OfficeServ 7400 GWIMT/GWIM User Manual
... The number of IPs for the ‘Local IP range’ and that for the ‘Remote IP range’ should be identical when setting PPTP VPN. For example, if the number of IPs for ‘Local IP range’ is 10 and that for ‘Remote IP range’ is 20, only 10 calls will be set. ...
... The number of IPs for the ‘Local IP range’ and that for the ‘Remote IP range’ should be identical when setting PPTP VPN. For example, if the number of IPs for ‘Local IP range’ is 10 and that for ‘Remote IP range’ is 20, only 10 calls will be set. ...
Brocade VDX 6940 Switch data sheet
... support dynamic growth in Virtual Machines (VMs), distributed applications, and Big Data, as well as the transition to cloudbased computing—without compromising performance. However, traditional data centers typically use inflexible, three-tier network designs that cannot efficiently manage east-wes ...
... support dynamic growth in Virtual Machines (VMs), distributed applications, and Big Data, as well as the transition to cloudbased computing—without compromising performance. However, traditional data centers typically use inflexible, three-tier network designs that cannot efficiently manage east-wes ...
Chapter 1 - Introduction
... a datagram header and the address of the next hop to which the datagram is forwarded? • The DESTINATION IP ADDRESS field in a datagram contains the address of the ultimate destination – it does not change as the datagram passes through the Internet ...
... a datagram header and the address of the next hop to which the datagram is forwarded? • The DESTINATION IP ADDRESS field in a datagram contains the address of the ultimate destination – it does not change as the datagram passes through the Internet ...
Chapter 1 - Introduction
... a datagram header and the address of the next hop to which the datagram is forwarded? • The DESTINATION IP ADDRESS field in a datagram contains the address of the ultimate destination – it does not change as the datagram passes through the Internet ...
... a datagram header and the address of the next hop to which the datagram is forwarded? • The DESTINATION IP ADDRESS field in a datagram contains the address of the ultimate destination – it does not change as the datagram passes through the Internet ...
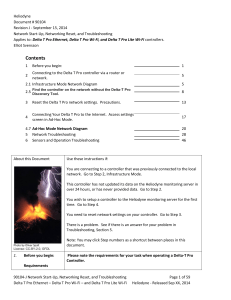
Contents - Heliodyne
... laptop to the same subnet/router as the Delta T Pro controller using either Ethernet cables or Wi-Fi. You may use either method to connect ...
... laptop to the same subnet/router as the Delta T Pro controller using either Ethernet cables or Wi-Fi. You may use either method to connect ...
ATM End User
... Remark: Signaling between the end-system and the ATM switch usually takes place over VPI=0 and VCI=5, although this is not always the case. If we implement a feature such as SVC tunneling, the signaling channel will often be over a VPI =/ 0. Also, some proprietary UNI and NNI protocols use VCI =/5 f ...
... Remark: Signaling between the end-system and the ATM switch usually takes place over VPI=0 and VCI=5, although this is not always the case. If we implement a feature such as SVC tunneling, the signaling channel will often be over a VPI =/ 0. Also, some proprietary UNI and NNI protocols use VCI =/5 f ...
"Resilient Overlay Networks"
... by without some serious problem affecting the connectivity provided by one or more Internet Service Providers (ISPs) [15]. Resilient Overlay Networks (RONs) are a remedy for some of these problems. Distributed applications layer a “resilient overlay network” over the underlying Internet routing subs ...
... by without some serious problem affecting the connectivity provided by one or more Internet Service Providers (ISPs) [15]. Resilient Overlay Networks (RONs) are a remedy for some of these problems. Distributed applications layer a “resilient overlay network” over the underlying Internet routing subs ...
DutyCon: A dynamic duty-cycle control approach to end
... DutyCon: A Dynamic Duty-Cycle Control Approach to End-to-End Delay Guarantees in Wireless Sensor Networks XIAODONG WANG, XIAORUI WANG, and LIU LIU, The Ohio State University GUOLIANG XING, Michigan State University ...
... DutyCon: A Dynamic Duty-Cycle Control Approach to End-to-End Delay Guarantees in Wireless Sensor Networks XIAODONG WANG, XIAORUI WANG, and LIU LIU, The Ohio State University GUOLIANG XING, Michigan State University ...
High Availability WLANs Based on Software-Defined
... Recently, the software defined networking (SDN) has attracted a lot of interest. The main characteristics of SDN is to decouple the control and data planes of a network and provide the freedom of programmability to development more efficient network applications [1]. Furthermore, the SDN also result ...
... Recently, the software defined networking (SDN) has attracted a lot of interest. The main characteristics of SDN is to decouple the control and data planes of a network and provide the freedom of programmability to development more efficient network applications [1]. Furthermore, the SDN also result ...
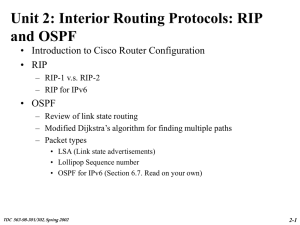
TDC 563-98-301/302, Spring 2002 2-14 TDC 563-98
... •The running configuration is stored in RAM. •Any configuration changes to the router are made to the running-configuration and take effect immediately after the command is entered. •The startup-configuration is saved in NVRAM and is loaded into the router's runningconfiguration when the router boot ...
... •The running configuration is stored in RAM. •Any configuration changes to the router are made to the running-configuration and take effect immediately after the command is entered. •The startup-configuration is saved in NVRAM and is loaded into the router's runningconfiguration when the router boot ...
Advanced Networking: Network Address Translation (NAT)
... • STUN-enabled hosts send an exploratory message to the external STUN server to determine the transmit and receive ports to use • The STUN server examines the incoming message and informs the client which public IP address and ports were used by the NAT • These are communicated to e.g. – SIP proxies ...
... • STUN-enabled hosts send an exploratory message to the external STUN server to determine the transmit and receive ports to use • The STUN server examines the incoming message and informs the client which public IP address and ports were used by the NAT • These are communicated to e.g. – SIP proxies ...
Computer Networking : Principles, Protocols and Practice Release
... Computer networks have used various types of physical media to exchange information, notably : • electrical cable. Information can be transmitted over different types of electrical cables. The most common ones are the twisted pairs (that are used in the telephone network, but also in enterprise netw ...
... Computer networks have used various types of physical media to exchange information, notably : • electrical cable. Information can be transmitted over different types of electrical cables. The most common ones are the twisted pairs (that are used in the telephone network, but also in enterprise netw ...
Apple Bonjour Services on the Cisco mDNS Enabled Controllers
... Another enhancement added in PI 2.2 is the capability of the Administrator or another pre-provisioned user to manage access privilege per service instance via the Cisco Prime Infrastructure portal. Imagine if the IT Administrator of a school allows each teacher privileges to access the Apple TVs in ...
... Another enhancement added in PI 2.2 is the capability of the Administrator or another pre-provisioned user to manage access privilege per service instance via the Cisco Prime Infrastructure portal. Imagine if the IT Administrator of a school allows each teacher privileges to access the Apple TVs in ...
Chromecast Deployment Guide, Release 7.6 Introduction
... devices, while still enabling Chromecast for use by a specific set of clients on a different VLAN. The specific set of clients can be assigned to a VLAN using AAA override. For example, consider a University campus with Chromecast devices installed in each classroom. The administrator wants to desig ...
... devices, while still enabling Chromecast for use by a specific set of clients on a different VLAN. The specific set of clients can be assigned to a VLAN using AAA override. For example, consider a University campus with Chromecast devices installed in each classroom. The administrator wants to desig ...
Release Notes for RingMaster Version 7.7.3.1
... Serial Numbers, and Authorization Codes. Software Serial numbers are sent when you order a base system (e.g., WLM-RTMS). Authorization Codes ( "AuthCodes") are sent when an additional capacity or feature is ordered. Both token types are transacted at the Juniper Networks License Management System (L ...
... Serial Numbers, and Authorization Codes. Software Serial numbers are sent when you order a base system (e.g., WLM-RTMS). Authorization Codes ( "AuthCodes") are sent when an additional capacity or feature is ordered. Both token types are transacted at the Juniper Networks License Management System (L ...
Aalborg Universitet Adaptive Capacity Management in Bluetooth Networks Son, L.T.
... in short radio range, highly dynamic network environment, low power, and scarce resources, many new research challenges occur, such as limited wireless bandwidth operation, routing, scheduling, network control, etc. Currently Bluetooth specification particularly does not describe in details about ho ...
... in short radio range, highly dynamic network environment, low power, and scarce resources, many new research challenges occur, such as limited wireless bandwidth operation, routing, scheduling, network control, etc. Currently Bluetooth specification particularly does not describe in details about ho ...
Configuring VoIP for SonicOS Enhanced
... of voice and data networks. VoIP security and network integrity are an essential part of any VoIP deployment. The same security threats that plague data networks today are inherited by VoIP but the addition of VoIP as an application on the network makes those threats even more dangerous. By adding V ...
... of voice and data networks. VoIP security and network integrity are an essential part of any VoIP deployment. The same security threats that plague data networks today are inherited by VoIP but the addition of VoIP as an application on the network makes those threats even more dangerous. By adding V ...
Where is the collision domain?
... An entry in the bridge table consists of : Node LAN (MAC) Address, Bridge Interface to which the node is connected to, the record creation time ...
... An entry in the bridge table consists of : Node LAN (MAC) Address, Bridge Interface to which the node is connected to, the record creation time ...
Lecture 8 - cda college
... Solves congestion problems Helps segment networks Provides high-speed connectivity to desktop ...
... Solves congestion problems Helps segment networks Provides high-speed connectivity to desktop ...
Slide 1
... environment database, AIS, MET information and revision of information on real-time basis etc. SWIM will support operational and administrative applications SWIM has already been adopted by FAA for its NextGen and EUROCONTRO for their SESAR program AMHS WORKSHOP ...
... environment database, AIS, MET information and revision of information on real-time basis etc. SWIM will support operational and administrative applications SWIM has already been adopted by FAA for its NextGen and EUROCONTRO for their SESAR program AMHS WORKSHOP ...
ECE/CS 4984: Lecture 11
... ● Delay is often very high ■ Round-trip time can be very long and variable ■ TCP’s timeout mechanisms may not work well ■ Problem exacerbated by link-level retransmission ● Links may be asymmetric ■ Delayed ACKs in the slow direction can limit throughput in the fast direction ...
... ● Delay is often very high ■ Round-trip time can be very long and variable ■ TCP’s timeout mechanisms may not work well ■ Problem exacerbated by link-level retransmission ● Links may be asymmetric ■ Delayed ACKs in the slow direction can limit throughput in the fast direction ...
Linksys E3000 User Guide
... Setup and use of the Router is easy using Cisco Connect, the software that is installed when you run the included CD. Advanced configuration of the Router is available through the provided browser‑based utility. For more wireless bandwidth, the Router can create two simultaneous yet separate Wireles ...
... Setup and use of the Router is easy using Cisco Connect, the software that is installed when you run the included CD. Advanced configuration of the Router is available through the provided browser‑based utility. For more wireless bandwidth, the Router can create two simultaneous yet separate Wireles ...