Next Generation Car Network - FlexRay
... FlexRay also offers many reliability features not available in CAN. Specifically, a redundant communication capability enables fully duplicated network configurations and schedule monitoring by hardware. FlexRay also offers flexible configurations, with support for topologies such as bus, star, and ...
... FlexRay also offers many reliability features not available in CAN. Specifically, a redundant communication capability enables fully duplicated network configurations and schedule monitoring by hardware. FlexRay also offers flexible configurations, with support for topologies such as bus, star, and ...
Sonicwall - Shalimar Infonet
... dynamically update each of these services as new updates become available. All-in-One, Network Security Solutions All-in-one security solutions are available from SonicWALL which are based upon deep packet inspection firewall and IPSec VPN technologies with integrated gateway anti-virus, anti-spywar ...
... dynamically update each of these services as new updates become available. All-in-One, Network Security Solutions All-in-one security solutions are available from SonicWALL which are based upon deep packet inspection firewall and IPSec VPN technologies with integrated gateway anti-virus, anti-spywar ...
cis82-mod7-DistanceVectorRouting-RIP
... What can cause routing loops? • Routing loops can occur when there are: – Incorrect or inconsistent routing updates due to slow convergence after a topology change. (Example coming up next.) – Incorrect or incomplete routing information (see presentation on Discard Routes) – Static routes incorrectl ...
... What can cause routing loops? • Routing loops can occur when there are: – Incorrect or inconsistent routing updates due to slow convergence after a topology change. (Example coming up next.) – Incorrect or incomplete routing information (see presentation on Discard Routes) – Static routes incorrectl ...
Core of the network
... Modems, dedicated connections, bandwidth 32 - 128 Kb/s, first fiber was build, Ethernet 10 Mb/s, PC based routers KA9Q a BSD/386. ...
... Modems, dedicated connections, bandwidth 32 - 128 Kb/s, first fiber was build, Ethernet 10 Mb/s, PC based routers KA9Q a BSD/386. ...
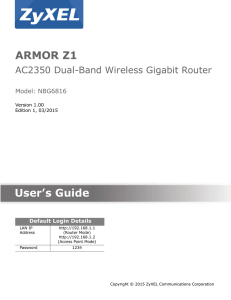
ARMOR Z1 User`s Guide
... Screenshots and graphics in this book may differ slightly from your product due to differences in your product firmware or your computer operating system. Every effort has been made to ensure that the information in this manual is accurate. ...
... Screenshots and graphics in this book may differ slightly from your product due to differences in your product firmware or your computer operating system. Every effort has been made to ensure that the information in this manual is accurate. ...
VoIPTutorial FCC 2011-05 - Computer Science, Columbia
... Buffering - time datagram is held before sending or before rendering Queuing - time spent in a router buffer waiting for route selection ...
... Buffering - time datagram is held before sending or before rendering Queuing - time spent in a router buffer waiting for route selection ...
Chapter 7
... What can cause routing loops? • Routing loops can occur when there are: – Incorrect or inconsistent routing updates due to slow convergence after a topology change. (Example coming up next.) – Incorrect or incomplete routing information (see presentation on Discard Routes) – Static routes incorrectl ...
... What can cause routing loops? • Routing loops can occur when there are: – Incorrect or inconsistent routing updates due to slow convergence after a topology change. (Example coming up next.) – Incorrect or incomplete routing information (see presentation on Discard Routes) – Static routes incorrectl ...
- TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
Integrating Cisco Press Resources into the
... • Link-state routing raises two concerns: – During the initial discovery process, link-state routing protocols flood the network with LSAs • Significantly decreases the network’s capability to transport data • This is temporary, but noticeable ...
... • Link-state routing raises two concerns: – During the initial discovery process, link-state routing protocols flood the network with LSAs • Significantly decreases the network’s capability to transport data • This is temporary, but noticeable ...
TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
What Is a Virtual Private Network?
... A virtual private network (VPN) allows the provisioning of private network services for an organization or organizations over a public or shared infrastructure such as the Internet or service provider backbone network. The shared service provider backbone network is known as the VPN backbone and is ...
... A virtual private network (VPN) allows the provisioning of private network services for an organization or organizations over a public or shared infrastructure such as the Internet or service provider backbone network. The shared service provider backbone network is known as the VPN backbone and is ...
Wiley Publishing - CCNA For Dummies [2000].
... Ethernet networks...........................................................................................................................22 Token Ring networks.....................................................................................................................22 FDDI: The double−r ...
... Ethernet networks...........................................................................................................................22 Token Ring networks.....................................................................................................................22 FDDI: The double−r ...
wireless mesh networks
... Per-hop RTT captures per-link performance parameters, although measurement is actually carried out at the network layer. ...
... Per-hop RTT captures per-link performance parameters, although measurement is actually carried out at the network layer. ...
Session MI.1 - PW/MPLS
... Not all routers are S-PEs, not all S-PEs are PW switching or dynamic MS-PW signalling capable ...
... Not all routers are S-PEs, not all S-PEs are PW switching or dynamic MS-PW signalling capable ...
DSL-2750U - D-Link
... Please, read this manual prior to installing the device. Make sure that you have all the necessary information and equipment. Operating System Configuration of the multifunction 3G/ADSL/Ethernet router DSL-2750U (hereinafter referred to as “the router”) is performed via the built-in web-based interf ...
... Please, read this manual prior to installing the device. Make sure that you have all the necessary information and equipment. Operating System Configuration of the multifunction 3G/ADSL/Ethernet router DSL-2750U (hereinafter referred to as “the router”) is performed via the built-in web-based interf ...
Chapter5-NetworkLayer
... • Each node knows distance of links to its neighbors • Each node advertises vector of lowest known distances to all neighbors • Each node uses received vectors to update its own ...
... • Each node knows distance of links to its neighbors • Each node advertises vector of lowest known distances to all neighbors • Each node uses received vectors to update its own ...
p2p
... partitioned into clusters of sizes in [k, 3k]. Layer H −1 has only one cluster which has a size in [2, 3k]. • A peer in a cluster at layer j < H is selected to be the head of that cluster. This head becomes a member of layer j + 1 if j < H − 1. The server S is the head of any cluster it belongs to. ...
... partitioned into clusters of sizes in [k, 3k]. Layer H −1 has only one cluster which has a size in [2, 3k]. • A peer in a cluster at layer j < H is selected to be the head of that cluster. This head becomes a member of layer j + 1 if j < H − 1. The server S is the head of any cluster it belongs to. ...
DEPLOYMENT IPV6 OVER IPV4 NETWORK INFRASTRUCTURE Tien Dung Hoang
... The purpose of this thesis is doing the research about IPv6, concentrate in how to deploy an IPv6 network based on IPv4 network without making any interruption to IPv4 network. This thesis is made for Financing and Promoting Technology Corporation (FPT) in Vietnam. This thesis is completed in two ma ...
... The purpose of this thesis is doing the research about IPv6, concentrate in how to deploy an IPv6 network based on IPv4 network without making any interruption to IPv4 network. This thesis is made for Financing and Promoting Technology Corporation (FPT) in Vietnam. This thesis is completed in two ma ...
Clustered Data ONTAP 8.3 Network Management Guide
... You need to understand how to configure networking components of the cluster during and after cluster setup. You also need to follow specific guidelines when cabling the nodes and switches in your network. ...
... You need to understand how to configure networking components of the cluster during and after cluster setup. You also need to follow specific guidelines when cabling the nodes and switches in your network. ...
Demystifying Layer 2 and Layer 3 VPNs
... 4.3 Business Features of Layer 2 and Layer 3 Services ................................................................................................................................................................... 37 4.3.1 Multi-point Any-to-Any Connectivity ..................................... ...
... 4.3 Business Features of Layer 2 and Layer 3 Services ................................................................................................................................................................... 37 4.3.1 Multi-point Any-to-Any Connectivity ..................................... ...
2009毕业答辩
... Overview of Femtocells Vivek Dev, COO of Telefonica O2 Europe ― “Our Apple iPhone and flat rate data tariffs place huge capacity demands on our networks. Because so much of that usage is at home, femtocells could play a crucial role in underpinning the explosive growth of mobile broadband ...
... Overview of Femtocells Vivek Dev, COO of Telefonica O2 Europe ― “Our Apple iPhone and flat rate data tariffs place huge capacity demands on our networks. Because so much of that usage is at home, femtocells could play a crucial role in underpinning the explosive growth of mobile broadband ...
SNMP Tutorial
... SYNTAX Time-Ticks ACCESS read-only STATUS mandatory DESCRIPTION “Time since the network management portion of the system was last re-initialised. ...
... SYNTAX Time-Ticks ACCESS read-only STATUS mandatory DESCRIPTION “Time since the network management portion of the system was last re-initialised. ...



![Wiley Publishing - CCNA For Dummies [2000].](http://s1.studyres.com/store/data/008049680_1-a9b72081a3d6e4abe69a6bd824c30e5a-300x300.png)