Chapter 6
... • Public-key systems provide several advantages over private-key systems: – The combination of keys required to provide private messages between enormous numbers of people is small – Key distribution is not a problem – Public-key systems make implementation of digital signatures possible ...
... • Public-key systems provide several advantages over private-key systems: – The combination of keys required to provide private messages between enormous numbers of people is small – Key distribution is not a problem – Public-key systems make implementation of digital signatures possible ...
pdf
... signature scheme: the master public key is a modulus N and an exponent e; the master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by us ...
... signature scheme: the master public key is a modulus N and an exponent e; the master secret key is d such that ed = 1 mod ϕ(N ). A user with identity ID is given secret key SKID = H(ID)d mod N (where H is modeled as a random oracle); this user can now sign messages with respect to his identity by us ...
notes
... Drawback: source must maintain two structures, hence needs additional complexity and overhead to maintain extra ...
... Drawback: source must maintain two structures, hence needs additional complexity and overhead to maintain extra ...
Presentation4 - University Of Worcester
... » method of checking incoming files to ensure that they are from a Microsoft approved source ...
... » method of checking incoming files to ensure that they are from a Microsoft approved source ...
Introduction to quantum cryptography
... • and telescopes with 8-inch mirrors to send and receive photons over the air. • Using the quantum transmitted key messages were encrypted at the rate 1 million bits per second. The speed was impressive but the distance between two NIST buildings was only 730 ...
... • and telescopes with 8-inch mirrors to send and receive photons over the air. • Using the quantum transmitted key messages were encrypted at the rate 1 million bits per second. The speed was impressive but the distance between two NIST buildings was only 730 ...
Section2.3
... alphabet is obtained by writing the letters of the resulting array column by column (starting with column 1) below the plaintext alphabet. ...
... alphabet is obtained by writing the letters of the resulting array column by column (starting with column 1) below the plaintext alphabet. ...
CryptoOddsAndEnds
... • when using end-to-end encryption must leave headers in clear – so network can correctly route information ...
... • when using end-to-end encryption must leave headers in clear – so network can correctly route information ...
Database Security
... Prompts for passwords for both the SYS and SYSTEM accounts on setup Both SYS and SYSTEM automatically have the DBA role • permits a user to create roles and users, grant privileges, etc. User accounts, roles, and privileges can be defined in several ways • Oracle Enterprise Manager Database Control ...
... Prompts for passwords for both the SYS and SYSTEM accounts on setup Both SYS and SYSTEM automatically have the DBA role • permits a user to create roles and users, grant privileges, etc. User accounts, roles, and privileges can be defined in several ways • Oracle Enterprise Manager Database Control ...
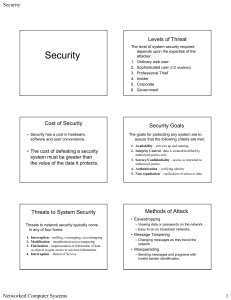
Security
... In 1976 Diffie & Hellman at Stanford U. developed public-key cryptography Asymmetric: – Private key – kept secret by owner – Public key – distributed freely to all who wish to send – Generated by computer algorithm, so a mathematical relation exists between them ... however ... – It is computational ...
... In 1976 Diffie & Hellman at Stanford U. developed public-key cryptography Asymmetric: – Private key – kept secret by owner – Public key – distributed freely to all who wish to send – Generated by computer algorithm, so a mathematical relation exists between them ... however ... – It is computational ...
Network Security For Distributed Simulation Systems
... 3: MS encrypts data with its private key and returns data to network ...
... 3: MS encrypts data with its private key and returns data to network ...
Devireddy
... TKIP resolves the key reuse in WEP by providing 128 bit “temporal key” in a dynamic way for securing data. It uses the same RC4 algorithm as WEP does and it is not considered as a long term solution. ...
... TKIP resolves the key reuse in WEP by providing 128 bit “temporal key” in a dynamic way for securing data. It uses the same RC4 algorithm as WEP does and it is not considered as a long term solution. ...
Enhancement of Security through a Cryptographic Algorithm
... passwords, and electronic commerce. In this paper, a mathematics-based, private-key, which we can call as decipher or decryption algorithm, is presented, which is modeled for implementing each character with a natural number. Section 2 explains the algorithm of encryption and decryption of the text ...
... passwords, and electronic commerce. In this paper, a mathematics-based, private-key, which we can call as decipher or decryption algorithm, is presented, which is modeled for implementing each character with a natural number. Section 2 explains the algorithm of encryption and decryption of the text ...
Secure Deduplication with Efficient and Reliable
... encrypting the convergent keys and outsourcing them to the cloud. However, such a baseline key management scheme generates an enormous number of keys with the increasing number of users and requires users to dedicatedly protect the master keys. To this end, we propose Dekey, a new construction in wh ...
... encrypting the convergent keys and outsourcing them to the cloud. However, such a baseline key management scheme generates an enormous number of keys with the increasing number of users and requires users to dedicatedly protect the master keys. To this end, we propose Dekey, a new construction in wh ...
Teaching Cryptologic Mathematics
... public-key ciphers may be introduced in a mathematics lesson by means of a real-life analogy on one-way streets where it is easy to go from a point P to another point Q, whereas it is practically impossible to go from Q to P. According to this equivalence, the public-key cipher may be viewed as the ...
... public-key ciphers may be introduced in a mathematics lesson by means of a real-life analogy on one-way streets where it is easy to go from a point P to another point Q, whereas it is practically impossible to go from Q to P. According to this equivalence, the public-key cipher may be viewed as the ...
Mod_7-Ch11
... – AES (Advanced Encryption Standard) • Keys can be 128, 192, or 256 bits • New standard ...
... – AES (Advanced Encryption Standard) • Keys can be 128, 192, or 256 bits • New standard ...
Gap Pad® 1500 - Bergquist Company
... WARRANTIES OF MARKETABILITY AND FITNESS FOR PURPOSE. Sellers’ and manufacturers’ only obligation shall be to replace such quantity of the product proved to be defective. Before using, user shall determine the suitability of the product for its intended use, and the user assumes all risks and liabili ...
... WARRANTIES OF MARKETABILITY AND FITNESS FOR PURPOSE. Sellers’ and manufacturers’ only obligation shall be to replace such quantity of the product proved to be defective. Before using, user shall determine the suitability of the product for its intended use, and the user assumes all risks and liabili ...
Three challenges with secret key encryption
... 1. What is “brute-force attack”? How the “brute-force attack” is related to Keyspace (the range of possible value of the Key)? Why the issue of number of bit required in a key to ensure secure encryption is controversial? A brute -force attack is applying all possible value of a key to the algorithm ...
... 1. What is “brute-force attack”? How the “brute-force attack” is related to Keyspace (the range of possible value of the Key)? Why the issue of number of bit required in a key to ensure secure encryption is controversial? A brute -force attack is applying all possible value of a key to the algorithm ...
Packaging Information: Data Compression and
... International Data Encryption Algorithm (IDEA) has been proposed to replace DES. It uses a 128-bit key. Longer keys make it more difficult for brute force discovery of the secret key ...
... International Data Encryption Algorithm (IDEA) has been proposed to replace DES. It uses a 128-bit key. Longer keys make it more difficult for brute force discovery of the secret key ...
MT311-14
... System security refers to the safety and stability of the computing environment. The safety and stability can be breached in a number of ways. When a malicious application (such as a virus) executes itself, it can cause damage to the system — for example, by deleting some critical files and renderin ...
... System security refers to the safety and stability of the computing environment. The safety and stability can be breached in a number of ways. When a malicious application (such as a virus) executes itself, it can cause damage to the system — for example, by deleting some critical files and renderin ...
Ecommerce: Security and Control
... – because it use Mathematics to calculate the key. Public key cryptography uses two keys, rather than one – hence, sometimes referred to asymmetric. Symmetric encryption is still in use, and will continue to be This is because of the computational overhead associated with public key encryption ...
... – because it use Mathematics to calculate the key. Public key cryptography uses two keys, rather than one – hence, sometimes referred to asymmetric. Symmetric encryption is still in use, and will continue to be This is because of the computational overhead associated with public key encryption ...
Slides on Security
... • Firewalls can be implemented in a router. • A firewall can restrict certain types of traffic activity on a network based on: – Source or destination IP address ...
... • Firewalls can be implemented in a router. • A firewall can restrict certain types of traffic activity on a network based on: – Source or destination IP address ...
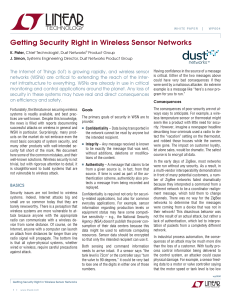
Getting Security Right in Wireless Sensor Networks
... The simplest solution to this reverse-engineering problem is to ensure that every communication session (or flow of data between two endpoints) has its own unique keys that are unknown to any other nodes in the network. In this case, even a compromised node in the network cannot snoop, manipulate, o ...
... The simplest solution to this reverse-engineering problem is to ensure that every communication session (or flow of data between two endpoints) has its own unique keys that are unknown to any other nodes in the network. In this case, even a compromised node in the network cannot snoop, manipulate, o ...
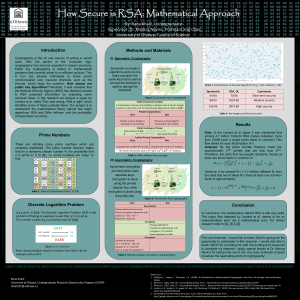
Genigraphics Research Poster Template 44x44
... unknown flaws. In this research we analyze a paper by Lenstra et al. called "Ron was wrong, Whit is right" which identifies some of these potential flaws. Our project is to understand the mathematical theory behind two major algorithms: RSA and Diffie Hellman, with the probability of these flaws occ ...
... unknown flaws. In this research we analyze a paper by Lenstra et al. called "Ron was wrong, Whit is right" which identifies some of these potential flaws. Our project is to understand the mathematical theory behind two major algorithms: RSA and Diffie Hellman, with the probability of these flaws occ ...
One-time pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked if used correctly. In this technique, a plaintext is paired with a random secret key (also referred to as a one-time pad). Then, each bit or character of the plaintext is encrypted by combining it with the corresponding bit or character from the pad using modular addition. If the key is truly random, is at least as long as the plaintext, is never reused in whole or in part, and is kept completely secret, then the resulting ciphertext will be impossible to decrypt or break. It has also been proven that any cipher with the perfect secrecy property must use keys with effectively the same requirements as OTP keys. However, practical problems have prevented one-time pads from being widely used.First described by Frank Miller in 1882, the one-time pad was re-invented in 1917. On July 22, 1919, U.S. Patent 1,310,719 was issued to Gilbert S. Vernam for the XOR operation used for the encryption of a one-time pad. It is derived from the Vernam cipher, named after Gilbert Vernam, one of its inventors. Vernam's system was a cipher that combined a message with a key read from a punched tape. In its original form, Vernam's system was vulnerable because the key tape was a loop, which was reused whenever the loop made a full cycle. One-time use came later, when Joseph Mauborgne recognized that if the key tape were totally random, then cryptanalysis would be impossible.The ""pad"" part of the name comes from early implementations where the key material was distributed as a pad of paper, so that the top sheet could be easily torn off and destroyed after use. For ease of concealment, the pad was sometimes reduced to such a small size that a powerful magnifying glass was required to use it. The KGB used pads of such size that they could fit in the palm of one's hand, or in a walnut shell. To increase security, one-time pads were sometimes printed onto sheets of highly flammable nitrocellulose, so that they could be quickly burned after use.There is some ambiguity to the term because some authors use the terms ""Vernam cipher"" and ""one-time pad"" synonymously, while others refer to any additive stream cipher as a ""Vernam cipher"", including those based on a cryptographically secure pseudorandom number generator (CSPRNG).