Lecture X - Integrity Constrains
... Example: If “Perryridge” is a branch name appearing in one of the tuples in the account relation, then there exists a tuple in the branch relation for branch “Perryridge”. ...
... Example: If “Perryridge” is a branch name appearing in one of the tuples in the account relation, then there exists a tuple in the branch relation for branch “Perryridge”. ...
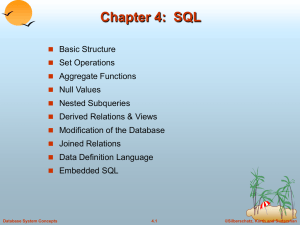
ppt - Avi Silberschatz
... Example: If “Perryridge” is a branch name appearing in one of the tuples in the account relation, then there exists a tuple in the branch relation for branch “Perryridge”. ...
... Example: If “Perryridge” is a branch name appearing in one of the tuples in the account relation, then there exists a tuple in the branch relation for branch “Perryridge”. ...
Oracle, SAP and MS SQL on Vblock System 540
... XtremIO database storage design considerations ......................................................................... 25 Storage layout for Oracle database ............................................................................................... 26 Storage layout for SQL database .......... ...
... XtremIO database storage design considerations ......................................................................... 25 Storage layout for Oracle database ............................................................................................... 26 Storage layout for SQL database .......... ...
Chapter 6: Integrity and Security Domain Constraints
... Then K1 and K2 form foreign keys on the relational schemas for E1 and E2 respectively. E1 ...
... Then K1 and K2 form foreign keys on the relational schemas for E1 and E2 respectively. E1 ...
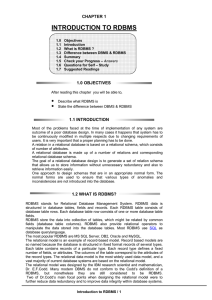
Module 1: Introduction
... Example: If “Perryridge” is a branch name appearing in one of the tuples in the account relation, then there exists a tuple in the branch relation for branch “Perryridge”. ...
... Example: If “Perryridge” is a branch name appearing in one of the tuples in the account relation, then there exists a tuple in the branch relation for branch “Perryridge”. ...
Referential Integrity
... Forms of authorization to modify the database schema: ! Index authorization - allows creation and deletion of indices. ! Resources authorization - allows creation of new relations. ! Alteration authorization - allows addition or deletion of attributes in ...
... Forms of authorization to modify the database schema: ! Index authorization - allows creation and deletion of indices. ! Resources authorization - allows creation of new relations. ! Alteration authorization - allows addition or deletion of attributes in ...
Database transaction
... The isolation level of an SQL-transaction specifies the extent to which the effects of actions by SQL-agents other than in the SQL-environment, are perceived within that SQL-transaction. Every isolation level guarantees that every SQL-transaction is executed; SQL-transactions not executing complete ...
... The isolation level of an SQL-transaction specifies the extent to which the effects of actions by SQL-agents other than in the SQL-environment, are perceived within that SQL-transaction. Every isolation level guarantees that every SQL-transaction is executed; SQL-transactions not executing complete ...
A Relational Data Warehouse for Multidimensional - CEUR
... conformance checking compares an event log to a manually created or previously discovered process model to measure the quality of the process model, and (3) process enhancement extends a process model with additional information (e.g., timestamps) to provide additional perspectives on the process. B ...
... conformance checking compares an event log to a manually created or previously discovered process model to measure the quality of the process model, and (3) process enhancement extends a process model with additional information (e.g., timestamps) to provide additional perspectives on the process. B ...
SS-L7.6 (pg. 5349)
... and other “Big Table Like” databases leverage the HadoopDFS by modeling Google Big Table [14]. These databases are designed for data mining applications that do little read-modify-write and where statistical consistency is more than adequate. Under these the relaxed restrictions there is potential t ...
... and other “Big Table Like” databases leverage the HadoopDFS by modeling Google Big Table [14]. These databases are designed for data mining applications that do little read-modify-write and where statistical consistency is more than adequate. Under these the relaxed restrictions there is potential t ...
Library Cache Hit Ratios
... This is the proportion of full table scans which are occurring on short tables. Short tables may be scanned by Oracle when this is quicker than using an index. Full table scans of long tables is generally bad for overall performance. Low figures for this graph may indicate lack of indexes on large t ...
... This is the proportion of full table scans which are occurring on short tables. Short tables may be scanned by Oracle when this is quicker than using an index. Full table scans of long tables is generally bad for overall performance. Low figures for this graph may indicate lack of indexes on large t ...
Database System Concepts, 5th Ed
... between the low-level data stored in the database and the application programs and queries submitted to the system. The storage manager is responsible to the following tasks: ...
... between the low-level data stored in the database and the application programs and queries submitted to the system. The storage manager is responsible to the following tasks: ...
Profiles, password policies, privileges, and roles
... • Profiles define database users behavior • In Oracle: – DBA_PROFILE view – ALTER USER ...
... • Profiles define database users behavior • In Oracle: – DBA_PROFILE view – ALTER USER ...
Engineering a Distributed Intrusion Tolerant Database
... –how many intrusions are detected, isolated, or masked –how many mistakes are made –how effectively can the damage be confined –how quick can the damage be assessed and repaired –how well can the system be adapted –availability: how often is a legitimate request rejected –integrity: how well can dat ...
... –how many intrusions are detected, isolated, or masked –how many mistakes are made –how effectively can the damage be confined –how quick can the damage be assessed and repaired –how well can the system be adapted –availability: how often is a legitimate request rejected –integrity: how well can dat ...
Object-Oriented Databases
... to define the schema. – STEP models are standardized schemas for different engineering application areas, e.g. AP209 – The exchanged data follows specialized STEP schemas, e.g. PART 21 most common (XML based too, PART 29) – CAx vendors normally not able to handle EXPRESS schemas – Only PART 29 files ...
... to define the schema. – STEP models are standardized schemas for different engineering application areas, e.g. AP209 – The exchanged data follows specialized STEP schemas, e.g. PART 21 most common (XML based too, PART 29) – CAx vendors normally not able to handle EXPRESS schemas – Only PART 29 files ...
Views
... Querying the WWW • Assume a virtual schema of the WWW, e.g., – Course(number, university, title, prof, quarter) ...
... Querying the WWW • Assume a virtual schema of the WWW, e.g., – Course(number, university, title, prof, quarter) ...
Application Context
... having which row groups to include in the cursor, if row grouping is being used, formatted as an SQL HAVING clause (excluding the HAVING itself). Passing null will cause all row groups to be included, and is required when row grouping is not being used. ...
... having which row groups to include in the cursor, if row grouping is being used, formatted as an SQL HAVING clause (excluding the HAVING itself). Passing null will cause all row groups to be included, and is required when row grouping is not being used. ...
branch-name
... average account balance is greater than $1200. select branch-name, avg-balance from (select branch-name, avg (balance) from account group by branch-name) as result (branch-name, avg-balance) where avg-balance > 1200 Note that we do not need to use the having clause, since we compute the temporary (v ...
... average account balance is greater than $1200. select branch-name, avg-balance from (select branch-name, avg (balance) from account group by branch-name) as result (branch-name, avg-balance) where avg-balance > 1200 Note that we do not need to use the having clause, since we compute the temporary (v ...
Introduction - CSE, IIT Bombay
... ■ Relational model ■ EntityRelationship data model (mainly for database design) ■ Objectbased data models (Objectoriented and Objectrelational) ■ Semistructured data model (XML) ...
... ■ Relational model ■ EntityRelationship data model (mainly for database design) ■ Objectbased data models (Objectoriented and Objectrelational) ■ Semistructured data model (XML) ...
- Courses - University of California, Berkeley
... available in many different configurations • They also tend to be VERY expensive • Pricing is usually based on users, or CPU’s Oct. 16, 2001 ...
... available in many different configurations • They also tend to be VERY expensive • Pricing is usually based on users, or CPU’s Oct. 16, 2001 ...
Protecting Sensitive Inforation with Database Encryption
... 3.6.6 Split knowledge and establishment of dual control of keys (so that it requires two or three people, each knowing only their part of the key, to reconstruct the whole key) 3.6.7 Prevention of unauthorized substitution of keys 3.6.8 Replacement of known or suspected compromised keys 3.6.9 Revoca ...
... 3.6.6 Split knowledge and establishment of dual control of keys (so that it requires two or three people, each knowing only their part of the key, to reconstruct the whole key) 3.6.7 Prevention of unauthorized substitution of keys 3.6.8 Replacement of known or suspected compromised keys 3.6.9 Revoca ...
Using VRML as an Interface to the 3D Data Warehouse
... However, there is an obvious limit in the usefulness of VRML to interact with the 3D data warehouse. Just like the WWW itself, VRML was initially created for viewing data only, not for interaction. Therefore, it delivers the 3-D model of a city, but you cannot use it in an intuitive way to interact ...
... However, there is an obvious limit in the usefulness of VRML to interact with the 3D data warehouse. Just like the WWW itself, VRML was initially created for viewing data only, not for interaction. Therefore, it delivers the 3-D model of a city, but you cannot use it in an intuitive way to interact ...
XML In An RDBMS World
... XML documents tend to be semi-structured, SQL tables are highly structured SQL tables aren’t as flexible or interchangable XML joins aren’t straightforward An XML document/element doesn’t serve multiple purposes as well as DB schema/table ...
... XML documents tend to be semi-structured, SQL tables are highly structured SQL tables aren’t as flexible or interchangable XML joins aren’t straightforward An XML document/element doesn’t serve multiple purposes as well as DB schema/table ...