SQL DATA DEFINITION: KEY CONSTRAINTS
... Can specify candidate keys with UNIQUE constraints Like primary key constraints, can specify candidate keys in the column declaration, or after all columns ¤ Can only specify multi-column candidate key after the ...
... Can specify candidate keys with UNIQUE constraints Like primary key constraints, can specify candidate keys in the column declaration, or after all columns ¤ Can only specify multi-column candidate key after the ...
MS-SQL Advantages - Sloan Digital Sky Survey
... database subset (number of database files and containers) that will be searched and a time approximation required to complete the search. The user decides whether the query is worth running based on its scope and the time required to search that scope. We compute the projected query cost by building ...
... database subset (number of database files and containers) that will be searched and a time approximation required to complete the search. The user decides whether the query is worth running based on its scope and the time required to search that scope. We compute the projected query cost by building ...
Information and Communication Technology
... If you try to update the database, you will get the error message: "You do not have permission to update this database". You get this error because you don't have write access to the server. To solve this problem, right-click the .mdb file and select Properties. Go to the Security tab and set the ac ...
... If you try to update the database, you will get the error message: "You do not have permission to update this database". You get this error because you don't have write access to the server. To solve this problem, right-click the .mdb file and select Properties. Go to the Security tab and set the ac ...
SilkRoute : A Framework for Publishing Relational Data - CS
... in which XML documents are generated from persistent data then sent over a network to an application. Numerous industry groups, including automotive, health care, and telecommunications, publish document type definitions (DTDs) and XML Schemata [World-Wide Web Consortium 2001a], which specify the fo ...
... in which XML documents are generated from persistent data then sent over a network to an application. Numerous industry groups, including automotive, health care, and telecommunications, publish document type definitions (DTDs) and XML Schemata [World-Wide Web Consortium 2001a], which specify the fo ...
Cracking the Database Store
... table scan, i.e. touching all tuples to select those of interest. The result produced in most systems is a stream of qualifying tuples. However, it can also be interpreted as a task to fragment the table into two pieces, i.e. apply horizontal fragmentation. This operation does not come for free, bec ...
... table scan, i.e. touching all tuples to select those of interest. The result produced in most systems is a stream of qualifying tuples. However, it can also be interpreted as a task to fragment the table into two pieces, i.e. apply horizontal fragmentation. This operation does not come for free, bec ...
CS211 Lecture: Persistence; Introduction to Relational Databases
... 1. There are database systems known as object-oriented databases, whose structure is object oriented. The entities stored in such databases are objects 2. However, most commercial databases use one of several non OO models, of which the most prevalent today is the RELATIONAL model. There are a whole ...
... 1. There are database systems known as object-oriented databases, whose structure is object oriented. The entities stored in such databases are objects 2. However, most commercial databases use one of several non OO models, of which the most prevalent today is the RELATIONAL model. There are a whole ...
ppt
... Unique: No two distinct tuples can have the same values in all key fields Minimal: A proper subset of the key attributes is not a key. ...
... Unique: No two distinct tuples can have the same values in all key fields Minimal: A proper subset of the key attributes is not a key. ...
MYCH3
... that you can deduce is not a candidate key, if this instance is legal. 2. Is there any example of an attribute (or set of attributes) that you can deduce is a candidate key? 3. Does every relational schema have some candidate key? Database Management Systems 3ed, R. Ramakrishnan and J. Gehrke ...
... that you can deduce is not a candidate key, if this instance is legal. 2. Is there any example of an attribute (or set of attributes) that you can deduce is a candidate key? 3. Does every relational schema have some candidate key? Database Management Systems 3ed, R. Ramakrishnan and J. Gehrke ...
2_Managing external data_2
... - impedance mismatch • SQL is a powerful, set-oriented, declarative language • SQL queries return sets of rows • host languages cannot handle large sets of structured data • cursors resolve the mismatch: • Demo ...
... - impedance mismatch • SQL is a powerful, set-oriented, declarative language • SQL queries return sets of rows • host languages cannot handle large sets of structured data • cursors resolve the mismatch: • Demo ...
Relational Algebra
... Selection ( ) Selects a subset of rows from relation. Projection ( ) Deletes unwanted columns from relation. Cross-product ( ) Allows us to combine two relations. Set-difference ( ) Gives tuples in rel. 1, but not in rel. 2. Union ( ) Gives tuples in rel. 1 and in rel. 2. ...
... Selection ( ) Selects a subset of rows from relation. Projection ( ) Deletes unwanted columns from relation. Cross-product ( ) Allows us to combine two relations. Set-difference ( ) Gives tuples in rel. 1, but not in rel. 2. Union ( ) Gives tuples in rel. 1 and in rel. 2. ...
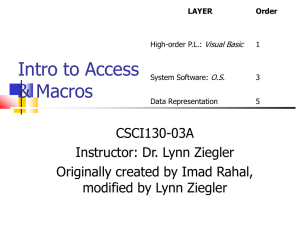
cse103day06
... Copy the c&u database from the Day 06 AFS space to your personal space Open it in Access and explore the tables. – What information is stored in each table? – What information is stored in two places? In one spot, it will be a primary key of the table (check Design View), in another, it will be used ...
... Copy the c&u database from the Day 06 AFS space to your personal space Open it in Access and explore the tables. – What information is stored in each table? – What information is stored in two places? In one spot, it will be a primary key of the table (check Design View), in another, it will be used ...
Implementation Plan - Project Management
... Frequency Daily Event, every 5minutes URL http://reports.is.ed.ac.uk/alerts_te st/scheduled/completionReminder ...
... Frequency Daily Event, every 5minutes URL http://reports.is.ed.ac.uk/alerts_te st/scheduled/completionReminder ...
Using Oracle GoldenGate 12c with SQL Server Databases
... The Delivery module applies each database change in the same order as it was committed in the source database to provide data and referential integrity. In addition, it applies changes within the same transaction context as they were on the source system for consistency on the target. Column Mapping ...
... The Delivery module applies each database change in the same order as it was committed in the source database to provide data and referential integrity. In addition, it applies changes within the same transaction context as they were on the source system for consistency on the target. Column Mapping ...
Relational Database Systems 1 - IfIS
... – explain the fundamental terms of • relational database systems • theoretical and practical query languages • conceptual and logical design of databases including normalization • application programming • further concepts like constraints, views, indexes, transactions and object databases ...
... – explain the fundamental terms of • relational database systems • theoretical and practical query languages • conceptual and logical design of databases including normalization • application programming • further concepts like constraints, views, indexes, transactions and object databases ...
Execute the Query
... 2a. Error reported back from database that query is invalid. 2b. Flow continues with step 5. ...
... 2a. Error reported back from database that query is invalid. 2b. Flow continues with step 5. ...
XML Presentation ()
... relational databases) We model the data as semistructured to facilitate exchange and integration Users see an integrated semistructured view that they can query Queries are eventually reformulated into queries over the structured resources (e.g. SQL) Only results need to be materialized ...
... relational databases) We model the data as semistructured to facilitate exchange and integration Users see an integrated semistructured view that they can query Queries are eventually reformulated into queries over the structured resources (e.g. SQL) Only results need to be materialized ...
Relational Algebra - LeMoyne
... Selection ( ) Selects a subset of rows from relation. Projection ( ) Deletes unwanted columns from relation. Cross-product ( ) Allows us to combine two relations. Set-difference ( ) Tuples in reln. 1, but not in reln. 2. Union ( ) Tuples in reln. 1 and in reln. 2. ...
... Selection ( ) Selects a subset of rows from relation. Projection ( ) Deletes unwanted columns from relation. Cross-product ( ) Allows us to combine two relations. Set-difference ( ) Tuples in reln. 1, but not in reln. 2. Union ( ) Tuples in reln. 1 and in reln. 2. ...
Relational Algebra
... Query Languages != programming languages! QLs not expected to be “Turing complete”. QLs not intended to be used for complex calculations. QLs support easy, efficient access to large data sets. ...
... Query Languages != programming languages! QLs not expected to be “Turing complete”. QLs not intended to be used for complex calculations. QLs support easy, efficient access to large data sets. ...
Slide 1
... • TotalHR SQL is a flexible product that provides a the ability for customization. • Customer’s requirements go further than the standard product. • Third Party Applications ...
... • TotalHR SQL is a flexible product that provides a the ability for customization. • Customer’s requirements go further than the standard product. • Third Party Applications ...
mysql_T1
... Structured Query Language (SQL): A standardized query language for getting information from a relational database. ...
... Structured Query Language (SQL): A standardized query language for getting information from a relational database. ...
XML Security
... • Datasets that are so large or complex that they are difficult to process using traditional database processing applications. • 2.5 quintillion ( 1 followed by 18 zeros ) bytes data being generated every day. • 72 hours per minute video uploaded to youtube. • Data of this scale and complexity needs ...
... • Datasets that are so large or complex that they are difficult to process using traditional database processing applications. • 2.5 quintillion ( 1 followed by 18 zeros ) bytes data being generated every day. • 72 hours per minute video uploaded to youtube. • Data of this scale and complexity needs ...
Database Architecture
... discussion. Some DBAs argue with an almost religious fervor instead of simply using common sense (this happens with several other database architecture topics as well). Most of the strong objections to using prefixes come from mere personal opinion instead of being based on sound logic. When using p ...
... discussion. Some DBAs argue with an almost religious fervor instead of simply using common sense (this happens with several other database architecture topics as well). Most of the strong objections to using prefixes come from mere personal opinion instead of being based on sound logic. When using p ...