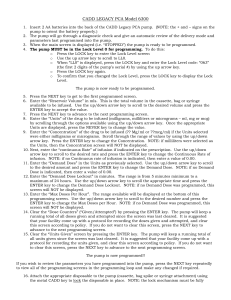
CADD LEGACY PCA Model 6300
... The pump is now ready to be programmed. 5. Press the NEXT key to get to the first programmed screen. 6. Enter the “Reservoir Volume” in mls. This is the total volume in the cassette, bag or syringe available to be infused. Use the up/down arrow key to scroll to the desired volume and press the ENTER ...
... The pump is now ready to be programmed. 5. Press the NEXT key to get to the first programmed screen. 6. Enter the “Reservoir Volume” in mls. This is the total volume in the cassette, bag or syringe available to be infused. Use the up/down arrow key to scroll to the desired volume and press the ENTER ...
Statistical Models for Steganography - uni
... Larger the cover message – Easier to hide message ...
... Larger the cover message – Easier to hide message ...
COS 338_day17
... Protection A can reduce the annual probability of damage by 50% ($2,500) If Protection A costs $1,000 per year, use it. If Protection A costs $4,000 per year, don’t use it. ...
... Protection A can reduce the annual probability of damage by 50% ($2,500) If Protection A costs $1,000 per year, use it. If Protection A costs $4,000 per year, don’t use it. ...
EAP
... • Easily encapsulated within any data link protocol • Provides a generalized framework for all sorts of authentication methods. • Simpler interoperability and compatibility across authentication methods • For example, when you dial a remote access server(RAS) and use EAP as part of your PPP connecti ...
... • Easily encapsulated within any data link protocol • Provides a generalized framework for all sorts of authentication methods. • Simpler interoperability and compatibility across authentication methods • For example, when you dial a remote access server(RAS) and use EAP as part of your PPP connecti ...
Internet Control Message Protocol
... important, as is correctly handling error conditions within the network routing itself. The Internet Control Message Protocol (ICMP) was developed for this task. ICMP is an error-reporting system. It is an integral part of IP and must be included in every IP implementation. This provides for consist ...
... important, as is correctly handling error conditions within the network routing itself. The Internet Control Message Protocol (ICMP) was developed for this task. ICMP is an error-reporting system. It is an integral part of IP and must be included in every IP implementation. This provides for consist ...
A. Message syntax
... defined in the xTEDS document, followed by an IP address (4 bytes) and a port number (2 bytes). Reply expected: Data (D) or Status (S) if request cannot be honored. SPECIAL CASE: If a data message is specified in xTEDS as having an external source (SOURCE=”EXTERNAL”), no reply is expected directly f ...
... defined in the xTEDS document, followed by an IP address (4 bytes) and a port number (2 bytes). Reply expected: Data (D) or Status (S) if request cannot be honored. SPECIAL CASE: If a data message is specified in xTEDS as having an external source (SOURCE=”EXTERNAL”), no reply is expected directly f ...
Practice Questions with Solutions
... 27. The reason that two-factor authentication is preferable over ordinary authentication is: a. Two-factor authentication is more difficult to crack b. It relies upon something the user knows c. It relies upon something that the user has d. Two-factor authentication uses stronger encryption algorit ...
... 27. The reason that two-factor authentication is preferable over ordinary authentication is: a. Two-factor authentication is more difficult to crack b. It relies upon something the user knows c. It relies upon something that the user has d. Two-factor authentication uses stronger encryption algorit ...
Hybrid cryptography using symmetric key encryption
... Step8: Decrypt the file to obtain the original file. Step9: Stop Thus from the above results we can see the encryption takes a little longer, but has more security. When all the three are implemented separately, we can also conclude that the error probability influences the output to get 100% satisf ...
... Step8: Decrypt the file to obtain the original file. Step9: Stop Thus from the above results we can see the encryption takes a little longer, but has more security. When all the three are implemented separately, we can also conclude that the error probability influences the output to get 100% satisf ...
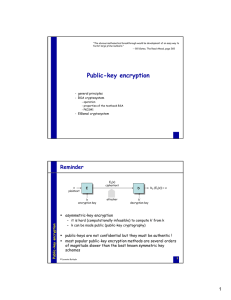
Public-key encryption
... this attack can be circumvented by imposing some structural constraints on plaintext messages – e.g., a plaintext must start with a well-known constant bit string – since r is random, m⋅r (mod n) will not have the right structure with very high probability, and Alice can refuse to respond ...
... this attack can be circumvented by imposing some structural constraints on plaintext messages – e.g., a plaintext must start with a well-known constant bit string – since r is random, m⋅r (mod n) will not have the right structure with very high probability, and Alice can refuse to respond ...
The key questions that we`d like to ask at the beginning
... In simple terms, PFS provides an added layer of security even if an eavesdropper listens in on your entire conversation. Because if a hacker does manage to gain access to the private key, he still won’t be able to recover the shared, short-term secret key and will not be able to decrypt any communi ...
... In simple terms, PFS provides an added layer of security even if an eavesdropper listens in on your entire conversation. Because if a hacker does manage to gain access to the private key, he still won’t be able to recover the shared, short-term secret key and will not be able to decrypt any communi ...
PK b
... (claim 1) The probability that B does not abort as a result of A’s trapdoor queries is at least 1/e. Hence, Pr[E1] ≧ 1/e. Pf: B will abort only when ci=0 and Pr[ci=0]=1/(qT+1), and the other parameters are independent with ci. Since A makes at most qT trapdoor queries, B does not abort as a result o ...
... (claim 1) The probability that B does not abort as a result of A’s trapdoor queries is at least 1/e. Hence, Pr[E1] ≧ 1/e. Pf: B will abort only when ci=0 and Pr[ci=0]=1/(qT+1), and the other parameters are independent with ci. Since A makes at most qT trapdoor queries, B does not abort as a result o ...
Apply encryption to network and system security
... Encryption is the process of taking some information or data, manipulating or changing its format in a way that stops it from being used or read by unauthorized people or systems. Encryption involves scrambling data so that it needs to be unscrambled, or decrypted, to be read. Encryption can be appl ...
... Encryption is the process of taking some information or data, manipulating or changing its format in a way that stops it from being used or read by unauthorized people or systems. Encryption involves scrambling data so that it needs to be unscrambled, or decrypted, to be read. Encryption can be appl ...
ppt
... If you have resources which are cached at the server (e.g. an SSL session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the same client are repeatedly satisfied by the same server during this session. The trade off is that the loa ...
... If you have resources which are cached at the server (e.g. an SSL session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the same client are repeatedly satisfied by the same server during this session. The trade off is that the loa ...
IPSEC Presentation
... • A collection of protocols for securing Internet Protocol (IP) communications by encrypting and authenticating all IP packets1 • Progressive standard • Defined in RFC 2401 thru 2409 • Purpose: – To protect IP packets – To provide defense against network attacks 1: From wikipedia.org ...
... • A collection of protocols for securing Internet Protocol (IP) communications by encrypting and authenticating all IP packets1 • Progressive standard • Defined in RFC 2401 thru 2409 • Purpose: – To protect IP packets – To provide defense against network attacks 1: From wikipedia.org ...
Chapter 9
... source quench for slowing down rate of transmission redirection for requesting a change in a routing table echo request/reply for checking destination reachability solicitation and advertisement for defaults in routing ...
... source quench for slowing down rate of transmission redirection for requesting a change in a routing table echo request/reply for checking destination reachability solicitation and advertisement for defaults in routing ...
Public-Key Cryptosystems Based on Hard Problems
... but it raised dust. Just name only a few up to date happenings. Cryptography is one of the two main branches of cryptology. It is the science which aim is to hiding the meaning of a message. Meanwhile the other one, cryptoanalysis deals with breaking cryptosystems. Cryptography is also can be splitt ...
... but it raised dust. Just name only a few up to date happenings. Cryptography is one of the two main branches of cryptology. It is the science which aim is to hiding the meaning of a message. Meanwhile the other one, cryptoanalysis deals with breaking cryptosystems. Cryptography is also can be splitt ...
6.1. Elliptic Curve Cryptography
... The purpose of cryptography is to transmit information in such a way that access to it is restricted entirely to the intended recipient. Originally the security of a cryptotext depended on the secrecy of the entire encrypting and decrypting procedures; however, today we use ciphers for which the alg ...
... The purpose of cryptography is to transmit information in such a way that access to it is restricted entirely to the intended recipient. Originally the security of a cryptotext depended on the secrecy of the entire encrypting and decrypting procedures; however, today we use ciphers for which the alg ...
Unit 11
... • unauthorized traffic saturates a network’s resources, restricting access for legitimate users • typical: flood servers with data packets ...
... • unauthorized traffic saturates a network’s resources, restricting access for legitimate users • typical: flood servers with data packets ...
Secure Email
... privacy (only the intended recipient can read the message) and authentication (the recipient can be assured of the identity of the sender). The technical capabilities for these functions has been known for many years, but they have only been applied to Internet mail recently. – Reality Check: Securi ...
... privacy (only the intended recipient can read the message) and authentication (the recipient can be assured of the identity of the sender). The technical capabilities for these functions has been known for many years, but they have only been applied to Internet mail recently. – Reality Check: Securi ...
For the following exercise determine the range (possible values) of
... Here the random variable is defined as: X = percent moisture content of a lot of raw material The range of the random variable is the set of all possible numbers which can be assigned to the random variable. The notation associated with the range is the lower case letter corresponding to the random ...
... Here the random variable is defined as: X = percent moisture content of a lot of raw material The range of the random variable is the set of all possible numbers which can be assigned to the random variable. The notation associated with the range is the lower case letter corresponding to the random ...
Cryptanalysis of Stream Cipher
... No security reduction but easy to analyze Not resistant to nonce reuse No incremental tags Flexible implementation sizes: 128/256 Performance: speed/size ...
... No security reduction but easy to analyze Not resistant to nonce reuse No incremental tags Flexible implementation sizes: 128/256 Performance: speed/size ...
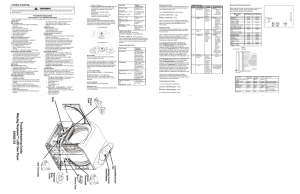
Troubleshooting Guide Maytag Neptune™ LED Gas Dryer 6390 2110
... keys for 2 seconds, will start a Membrane Pad Switch Test. To exit the test at any point, press the same keys again for 2 seconds or press the OFF key to exit Service Mode. Diagnostic Codes The Diagnostic Codes are identified when the severity level of the abnormality detected is higher and service ...
... keys for 2 seconds, will start a Membrane Pad Switch Test. To exit the test at any point, press the same keys again for 2 seconds or press the OFF key to exit Service Mode. Diagnostic Codes The Diagnostic Codes are identified when the severity level of the abnormality detected is higher and service ...
One-time pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked if used correctly. In this technique, a plaintext is paired with a random secret key (also referred to as a one-time pad). Then, each bit or character of the plaintext is encrypted by combining it with the corresponding bit or character from the pad using modular addition. If the key is truly random, is at least as long as the plaintext, is never reused in whole or in part, and is kept completely secret, then the resulting ciphertext will be impossible to decrypt or break. It has also been proven that any cipher with the perfect secrecy property must use keys with effectively the same requirements as OTP keys. However, practical problems have prevented one-time pads from being widely used.First described by Frank Miller in 1882, the one-time pad was re-invented in 1917. On July 22, 1919, U.S. Patent 1,310,719 was issued to Gilbert S. Vernam for the XOR operation used for the encryption of a one-time pad. It is derived from the Vernam cipher, named after Gilbert Vernam, one of its inventors. Vernam's system was a cipher that combined a message with a key read from a punched tape. In its original form, Vernam's system was vulnerable because the key tape was a loop, which was reused whenever the loop made a full cycle. One-time use came later, when Joseph Mauborgne recognized that if the key tape were totally random, then cryptanalysis would be impossible.The ""pad"" part of the name comes from early implementations where the key material was distributed as a pad of paper, so that the top sheet could be easily torn off and destroyed after use. For ease of concealment, the pad was sometimes reduced to such a small size that a powerful magnifying glass was required to use it. The KGB used pads of such size that they could fit in the palm of one's hand, or in a walnut shell. To increase security, one-time pads were sometimes printed onto sheets of highly flammable nitrocellulose, so that they could be quickly burned after use.There is some ambiguity to the term because some authors use the terms ""Vernam cipher"" and ""one-time pad"" synonymously, while others refer to any additive stream cipher as a ""Vernam cipher"", including those based on a cryptographically secure pseudorandom number generator (CSPRNG).