Lect 1 - Intro
... Some additional aspects are often mentioned: Authenticity: • The property of being genuine and able to be verified • Confidence in the validity of a transmission, verifiability of a message originator, inputs arriving from trusted sources • Verifiability of a user’s identity Accountability: • Acti ...
... Some additional aspects are often mentioned: Authenticity: • The property of being genuine and able to be verified • Confidence in the validity of a transmission, verifiability of a message originator, inputs arriving from trusted sources • Verifiability of a user’s identity Accountability: • Acti ...
CNG 131 – Principles of Information Assurance Provides students
... CNG 131 – Principles of Information Assurance Provides students with the skills and knowledge required to survey key issues associated with protecting information assets, determine the levels of protection and response to security incidents, and design a consistent, reasonable information security s ...
... CNG 131 – Principles of Information Assurance Provides students with the skills and knowledge required to survey key issues associated with protecting information assets, determine the levels of protection and response to security incidents, and design a consistent, reasonable information security s ...
Chapter 5 Protecting Information Resources
... Enables the designer or programmer to bypass system security and sneak back into the system later to access programs or files System users aren’t aware a backdoor has ...
... Enables the designer or programmer to bypass system security and sneak back into the system later to access programs or files System users aren’t aware a backdoor has ...
Information Security - National University of Sciences and
... • Attaches itself to some host program e.g. a word document • Executes when word document is opened • Make copies of itself by attaching itself by other host programs • Can do all sorts of damage • Fill up storage and memory, modify/destroy data, erase hard disk ...
... • Attaches itself to some host program e.g. a word document • Executes when word document is opened • Make copies of itself by attaching itself by other host programs • Can do all sorts of damage • Fill up storage and memory, modify/destroy data, erase hard disk ...
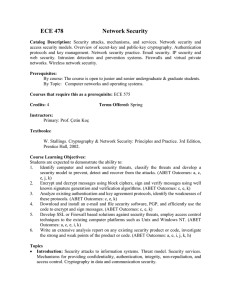
Course Learning Objectives:
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
download
... • origin, destination • protection against denial by one of the parties in a communication ...
... • origin, destination • protection against denial by one of the parties in a communication ...
Richard D - Expert Witness Network
... participated in a multitude of classified worldwide taskings in support of U.S. and foreign governments, militaries, and agencies while assigned in a myriad of sensitive billets and was a founding member of the Navy’s first counter-terrorist team. As an original member of the Naval Security Coordina ...
... participated in a multitude of classified worldwide taskings in support of U.S. and foreign governments, militaries, and agencies while assigned in a myriad of sensitive billets and was a founding member of the Navy’s first counter-terrorist team. As an original member of the Naval Security Coordina ...
Shawn Bracken - CISSP103 Chester StMenlo Park, CA 94025
... 1998, Response Center Engineer, Hewlett Packard Company, Roseville, CA. Member of the backline-utilities team in HP's response center supporting HP-UX. Supported HP-UX Trusted Systems secure accounting/auditing and kernel configuration Our team was the 3rd layer support known as "backline" whi ...
... 1998, Response Center Engineer, Hewlett Packard Company, Roseville, CA. Member of the backline-utilities team in HP's response center supporting HP-UX. Supported HP-UX Trusted Systems secure accounting/auditing and kernel configuration Our team was the 3rd layer support known as "backline" whi ...
Federal Bio
... Mr. Crane is located in Washington, DC where works for the Department of Homeland Security. Previously Mr. Crane was a Senior Information Security Consultant with Foundstone, a wholly owned subsidiary of McAfee, Inc. There he created and led the Information Security Management program. Service line ...
... Mr. Crane is located in Washington, DC where works for the Department of Homeland Security. Previously Mr. Crane was a Senior Information Security Consultant with Foundstone, a wholly owned subsidiary of McAfee, Inc. There he created and led the Information Security Management program. Service line ...
Alice and Bob Get Physical: Insights into Physical Layer Security
... About the Talk Although conventional cryptographic security mechanisms are essential to the overall problem of securing wireless networks, these techniques do not directly leverage the unique properties of the wireless domain to address security threats. The properties of the wireless medium are a p ...
... About the Talk Although conventional cryptographic security mechanisms are essential to the overall problem of securing wireless networks, these techniques do not directly leverage the unique properties of the wireless domain to address security threats. The properties of the wireless medium are a p ...
Skating on Stilts
... Attacker: Many report government-style attacks •Half report “stealthy infiltration by high-level adversary … like in Ghostnet” ...
... Attacker: Many report government-style attacks •Half report “stealthy infiltration by high-level adversary … like in Ghostnet” ...
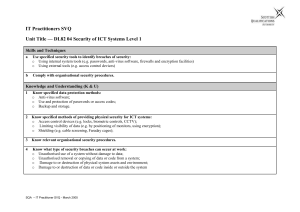
it user svq – level 2
... o Access control devices (e.g. locks, biometric controls, CCTV); o Limiting visibility of data (e.g. by positioning of monitors, using encryption); o Shielding (e.g. cable screening, Faraday cages); ...
... o Access control devices (e.g. locks, biometric controls, CCTV); o Limiting visibility of data (e.g. by positioning of monitors, using encryption); o Shielding (e.g. cable screening, Faraday cages); ...
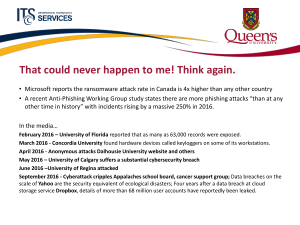
Cybersecurity - Queen`s Wiki
... • Microsoft reports the ransomware attack rate in Canada is 4x higher than any other country • A recent Anti-Phishing Working Group study states there are more phishing attacks “than at any other time in history” with incidents rising by a massive 250% in 2016. ...
... • Microsoft reports the ransomware attack rate in Canada is 4x higher than any other country • A recent Anti-Phishing Working Group study states there are more phishing attacks “than at any other time in history” with incidents rising by a massive 250% in 2016. ...
Why Cryptography is Harder Than It Looks
... • A good system balances actual failures against potential failures • Non-invasive attacks CAN be totally prevented • Targeted attacks can only be withstood up to a point • The problems with cryptography are not in the algorithms and protocols, but the implementation – Weakness are found at human in ...
... • A good system balances actual failures against potential failures • Non-invasive attacks CAN be totally prevented • Targeted attacks can only be withstood up to a point • The problems with cryptography are not in the algorithms and protocols, but the implementation – Weakness are found at human in ...
Enter Title in Docm Properties
... Job Category: Engineering/Software/Technical Company: Tofino Security (a subsidiary of Belden Inc.) is an internationally recognized team of security, software development and control systems professionals dedicated to defending critical Supervisory Control and Data Acquisition (SCADA) and industria ...
... Job Category: Engineering/Software/Technical Company: Tofino Security (a subsidiary of Belden Inc.) is an internationally recognized team of security, software development and control systems professionals dedicated to defending critical Supervisory Control and Data Acquisition (SCADA) and industria ...
Security
... The Security Problem A system is secure if its resources are used and accessed as intended under all circumstances. Security violations can be accidental (easier to protect) or intentional (malicious) (harder to protect). Some accidental and malicious security violations are: Confidentiality breach ...
... The Security Problem A system is secure if its resources are used and accessed as intended under all circumstances. Security violations can be accidental (easier to protect) or intentional (malicious) (harder to protect). Some accidental and malicious security violations are: Confidentiality breach ...
Proposed Part 73 Fuel Cycle Facility Security Rulemaking
... Background • 10 CFR Part 73, Physical Protection of Plants and Materials, has been revised subpart-by-subpart over the last 25 years • Lessons learned ((e.g., g threat and implementation)) • Commission directed engagement of a “broad” range of stakeholders ...
... Background • 10 CFR Part 73, Physical Protection of Plants and Materials, has been revised subpart-by-subpart over the last 25 years • Lessons learned ((e.g., g threat and implementation)) • Commission directed engagement of a “broad” range of stakeholders ...
Network Security Analysis Prepared By: cowave Communication
... security covers with customized solutions. 2. Security solutions should be one of the best who ...
... security covers with customized solutions. 2. Security solutions should be one of the best who ...
cisco.camre.ac.uk
... Preventing a security incursion, like the attacks themselves, is a constantly evolving process. The security measures described in the next series of lesson are a sample of those in use and are an introduction to what you may be expected to use in the ICT industry. ...
... Preventing a security incursion, like the attacks themselves, is a constantly evolving process. The security measures described in the next series of lesson are a sample of those in use and are an introduction to what you may be expected to use in the ICT industry. ...
One Team, One Fight
... Deputy Under Secretary for Cybersecurity and Communications Department of Homeland Security ...
... Deputy Under Secretary for Cybersecurity and Communications Department of Homeland Security ...
Airport security
Airport security refers to the techniques and methods used in protecting passengers, staff and aircraft which use the airports from accidental/malicious harm, crime and other threats.