBOOK
... optimization, business intelligence, and in fact any technology which reduces the uncertainty involved in decision making, and increases decision making efficiency. The traditional business use of information technology can be seen as an extension of the filing cabinet and desktop calculator. Comput ...
... optimization, business intelligence, and in fact any technology which reduces the uncertainty involved in decision making, and increases decision making efficiency. The traditional business use of information technology can be seen as an extension of the filing cabinet and desktop calculator. Comput ...
Fluctuations of kinematic quantities in p+p interactions at the CERN
... New method of correcting results on fluctuations for experimental and physics biases was introduced. Uncorrected ΦpT results for p+p collisions at beam momenta: 20, 31, 40, 80, 158 GeV/c were presented. Soon corrected results will be shown. Two-particle correlations in azimuthal angle and pseudo-rap ...
... New method of correcting results on fluctuations for experimental and physics biases was introduced. Uncorrected ΦpT results for p+p collisions at beam momenta: 20, 31, 40, 80, 158 GeV/c were presented. Soon corrected results will be shown. Two-particle correlations in azimuthal angle and pseudo-rap ...
Single diffractive hadron-nucleus interactions within the dual parton
... In order to compare the predictions given by the model with the data [15] we count only such diffractive interactions in which the projectile hadron remains intact and the involved target nucleon is excited diffractively. The treatment of the chains fragmenting into the diffractive final state is id ...
... In order to compare the predictions given by the model with the data [15] we count only such diffractive interactions in which the projectile hadron remains intact and the involved target nucleon is excited diffractively. The treatment of the chains fragmenting into the diffractive final state is id ...
system-, load-file-, procedure-, and instruction
... During program updates, sample data must be ignored Program counter samples must be interpreted • Intermediate representation contains CFG information • PC samples are scaled for basic block size • Aggregate basic block execution profile is created Morph ...
... During program updates, sample data must be ignored Program counter samples must be interpreted • Intermediate representation contains CFG information • PC samples are scaled for basic block size • Aggregate basic block execution profile is created Morph ...
DEVELOPMENT OF ABRAHAM MODEL CORRELATIONS FOR
... the manufacture of new chemical materials and pharmaceutical products. For newly synthesized compounds, supply is often very limited and there is not always sufficient material to measure the compound’s solubility in every solvent of possible interest. To address this concern, researchers have turne ...
... the manufacture of new chemical materials and pharmaceutical products. For newly synthesized compounds, supply is often very limited and there is not always sufficient material to measure the compound’s solubility in every solvent of possible interest. To address this concern, researchers have turne ...
Computer Network (NEW)hot!
... communication channels that allow sharing of resources and information. Where at least one process in one device is able to send/receive data to/from at least one process residing in a remote device, then the two devices are said to be in a network. Simply, more than one computer interconnected thro ...
... communication channels that allow sharing of resources and information. Where at least one process in one device is able to send/receive data to/from at least one process residing in a remote device, then the two devices are said to be in a network. Simply, more than one computer interconnected thro ...
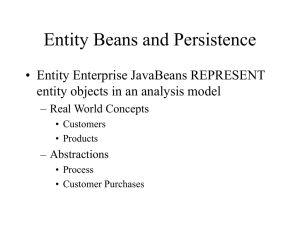
Chapter 20: Entity Beans and Persistence
... bean that it must invalidate the current cached state and prepare for business method invocations – Practically, this mean replacing the state by loading it from the database • For this you'll need the PK – by the time that ejbLoad() is called, the PK is associated with the entity and is available f ...
... bean that it must invalidate the current cached state and prepare for business method invocations – Practically, this mean replacing the state by loading it from the database • For this you'll need the PK – by the time that ejbLoad() is called, the PK is associated with the entity and is available f ...
Spatial Database for Geographic Information System (GIS
... functions that facilitate the storage, retrieval, update, and query of collections of spatial features in an Oracle database. Spatial consists of the following[3]: • A schema (MDSYS) that prescribes the storage, syntax, and semantics of supported geometric data types • A spatial indexing mechanism • ...
... functions that facilitate the storage, retrieval, update, and query of collections of spatial features in an Oracle database. Spatial consists of the following[3]: • A schema (MDSYS) that prescribes the storage, syntax, and semantics of supported geometric data types • A spatial indexing mechanism • ...
Privacy Law`s Midlife Crisis: A Critical
... First, the second generation fails to update the definition of personal data,1 the fundamental building block of the framework. Recent advances in reidentification science have shown the futility of traditional de-identification techniques in a big data ecosystem. Consequently, the scope of the fram ...
... First, the second generation fails to update the definition of personal data,1 the fundamental building block of the framework. Recent advances in reidentification science have shown the futility of traditional de-identification techniques in a big data ecosystem. Consequently, the scope of the fram ...
K1B2816BAA
... The world is moving into the mobile multi-media era and therefore the mobile handsets need bigger & faster memory capacity to handle the multi-media data. SAMSUNG’s UtRAM products are designed to meet all the request from the various customers who want to cope with the fast growing mobile market. Ut ...
... The world is moving into the mobile multi-media era and therefore the mobile handsets need bigger & faster memory capacity to handle the multi-media data. SAMSUNG’s UtRAM products are designed to meet all the request from the various customers who want to cope with the fast growing mobile market. Ut ...
An Update on SAS Software and ODBC
... of accessing information from a variety of data sources. ODBC allows applications to access different database file types whose drivers are installed on your machine. Your system comes configured with several standard ODBC drivers. Users can add addition drivers as needed. WHERE ITS AT - ODBC The go ...
... of accessing information from a variety of data sources. ODBC allows applications to access different database file types whose drivers are installed on your machine. Your system comes configured with several standard ODBC drivers. Users can add addition drivers as needed. WHERE ITS AT - ODBC The go ...
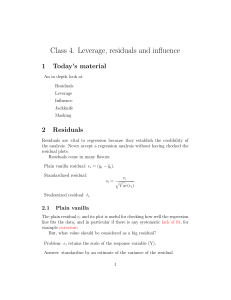
Class 4. Leverage, residuals and influence
... But, ei = (yi − ŷi ), which is more than just yi . Turns out, V ar(ei ) = σ 2 (1 − hii ). Use standardized residual, si . The quantity, hii is fundamental to regression. An heuristic explanation of hii (visually we are dragging a single point upward and measuring how the regression line follows): T ...
... But, ei = (yi − ŷi ), which is more than just yi . Turns out, V ar(ei ) = σ 2 (1 − hii ). Use standardized residual, si . The quantity, hii is fundamental to regression. An heuristic explanation of hii (visually we are dragging a single point upward and measuring how the regression line follows): T ...
WINFS_FinPPT
... - Custom made such queries such as to find “all persons whom I called last weekend”. Data mining - WinFS can give more information about data, by using data mining techniques. ...
... - Custom made such queries such as to find “all persons whom I called last weekend”. Data mining - WinFS can give more information about data, by using data mining techniques. ...
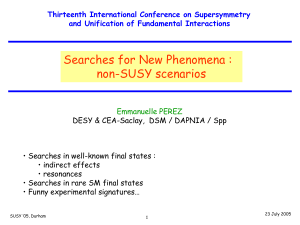
Searches for NP : non-SUSY scenarios
... 1 b-tagged jet, sample of ~ 100 events Search for a mass peak in M(jj) & M(Wjj) ...
... 1 b-tagged jet, sample of ~ 100 events Search for a mass peak in M(jj) & M(Wjj) ...
Xml and Relational Databases
... What is an XML Database? Simply a database that stores XML Documents There are two major types of XML databases: XML-enabled: These map all XML to a traditional database (such as a relational database), accepting XML as input and rendering XML as ...
... What is an XML Database? Simply a database that stores XML Documents There are two major types of XML databases: XML-enabled: These map all XML to a traditional database (such as a relational database), accepting XML as input and rendering XML as ...
PowerPoint
... – Collections of [name, value] pairs or maybe [name, type, value] triples – Collections typically set or list
...
... – Collections of [name, value] pairs or maybe [name, type, value] triples – Collections typically set
View File - University of Engineering and Technology, Taxila
... • The first objective of the ICDE v2.0 architecture is to provide an infrastructure to support a programming interface for third party client tools to access the ICDE data store. This must offer: – Flexibility in terms of platform and application deployment/ configuration needs for third party tools ...
... • The first objective of the ICDE v2.0 architecture is to provide an infrastructure to support a programming interface for third party client tools to access the ICDE data store. This must offer: – Flexibility in terms of platform and application deployment/ configuration needs for third party tools ...
Relationalizing RDF stores for tools reusability
... Every new data storage paradigm comes with its own demands for data modeling and visualization tools to simplify data management. In order to salvage the time, effort, and resources exhausted in the development of such tools for existing, mature technologies such as relational database management sy ...
... Every new data storage paradigm comes with its own demands for data modeling and visualization tools to simplify data management. In order to salvage the time, effort, and resources exhausted in the development of such tools for existing, mature technologies such as relational database management sy ...
Data mining of temporal sequences for the prediction of infrequent
... is carried out at opportunities based on the physical condition of the system. The automatic diagnosis of the physical condition of systems allows to detect degradation or failures either prior or directly upon their occurrence. Diagnosis is a term which englobes at the same time the observation of ...
... is carried out at opportunities based on the physical condition of the system. The automatic diagnosis of the physical condition of systems allows to detect degradation or failures either prior or directly upon their occurrence. Diagnosis is a term which englobes at the same time the observation of ...
Data mining of temporal sequences for the prediction of infrequent
... is carried out at opportunities based on the physical condition of the system. The automatic diagnosis of the physical condition of systems allows to detect degradation or failures either prior or directly upon their occurrence. Diagnosis is a term which englobes at the same time the observation of ...
... is carried out at opportunities based on the physical condition of the system. The automatic diagnosis of the physical condition of systems allows to detect degradation or failures either prior or directly upon their occurrence. Diagnosis is a term which englobes at the same time the observation of ...
the method of a two-level text-meaning similarity
... A primary use of graph theory in social network analysis is to identify “important” actors. Centrality and prestige concepts seek to quantify graph theoretic ideas about an individual actor’s prominence within a network by summarizing structural relations among the G-nodes. Group-level indexes of ce ...
... A primary use of graph theory in social network analysis is to identify “important” actors. Centrality and prestige concepts seek to quantify graph theoretic ideas about an individual actor’s prominence within a network by summarizing structural relations among the G-nodes. Group-level indexes of ce ...
Data analysis

Analysis of data is a process of inspecting, cleaning, transforming, and modeling data with the goal of discovering useful information, suggesting conclusions, and supporting decision-making. Data analysis has multiple facets and approaches, encompassing diverse techniques under a variety of names, in different business, science, and social science domains.Data mining is a particular data analysis technique that focuses on modeling and knowledge discovery for predictive rather than purely descriptive purposes. Business intelligence covers data analysis that relies heavily on aggregation, focusing on business information. In statistical applications, some people divide data analysis into descriptive statistics, exploratory data analysis (EDA), and confirmatory data analysis (CDA). EDA focuses on discovering new features in the data and CDA on confirming or falsifying existing hypotheses. Predictive analytics focuses on application of statistical models for predictive forecasting or classification, while text analytics applies statistical, linguistic, and structural techniques to extract and classify information from textual sources, a species of unstructured data. All are varieties of data analysis.Data integration is a precursor to data analysis, and data analysis is closely linked to data visualization and data dissemination. The term data analysis is sometimes used as a synonym for data modeling.