* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Threats in the Digital World
SIP extensions for the IP Multimedia Subsystem wikipedia , lookup
Network tap wikipedia , lookup
Server Message Block wikipedia , lookup
Remote Desktop Services wikipedia , lookup
Deep packet inspection wikipedia , lookup
Distributed firewall wikipedia , lookup
TCP congestion control wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Internet protocol suite wikipedia , lookup
Parallel port wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
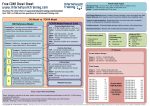
External Threats -People & Technology Rudeyna Quadri February 11, 2003 Thursday, May 25, 2017 Outline Threats in the Digital World People in the Digital World Prelude to Hacking Footprinting Scanning Enumeration Threats in the Digital World They mirror the threats in the physical world Digital embezzlement Digital bank robbery Invasion of privacy Theft Racketeering Vandalism Exploitation Extortion fraud Threats in the Digital World Changing nature of the attacks Attacks may have same goals and share a lot of the techniques with the physical world, they are very different More common More widespread Harder to track Effects will be more devastating Real-Life Lessons What happened: Front page replaced How: Two years since server code was updated Lesson: Update systems frequently Source: Internet World What happened: Home page text replaced How: Failed to update operating system in timely fashion Lesson: Always apply latest patches What happened: Customer details compromised on web site How: Glitch on the web site Lesson: Usage of stronger customer authentication needed & development control processes Threats in the Digital World Internet has three features which make the threats more horrifying Automation Action at a Distance Technique Propogation Automation Computer excel at dull, repetitive tasks Salami Attack Fast automation makes attacks with a minimal rate of return profitable Even a success rate of 1 in 10,000 is acceptable Violation of privacy Action At a Distance Internet has no borders..every two points are adjacent Internet hackers don’t have to be anywhere near their prey Finding attackers sometime becomes impossible Lack of uniform international laws make it harder to track cyber criminals across national borders. Technique Propagation Electronic counterfeiter Only the first attacker has to be skilled..everyone else can use his/her software Threats to the Digital World..People Who are the adversaries in the digital world? We can categorize them in several ways Objectives Access Resources Expertise Risk Objectives Raw damage Financial gain Information Levels of Access, resource & Expertise Insider has much more access than someone outside the organization Access to different levels of resources: some are well funded, while others operate on a shoestring Some have technical expertise while others have none Levels of Risk Risk tolerance is varied Publicity seekers probably won’t want to go to jail. Definitions Risk = Threat X Vulnerability Being “at risk" is being exposed to threats. Risks are subjective -- the potential to incur consequences of harm or loss of target assets. A Risk Factor is the likelihood of resources being attacked. Threats are dangerous actions that can cause harm. The degree of threat depends on the attacker's Skills, Knowledge, Resources, Authority, and Motives. Vulnerabilities are weaknesses in victims that allow a threat to become effective. Hacker Jargons (Some) A rogue user is an authorized user who, without permission, accessesrestricted assets. A bogie is an unauthorized user who subverts security systems. A cracker breaks into others’ computing facilities for their own personal gain - be it financial, revenge, or amusement. A hacktivist is a cracker with a cause. (Example of hactivism: Building Peekabooty to get around governments blocking websites) A terrorist uses fear to blackmail others into doing what they want. Hacking Jargons (Some) White Hats are also called “ethical" hackers, such as the Axent (now Symantec) Tiger Team Black Hats disregard generally accepted social conventions and laws. Script kiddie is a derogatory term for a wannabe cracker who lacks programming skills and thus relies on prewritten scripts and toolkits for their exploits. Journeyman is an experienced hacker: someone who has collected many tools and made many connections. A Puppet Master (wizard) produces exploits. Source: http://www.wilsonmar.com/1secvul.htm Types of Adversaries The Hacker FBI Seeks Hacker Who Stole eBay Info Sat Feb 8,10:50 AM ET CHARLOTTE, N.C. A hacker used a University of North Carolina computer system to steal personal financial information from eBay users, and at least one person lost money, the FBI (news - web sites) said Friday. The Hacker “Cracker” for the bad guys– “Hacker for the good ones Today’s hackers are Twenty-something & younger Usually male Have their own counterculture Hacker names, handles, lingo, rules Only a small percentage of the hackers are actually smart. The Hacker Hacker stereotyped Real hackers have an understanding of technology at a basic level. The rest are called lames or Script Kiddies Usually have a lot of time but limited financial resources The Hacker Hackers write hacking tools which can automate the process of breaking into systems. Lone Criminals Lone criminals cause the bulk of computer related crimes Maybe insiders who notice a flaw in the system & decide to exploit Lone criminals will usually target commerce systems. Malicious Insiders Someone in the system who wants to attack Perimeter defense not relevant Not always attack system 1991: employees in Charles Scwab in SF used company’s e-mail system to buy and sell cocaine. Insiders are not necesarrily employess. Maybe: Contractors Consultants Insider Attack Most of the security measures are powerless against insiders. Systems are more vulnerable to them Motivational factors for Insiders: Revenge Financial Gain Institutional Change Publicity Other Adversaries Industrial Spy: Precise motivation of gaining edge over competitors admissions administrator at Princeton broke into a Yale admissions computer to look at student applicant records. Source: http://www.all.net/ Press: Subspecies of industrial spy, but different motivation— creating sensation. Organized Crime: Use technology in two ways: New Venue for crime: Hacking tools to break into bank computers, stealing cell phone ID’s and reselling them. Uses computers to assist in its core business. Other Adversaries Police Information gathering Have legal right to “eavesdrop” (with warrant) No guarantee that the information will be used ethically in the future. Terrorist More concerned with causing harm than information gathering Denial of Service, and outright destruction. Other Adversaries National Intelligence Organizations CIA, NSA, KGB, MI5, MI6 Usually extremely well funded Some national intelligence organizations are involved in industrial espionage and passing on the info to their national companies. Infowarriors Military adversary who targets enemy’s information or network infrastructure. Attacks range from subtly modifying systems so that they do not work to blowing up the system. Usually have the resources of the government behind. More short term goal oriented Higher risk tolerance. Hacking..first steps Before in-depth hacking can be performed, three essential tasks must be completed Footprinting Scanning Enumerating Footprinting Create a complete profile of an organization’s security posture Steps Determine the scope of activities Network Enumeration Check organization’s website for info Review HTML source code for comments Identify domain names and associated networks DNS Interrogation Query the DNS Zone Transfer Scanning Footprinting provides a list of network and IP addresses through whois queries Scanning determines what systems are alive and reachable from the Internet Scanning Tools for Scanning Ping Sweeps Port Scans Automated Discovery Tools Scanning – Ping Sweeps One of the basic steps in mapping out a network is performing an automated ping sweep on a range of IP addresses. Ping traditionally sends ICMP ECHO to elicit an ICMP ECHO REPLY Tools for Ping Sweeps fping Operates in UNIX Available in http://www.fping.com uses the Internet Control Message Protocol (ICMP) echo request to determine if a host is up. “fping is different from ping in that you can specify any number of hosts on the command line, or specify a file containing the lists of hosts to ping. Instead of trying one host until it timeouts or replies, fping will send out a ping packet and move on to the next host in a round-robin fashion. If a host replies, it is noted and removed from the list of hosts to check. If a host does not respond within a certain time limit and/or retry limit it will be considered unreachable” Tools for Ping Sweeps Pinger Freeware for Windows http://www.nmrc.org/files/snt/#chk-scan Like fping, Pinger sends out multiple ICMP ECHO packets in parralel and waits and listens for responses. Allows user to resolve hostnames and save output to file Tools for Ping Sweeps For Windows WS_Ping ProPack www.ipswitch.com Price Single User $37.50 10 User Pack $280 20 User Pack $540 50 User Pack $1,300 100 User Pack$2,450 Source: www.ipswitch.com Price withService Agreement $87.50 $330 $637 $1,534 $2,891 Ping Sweep Other Devices NMAP provides Ping Sweep facilities Icmpenum from Simple Nomad Special feature ICMP TIME STAMP REQUEST ICMP INFO REQUEST Can use spoofed packets to avoid detection Ping Sweep Countermeasures Detection Through network based IDS like snort Other Unix-Based: Scanlogd, Ippl 1.4.14 etc. Windows based Genius( freeware): detects TCP Scan to a particular port BlackIce (Commercial) Ping Sweep Countermeasures Prevention Carefully evaluate the ICMP traffic to allow in the network or into specific systems. ICMP Traffics can be limited with ACLs to specific IP addresses of the ISP. Port Scanning Process of connecting to TCP and UDP ports on the target system to determine what services are running or are in a LISTENING state Three main objectives: Identify both the TCP and UDP services running on the target system Identify the type of operating system Identify specific application or versions of an operating system. Port Scanning Types of port scan TCP connect scan: connects to the target port and completes a full three-way hand-shake (SYN, SYN/SCK, and ACK). Easily detected by the target system. TCP SYN scan: SYN packet sent to the target port, if SYN/ACK is received, it is in listening state. If RST/ACK received, port is not listening. Stealthier than full scan, and may not be logged by the target system. Types of Port Scan TCP Fin Scan: sends a FIN packet to the target port, target port sends back RST for all closed ports. Usually only works on Unix based TCP/IP stacks. TCP Xmas Tree scan: sends a FIN, URG and PUSH packet to the target port. Target sends back RST for all closed ports. TCP Null Scan: turns off all flags. Targeyt system sends back RST for all closed ports. TCP ACK Scan: used to map out firewall rulesets. Helps determine if firewall is stateless or stateful Port Scanning Toolkit Unix Based: Strobe: TCP Port Scanning Utility One of the fastest and most reliable Optimizes system and network resources and scan target system efficiently. We only see half the picture as Strobe does not provide UDP scanning capabilities. UDP_scan Reliable Sometimes triggers a message from major IDS products..not stealthy Port Scanning Toolkit Unix based Netcat Provides both TCP and UDP scanning abilities Network Mapper (NMAP) Nmap can scan a system or an entire network Possible to save output to a file Able to launch decoy scans Can do identity scanning Port Scanning Toolkit Windows Based Port Probe (From NetScan Tools Pro 2003) SuperScan & WinScan TCP Port scanner Free ipEye Target IP & portlists can be imported from files. TCP & UDP Scan Performs source port scanning, as well as SYN, FIN and Xmas tree scans. Windows UDP Port Scanner (WUPS). Port Scanning Countermeasures Detection Detecting port scan activity is important to understand when an attack may occur and by whom. Primary methods for detection are network based IDS programs like: Internet Security Sytems’ Real Secure Snort Port Scanning Countermeasures Detection Unix Host based perspective: Scanlogd: detect & log attacks Psionic PortSentry: detect and respond to active attacks. Respond: automatically set kernel filtering rules that add a rule to prohibit access from the offending system. Cons to retaliation? Spoofing. Firewalls: can be configured to detect port scan attempts. Port Scanning Countermeasures Detection Windows based Genius BlackIce Prevention: Disable all unnecessary services Detecting the Operating System The Second objective of scanning to to determine the operating system. Tools: NMAP (again) Queso Both of these provide Stack Fingerprinting capabilities Detecting the Operating System Stack Fingerprinting There are many nuances that vary between one vendor’s IP stack implementation and another. Probing these differences can help us begin to make an educated guess as to the exact operating system in use. This is known as stack fingerprinting. Stack Fingerprinting Types of Probes: FIN Probe Bogus Flag Probe Initial Sequence Number Sampling “Don’t Fragment Bit” monitoring TCP intial window size ACK Value ICMP error Message Quneching ICMP message quoting ICMP error message-echoing integrity Types of Service (TOS) Fragmentation Handling Please see Hacking Exposed (pp55-56) for details of these probes. Passive Stack Fingerprinting Instead of sending packets to target systems, attacker passively monitors network traffic to determine the operating system in use. Passive Signatures: TTL: What does the operating system set as the time-to-live on the outbound packet? Window Size: What does the oeprating system set as the Window Size? DF: The does operating system set the Don’t Fragment Bit? Operating System Detection Countermeasures Detection: Port scanning detection tools can be used to watch for operating system detection Prevention: Not an easy problem. May be possible to change one of the unique stack fingerprint characteristics, but may adversely affect the functionality of the system. Robust secure proxies or firewalls should be subject to Internet scans. ENUMERATION Process of Identifying Valid user accounts Poorly protected resource shares Enumeration Involves Difference in level of intrusion: Active connection to systems Directed queries Types of Information: Network resources & share Users & Groups Applications & Banners ENUMERATION (Continued) Windows NT/2000 Enumeration Common Internet File System/Server Message Block (CIFS/SMB) NetBIOS Windows NT/2000 Resource Toolkit (NTRK) Windows NT Hacking Kit! Null Sessions CIFS/SMB standards include APIs that return rich information about a machine via TCP port 139-even to unauthenticated users. First step towards accessing these APIs is to create a null session. Create a null session net use \\129.118.50.37 \IPc$ “” /u:“” “Share” – IPC$ Built-in anonymous user /u: “” Null password “” Attacker now can access information about: Network info, shares, users, groups, registry keys. Etc. Null Session countermeasures: Sessions require access to TCP 139 (and/or 445 on Win 2000) Filter TCP and UDP ports 139 & 445 at all perimeter network access devices. Disable SMB service entirely Windows NT Service Pack 3 has a facility named Restrict Anonymous – which prevents enumeration of sensitive information over null sessions. This fix is slightly easier to implement on Windows 2000 NetBIOS Enumeration Net view lists domains available on the network. X:\>net view /domain Domain -------------------------------------ATMO BA BA.TTU.EDU HOME NTUST WORKGROUP The command completed successfully. NetBIOS Enumeration This command list computers in a particular domain X:\>net view /domain:atmo Server Name Remark --------------------------------------------------------\\EMPYREAN \\HABOOB \\THUNDER Samba 2.0.4b Server on hailshaft \\TYPHOON The command completed successfully. NetBIOS Enumeration Nbtstat: calls up the netBIOS Name Table from a remote system. X:\>nbtstat -a 129.118.50.37 Local Area Connection: Node IpAddress: [129.118.50.38] Scope Id: [] NetBIOS Remote Machine Name Table Name Type Status --------------------------------------------BAMDC1 <00> UNIQUE Registered BAMDC1 <20> UNIQUE Registered BA <00> GROUP Registered BA <1C> GROUP Registered BA <1E> GROUP Registered BAMDC1 <03> UNIQUE Registered MAC Address = 00-B0-D0-7F-CB-75 Please See Hacking Exposed ch 3, for explanation of these codes. NetBIOS Enumeration nbtStat: Two main drawbacks of nbtstat are that it is restricted to operating on a single user and its rather inscrutable output. nbtScan, a freeware, addresses these issues. nbtScan can scan a whole range of IP addresses. Table headers of nbtscan: IP Address NetBIOS Name Server User MAC Address NetBIOS Enumeration Nt/2000 Domain Controllers NTRK Tool called nltests identifies the primary and backup domain controllers in a domain. Share enumeration tools from RK: New view: lists shares on the system Rmtshare: output similar to net view Srvcheck: displays shares & authorized users Srvinfo NetBIOS Enumeration: 3rd Party Software DumpSec (http://www.somarsoft.com): Audits everything for file system permission to services available on remote system. Basic user information can be obtained through null session using DumpSec. Can be run from Command line, making automation & scripting easy. Legion: NetBIOS Scanner GUI Reveal all available shares. Tries to connect to shares by using list of user-supplied passwords. NetBIOS Enumeration: 3rd Party Software NetBIOS Auditing Tool (NAT): http://www.hackingexposed.com Both command line & graphical interface Finds & attempts forced entry into shares. Epdump: shows addresses bound to IP addresses and port numbers. Getmac: gets the MAC address & device names for NICs Netdom: info about NT domains ona wire, including domain membership & identities of backup domain controllers Netviewx: lists nodes in domains & services they run NetBIOS Enumeration Countermeasures Deny Access to TCP & UPD 135-139 Block access using a router, firewall, or other network gatekeepers Only way to prevent user data from appearing in NetBIOS name table dumps is to disable the Alerter and Messenger service on individual hosts. NT/2000 SNMP Enumeration If the system is running Simple Network Management Protocol (SNMP) agent accessible via default community strings like “public”, enumerating NT users is possible through snmputil in NTRK. Snmputil can reveal: Running services Share names Share paths Comments on shares Usernames Domain names NT/2000 SNMP Enumeration Countermeasures Countermeasures: Remove SNMP agent If removing is not an option, ensure that it is properly configured with private community names (not the default “public”); Edit the Registry to permit only approved access to the SNMP community Name. NT/2000 Host Enumeration Enumerating users via CIFS/SMB NTRK tools like usrstat, showgrps, local and global utilities casn provide more information about users. Dumpsec can pull a list of users, groups, and the NT system’s policies and user rights. NT/2000 Host Enumeration NTRK Tools such as usrstat, showgrps, local and global utilities, provide info about users. Dumpsec: Dumpsec and pull a list of users gorups and the NT systems policies and user rights. User2sid/sid2user: Looks up looks up NT Security Identifiers (SID: a variable-length numeric value issued to an NT System at installation) from user name & vice versa. NT/2000 Host Enumeration Enum: A comprehensive enumeration tool. A Sample of the command line switches: -U: Get Userlist -M: get machine list _N: get namelist dump -S: get sharelist -P: get password policy information -G: get group and member list -d: be detailed Automates the setup and tear down of null sessions. NT/2000 Host Enumeration countermeasures Block acess to TCP & UDP ports 135159, and 445. Disable SMB services or set to RestrictAnonymous. Disable file & print sharing for Microsoft Networks. Win 2000 Active Directory Enumeration using Idp The most fundamental change introduced by Win 20000 is the addition of a lightweight Directory Access Protocol (LDAP) – based directory service that Microsoft calls Active Directory(AD). AD is designed to contain a unified, logical representation of all the objects relevant to the corporate technology infrastructure. The Windows 2000 simple LDAP client called the Active Directory Administration Tool (ldp.exe) that connects to an AD server and browses the contents of the directory. Simply pointing ldp at a Win 2000 domain controller will enumerate all of the existing users and groups with a simple LDAP query. NT/2000 Applications and Banner Grabbing Connecting to remote applications and observing the output is called banner grabbing. Identifies the software and version running on the server, which in many cases is enough to set the vulnerability research process in motion Telnet & netcat are two tools for banner grabbing. Banner Grabbing Countermeasures Inventory mission-critical applications, and find correct way to disable presentation of vendor and version in banners. Audit regularly with port scans and raw netcat connects. The End