slides - cse.sc.edu
... 1. Dormant phase: the virus is idle. (not all viruses have this stage) 2. Propagation phase: the virus places an identical copy of itself into other programs of into certain system areas. 3. Triggering phase: the virus is activated to perform the function for which it was created. 4. Execution phase ...
... 1. Dormant phase: the virus is idle. (not all viruses have this stage) 2. Propagation phase: the virus places an identical copy of itself into other programs of into certain system areas. 3. Triggering phase: the virus is activated to perform the function for which it was created. 4. Execution phase ...
macro virus - University of Windsor
... • Malware : any piece of malicious software. • Security tools and toolkits : are designed to be used by security professionals to protect their sites. These can also be used by unauthorized individuals to probe for weaknesses. The purposes, not the approach, makes a program malicious. • Many of the ...
... • Malware : any piece of malicious software. • Security tools and toolkits : are designed to be used by security professionals to protect their sites. These can also be used by unauthorized individuals to probe for weaknesses. The purposes, not the approach, makes a program malicious. • Many of the ...
Chapter 03
... OS Checks permission on file, OS does something else… Hacker makes file a symbolic link from readme to /etc/shadow. ◦ OS allows access to file. Hacker changes passwords. ...
... OS Checks permission on file, OS does something else… Hacker makes file a symbolic link from readme to /etc/shadow. ◦ OS allows access to file. Hacker changes passwords. ...
Lesson 11a - Malicious Software (Malware)
... First virus anywhere was ‘creeper’ developed by Bob Thomas at BBN Technologies (1971) using ARPANET to infect Dec PDP-10 computers running Tenex Reaper program was written to eradicate Creeper Elk Cloner written in 1981 by Richard Skrenka as a practical joke – spread through floppy disk to Apple DOS ...
... First virus anywhere was ‘creeper’ developed by Bob Thomas at BBN Technologies (1971) using ARPANET to infect Dec PDP-10 computers running Tenex Reaper program was written to eradicate Creeper Elk Cloner written in 1981 by Richard Skrenka as a practical joke – spread through floppy disk to Apple DOS ...
OnLinePrivacy - Cal State LA
... Often hidden inside innocuous programs. Viruses in e-mails often masquerade as games or pictures and use beguiling subject lines (e.g., "My girlfriend nude") to encourage users to open and run them. Try to replicate themselves by infecting other programs on your computer. ...
... Often hidden inside innocuous programs. Viruses in e-mails often masquerade as games or pictures and use beguiling subject lines (e.g., "My girlfriend nude") to encourage users to open and run them. Try to replicate themselves by infecting other programs on your computer. ...
EXECUTIVE SUMMARY
... Why would scanning ProfitStars data for viruses cause problems? At least three kinds of problems might occur when scanning ProfitStars data files: 1. The antivirus program modifies a ProfitStars data file. Antivirus programs sometimes incorrectly detect a virus—they identify a virus when in fact no ...
... Why would scanning ProfitStars data for viruses cause problems? At least three kinds of problems might occur when scanning ProfitStars data files: 1. The antivirus program modifies a ProfitStars data file. Antivirus programs sometimes incorrectly detect a virus—they identify a virus when in fact no ...
Viruses - Binus Repository
... What is a Virus? • A program that is designed explore or exploit the security of a system • Originally designed to perform useful functions they were given the name “daemons” • Daemons are independent processes that have a “life” of their own. • Daemons run in the background of a operating system a ...
... What is a Virus? • A program that is designed explore or exploit the security of a system • Originally designed to perform useful functions they were given the name “daemons” • Daemons are independent processes that have a “life” of their own. • Daemons run in the background of a operating system a ...
A Primer on Computer Security
... TimeSink), is distributed with many freeware and shareware programs, including the Windows version of the ...
... TimeSink), is distributed with many freeware and shareware programs, including the Windows version of the ...
Ethics
... What is a Virus? Self-replicating piece of code that attaches itself to other programs; usually requires human interaction to propagate ...
... What is a Virus? Self-replicating piece of code that attaches itself to other programs; usually requires human interaction to propagate ...
Lecture 16 - Suraj @ LUMS
... – Also called propagating Trojan horse – Early version of animal game used this to delete copies of itself ...
... – Also called propagating Trojan horse – Early version of animal game used this to delete copies of itself ...
Networks and Security - Web Services Overview
... Require user interaction for propagation -- e.g. Open a file, boot from floppy, launch an executable, click on e-mail attachment etc. ...
... Require user interaction for propagation -- e.g. Open a file, boot from floppy, launch an executable, click on e-mail attachment etc. ...
Figure 6-1
... a normal virus, except they rely on people to spread the infection, not a computer. A good example of a social engineering virus is the Good Times virus hoax that has circulated on the Internet for many years. This e-mail message announces that a dangerous virus is being circulated via e-mail and ha ...
... a normal virus, except they rely on people to spread the infection, not a computer. A good example of a social engineering virus is the Good Times virus hoax that has circulated on the Internet for many years. This e-mail message announces that a dangerous virus is being circulated via e-mail and ha ...
Security
... After virus has captured interrupt, trap vectors After OS has retaken printer interrupt vector After virus has noticed loss of printer interrupt vector and recaptured it ...
... After virus has captured interrupt, trap vectors After OS has retaken printer interrupt vector After virus has noticed loss of printer interrupt vector and recaptured it ...
Chapter 06
... • Event or condition that determines when the payload is activated or delivered • Sometimes known as a logic bomb Payload • What the virus does (besides spreading) • May involve damage or benign but noticeable activity ...
... • Event or condition that determines when the payload is activated or delivered • Sometimes known as a logic bomb Payload • What the virus does (besides spreading) • May involve damage or benign but noticeable activity ...
Document
... We know you use : Microsoft Windows 98 Your navigator has the code: Mozilla/4.78 [en] (Win98; U) In fact it is: Netscape Communicator 4.x English ...
... We know you use : Microsoft Windows 98 Your navigator has the code: Mozilla/4.78 [en] (Win98; U) In fact it is: Netscape Communicator 4.x English ...
William Stallings, Cryptography and Network Security 5/e
... The event or condition that determines when the payload is activated or delivered ...
... The event or condition that determines when the payload is activated or delivered ...
Victims who were Hacked PowerPoint Presentation
... What Anti-Virus Softwares Are Available For Businesses There are many anti-virus soft wares out there tailored to businesses. Such as: -AVG (Business Edition) -Bitdefender -McaAfee -Avira (Professional Security) (Endpoint Security) (Small Business Security Suite) (Business Security Suite) -And many ...
... What Anti-Virus Softwares Are Available For Businesses There are many anti-virus soft wares out there tailored to businesses. Such as: -AVG (Business Edition) -Bitdefender -McaAfee -Avira (Professional Security) (Endpoint Security) (Small Business Security Suite) (Business Security Suite) -And many ...
Antivirus Software
... that is unique for a particular input – For the same input, the checksum will not change unless the input changes ...
... that is unique for a particular input – For the same input, the checksum will not change unless the input changes ...
Computer Security Presentation
... offices. Drivers and applicants endured sometimes long waits at the newly overhauled New Jersey Motor Vehicle Commission's (MVC) offices on three days last week after a hard charging computer virus struck its statewide system. A survey conducted by Internet service provider America Online Inc. found ...
... offices. Drivers and applicants endured sometimes long waits at the newly overhauled New Jersey Motor Vehicle Commission's (MVC) offices on three days last week after a hard charging computer virus struck its statewide system. A survey conducted by Internet service provider America Online Inc. found ...
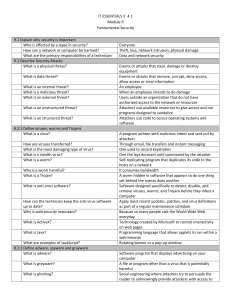
IT ESSENTIALS V. 4.1 Module 9 Fundamental Security 9.1 Explain
... Attackers use available resources to give access and run programs designed to vandalize Attackers use code to access operating systems and software A program written with malicious intent and sent out by attackers Through email, file transfers and instant messaging One used to record keystrokes One ...
... Attackers use available resources to give access and run programs designed to vandalize Attackers use code to access operating systems and software A program written with malicious intent and sent out by attackers Through email, file transfers and instant messaging One used to record keystrokes One ...
Crime and Security in the Networked Economy Part 4
... Encrypting Communications Increases Security ...
... Encrypting Communications Increases Security ...
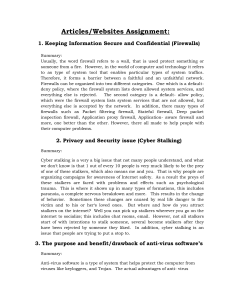
File
... we don’t know is that 1 out of every 10 people is very muck likely to be the prey of one of these stalkers, which also means me and you. That is why people are organizing campaigns for awareness of Internet safety. As a result the preys of these stalkers are faced with problems and effects such as p ...
... we don’t know is that 1 out of every 10 people is very muck likely to be the prey of one of these stalkers, which also means me and you. That is why people are organizing campaigns for awareness of Internet safety. As a result the preys of these stalkers are faced with problems and effects such as p ...
www.uob.edu.pk
... The event or condition that determines when the payload is activated or delivered ...
... The event or condition that determines when the payload is activated or delivered ...
File
... Viruses keep a low profile, so as to spread widely without being detected. Most of the time, the virus code simply infects new programs or disks. Eventually, often at a predefined date and time, the virus payload kicks in. Early virus payloads were often mindlessly destructive; these days they're mo ...
... Viruses keep a low profile, so as to spread widely without being detected. Most of the time, the virus code simply infects new programs or disks. Eventually, often at a predefined date and time, the virus payload kicks in. Early virus payloads were often mindlessly destructive; these days they're mo ...
Computer virus

A computer virus is a malware program that, when executed, replicates by inserting copies of itself (possibly modified) into other computer programs, data files, or the boot sector of the hard drive; when this replication succeeds, the affected areas are then said to be ""infected"". Viruses often perform some type of harmful activity on infected hosts, such as stealing hard disk space or CPU time, accessing private information, corrupting data, displaying political or humorous messages on the user's screen, spamming their contacts, logging their keystrokes, or even rendering the computer useless. However, not all viruses carry a destructive payload or attempt to hide themselves—the defining characteristic of viruses is that they are self-replicating computer programs which install themselves without user consent.Virus writers use social engineering and exploit detailed knowledge of security vulnerabilities to gain access to their hosts' computing resources. The vast majority of viruses target systems running Microsoft Windows, employing a variety of mechanisms to infect new hosts, and often using complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can include seeking profit, desire to send a political message, personal amusement, to demonstrate that a vulnerability exists in software, for sabotage and denial of service, or simply because they wish to explore artificial life and evolutionary algorithms.Computer viruses currently cause billions of dollars' worth of economic damage each year, due to causing systems failure, wasting computer resources, corrupting data, increasing maintenance costs, etc. In response, free, open-source antivirus tools have been developed, and an industry of antivirus software has cropped up, selling or freely distributing virus protection to users of various operating systems. Even though no currently existing antivirus software is able to uncover all computer viruses (especially new ones), computer security researchers are actively searching for new ways to enable antivirus solutions to more effectively detect emerging viruses, before they have already become widely distributed.