* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Set 1 File
Airborne Networking wikipedia , lookup
Deep packet inspection wikipedia , lookup
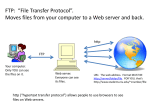
Internet protocol suite wikipedia , lookup
Remote Desktop Services wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Cross-site scripting wikipedia , lookup
Zero-configuration networking wikipedia , lookup
UniPro protocol stack wikipedia , lookup
Networking review Chapter 1, Chapter 2, Chapter 3 1 Theory chapters Why Networked Java? Basic Network Concepts Basic Web Concepts 2 Networking tasks Java Network Programming will help you to take advantage of Java's network class library to quickly and easily write programs that accomplish many common networking tasks. Some of these include : Browsing the Web with HTTP Parsing and rendering HTML Sending email with SMTP Receiving email with POP and IMAP Writing multithreaded servers Installing new protocol and content handlers into browsers Encrypting communications for confidentiality, authentication, and guaranteed message integrity Designing GUI clients for network services Posting data to server-side programs Looking up hosts using DNS Downloading files with anonymous FTP Connecting sockets for low-level network communication Distributing applications across multiple systems with Remote Method Invocation 3 Why Networked Java ? Java was the first programming language designed from the ground up with networking in mind and it makes writing network programs easy. This course shows you many of complete programs that take advantage of the Internet. Some are simple textbook examples, while others are completely functional applications. One thing you'll notice in the fully functional applications is just how little code is devoted to networking. The part of the program that deals with the network is almost always the shortest and simplest. In brief, it is easy for Java applications to send and receive data across the Internet 4 What Can a Network Program Do ? Retrieve Data Network client retrieves data from a server. Network clients written in Java can speak standard protocols like HTTP, FTP, or SMTP to communicate with existing servers written in a variety of languages. More importantly, programs can speak custom protocols designed for specific purposes. Send Data Web browsers are optimized for retrieving data: they send only limited amounts of data back to the server. Java programs have no such limitations. (File storage and Massively parallel computing) Peer-to-Peer Interaction (Games, Real-time chat, Collaborative work, Video conference, File sharing, e.g. BitTorrent) Servers (file servers, print servers, email servers, directory servers, domain name servers, FTP servers, TFTP servers or custom servers like online games server ) Searching the Web (Google search, spiders, agents) Electronic Commerce (Java applets) 5 Basic Network Concepts A network is a collection of computers and other devices that can send data to and receive data from each other. Each machine on a network is called a node. Most nodes are computers, printers, routers, bridges, gateways, etc. The word host to refer to a node that is a general-purpose computer. Every network node has an address. All modern computer networks are packet-switched networks: data traveling on the network is broken into chunks called packets and each packet is handled separately. Each packet contains information about who sent it and where it's going. A protocol is a precise set of rules defining how computers communicate: the format of addresses, how data is split into packets, and so on. 6 The Layers of a Network 7 The Internet Layer The Internet Protocol (IP) is the most widely used network layer protocol in the world and the only network layer protocol Java understands. Data is sent across the internet layer in packets called datagrams. Each IP datagram contains a header between 20 and 60 bytes long and a payload that contains up to 65,515 bytes of data. (In practice, most IP datagrams are much smaller, ranging from a few dozen bytes to a little more than eight kilobytes.) 8 Transport Layer The transport layer is responsible for ensuring that packets are received in the order they were sent and making sure that no data is lost or corrupted. If a packet is lost, the transport layer can ask the sender to retransmit the packet. Transmission Control Protocol (TCP), is a high-overhead protocol that allows for retransmission of lost or corrupted data and delivery of bytes in the order they were sent. User Datagram Protocol (UDP), allows the receiver to detect corrupted packets but does not guarantee that packets are delivered in the correct order (or at all). However, UDP is often much faster than TCP. TCP is called a reliable protocol; UDP is an unreliable protocol. 9 The Application Layer The layer that delivers data to the user is called the application layer. HTTP (for the World Wide Web) makes sure that your web browser knows to display a graphic image as a picture, not a long stream of numbers. SMTP, POP, and IMAP for email; FTP, FSP, and TFTP for file transfer; NFS for file access; NNTP for news transfer; Gnutella, FastTrack, BitTorrent, and Freenet for file sharing; and many, many more. In addition, your programs can define their own application layer protocols as necessary. 10 Internet addresses 11 Every host on the Internet is identified by a unique, four-byte Internet Protocol (IP) address. This is written in dotted quad format like 199.1.32.90 where each byte is an unsigned integer between 0 and 255. There are about four billion unique IP addresses (2³²). When data is transmitted across the network, the packet’s header includes the address of the machine for which the packet is intended (the destination address) and the address of the machine that sent the packet (the source address). Routers along the way choose the best route to send the packet along by inspecting the destination address. The source address is included so the recipient will know who to reply to. Domain Name System (DNS) Numeric addresses are mapped to names like www.uop.edo.jo by DNS. Each site runs domain name server software that translates names to IP addresses and vice versa DNS is a distributed system 12 The InetAddress Class The java.net.InetAddress class represents an IP address. It converts numeric addresses to host names and host names to numeric addresses. It is used by other network classes like Socket and ServerSocket to identify hosts 13 Ports 14 In general a host has only one Internet address This address is subdivided into 65,536 ports. Ports are logical abstractions that allow one host to communicate simultaneously with many other hosts Many services run on well-known ports. For example, http tends to run on port 80 Ports numbers are used by transport layer 15 The Client/Server Model 16 IETF RFCs Requests For Comment Document how much of the Internet works Various status levels from obsolete to required to informational TCP/IP, telnet, SMTP, MIME, HTTP, and more http://www.faqs.org/rfc/ 17 W3C (World Wide Web Consortium) IETF is a relatively informal, democratic body open to participation by any interested party. W3C is a vendor organization, controlled by dues-paying member corporations, that explicitly excludes participation by individuals. For the most part, the W3C tries to define standards in advance of implementation. W3C standards include HTTP, HTML, and XML. 18 Basic Web Concepts Many of your programs will be applets on web pages, servlets running on the server, or web services that need to talk to other web servers and clients. Therefore, it’s important to have a solid understanding of the interaction between web servers and web browsers. The Hypertext Transfer Protocol (HTTP) is a standard that defines how a web client talks to a server and how data is transferred from the server back to the client. The most common format for data transferred over the Web is the Hypertext Markup Language (HTML). 19 URL (I) HTML is a “hypertext markup language” because it includes a way to specify links to other documents identified by URLs. A URL, short for "Uniform Resource Locator", is a way to clearly identify the location of a resource on the Internet. The syntax of a URL is: protocol://username@hostname:port/path/filename?query#frag ment Protocol part can be file, ftp, http, https … Hostname part of a URL is the name of the server that provides the resource you want, such as www.oreilly.com 20 URL (II) The username is an optional name for the server. The port number is also optional. The path points to a particular directory on the specified server. The filename points to a particular file in the directory specified by the path. The query string provides additional arguments for the server. It’s commonly used only in http URLs, where it contains form data for input to programs running on the server. The fragment references a particular part of the remote resource. 21 URL (III) A named anchor is created in an HTML document with a tag, like this: <A NAME="xtocid1902914">Comments</A> This tag identifies a particular point in a document. To refer to this point, a URL includes not only the document’s filename but the named anchor separated from the rest of the URL by a #: http://www.cafeaulait.org/javafaq.html#xtocid1902914 22 Example URLs http://java.sun.com/ file:///Macintosh%20HD/Java/Docs/JDK%201.1.1%20docs/api/ja va.net.InetAddress.html#_top_ http://www.macintouch.com:80/newsrecent.shtml ftp://ftp.info.apple.com/pub/ mailto:[email protected] telnet://utopia.poly.edu ftp://mp3:[email protected]:21000/c%3a/stuff/mp3/ http://[email protected]/ http://metalab.unc.edu/nywc/comps.phtml?category=Choral+Wo rks 23 Normal web surfing uses these two steps: The browser requests a page The server sends the page Data flows primarily from the server to the client. 24 Forms There are times when the server needs to get data from the client rather than the other way around. The common way to do this is with a form like this one: 25 CGI The user types data into a form and hits the submit button. The browser sends the data to the server using the Common Gateway Interface, CGI. CGI uses the HTTP protocol to transmit the data, either as part of the query string or as separate data following the MIME (Multipurpose Internet Mail Extensions)header. 26 GET and POST When the data is sent as a query string included with the file request, this is called CGI GET. When the form data is sent as data attached to the request following the MIME header, this is called CGI POST Other request types: HEAD retrieves only the header for the file, not the actual data. PUT uploads a resource to the server, and DELETE removes a resource from the server. 27 HTTP Web browsers communicate with web servers through a standard protocol known as HTTP, an acronym for HyperText Transfer Protocol. This protocol defines 28 how a browser requests a file from a web server how a browser sends additional data along with the request (e.g. the data formats it can accept), how the server sends data back to the client response codes A Typical HTTP Connection 29 Client opens a socket to port 80 on the server. Client sends a GET request including the name and path of the file it wants and the version of the HTTP protocol it supports. The client sends a MIME header. The client sends a blank line. The server sends a MIME header The server sends the data in the file. The server closes the connection. What the client sends to the server GET /index.html HTTP/1.0 (operation to return resource) Accept: text/html, text/plain, image/gif, image/jpeg (data accepted by client) User-Agent: Lynx/2.4 libwww/2.1.4 (browser type) Host: www.cafeaulait.org (server name) 30 MIME MIME is an acronym for "Multipurpose Internet Mail Extensions". an Internet standard defined in RFCs 2045 through 2049 originally intended for use with email messages, but has been adopted for use in HTTP to describe a file’s contents so that client software can tell the difference between different kinds of data. For example, HTML’s content type is text/html; the type is text, and the subtype is html. The content type for a GIF image is image/gif; the type is image, and the subtype is gif. 31 Server Response When a web server responds to a web browser it sends a response message and a MIME header along with the response that looks something like this: HTTP/1.1 200 OK Date: Mon, 15 Sep 2003 21:06:50 GMT Server: Apache/2.0.40 (Red Hat Linux) Last-Modified: Tue, 15 Apr 2003 17:28:57 GMT Connection: close Content-Type: text/html; charset=ISO-8859-1 Content-length: 107 <html> <head> <title> A Sample HTML file </title> </head> <body> The rest of the document goes here </body> </html> 32 Server-Side Programs Server generates web pages dynamically to meet user requests, instead of sending static files form hard drive. Such server-side programs are often written using servlets or Java Server Pages (JSP). They can also be written with other languages, such as C and Perl, or other frameworks, such as ASP and PHP. The concern in this book is not so much with how these programs are written as with how your programs communicate with them. One advantage to HTTP is that it really doesn’t matter how the other side of the connection is written, as long as it speaks the same basic HTTP protocol. 33 Server-Side Programs The simplest server-side programs run without any input from the user. From the viewpoint of the client, these programs are accessed like any other web page. A slightly more complex server-side program processes user input from HTML forms. Example 3-1. A simple form with input fields for a name and an email address <HTML> <HEAD> <TITLE>Sample Form</TITLE> </HEAD> <BODY> <FORM METHOD=GET ACTION="/cgi/reg.pl"> <PRE> Please enter your name: <INPUT NAME="username" SIZE=40> Please enter your email address: <INPUT NAME="email" SIZE=40> </PRE> <INPUT TYPE="SUBMIT"> </FORM> </BODY> </HTML> 34 Server-Side Programs The web browser reads the data the user types and encodes it in a simple fashion. The name of each field is separated from its value by the equals sign (=). Different fields are separated from each other by an ampersand (&). For example, the data from the form in Figure 3-3 is encoded as: username=Elliotte+Harold&email=elharo%40macfaq.com This is called the query string. 35 Server-Side Programs There are two methods by which the query string can be sent to the server: GET and POST. If the form specifies the GET method, the browser attaches the query string to the URL it sends to the server. Forms that specify POST send the query string on an output stream. GET /cgi/reg.pl?username=Elliotte+Harold&email=elharo%40macfaq.com HTTP/1.0 POST /cgi-bin/register.pl HTTP 1.0 Content-type: application/x-www-form-urlencoded Content-length: 65 username=Elliotte+Harold&email=elharo%40metalab.unc.edu GET is intended for noncommital actions, like browsing a static web page. POST is intended for actions that commit to something. 36