International Technical Support Organization Asynchronous
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1995. All rights reserved. Note to U.S. Government Users — Do ...
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1995. All rights reserved. Note to U.S. Government Users — Do ...
PDF
... Most attacks against BGP share a single goal: gaining control over traffic to one or more prefixes from one or more routers. Attackers might have any of several motives for doing so: eavesdropping, spoofing, denial of service, or simply increasing the volume of traffic carried over a particular netw ...
... Most attacks against BGP share a single goal: gaining control over traffic to one or more prefixes from one or more routers. Attackers might have any of several motives for doing so: eavesdropping, spoofing, denial of service, or simply increasing the volume of traffic carried over a particular netw ...
S9700 Series Terabit Routing Switches
... upstream transmissions. The S5700 can be used in various enterprise network scenarios. For example, it can function as an access or aggregation switch on a campus network, a gigabit access switch in an Internet data center (IDC), or a desktop switch to provide 1000 Mbit/s access for terminals. The S ...
... upstream transmissions. The S5700 can be used in various enterprise network scenarios. For example, it can function as an access or aggregation switch on a campus network, a gigabit access switch in an Internet data center (IDC), or a desktop switch to provide 1000 Mbit/s access for terminals. The S ...
Drafting Behind Akamai - Northwestern University
... Independent measurements – Redundant – Non-scalable – Can cause problems • E.g., synchronization ...
... Independent measurements – Redundant – Non-scalable – Can cause problems • E.g., synchronization ...
VoIP
... audio VOIP PDU’s divided into smaller units, e.g. four 5 msec units per 20 msec audio VOIP PDU PDU contains small units from different VOIP PDU’s if PDU lost, still have most of every original VOIP PDU no redundancy overhead, but increases playout delay ...
... audio VOIP PDU’s divided into smaller units, e.g. four 5 msec units per 20 msec audio VOIP PDU PDU contains small units from different VOIP PDU’s if PDU lost, still have most of every original VOIP PDU no redundancy overhead, but increases playout delay ...
Apuntes seguridad Redes Avanzadas 0708
... the multicast distribution tree (MDT) [4]. Originally [5], IP multicast was defined under the Any Source Multicast (ASM) model, where a multicast address is the identification of a multicast group G. In the ASM model, senders can transmit data to G without any registration or authentication, and rec ...
... the multicast distribution tree (MDT) [4]. Originally [5], IP multicast was defined under the Any Source Multicast (ASM) model, where a multicast address is the identification of a multicast group G. In the ASM model, senders can transmit data to G without any registration or authentication, and rec ...
CN 2015 1-2 - DSpace
... connection to a called party before any communication is possible. It maintain the connection to transfer message The circuit is terminated when the connection is closed. ...
... connection to a called party before any communication is possible. It maintain the connection to transfer message The circuit is terminated when the connection is closed. ...
Cisco ANA VNE Drivers Data Sheet
... ANA VNE drivers are also user extensible to manage new hardware modules, device types, events, and device software versions that have compatible management instrumentation. Customers can perform private VNE extensions to gain competitiveness with the latest device software and hardware and, at the s ...
... ANA VNE drivers are also user extensible to manage new hardware modules, device types, events, and device software versions that have compatible management instrumentation. Customers can perform private VNE extensions to gain competitiveness with the latest device software and hardware and, at the s ...
Advanced Routing - Fortinet Document Library
... How this guide is organized This chapter describes advanced static routing concepts and how to implement dynamic routing on FortiGate units. This FortiOS Handbook chapter contains the following sections: Advanced Static Routing explains universal and static routing concepts, equal cost multipath (EC ...
... How this guide is organized This chapter describes advanced static routing concepts and how to implement dynamic routing on FortiGate units. This FortiOS Handbook chapter contains the following sections: Advanced Static Routing explains universal and static routing concepts, equal cost multipath (EC ...
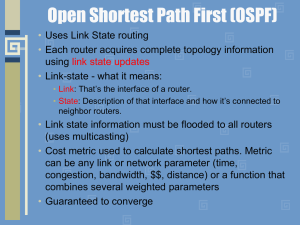
module10b
... • Exstart state – beginning of the LSDB exchange between both routers. • Exchange state – DBD (Database Descriptor) packets are exchanged. DBDs contain LSAs headers. Routers see what LSAs they need. • Loading state – one neighbor start by sending LSRs (Link State Requests) for every network it doesn ...
... • Exstart state – beginning of the LSDB exchange between both routers. • Exchange state – DBD (Database Descriptor) packets are exchanged. DBDs contain LSAs headers. Routers see what LSAs they need. • Loading state – one neighbor start by sending LSRs (Link State Requests) for every network it doesn ...
cis185-ROUTE-lecture6-BGP-Part1
... 207.46.0.0/16 to your ISP. On the receiving side, the ISP does not filter out this incorrect route, allowing it to be advertised to the rest of the Internet. This particular CIDR block belongs to Microsoft, and you have just claimed to have a route to that destination. A significant portion of ...
... 207.46.0.0/16 to your ISP. On the receiving side, the ISP does not filter out this incorrect route, allowing it to be advertised to the rest of the Internet. This particular CIDR block belongs to Microsoft, and you have just claimed to have a route to that destination. A significant portion of ...
Personal Area Networking Bluetooth Profile
... The Personal Area Networking (PAN) Profile describe how two or more Bluetooth enabled devices can form an ad-hoc network and how the same mechanism can be used to access a remote network through a network access point. The profile roles contained in this document are the Network Access Point, Group ...
... The Personal Area Networking (PAN) Profile describe how two or more Bluetooth enabled devices can form an ad-hoc network and how the same mechanism can be used to access a remote network through a network access point. The profile roles contained in this document are the Network Access Point, Group ...
Hands-on Labs
... So what’s an administrator to do to mitigate the impact of managing really big networks? Well, it’s possible to divide the network into multiple distinct EIGRP autonomous systems, or ASes. Each AS is populated by a contiguous series of routers, and route information can be shared among the different ...
... So what’s an administrator to do to mitigate the impact of managing really big networks? Well, it’s possible to divide the network into multiple distinct EIGRP autonomous systems, or ASes. Each AS is populated by a contiguous series of routers, and route information can be shared among the different ...
ConnectPort X Family User`s Guide
... ©Digi International Inc. 2011. All Rights Reserved. The Digi logo, Digi Connect, iDigi, ConnectPort, Digi SureLink, Digi Dialserv are trademarks or registered trademarks of Digi International, Inc. All other trademarks mentioned in this document are the property of their respective owners. Informat ...
... ©Digi International Inc. 2011. All Rights Reserved. The Digi logo, Digi Connect, iDigi, ConnectPort, Digi SureLink, Digi Dialserv are trademarks or registered trademarks of Digi International, Inc. All other trademarks mentioned in this document are the property of their respective owners. Informat ...
Introduction to IPv6
... IPv6 is the evolution of IPv4, the most successful network protocol of the history. IPv4 and IPv6 are not “compatibles on the wire”, which means an IPv4 only host can’t communicate with an IPv6 only host by itselves. IPv6 will not substitute IPv4, both protocol will co-exists for several years. Just ...
... IPv6 is the evolution of IPv4, the most successful network protocol of the history. IPv4 and IPv6 are not “compatibles on the wire”, which means an IPv4 only host can’t communicate with an IPv6 only host by itselves. IPv6 will not substitute IPv4, both protocol will co-exists for several years. Just ...
Avoiding traceroute anomalies with Paris traceroute - Events
... the problem for skitter [7], but they do not report a solution. In practice, the arts++ tool for reading skitter data reports only the first address obtained for each hop. With Rocketfuel [8], Spring et al. attribute a lower confidence level to links inferred from hops that respond with multiple addre ...
... the problem for skitter [7], but they do not report a solution. In practice, the arts++ tool for reading skitter data reports only the first address obtained for each hop. With Rocketfuel [8], Spring et al. attribute a lower confidence level to links inferred from hops that respond with multiple addre ...
The Gartner Glossary of Information Technology Acronyms and Terms
... A protocol that maps network-assigned addresses to underlying data link addresses in an AppleTalk network. ABAP (Advanced Business Application Programming) The core tool for development in SAP’s R/3 system. ABC (activity-based costing) An improved approach to understanding where and why costs are in ...
... A protocol that maps network-assigned addresses to underlying data link addresses in an AppleTalk network. ABAP (Advanced Business Application Programming) The core tool for development in SAP’s R/3 system. ABC (activity-based costing) An improved approach to understanding where and why costs are in ...
A.1 General
... Technical Specification Group Core Network and Terminals; Interworking between SIP-I based circuit-switched core network and other networks (Release 13) ...
... Technical Specification Group Core Network and Terminals; Interworking between SIP-I based circuit-switched core network and other networks (Release 13) ...
Document
... • For the latest PowerPoints for all my CCNA, CCNP, and Wireless classes, please go to my web site: http://www.cabrillo.cc.ca.us/~rgraziani/ • The username is cisco and the password is perlman for all of my materials. • If you have any questions on any of my materials or the curriculum, please feel ...
... • For the latest PowerPoints for all my CCNA, CCNP, and Wireless classes, please go to my web site: http://www.cabrillo.cc.ca.us/~rgraziani/ • The username is cisco and the password is perlman for all of my materials. • If you have any questions on any of my materials or the curriculum, please feel ...
1 Introduction
... Currently TCP implementations use a coarse granularity (typically 500 ms) timer for the retransmission time out. As a result, during congestion, the TCP connection loses time waiting for the time out. In Fig. 4, the horizontal line (at the cwnd value) shows the time lost when waiting for a time out ...
... Currently TCP implementations use a coarse granularity (typically 500 ms) timer for the retransmission time out. As a result, during congestion, the TCP connection loses time waiting for the time out. In Fig. 4, the horizontal line (at the cwnd value) shows the time lost when waiting for a time out ...
Nortel Secure Network Access 2.0 802.1X
... Nortel is a recognized leader in delivering communications capabilities that enhance the human experience, ignite and power global commerce, and secure and protect the world’s most critical information. Serving both service provider and enterprise customers, Nortel delivers innovative technology sol ...
... Nortel is a recognized leader in delivering communications capabilities that enhance the human experience, ignite and power global commerce, and secure and protect the world’s most critical information. Serving both service provider and enterprise customers, Nortel delivers innovative technology sol ...