Layer2-network
... • Forwards each incoming frame to the port where the destination node is – Reduces the collision domain – Makes more efficient use of the wire – Nodes don’t waste time checking frames not destined to ...
... • Forwards each incoming frame to the port where the destination node is – Reduces the collision domain – Makes more efficient use of the wire – Nodes don’t waste time checking frames not destined to ...
downloading
... • Forwards each incoming frame to the port where the destination node is – Reduces the collision domain – Makes more efficient use of the wire – Nodes don’t waste time checking frames not destined to ...
... • Forwards each incoming frame to the port where the destination node is – Reduces the collision domain – Makes more efficient use of the wire – Nodes don’t waste time checking frames not destined to ...
Ports and IPv6
... Generally speaking, a computer has a single physical connection to the network. All data destined for a particular computer arrives through that connection. However, the data may be intended for different applications running on the computer. So how does the computer know to which application to for ...
... Generally speaking, a computer has a single physical connection to the network. All data destined for a particular computer arrives through that connection. However, the data may be intended for different applications running on the computer. So how does the computer know to which application to for ...
The Spanning Tree Protocol - Dipartimento di Scienze Ambientali
... It sends HELLO packets communicating all the other bridges on the link its known root, and the distance to it When a bridge receives a HELLO from a LAN segment in which a bridge claims to be closer to the root or with same distance but smaller ID, then the bridge stop sending hello packets on that L ...
... It sends HELLO packets communicating all the other bridges on the link its known root, and the distance to it When a bridge receives a HELLO from a LAN segment in which a bridge claims to be closer to the root or with same distance but smaller ID, then the bridge stop sending hello packets on that L ...
Document
... • By interconnecting multiple switches with redundant paths, you overcome problems with faulty cables or port failures • Another less well-known side effect of a loop is the corruption of the forwarding tables on all the switches • It would take very little time before Layer 2 broadcast loops comple ...
... • By interconnecting multiple switches with redundant paths, you overcome problems with faulty cables or port failures • Another less well-known side effect of a loop is the corruption of the forwarding tables on all the switches • It would take very little time before Layer 2 broadcast loops comple ...
LAN Overview
... each bridge assigned unique identifier cost assigned to each bridge port exchange information between bridges to find spanning tree automatically updated whenever topology changes ...
... each bridge assigned unique identifier cost assigned to each bridge port exchange information between bridges to find spanning tree automatically updated whenever topology changes ...
Week_Five_Network_ppt
... Multi-homing is to provide more that one connection for a system to access and offer network services. In an enterprise network, multi-homing provides access to more than one entry into the Internet. Example: WAN backup and ISP redundancy If a server has more than one network layer address ...
... Multi-homing is to provide more that one connection for a system to access and offer network services. In an enterprise network, multi-homing provides access to more than one entry into the Internet. Example: WAN backup and ISP redundancy If a server has more than one network layer address ...
Chapter 3: Internetworking (part 1)
... Each bridge computes the shortest path to the root and notes which of its ports is on this path ...
... Each bridge computes the shortest path to the root and notes which of its ports is on this path ...
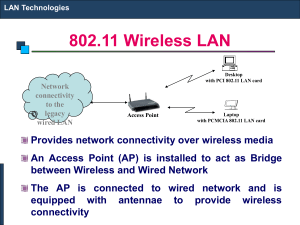
802.11 Wireless LAN
... network segments within the same network. They operate at the OSI data link layer (Layer 2) and are independent of higherlayer protocols. The function of the bridge is to make ...
... network segments within the same network. They operate at the OSI data link layer (Layer 2) and are independent of higherlayer protocols. The function of the bridge is to make ...
ITEC275v2
... • Use Bridge Protocol Data Units (BPDU) skew detection on Cisco switches • Use IEEE 802.1w – Provides rapid reconfiguration of the spanning tree – Also known as RSTP ...
... • Use Bridge Protocol Data Units (BPDU) skew detection on Cisco switches • Use IEEE 802.1w – Provides rapid reconfiguration of the spanning tree – Also known as RSTP ...
Switching
... • Need to disable ports, so that no loops in network • Like creating a spanning tree in a graph - View switches and networks as nodes, ports as edges ...
... • Need to disable ports, so that no loops in network • Like creating a spanning tree in a graph - View switches and networks as nodes, ports as edges ...
Week 2
... • Aging timer - the number of seconds a MAC-address will be kept in the forwarding database after having received a packet from this MAC address. • Forward delay timer - the time spent in each of the Listening and Learning states before the Forwarding state is entered. • Hello timer – The time inter ...
... • Aging timer - the number of seconds a MAC-address will be kept in the forwarding database after having received a packet from this MAC address. • Forward delay timer - the time spent in each of the Listening and Learning states before the Forwarding state is entered. • Hello timer – The time inter ...
Ethernet - SigmaNet
... The default system MTU for traffic on the switch is 1500 bytes. You can configure the switch to support larger frames by using the system mtu global configuration command. Because the 802.1Q tunneling feature increases the frame size by 4 bytes when the metro tag is added, you must configure all swi ...
... The default system MTU for traffic on the switch is 1500 bytes. You can configure the switch to support larger frames by using the system mtu global configuration command. Because the 802.1Q tunneling feature increases the frame size by 4 bytes when the metro tag is added, you must configure all swi ...
Spanning Tree Protocol (STP)
... path to the root bridge. • Each switch uses the STA to determine which ports to block. • The STA considers both path and port costs when determining which path to leave unblocked. • The path costs are calculated using port cost values associated with port speeds for each switch port along a given pa ...
... path to the root bridge. • Each switch uses the STA to determine which ports to block. • The STA considers both path and port costs when determining which path to leave unblocked. • The path costs are calculated using port cost values associated with port speeds for each switch port along a given pa ...
Solution to test 2
... Source address = 158.132.2.100 and destination address = 255.255.255.255. All nodes on subnet 1 will receive this ICMP request message and send reply messages to 158.132.2.100. Since the routers do not check the source addresses when forwarding, all the reply messages will be forwarded to subnet 2. ...
... Source address = 158.132.2.100 and destination address = 255.255.255.255. All nodes on subnet 1 will receive this ICMP request message and send reply messages to 158.132.2.100. Since the routers do not check the source addresses when forwarding, all the reply messages will be forwarded to subnet 2. ...
Network Layer
... How does a switch make its decision? ◦ This depends on the approach {connectionless, etc} ◦ In general, look at the header of the packet for an identifier (could be a local id, could be an IP addr) Use this to make your decision by looking up the ID in a table, and forward accordingly ...
... How does a switch make its decision? ◦ This depends on the approach {connectionless, etc} ◦ In general, look at the header of the packet for an identifier (could be a local id, could be an IP addr) Use this to make your decision by looking up the ID in a table, and forward accordingly ...
Lecture08
... (Note: Now we usually use low CPU computer as part of these devices, if programmable) ...
... (Note: Now we usually use low CPU computer as part of these devices, if programmable) ...
Spanning Tree Protocol
... • During the time that the Layer 2 network is converging, MAC addresses that can no longer be reached still exist in the CAM table. • STP topology change process forces the switch to purge MAC addresses in the CAM table faster. • When a root bridge sends out a topology change BPDU the topology chang ...
... • During the time that the Layer 2 network is converging, MAC addresses that can no longer be reached still exist in the CAM table. • STP topology change process forces the switch to purge MAC addresses in the CAM table faster. • When a root bridge sends out a topology change BPDU the topology chang ...
Chapter 3 Part 1 Switching and Bridging Networking CS 3470, Section 1
... tear down of the circuit after each use. No one else can use any of the bandwidth during an active session—even if it is idle! Known as a connection-oriented approach ...
... tear down of the circuit after each use. No one else can use any of the bandwidth during an active session—even if it is idle! Known as a connection-oriented approach ...
lan-switches
... Ethernet Hubs vs. Ethernet Switches • An Ethernet switch is a packet switch for Ethernet frames • Buffering of frames prevents collisions. • Each port is isolated and builds its own collision domain • An Ethernet Hub does not perform buffering: • Collisions occur if two frames arrive at the same ti ...
... Ethernet Hubs vs. Ethernet Switches • An Ethernet switch is a packet switch for Ethernet frames • Buffering of frames prevents collisions. • Each port is isolated and builds its own collision domain • An Ethernet Hub does not perform buffering: • Collisions occur if two frames arrive at the same ti ...
Spanning Tree Protocol for Bridges/Switches
... • Selected ports are placed in the forwarding state, meaning that B will forward packets to and from those ports. • All other ports are placed in the blocking state, meaning that B will NOT forward packet to and from them. ...
... • Selected ports are placed in the forwarding state, meaning that B will forward packets to and from those ports. • All other ports are placed in the blocking state, meaning that B will NOT forward packet to and from them. ...
Defense - Northwestern Networks Group
... • Layer 3 will only use one of the existing equal cost paths • Packet re-ordering occurs if layer 3 blindly takes advantage of path diversity – Creates overhead at host as TCP must order the packets ...
... • Layer 3 will only use one of the existing equal cost paths • Packet re-ordering occurs if layer 3 blindly takes advantage of path diversity – Creates overhead at host as TCP must order the packets ...
LAN Switching
... With the help of the BPDUs, bridges can: • Elect a single bridge as the root bridge. • Calculate the distance of the shortest path to the root bridge • Each LAN can determine a designated bridge, which is the bridge closest to the root on a shared medium (e.g., Ethernet). The designated bridge will ...
... With the help of the BPDUs, bridges can: • Elect a single bridge as the root bridge. • Calculate the distance of the shortest path to the root bridge • Each LAN can determine a designated bridge, which is the bridge closest to the root on a shared medium (e.g., Ethernet). The designated bridge will ...
LANs - UQAC
... suitable for internets that are stable a fixed route is selected for each pair of LANs • usually least hop route ...
... suitable for internets that are stable a fixed route is selected for each pair of LANs • usually least hop route ...
Spanning Tree Protocol
The Spanning Tree Protocol (STP) is an older network protocol that ensures a loop-free topology for any bridged Ethernet local area network. The basic function of STP is to prevent bridge loops and the broadcast radiation that results from them. Spanning tree also allows a network design to include spare (redundant) links to provide automatic backup paths if an active link fails, without the danger of bridge loops, or the need for manual enabling/disabling of these backup links.Spanning Tree Protocol (STP) was originally standardized as IEEE 802.1D, in 802.1d-1998, but much of the functionality (spanning tree, rapid spanning tree, multiple spanning tree) previously specified in 802.1D, 801.1s, 802.1w has been incorporated into IEEE 802.1Q-2014 which includes shortest path bridging, the IEEE sanctioned replacement for these spanning tree functions.As the name suggests, it creates a spanning tree within a network of connected layer-2 bridges (typically Ethernet switches), and disables those links that are not part of the spanning tree, leaving a single active path between any two network nodes. STP is based on an algorithm that was invented by Radia Perlman while she was working for Digital Equipment Corporation.