* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download Modern Internet architecture & technology
Computer network wikipedia , lookup
Airborne Networking wikipedia , lookup
Dynamic Host Configuration Protocol wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
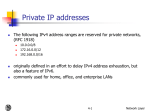
Parallel port wikipedia , lookup
Distributed firewall wikipedia , lookup
Network tap wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Network Address Translation (NAT) 1 Overview Motivation End-to-end principle Role of IP addresses Basic NAT types and their behaviors NAT traversal: STUN 2 History Early 1990s IPv4 Address consumption concern Two approaches • IPv6 and NAT NATs were initially intended to allow devices to share an address pool dynamically NAT goes against Internet end-to-end principle 3 First RFC about NAT in 1994 NAT vs. DHCP? IETF hates NATs No standardization -> backfire Motivation DSL and cable modem business model ISP wants to save money Even multi-homing Security: Inbound traffic filtering 4 In PSTNs, there is extension Changing next higher ISP becomes easier Not simultaneous access, no servers stateful firewall End-to-end principle 5 RFC 1958: “An end-to-end protocol design should not rely on the maintenance of state (i.e., information about the state of the end-to-end communication) inside the network. Such state should be maintained only in the endpoints, in such a way that the state can only be destroyed when the endpoint itself breaks (known as fatesharing). An immediate consequence of this is that datagrams are better than classical virtual circuits. The network's job is to transmit datagrams as efficiently and flexibly as possible. Everything else should be done at the fringes.” Middle boxes 6 Middle box = “any intermediary device performing functions other than the normal, standard functions of an IP router on the datagram path between a source host and destination host” L2, L3, L4, L7, … explicit vs. implicit functional vs. optimizing routing vs. processing soft vs. hard state fail-over vs. restart Examples: NATs SOCKS gateway IP tunnel endpoint Transport relay Load balancers Application firewalls Transcoders (RFC 3234) Proxies Caches Modified DNS servers Anonymizers Private Network Private IP network is an IP network that is not directly connected to the Internet IP addresses in a private network can be assigned arbitrarily. Generally, private networks use addresses from the following experimental address ranges (non-routable addresses): 7 Not registered and not guaranteed to be globally unique 10.0.0.0 – 10.255.255.255 172.16.0.0 – 172.31.255.255 192.168.0.0 – 192.168.255.255 Private Addresses H1 10.0.1.2 H3 H2 10.0.1.2 10.0.1.3 10.0.1.1 10.0.1.3 10.0.1.1 Private network 1 Private network 1 Internet R1 128.195.4.119 128.143.71.21 213.168.112.3 H5 8 H4 R2 Network Address Translation (NAT) NAT is a router function where IP addresses (and possibly port numbers) of IP datagrams are replaced at the boundary of a private network NAT is a method that enables hosts on private networks to communicate with hosts on the Internet NAT is run on routers that connect private networks to the public Internet, to replace the IP address-port pair of an IP packet with another IP address-port pair. Topology sensitive • inside (private) vs. outside (public) 9 Basic operation of NAT 10 NAT device has address translation table Main uses of NAT 11 Pooling of IP addresses Supporting migration between network service providers IP masquerading Load balancing of servers Pooling of IP addresses Scenario: Corporate network has many hosts but only a small number of public IP addresses NAT solution: 12 Corporate network is managed with a private address space NAT device, located at the boundary between the corporate network and the public Internet, manages a pool of public IP addresses When a host from the corporate network sends an IP datagram to a host in the public Internet, the NAT device picks a public IP address from the address pool, and binds this address to the private address of the host Pooling of IP addresses Private network Internet Source = 10.0.1.2 Destination = 213.168.112.3 Source = 128.143.71.21 Destination = 213.168.112.3 NAT device private address: 10.0.1.2 public address: H1 213.168.112.3 H5 Private Address Public Address 10.0.1.2 Pool of addresses: 128.143.71.0-128.143.71.30 13 public address: Supporting migration between network service providers Scenario: In CIDR, the IP addresses in a corporate network are obtained from the service provider. Changing the service provider requires changing all IP addresses in the network. NAT solution: Assign private addresses to the hosts of the corporate network NAT device has static address translation entries which bind the private address of a host to the public address. Migration to a new network service provider merely requires an update of the NAT device. The migration is not noticeable to the hosts on the network. Note: The difference to the use of NAT with IP address pooling is that the mapping of public and private IP addresses is static. 14 Supporting migration between network service providers 15 IP masquerading Also called: Network address and port translation (NAPT) Scenario: Single public IP address is mapped to multiple hosts in a private network. NAT solution: 16 Assign private addresses to the hosts of the corporate network NAT device modifies the port numbers for outgoing traffic IP masquerading 17 Load balancing of servers Scenario: Balance the load on a set of identical servers, which are accessible from a single IP address NAT solution: 18 Here, the servers are assigned private addresses NAT device acts as a proxy for requests to the server from the public network The NAT device changes the destination IP address of arriving packets to one of the private addresses for a server A sensible strategy for balancing the load of the servers is to assign the addresses of the servers in a roundrobin fashion. Load balancing of servers 19 Concerns about NAT Performance: Modifying the IP header by changing the IP address requires that NAT boxes recalculate the IP header checksum Modifying port number requires that NAT boxes recalculate TCP checksum 20 Fragmentation Care must be taken that a datagram that is fragmented before it reaches the NAT device, is not assigned a different IP address or different port numbers for each of the fragments. Concerns about NAT End-to-end connectivity: 21 NAT destroys universal end-to-end reachability of hosts on the Internet. A host in the public Internet often cannot initiate communication to a host in a private network • Hamper peer-to-peer applications The problem is worse, when two hosts that are in a private network need to communicate with each other Typically, the address-port mapping is maintained soft-state (in minutes) Concerns about NAT IP address in application data: 22 Applications that carry IP addresses in the payload of the application data generally do not work across a private-public network boundary. Some NAT devices inspect the payload of widely used application layer protocols and, if an IP address is detected in the applicationlayer header or the application payload, translate the address according to the address translation table. NAT and FTP 23 Normal FTP operation NAT and FTP 24 NAT device with FTP support NAT and FTP 25 FTP in passive mode and NAT. NAT Traversal 26 NAPT Traversal 27 NAT types Symmetric Port restricted cone Address restricted cone Full cone Hairpin Different not only on a vendor-by-vendor basis but also on a model-by-model basis 28 Symmetric NAT 29 •NAT mapping btw src_addr/src_port and dest_addr/dest_port is fixed •The most restrictive form •It has been observed to be rare Full-cone NAT 30 The least restrictive form Binding of a local address/port can be used by any remote host (Address) Restricted-cone NAT 31 NAT binding is accessible only by the destination host different port can be used Port-restricted-cone NAT NAT binding is accessible by any remote host 32 But only same port should be used Typically, the internal host had previously sent a packet the remote host Hairpin NAT D 33 A local host can direct a packet to the public address/port of an already mapped local host Nondeterministic NATs NATs change their types of behavior when a binding conflict occurs Example Some NATs attempt to preserve the port number in the binding If the port number is available, the NAT behaves like a full-cone NAT If that port is already occupied by other host, the NAT may change the type, e.g. a symmetric NAT 34 What is STUN? Who uses it? STUN – Simple Traversal of User Datagram Protocol through Network Address Translators. The protocol is defined in RFC 3489. Protocols like SIP and applications like Google Talk use STUN to gather important information about the network configuration. 35 What does it do? 36 STUN is a client-server protocol that “allows entities behind a NAT to first discover the presence of a NAT and the type of NAT, and then to learn the addresses bindings allocated by the NAT.” In other words, it’s a means of discovering the public IP and port numbers that a NAT assigns to a node on a private LAN. In addition, STUN does not require any special network configuration and works with a variety of existing networks, but not all. *http://tools.ietf.org/html/rfc3489 STUN and NAT terminology A STUN Client is a node that generates the STUN requests. A STUN Server is a node that receives the STUN requests and generates the STUN responses. NAT 37 usually part of a firewall or router A picture i worth 1000 words 38 How STUN generally works A STUN Client sends a STUN request to a STUN Server. The Client then waits for the Server to send a STUN response 39 STUN client is typically embedded in application STUN server has two IP addresses The trick is to analyze the response from the server to determine the type of NAT router and the associated bindings the router has given to internal nodes. The STUN Message 40 The following STUN attributes in the payload are especially important: MAPPED-ADDRESS : Found in STUN responses. It contains the IP address and port number of the STUN request. I.e., the public IP and port of the STUN client. CHANGE-REQUEST : Found in STUN requests. It contains flags for the IP address and port number of the server. If set, the client is asking the server to send the response from a different IP and port. (We will see why later) CHANGED-ADDRESS – Found in STUN responses. It contains the alternate IP address and port number of the server due to CHANGE-REQUEST NAT discovery (test 1) 41 To determine if a NAT router/firewall is present, send a STUN request to the server. Wait for a response and analyze it. If the IP address and port number in the MAPPED-ADDRESS attribute of the payload in the STUN response equal the local IP address and port number that it bound to when sending the request, then the client is NOT behind a NAT router. Otherwise, it is behind a NAT router. NAT discovery – Full Cone (test 2) Full Cone NAT router – The client sets the IP address and port number flags in the CHANGE-REQUEST of the STUN request. This causes the server to send the response from the alternate IP and port number. 42 If the client receives the STUN response, then the client is behind a full cone router. Otherwise, it is behind one of the other three NAT routers. NAT discovery – Symmetric (test 3) Symmetric NAT – The client sends two STUN requests. One request is sent to a server at IP address X and port P, and another to a server at IP address Y and port P. 43 If the IP addresses and ports from the MAPPED-ADDRESS attributes in the two responses do not match, then it is behind a Symmetric NAT router. If they do match, then it is behind one of the remaining two NAT routers. NAT discovery – Restricted (test 4) Restricted NAT – The port flag in the CHANGE-REQUEST attribute of the request is set. This instructs the server to send a response from a different port. 44 If the response is received, it is behind a restricted NAT router. If no response is received, it is behind a port restricted NAT router. 45 Limitations of STUN Does not address incoming TCP connections. 46 STUNT and other proposals Does not allow incoming UDP connections through a symmetric NAT STUN “is not a cure-all for the problems associated with NAT.” “The problems in STUN have to do with the lack of standardized behaviors and controls in NATs, which results in a proliferation of devices whose behavior is highly unpredictable, extremely variable, and uncontrollable. Ultimately, the solution is to make the environment less hostile, and to introduce controls and standardized behaviors into NAT. However, until such time as that happens, STUN provides a good short term solution given the terrible conditions under which it is forced to operate.” NAT traversal 47 48 49 50 51 52 53 54 55 56 57 58 59 Other issues Symmetric NATs The first packet for hole punching will be dropped And the port number (for the other peer) is changed from the one for the server Port prediction technique • May not work 60 Nested NATs