the method of a two-level text-meaning similarity
... A primary use of graph theory in social network analysis is to identify “important” actors. Centrality and prestige concepts seek to quantify graph theoretic ideas about an individual actor’s prominence within a network by summarizing structural relations among the G-nodes. Group-level indexes of ce ...
... A primary use of graph theory in social network analysis is to identify “important” actors. Centrality and prestige concepts seek to quantify graph theoretic ideas about an individual actor’s prominence within a network by summarizing structural relations among the G-nodes. Group-level indexes of ce ...
Predictive Subspace Clustering - ETH
... associated with this problem: (a) identifying the true subspaces is dependent on recovering the true clusters and vice-versa; (b) subspaces can intersect at several locations which causes difficulties when attempting to assign points to subspaces at these intersections, and standard clustering techn ...
... associated with this problem: (a) identifying the true subspaces is dependent on recovering the true clusters and vice-versa; (b) subspaces can intersect at several locations which causes difficulties when attempting to assign points to subspaces at these intersections, and standard clustering techn ...
Measuring Recidivism: Definitions, Errors, and Data Sources
... Error will exist in studies no matter what definition they choose to use. These errors are not unreasonable, though, and any definition will underestimate the “true” recidivism rate because rates are based on official criminal record data which will only show crimes for which people have been arres ...
... Error will exist in studies no matter what definition they choose to use. These errors are not unreasonable, though, and any definition will underestimate the “true” recidivism rate because rates are based on official criminal record data which will only show crimes for which people have been arres ...
IOSR Journal of Computer Engineering (IOSR-JCE) PP 09-11 www.iosrjournals.org
... In this days, the data mining is turn out as promising to handle data. Using arbitrage data mining techniques, real world software problems can be solved. Bug repository used for storing software bugs so they can be managed. So it plays an important role. Software industries spend more than 45 perce ...
... In this days, the data mining is turn out as promising to handle data. Using arbitrage data mining techniques, real world software problems can be solved. Bug repository used for storing software bugs so they can be managed. So it plays an important role. Software industries spend more than 45 perce ...
Chapter 17 Designing Effective Input
... When the relationship is one-to-many, the primary key of the file at the one end of the relationship should be contained as a foreign key on the file at the many end of the relationship A many-to-many relationship should be divided into two one-to-many relationships with an associative entity in t ...
... When the relationship is one-to-many, the primary key of the file at the one end of the relationship should be contained as a foreign key on the file at the many end of the relationship A many-to-many relationship should be divided into two one-to-many relationships with an associative entity in t ...
REDCap General Security Overview Introduction REDCap
... data, to add or modify database fields or survey questions, to build or run reports, to modify user privileges, to view the logging records, and so on. Another feature called Data Access Groups can be implemented to help segregate users and the data they enter by placing users into data access group ...
... data, to add or modify database fields or survey questions, to build or run reports, to modify user privileges, to view the logging records, and so on. Another feature called Data Access Groups can be implemented to help segregate users and the data they enter by placing users into data access group ...
On Pebble Automata for Data Languages with
... languages in which the first order part is restricted to two variables only. An important feature of data automata is that their emptiness problem is decidable, even for the infinite words, but is at least as hard as reachability for Petri nets. The automata themselves always work nondeterministica ...
... languages in which the first order part is restricted to two variables only. An important feature of data automata is that their emptiness problem is decidable, even for the infinite words, but is at least as hard as reachability for Petri nets. The automata themselves always work nondeterministica ...
Magnetotellurics with a remote magnetic reference
... MT array array is is uncorreuncorrenoise fated with with noise noise in in the the reference reference channels. channels.It should shouldbe be lated noted that that since sinceequation equation(I) (I) and and then then (2) is is multiplied multiplied noted in tum turn by by aa single single referen ...
... MT array array is is uncorreuncorrenoise fated with with noise noise in in the the reference reference channels. channels.It should shouldbe be lated noted that that since sinceequation equation(I) (I) and and then then (2) is is multiplied multiplied noted in tum turn by by aa single single referen ...
literature survey
... ambiguity or term-relatedness of the query to predict its difficultness. Examples like average document frequency of the query terms or the number of documents which contain atleast one query term. These methods generally predict that more the discriminative query terms are the easier the query will ...
... ambiguity or term-relatedness of the query to predict its difficultness. Examples like average document frequency of the query terms or the number of documents which contain atleast one query term. These methods generally predict that more the discriminative query terms are the easier the query will ...
Functional Data Structures for Typed Racket
... That does not prevent them from benefiting from the data structures presented in this paper, however. Typed Racket automatically supports interoperation between typed and untyped code, allowing any program to use the data structures presented here, regardless of whether it is typed. Typed Racket doe ...
... That does not prevent them from benefiting from the data structures presented in this paper, however. Typed Racket automatically supports interoperation between typed and untyped code, allowing any program to use the data structures presented here, regardless of whether it is typed. Typed Racket doe ...
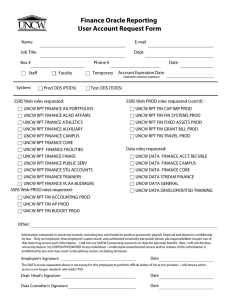
Finance Oracle Reporting User Account Request Form
... UNCW RPT FIN ACCOUNTING PROD UNCW RPT FIN AP PROD UNCW RPT FIN BUDGET PROD Other: Information contained in university records, including but not limited to student, personnel, payroll, financial and alumni is confidential by law. Only an employee, that employee's supervisor(s) and authorized univers ...
... UNCW RPT FIN ACCOUNTING PROD UNCW RPT FIN AP PROD UNCW RPT FIN BUDGET PROD Other: Information contained in university records, including but not limited to student, personnel, payroll, financial and alumni is confidential by law. Only an employee, that employee's supervisor(s) and authorized univers ...
Gonito.net – open platform for research competition, cooperation
... At this time, the accuracy, (root-)mean-square error and BLEU metrics are implemented in GEval. Due to the application author’s background in natural language processing the stress has been on NLP metrics and challenges so far. Nevertheless, Gonito.net could be used for any machine learning challeng ...
... At this time, the accuracy, (root-)mean-square error and BLEU metrics are implemented in GEval. Due to the application author’s background in natural language processing the stress has been on NLP metrics and challenges so far. Nevertheless, Gonito.net could be used for any machine learning challeng ...
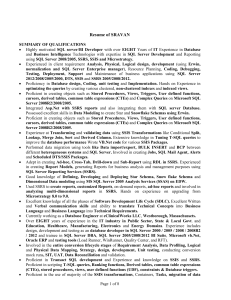
Resume of SRAVAN
... Participate in creating data conversion and migration strategy, conversion design and conversion development documents. Participate in Data Modeling Sessions. Hosted SSIS, SSRS knowledge transfer, data quality issue meetings with the client on a weekly/biweekly basis. Wrote T-SQL queries to vali ...
... Participate in creating data conversion and migration strategy, conversion design and conversion development documents. Participate in Data Modeling Sessions. Hosted SSIS, SSRS knowledge transfer, data quality issue meetings with the client on a weekly/biweekly basis. Wrote T-SQL queries to vali ...
Ultimate Hacking: Hands On
... launching attacks against his network A user complains her computer is slow and odd background processes are running ...
... launching attacks against his network A user complains her computer is slow and odd background processes are running ...
Can Financial Statement Auditors Detect More Fraud? How Can
... • Fraud detection procedures can be time‐consuming and expensive; audits are viewed as a commodity—i.e. why pay more for an audit than you have to; so price competition makes extra procedures commercially impractical ...
... • Fraud detection procedures can be time‐consuming and expensive; audits are viewed as a commodity—i.e. why pay more for an audit than you have to; so price competition makes extra procedures commercially impractical ...
When Development Means Business FY2000 First Quarter
... XML versus databases “The truth of the matter. The RDBMS is not going anywhere anytime soon, if ever. Even ignoring serious issues such as relational data representation in XML, the DBMS technology is a core part of too many applications in use today. Although XML may be a realistic possibility for ...
... XML versus databases “The truth of the matter. The RDBMS is not going anywhere anytime soon, if ever. Even ignoring serious issues such as relational data representation in XML, the DBMS technology is a core part of too many applications in use today. Although XML may be a realistic possibility for ...
High Dimensional Similarity Joins: Algorithms and Performance
... Spatial Join algorithm, named Multidimensional Spatial Join (MSJ), to solve the multidimensional join problem. We evaluate MSJ along with several other speci c algorithms, comparing their performance for various dimensionalities on both real and synthetic multidimensional data sets. Our experimental ...
... Spatial Join algorithm, named Multidimensional Spatial Join (MSJ), to solve the multidimensional join problem. We evaluate MSJ along with several other speci c algorithms, comparing their performance for various dimensionalities on both real and synthetic multidimensional data sets. Our experimental ...
SCT Operational Data Store / Banner to the ODS Implementation
... As data is entered into SCT Banner, it is typically processed one row at a time. For each field being entered, the data is verified for field syntax, such as date or numeric formats, and fields requiring additional verification against rule tables. After the values are properly checked, the data is ...
... As data is entered into SCT Banner, it is typically processed one row at a time. For each field being entered, the data is verified for field syntax, such as date or numeric formats, and fields requiring additional verification against rule tables. After the values are properly checked, the data is ...
download
... – Logical processes may be assigned to physical processors such as PCs, servers, mainframes, people, or devices in a network. A physical DFD would model that network structure. – Each logical process requires an implementation as one or more physical processes. Note that a logical process may be spl ...
... – Logical processes may be assigned to physical processors such as PCs, servers, mainframes, people, or devices in a network. A physical DFD would model that network structure. – Each logical process requires an implementation as one or more physical processes. Note that a logical process may be spl ...
Microsoft® ADO.NET
... Represents a cache of data that contains tables, columns, relationships, and constraints, just like a database Regardless of where the source data comes from, data can all be placed into DataSet objects Tracks changes that are made to the data it holds before updating the source data DataSet are als ...
... Represents a cache of data that contains tables, columns, relationships, and constraints, just like a database Regardless of where the source data comes from, data can all be placed into DataSet objects Tracks changes that are made to the data it holds before updating the source data DataSet are als ...
Session Title
... Conditions and exceptions are usually processed by the application server This generates additional data transfer between database and application servers If conditions and exceptions have to be used, the amount of data to be processed should be minimized with filters When multiple drilldowns ar ...
... Conditions and exceptions are usually processed by the application server This generates additional data transfer between database and application servers If conditions and exceptions have to be used, the amount of data to be processed should be minimized with filters When multiple drilldowns ar ...
Configuring the Analysis Services Query Log
... people, places, and events depicted herein are fictitious, and no association with any real company, organization, product, domain name, e-mail address, logo, person, place, or event is intended or should be inferred. 2006 Microsoft Corporation. All rights reserved. Microsoft and Windows are eithe ...
... people, places, and events depicted herein are fictitious, and no association with any real company, organization, product, domain name, e-mail address, logo, person, place, or event is intended or should be inferred. 2006 Microsoft Corporation. All rights reserved. Microsoft and Windows are eithe ...
Trigger Studies with Minimum Bias data samples
... multiple parton-parton scattering, string fragmentation • PYTHIA ATLAS AMBT1: P6 tuned by ATLAS to the low-multiplicity data • PYTHIA ATLAS MC09 (reference) P6 tune: parameters tuned to underlying events and minimum bias data from Tevatron at 630 GeV to 1. 8 TeV (ATLAS optimization), used to determi ...
... multiple parton-parton scattering, string fragmentation • PYTHIA ATLAS AMBT1: P6 tuned by ATLAS to the low-multiplicity data • PYTHIA ATLAS MC09 (reference) P6 tune: parameters tuned to underlying events and minimum bias data from Tevatron at 630 GeV to 1. 8 TeV (ATLAS optimization), used to determi ...
chap17
... When the relationship is one-to-many, the primary key of the file at the one end of the relationship should be contained as a foreign key on the file at the many end of the relationship A many-to-many relationship should be divided into two one-to-many relationships with an associative entity in t ...
... When the relationship is one-to-many, the primary key of the file at the one end of the relationship should be contained as a foreign key on the file at the many end of the relationship A many-to-many relationship should be divided into two one-to-many relationships with an associative entity in t ...
Learning Dependencies between Case Frame Slots
... (i.e. a set of dependency trees), whose nodes represent the random variables, and whose directed arcs represent the dependencies that exist between these random variables, each labeled with a number of parameters specifying the probabilistic dependency. (A dendroid distribution is a restricted form ...
... (i.e. a set of dependency trees), whose nodes represent the random variables, and whose directed arcs represent the dependencies that exist between these random variables, each labeled with a number of parameters specifying the probabilistic dependency. (A dendroid distribution is a restricted form ...
Data analysis

Analysis of data is a process of inspecting, cleaning, transforming, and modeling data with the goal of discovering useful information, suggesting conclusions, and supporting decision-making. Data analysis has multiple facets and approaches, encompassing diverse techniques under a variety of names, in different business, science, and social science domains.Data mining is a particular data analysis technique that focuses on modeling and knowledge discovery for predictive rather than purely descriptive purposes. Business intelligence covers data analysis that relies heavily on aggregation, focusing on business information. In statistical applications, some people divide data analysis into descriptive statistics, exploratory data analysis (EDA), and confirmatory data analysis (CDA). EDA focuses on discovering new features in the data and CDA on confirming or falsifying existing hypotheses. Predictive analytics focuses on application of statistical models for predictive forecasting or classification, while text analytics applies statistical, linguistic, and structural techniques to extract and classify information from textual sources, a species of unstructured data. All are varieties of data analysis.Data integration is a precursor to data analysis, and data analysis is closely linked to data visualization and data dissemination. The term data analysis is sometimes used as a synonym for data modeling.