* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Number Theory & RSA
List of important publications in mathematics wikipedia , lookup
Factorization of polynomials over finite fields wikipedia , lookup
Elementary mathematics wikipedia , lookup
Fundamental theorem of algebra wikipedia , lookup
Fermat's Last Theorem wikipedia , lookup
Wiles's proof of Fermat's Last Theorem wikipedia , lookup
Collatz conjecture wikipedia , lookup
List of prime numbers wikipedia , lookup
"The demand is for people who really understand and
have practiced forensics, for people who really
understand and have practiced intrusion detection,
system testing, vulnerability testing and penetration
testing“
--"The SANS 2005 Salary Survey," System
Administration, Networking, and Security
(SANS) Institute
1
Public Key Systems
Two keys:
Public Key=(n, e)
n and e are public.
Private Key=(n, d)
d:
known only to the owner of the key;
infeasible to find d, given n and e.
EXAMPLE: Let m: plaintext message
c: cipher
2
Example of RSA System
….. 1
(developed by Rivest, Shamir, and Adleman)
Let the key belong to Alice.
Bob wants to send a confidential
message to Alice, using PK system.
Bob knows only the public key.
He uses the public key to create
c=me mod n
…………….[1]
He sends c to Alice on the Internet.
Eve can sniff c. But she cannot
understand it.
3
Example of RSA System
….. 2
Alice can find m:
m = cd mod n
…………….[2]
To Prove: (a) possible to find n, e and d
so that equations [1] and [2] can work
out;
(b) infeasible to find d, given n and e.
Note: The minimum size of n: 1024 bits
( i.e.309 digit decimal number).
4
…aesthetic distance: To appreciate art you need be
not too far and not too close.
Engineers are too close to Mathematics to
appreciate, admire and enjoy Mathematics.
-- From King's 'The Art of Mathematics‘
Note: Both engineers and scientists use Mathematics extensively.
So King’s quote is equally true for scientists.
5
Number Theory: A Revision
nla
n divides a or n is a divisor of a
Þ
prime number if its only divisors are
±1
Unique factors of any integer a > 1:
a = pap
p P
where P is the set of prime numbers
and where ap is the degree of p
c = a.b cp = (ap+bp) for all p.
Ex:33033 = 3x7x112 X13; 85833 = 3x3x3x11x172
c3 = 3+1 =4, c7 = 1, c11 = 2 +1 = 3, c13 = 1, c17 = 2
a|b ap bp for all p; 143|33033
6
gcd, Relative prime number:
Greatest Common Divisor:
gcd(a,b) = max [k such that k|a and k|b]
kp= min(ap,bp) for all p;
Ex: to find gcd(33033, 85833): k3= 1, k11= 1
Calculating the prime factors of a large number is a
difficult task. So this formula does not really provide an
easy method for evaluation of gcd.
Relative Prime Numbers:
a and b are said to be relative prime numbers if they
have no factor (other than ±1 ) in common, i.e,
if
gcd (a, b) = ±1.
7
Modular Arithmetic: A Revision
If a is an integer and
n is a positive integer
a mod n = remainder on dividing a by n
a = a/n * n + a mod n
Two numbers are said to be CONGRUENT
MODULO n if
a mod n = b mod n
a b mod n
8
Modular Arithmetic:
A Revision (continued)
Modular Arithmetic: a = q.n + r
q = a/n
0 <= r <n;
x largest integer that is less than or equal to x.
r
0
1.n
2.n
q.n
a
(q+1).n
r
-q.n
0
a
-(q-1).n
Thus 11 = 1.7 + 4
-11 = -2.7 + 3
-3.n
r = 4 = 11 mod 7
r = 3 =-11mod 7
-2.n
-n
9
Theorems:
Theorems:
1.
2.
3.
4.
a b mod n if n | (a-b)
a mod n = b mod n
a = b mod n
a = b mod n b = a mod n
a = b mod n and b = c mod n
a = c mod n
10
Modular Arithmetic Operations:
All Integers
Modulo operator
Integers from 0 to (n-1)
Modular Arithmetic Operations:
1. [(a mod n) + (b mod n)] mod n = (a + b) mod n
2. [(a mod n) – (b mod n )] mod n = (a – b) mod n
3. [(a mod n) * (b mod n )] mod n = (a * b) mod n
•
11
Examples of Modular Arithmetic:
11 7 mod 13 = (11 4 * 11 2 * 11) mod 13
=[(11 4 mod 13) * (11 2 mod 13) * (11 mod 13)]mod 13
2 mod 13 = 4
11
(11 2 * 11 2) mod 13
= ((11 2 mod 13) * (11 2 mod 13)) mod 13
= 16 mod 13 = 3
7 mod 13 = (3 * 4 * 11) mod 13 = 2
11
Thus Rules of Addition, Subtraction and Multiplication
carry over into Modular Arithmetic.
12
Additive inverse, Multiplicative inverse:
Additive Inverse or Negative of a number:
y = negative of a number x mod n
if x + y 0 mod n
Example:
Additive inverse of 5 mod 8 is 3.
Multiplicative Inverse:
y = multiplicative inverse of a number x
if x * y = 1 mod n
13
Properties of Modular Arithmetic:
Example:
Multiplicative inverse of 3 mod 8 is 3
Not all numbers may have a multiplicative inverse.
Properties of Modular Arithmetic: for a prime
number n:
Zn = set of non-negative integers less than n
={0, 1, 2, ………….(n-1)}
Zn Set of residues modulo n.
14
Properties of Modular Arithmetic: (cont.)
For integers in Zn, the following properties hold:
Commutative law:
(w + x) mod n = (x + w) mod n
(w * x) mod n = ( x * w) mod n
Associative laws:
[(w + x) + y] mod n = [w + (x + y)] mod n
[(w * x) * y] mod n = [w * (x * y)] mod n
Distributive law:
[w * (x + y)] mod n = [(w * x) + (w * y)] mod n
15
Properties of Modular Arithmetic: (cont.)
Identities:
(0 + w) mod n = w mod n
(1 * w) mod n = w mod n
Additive Inverse (w):
For each w Zn ,
there exists a z in Zn such that w + z 0 mod n
16
4 steps to Euler’s Corollary
Step 1
a
a positive integer, not divisible by Þ
Þ
a prime number
Fermats Theorem: ap-1= 1 mod p
Alternate Form: ap= a mod p
For Fermat’s Theorem, it is SUFFICIENT for p
to be a prime number.
Even if ap-1 were to be 1 for all values of a, it
does not NECESSARILY mean that p is prime.
Note: LHS = a**p
17
Fermat’s Theorem
If Þ is prime and a is a positive integer not
divisible by p,
aÞ-1 = 1 mod Þ OR aÞ = a mod Þ
PROOF:
Consider the set
ZÞ= {0,1,…. Þ –1}
We know that if each element of ZÞ is multiplied
by “a mod Þ”, the result is a set of all the
elements of ZÞ (with a different sequence)
18
Fermat’s Theorem: Proof
On multiplying all the elements of ZÞ ,except 0,
we get (Þ-1)!
On multiplying each element of ZÞ,, except 0,
with “a mod p”, we get
{0, a mod Þ, 2a mod Þ……(Þ-1)a mod Þ}
This set consists of all the elements of ZÞ in
some order. Hence if all the elements are
multiplied together, except 0, we should get
(Þ-1)!
19
Fermat’s Theorem: Proof
(cont.)
{a mod Þ * 2a mod Þ… *(Þ-1) a mod p} mod Þ
= (Þ-1)!
OR a Þ-1 (Þ-1)! mod Þ = (Þ-1)!
(Þ-1)! is relatively prime to Þ. So It can be
cancelled
OR a Þ-1 mod Þ = 1
OR a Þ-1 =1 mod Þ
OR aÞ = a mod Þ
20
A Definition:
Square-free numbers
a square-free, or quadratfrei,
integer: one divisible by no perfect
square, except 1.
Examples: 10 is square-free but 18 is not,
as it is divisible by 9 = 32.
The smallest square-free numbers: 1, 2,
3, 5, 6, 7, 10, 11, 13, 14, 15, 17, 19,
21, 22, 23, 26, 29, 30, 31, 33, 34, 35,
37, 38, 39, ...
21
Fermat Liars
Carmichael number: a composite positive
integer n which satisfies the equation
bn-1 = 1 mod n
for all positive integers b which are relatively
prime to n
Korselt Theorem (1899): A positive odd
composite integer n is a Carmichael number if
and only if n is square-free, and for all prime
divisors p of n, it is true that (p − 1) divides
(n − 1).
22
Carmichael Numbers
Korselt: found the properties, but could not
find an example
Carmichael (1910) found the first example of
561 = 3x11x17.
positive
odd
composite integer
square-free
for all prime divisors p of n, (p − 1) divides (n − 1).
2, 10 and 16 divide 560
Other Examples: = 1105, 1729, 2465, 2821,
6601, 8911….
23
4 steps
…..continued 2
Step 2: n
a positive integer
Euler’s Totient Function
(n) = number of positive integers less than n
and relatively prime to n
If n = Þ, a prime number,
(n) = (Þ-1);
Ex 1: (37) = 36 because 37 is prime;
Ex 2: (35) =24;
leaving aside 5,10,15,20,25,30,7,14,21,28
24
Euler’s Totient Function
(n) = number of positive integers less than n
and relatively prime to n.
If n = Þ * q where Þ and q are both prime.
n is called a SMOOTH NUMBER (ie it is a
product of smaller prime numbers.)
(n) = (Þ*q)
(p) = Þ - 1
(q) = q – 1
To Prove: (p.q) = (p-1).(q-1)
25
Euler’s Totient Function
for the product of two prime numbers
For (n) the residues will be
S1={0,1,2,………………..(Þq-1)}
Out of S1, the residues that are not relatively
prime to n are:
S2 = {Þ, 2Þ, ….(q-1) Þ},
S3 = {q, 2q,……(Þ-1)q}
and 0
26
Euler’s Totient Function
for the product of two prime numbers
contd.
The number of elements of S1 = Þq
The number of elements of S2 = q-1
The number of elements of S3 = Þ-1
Hence the number of relatively prime elements
in S1 is:
(n)= Þq – [(q-1)+(Þ-1)+1]
= Þq – q + 1 - p
= (Þ-1)(q-1) = (Þ) * (q)
27
4 steps
…..continued 3
Step 3: Euler’s theorem: Generalization
of Fermat’s theorem:
If a and n are relatively prime
Euler’s Theorem
a(n) + 1 = a mod n
Note: LHS = a**{(n) +1}
28
Euler’s Theorem
For every a and n that is relatively prime,
a(n) = 1 mod n
PROOF:
If n = prime,
(n) = n – 1
By Fermat’s Theorem a(n) = 1 mod n
If n is a positive integer, (n) = the number of
positive integers less than n and relatively
prime to n.
29
Euler’s Theorem: Proof
Consider such positive integers as follows:
S1 = {x1, x2…… x(n) }
The members of S1 contain no duplicates.
Now multiply each element with a mod n
S2 = {a x1mod n, a x2mod n… a x(n) mod n}
30
Euler’s Theorem Proof ……..cont.
The set S2 is a permutation of S1 because:
i)
a is relatively prime to n.
ii)
xi is relatively prime to n.
iii)
Therefore axi is also relatively prime to n.
Hence every element axi mod n will have a
value less than n.
Hence every element of S2 is relatively prime to
n and less than n.
Moreover the number of elements of S2 is equal
to that of S1.
31
Euler’s Theorem Proof ……..cont.
Moreover S2 contains no duplicates.
It is because if
axi mod n = axj mod n, then
xi must be equal to xj
But S1 has no duplicates
32
Euler’s Theorem Proof ……..cont.
On multiplying the terms of S1 and S2
(n)
(n)
( axi mod n) = xi OR
i=1
i=1
(n)
(n)
(axi)=( xi )mod n OR
i=1
i=1
(n)
a
= 1 mod n
OR
(n) + 1
a
= a mod n
33
4 steps
…..continued 4
Step 4: Euler’s Corollary
Given two prime numbers p and q,
Two integers n and m such that
n=pq, and,
m is any number such that
0<m<n
Now m and n are not required to be relatively
prime.
Euler’s Corollary: m(n) + 1 =m(p-1)(q-1) +1
=m mod n
34
Proof
Corollary to Euler’s Theorem …1
Given: 2 prime numbers p and q. Consider two
integers m and n such that n = p*q and
0<m<n
Step 1
m (n) + 1 = m(p-1)(q-1) + 1
Since n = p.q where p and q are prime, Euler’s
Totient function:
(n) = (p-1)(q-1)
35
Proof
Corollary to Euler’s Theorem
…2
Step 2
To prove
m (n) + 1 =m (p-1)(q-1)+1 = m mod n
Two possibilities: Either gcd(m,n) is equal to 1
or it is NOT equal to 1.
The First Possibility:
If gcd(m,n) = 1
i.e.if m and n are relatively prime,
by virtue of Euler’s theorem,
the relationship holds.
36
Proof
Corollary to Euler’s Theorem
…3
The Second Possibility: If gcd(m,n) != 1,
m is either a multiple of p or it is a multiple of q
(Can’t be a multiple of both since m<n)
Consider m as a multiple of p.
Then gcd(m,q)=1
m (q) = 1 mod q --by Euler’s theorem
Therefore by Modulo arithmetic rules,
[m (q)](p) = 1 mod q OR
m(n) = 1 mod q OR m(n) = 1 + kq
(where k = some integer)
37
Proof
Corollary to Euler’s Theorem
…4
Multiply with m = cp where c is an integer
m(n)+1 = m + kcqp = m + kcn
= m mod n
If m was to be a multiple of q, a similar process
would again bring us to the same conclusion.
Hence:
m(n)+1 = m(p-1)(q-1)+1 = m mod n
38
Proof
Corollary to Euler’s Theorem
…5
If k is an integer,
mk(n)+1 = [(m(n) )k * m ] mod n
= [(1)k * m] mod n by Euler’s Theorem
= m mod n
39
“Having a state-of-the-art alarm system for your
home does little good, if a burglar can walk up to
your front door and watch you enter the disarm
code.”
Where is W. Diffie?: Whitfield Diffie, the
inventor of the Public Key
Encryption concept,and Sun's Chief
Security Officer, named as a “SUN
FELLOW”.
40
A definition and a formula: A revision
TOTIENT FUNCTION: (n) = number of
positive integers less than n and relatively
prime to n
If n = Þ * q where Þ and q are both prime,
(n) = (Þ-1)(q-1)
Step 4: Euler’s Corollary: Given
two prime numbers p and q, and,
two integers n and m such that
n=pq, and, 0<m<n
m(n) + 1 =m mod n
41
RSA Method
Choose 2 prime numbers: p, q
Compute
n=pq,
n is called the modulus.
(an ordinary product, not a mod product;
p and q: nearly equal, of 1024 bits or more)
DEFINITION: Smooth Number: product of two prime numbers
z=(p-1)(q-1)
( i.e. z is the Totient function of n)
Choose e, so that
e is a part of the public key.
3 ≤ e < z, and,
it has no common factor with z
(i.e. e and z are relatively prime or co-prime; e is usually a
“smaller” odd number: Example: e =3 for signatures and 5
for encryption; values like 65537 may be considered.) 42
RSA method
public vs private
Find d, so that
d is less than z, and,
(ed-1) is exactly divisible by z --> (de mod z = 1)
(i.e. d is the multiplicative inverse of e mod z; d can
be calculated by using the Extended Euclid’s Algorithm)
p, q, z and d are private.
n and e are public.
Public Key=(n, e)
Private Key=(n, d)
It is infeasible to find d, given n and e.
43
Size of Numbers
200 decimal digit number:
approx 663 bits: factorization done in May
2005 by lattice sieve algorithm
(takes thousands of MIPS years; 1 GHz:
Pentium: 250 MIPS machine)
309 decimal digits:
1024 bits
Number of bits of plain text < key length
Size of ciphertext = key length
Public key: small; private key: larger
44
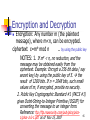
Encryption and Decryption
Encryption: Any number m (the plaintext
message), where m<n, can be encrypted.
ciphertext c=me mod n
.. by using the public key
NOTES: 1. If me < n, no reduction, and the
message may be obtained easily from the
ciphertext. Example: Encrypt a 256 bit data ( say
secret key) by using the public key of 5. the
result of 1280 bits. If n = 2048 bits, such small
values of m, if encrypted, provide no security.
2. Public Key Cryptographic Standard #1 (PKCS #1)
gives Octet-String-to-Integer Primitive (OS2IP) for
converting the message to an integer form.
Reference: ftp://ftp.rsasecurity.com/pub/pkcs/pkcs- 45
1/pkcs-1v2-1.pdf as of Nov 15, 2007
Proof
Decryption: cd mod n gives us back m.
d
PROOF: To prove that c mod n is equal to
m:
cd mod n = (me)d mod n = m de mod n
de =1 mod z. -- Refer to slide 43
Therefore de = kz +1 =k(n) +1
m de = m k(n) +1 = m .(m (n)) k
By the corollary to Euler’s theorem,
m(n) = 1 mod n = 1
since 1<n
Hence cd mod n= m de mod n = m
46
Multiplicative Inverse: Revision
Extended Euclid’s Algorithm
EXTENDED EUCLID(m, b)
1.(A1, A2, A3)(1, 0, m);
(B1, B2, B3)(0, 1, b)
2. if B3 = 0,
return A3 = gcd(m, b); no inverse
3. if B3 = 1
return B3 = gcd(m, b); B2 = b–1 mod m
B2: multiplicative inverse of b
4. Q = A3/B3
5. (T1, T2, T3)(A1 – Q B1, A2 – Q B2, A3 – Q
B3)
6. (A1, A2, A3)(B1, B2, B3)
7. (B1, B2, B3)(T1, T2, T3)
8. goto 2
47
Multiplicative Inverse
Let c be the Multiplicative Inverse of b mod n.
b.c = 1 mod n = k.n + 1
Therefore
b.(c + n) = (k + b).n + 1
= k1.n + 1
Thus c, c + n, c + 2n……. are all multiplicative
inverses of c. However for a field Zp, with
members as 0,1,2,3…….(p-1), the smallest
positive number would be said to be the
Multiplicative Inverse.
48
Example 1
Ref: Q 4?
p=3, q=11, two prime numbers
n=p.q=33
z=(p-1)(q-1)=2X10=20
Choose e so that e<z AND e has no common
factor with z (Hint: e=9)
Choose d so that (ed-1) is exactly divisible by z
i.e. Find inverse of e mod z.
d=9.
Message = 1000, 0101, 1100, 1100, 1111
For hand Computation: In decimal, these are
8,5,12,12,15
49
Example1
continued
Encryption and Decryption
Example of 1st row:
m
me
c= me mod n
8
134,217,728
29
5
1,953,125
20
12
5,159,780,352
12
82mod33=31
12
5,159,780,352
12
15
38,443,359,375
3
84mod33=31x31mod33
=961mod33=4
c
cd
m=cd mod n
29
14,507,145,975,869
8
20
512,000,000,000
5
12
5,159,780,352
12
12
5,159,780,352
12
3
19,683
15
c=89 mod33
88mod33=4x4mod33
=16mod33=16
89mod33=16x8mod33=
29
50
"He that will not apply new remedies must expect
new evils;….. for time is the greatest innovator"
Sir Francis Bacon (1561-1626),
British philosopher
51
Efficiency of computation
Both encryption and decryption involve ab.
((a mod n) x (b mod n)) mod n= axb mod n
Thus a2, a4, a8, a16……….. may be computed.
Efficiency:
1.depends upon better algorithms; Cormen Leiserson
Rivest Stein (CLRS) algorithm for ab mod n.
2. If p and q are known, Chinese Remainder Theorem
(CRT) can help in sharply reducing the calculation;
Garner’s Formula: 11 times faster than CRT; requires
only one pre-computed multiplicative inverse at the
cost of a higher memory requirement
52
Developing an Algorithm
b, the exponent, in its binary number representation:
bk bk-1 bk-2……. b0
b = bk. 2k + bk-1. 2k-1 + ……… + b1. 21 + b0. 20
If ci = bi.2i
ab mod n = ((a ck ). (a ck -1).…….. (a c1 ). (a c0 ))modn
ab mod n = ( (aci))mod n, as i varies from 0 to k.
Note: a ** ci
ab mod n = ( (aci))mod n
=(((((a ck )mod n). (a ck -1))mod n). …….. (a
))mod n. (a c0 )) mod n
c
1
53
Cormen Leiserson Rivest Stein (CLRS) algorithm
for efficiently computing d= ab mod n
k: the highest (non-zero) value when b is expressed in
binary form:
b = bk 2k+ bk-1 2k-1+ ..+ b1 21+ b0
c 0; d 1 ;
for i k down to 0
do c 2xc ;
d (dxd) mod n ;
if bi = 1
then c c + 1 ;
d (dxa) mod n ;
return d ;
The final value of c is the exponent b. The two steps
for the calculation of c are not required, if the only
objective is to find the value of d.
54
Example:
11
128 mod527
11 is 1011 in binary.
So b3 = b1 = b0 = 1.
Only b2= 0
c = 0, d = 1
Step 1: for i = 3
c=0, d = 1,
For b3= 1, c = 1,
d= 128 mod 527 = 128
Step 2: for i = 2: c =2, d = 128x128 mod 527
b2= 0
= 16,384 mod 527 =47
55
Example: 12811mod527
continued
Step3: for i =1: c = 4,
d = 47x47mod 527 = 2209mod 527 =101
For b1= 1, c = 5,
d= 101x128mod527= 12928mod527=280
Step4: for i =0: c = 10,
d=280x280mod527= 78,400mod527=404
For b0= 1, c = 11,
d= 404x128mod527= 51712mod527=66
Hence 12811mod527 = 66
56
Use of CRT
Since the public key e may be much smaller in
terms of number of bits than d Efficiency:
more important while doing md mod n.
If the private key d owner knows the values of
p and q, CRT can be used for better
efficiency.
57
Efficiency of computation:
Chinese Remainder Theorem
CRT: Possible to reconstruct integers in a particular
range from their residues modulo a set of pair-wise
relatively prime moduli.
Ref: Sun Tzu Suan Ching of 3rd century: Sun Tzu's
Calculation Classic" (more exact definition: next slide)
TERMINOLOGY: A and B: members of a group ZN:
Let N = n1. n2 . n3 . n4 . ………. nk, where n1 ..., nk are
integers which are pairwise coprime (meaning gcd
(ni, nj) = 1 whenever i ≠ j).
Let
a1 = A mod n1; a2 = A mod n2 ; ……..
…………………….. ak = A mod nk
58
Chinese Remainder Theorem
continued 2
CRT: (i) There is a one-to-one mapping
between A (a1, a2, ……… ak).
(a1, a2, ……… ak): called the CRT representation
of A
(ii) Operations between any two members- A
and B- of ZM may be equivalently performed
on the corresponding elements of the two
tuples (a1, a2, ……… ak) and
(b1, b2, ……… bk).
59
CRT
Two problems: Find A
Problem 1:
Find A if
A mod 3 = 2
A mod 5 = 0
A mod 7 = 0
Problem 2:
Find B if
B mod 7 = 3
B mod 11 = 0
B mod 13 = 6
60
CRT
Two problems: One Solution
Let N = n1. n2 . n3 . n4 . ………. nk, where n1 ..., nk
are integers which are pairwise coprime
(meaning gcd (ni, nj) = 1 whenever i ≠ j).
For 1 ≤ i ≤ k
ai = A mod ni
Ni = N/ ni
Let inverse of Ni mod ni = Ri
( i. e.
Ri.Ni mod ni = 1)
A = (Σ ai. Ni . Ri ) mod N
61
CRT: Problem 1:
Find A. Given a1, a2, ……… ak
Find A if A mod 3 = 2; A mod 5 = 0; A mod 7 = 0
N = n1. n2 . n3 = 3*5*7 = 105
N1 = N/ n1 = 35; R1.N1mod 3 = 1 R1 = 2
(By using (a x b)mod n
=[a mod n x b mod n] mod n
R1.35 mod 3 (R1.(35 mod 3)) = R1.2 mod 3=1)
N2 = N/ n2 = 21 ; R2.N2mod 5 = 1 R2 = 1
N3 = N/ n3 = 15 ; R3.N3mod 7 = 1 R3 = 1
A = (2.35.2 + 0.21.1 + 0.15.1)mod 105 = 35
62
CRT: Problem 2:
Find B
Use: (a + b)mod n
=[a mod n + b mod n] mod n
Given: B mod 7 = 3; B mod 11 = 1; B mod 13 = 6
N = n1. n2 . n3 = 7*11*13 = 1001
N1 = N/ n1 = 143; R1.N1mod 7 = 1 R1 = 5
N2 = N/ n2 = 91; R2.N2mod 11 = 1 R2 = 4
N3 = N/ n3 = 77; R3.N3mod 13 = 1 R3 = 12
A = (3.143.5 + 1.91. 4 + 6.77. 12)mod 1001 =
(2145 mod 1001+364+5544 mod 1001) mod1001
= (143 + 364 + 539) mod 1001 = 1046 mod 1001
= 45
63
CRT Algorithm:
Given: k, n1, n2 , n3 , a1, a2 , a3;
To Find: A
A 0; N n1 ;
for i 2 to k
N N*ni;
for i 1 to k
Ni N/ ni ;
Ri Ni-1 mod ni ;
c Ri.Ni.ai mod N ;
A A + c mod N ;
return A ;
64
CRT:
Fermat’s Theorem for Computational Ease
CRT representation of A = md mod pq:
a1 = md mod p and a2 = md mod q.
d may be much larger than p or q. In such a
case, Fermat’s Theorem may be used for
simplification.
By Fermat’s Theorem: aÞ-1 = 1 mod Þ:
a1 = md mod p = md mod(p-1) mod p, and
a2 = md mod q = md mod(q-1) mod q.
From a1, a2: A can be evaluated..
65
Example: RSA Exponentiation using CRT
A= 1283031 mod 3599…1
N = 3599 = 61x59 = pq
Using CRT:
A = 1283031 mod 3599 a1. a2
Where a1 = 1283031 mod 61
a2 = 1283031 mod 59
Using Fermat’s theorem: aÞ-1 mod Þ = 1
a1 = 1283031 mod 60 mod 61 = 12831mod 61
a2 = 1283031mod58 mod 59 =12815 mod 59
66
Example: 1283031 mod 3599 …
CLRS Algorithm for
a1 =
continued 2
12831mod 61
31: 11111;
c 0; d 1;
i = 4: c = 0, d = 1
b4 = 1: c = 1; d = 1x128 mod 61 = 6
i = 3: c = 2, d = 6x6 mod 61 = 36
b3 = 1: c = 3; d = 36x128 mod 61 = 33
(36x128 = 4608 = 61x75 + 33)
i = 2: c = 6, d = 33x33 mod 61 = 52
(33x33 = 1089 = 61x17 + 52)
b2 = 1: c = 7; d = 52x128 mod 61 = 7
(52x128 = 6656 = 61x109 + 7)
67
Example: 1283031 mod 3599
CLRS Algorithm for a1 = 12831mod 61 …. continued 3
i = 1: c = 14, d = 7x7 mod 61 = 49
b1 = 1: c = 15; d = 49x128 mod 61 = 50
(49x128 = 6272 = 61x102 + 50)
i = 0: c = 30, d = 50x50 mod 61 = 60
(50x50 = 2500 = 61x40 + 60)
b0 = 1: c = 31; d = 60x128 mod 61 = 55
(60x128 = 7680 = 61x125 + 55)
Hence
a1 = 12831mod 61 = 55
68
Example: 1283031 mod 3599 …
CLRS Algorithm for
a2 =
continued 4
12815 mod 59
15: 1111;
c 0; d 1;
i = 3: c = 0, d = 1
b3 = 1: c = 1; d = 1x128 mod 59 = 10
i = 2: c = 2, d = 10x10 mod 59 = 41
b2 = 1: c = 3; d = 41x128 mod 59 = 56
(41x128 = 5248 = 59x88 + 56)
i = 1: c = 6, d = 56x56 mod 59 = 9
(56x56 = 3136 = 59x53 + 9)
b1 = 1: c = 7; d = 9x128 mod 59 = 31
(9x128 = 1152 = 59x19 + 31)69
Example: 1283031 mod 3599 …
CLRS Algorithm for a2 = 12815 mod 59..
continued 5
i = 0: c = 14, d = 31x31 mod 59 = 17
(31x31 = 961 = 59x16 + 17)
b0 = 1: c = 15; d = 17x128 mod 59 = 52
(17x128 = 2176 = 59x36 + 52)
Hence a2 = 12815 mod 59 = 52
For calculating A, assume
n1 = p = 61
n2 = q = 59
Now we have to find Ni N/ ni ;
Ri Ni-1 mod ni
70
Finding Inverses
XTENDED EUCLID(m, b)ALGORITHM: m>b
1.(A1, A2, A3)(1, 0, m);
(B1, B2, B3)(0, 1, b)
2. if B3 = 0,
return A3 = gcd(m, b); no inverse
And gcd(m, b)= A2.b + A1.m
3. if B3 = 1
return B3 = gcd(m, b); B2 = b–1 mod m
B2: multiplicative inverse of b with modulus m
4. Q = A3/B3
5. (T1, T2, T3)(A1 – Q B1, A2 – Q B2, A3 – Q
B3)
6. (A1, A2, A3)(B1, B2, B3)
7. (B1, B2, B3)(T1, T2, T3)
8. goto 2
Note: In this process, the invariants are: 71
Example: Inverse of 550 in GF(1759)
Hence 355 is multiplicative inverse of 550 mod 1759.
If B2 be –ve, subtract it from m to get the answer. 72
Example: 1283031 mod 3599 …
continued 6
Finding Inverses: EXTENDED EUCLID ALGORITHM
N1 = N/ n1 = 59; R1.59 mod 61 = 1
1 0
61
0
1
59
1
0
1
59
1
-1
2
29 1
-1
2
-29 30 1
Therefore R1 = 30
N2 = N/ n2 = 61; R2.61 mod 59 = R2.(61 mod
59). mod 59 = R2.2 mod 59 =1
1
0
59
0
1
2
29 0
1
2
1
-29 1
Therefore R2 = -29 + 59 = 30
73
Example: 1283031 mod 3599 … continued 7
To Find A by using CRT
A = (55*59*30 + 52*61*30) mod 3599
=((55*59 + 52*61) mod 3599 *30) mod 3599
=((3245 + 3172) mod 3599 *30) mod 3599
=((6417) mod 3599 *30) mod 3599
=(2818*30) mod 3599
=(84540) mod 3599
=1763
The calculation requires two multiplicative
inverses.
74
Example: 1283031 mod 3599
… continued 8
To Find A by using Garner’s Formula
Garner’s Formula:
A = (((a1- a2)(R1 mod p)) mod p)q + a2
where (R1. q-1 )mod p = 1 i.e. R1 = q-1 for mod p
Note: Garner’s formula requires the calculation of only
one inverse – which can be pre-computed.
R1 = 30
A = (((55- 52)(30 mod 61)) mod 61)59 + 52
= 29x59 + 52 = 1711 + 52 = 1763.
Reference:
http://en.wikipedia.org/?title=Talk:Chinese_remainder_theorem
75
Key Generation
Select two large prime numbers p and q.
-- each of the order of 1024 bits about
309 decimal digits
n = p.q
Iterative process: (may use Euclid’s Extended
Algorithm or some more efficient one)
Select e such that gcd (z,e) =1
---The probability that two random numbers would
be relatively prime is said to be 0.6.
Select d such that d.e = 1 mod z
RSA decryption: 4 times faster than in CRT;
requires twice the memory
76
Security
Security is in factorization of large numbers
155 dec digits (512 bits) number was
factorized in Aug 99 using 8000 MIPs-Years.
(A 1 GHz Pentium is a 250 MIPs machine.
Thus using one pentium machine, it may
have taken 32 years to do the job.)
In 1999, it was thought that 1024 bits
number would take about 10 million
MIPs-Years (40,000 years of a pentium
machine)
2005: 1024 bit number was factorized
77
Public-Key Cryptography Standard (PKCS) #1:
RSA Cryptography Standard
Reference: ftp://ftp.rsasecurity.com/pub/pkcs/pkcs-1/pkcs-1v2-1.doc as of Nov
18, 2007
Two Formats for RSA
For message encryption (Ref: Section 7.2.1 Step 2b)
0
2 At least 8 random 0
nonzero octets
data
NOTES: 1 byte of 0s; second byte specifies message;
eight random octets: cipher different; a byte of zeros
ends padding
For signatures (Ref: Section 9.2 Step 5)
0
1 At least 8 octets
of FF
0
data
78