* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Computer Security: Principles and Practice, 1/e
Wake-on-LAN wikipedia , lookup
Deep packet inspection wikipedia , lookup
Distributed firewall wikipedia , lookup
Transport Layer Security wikipedia , lookup
Extensible Authentication Protocol wikipedia , lookup
Computer security wikipedia , lookup
Internet protocol suite wikipedia , lookup
Wireless security wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
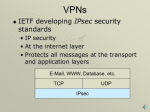
Computer Security: Principles and Practice Chapter 21 – Internet Security Protocols and Standards First Edition by William Stallings and Lawrie Brown Lecture slides by Lawrie Brown Objectives The student should be able to Define VPN, intranet VPN, extranet VPN, tunnel. Describe the advantages of link versus end-to-end encryption. Define the protection provided by SSL, TLS, IPsec. Show where the following protocols exist in the protocol stack, and describe which applications they can be used with: SSL, TLS, IPSec, S-MIME. Show a diagram of what happens to a packet during Tunnel versus Transport mode concerning the packet format. Describe the difference between IPSec’s Authentication Header and . Encapsulated Security Payload protocols Internet Security Protocols and Standards Secure Sockets Layer (SSL) / Transport Layer Security (TLS) IPv4 and IPv6 Security S/MIME (Secure/Multipurpose Internet Mail Extension) VPNs Virtual Private Network (VPN): A means of carrying private traffic over a public network Uses link encryption to give users sense that they are operating on a private network when they are actually transmitting over a public network Communications pass through an encrypted tunnel Intranet VPN: Connects two or more private networks within the same company Extranet VPN: Connects two or more private networks between different companies E.g., B2B or business-to-business communication. Remote Access VPN: A roaming user has access to a private network via wireless, hotel room, etc. Encryption Types Source Destination Router End-to-End Encryption Link Encryption Importance of Encryption Location: MAC A P L I C A P L I C TCP TCP IP IP IP LLC MAC LLC MAC LLC MAC LLC MAC Physical Physical Physical Physical Wireless MAC LLC IP Wired TCP App - Data CRC Importance of Encryption Location: IP A P L I C A P L I C TCP VPN Router/Firewall may unencrypt IPSEC/ IP LLC MAC IPSEC/ IP LLC LLC MAC MAC Physical MAC Physical LLC IP TCP Physical App - Data TCP IP LLC MAC Physical CRC Importance of Encryption Location: App. HTTPS HTTPS HTTP HTTP A P L I C A P L I C TCP TCP IP IP IP LLC MAC LLC MAC LLC MAC LLC MAC Physical Physical Physical Physical MAC LLC IP TCP App - Data CRC Link versus End-to-End Encryption Use when LINK is vulnerable: Packet sniffers & eavesdroppers Use when Intermediate nodes may be compromised Link-Specific: All packets transmitted on the single link are encrypted Connection-Specific: A connection is encrypted across all its links Encrypted for all protocol layers (at or above encryption layer) Encrypted for upper layer protocols only Intermediate nodes decrypt Intermediate nodes cannot decrypt Provides node authentication Provides user authentication Transparent to user: One key per link Not user-transparent: One key per connection One algorithm for all users User selects encryption algorithm Encryption done in hardware Encryption done in hardware or software Virtual Private Network (VPN) IP Security (IPsec) Secure Shell (SSH) Secure Socket Layer (SSL) Encryption Protocols HTTP FTP SMTP TCP or UDP HTTP HTTP SSL or TLS TCP IPSec IP IP VPN HTTPS Secure Sockets Layer (SSL) transport layer security service originally developed by Netscape version 3 designed with public input subsequently became Internet standard RFC2246: Transport Layer Security (TLS) use TCP to provide a reliable endto-end service may be provided in underlying protocol suite or embedded in specific packages SSL + HTTP used together = HTTPS HTTP SSL or TLS TCP IP SSL Protocol Stack Record: Fragmentation, compression, MAC, encryption Handshake: Setup: Negotiation of security Alert: Notifications of warnings or serious problems Change Cipher Spec: Change state to active SSL Record Protocol Services message integrity using a MAC with shared secret key similar to HMAC but with different padding confidentiality using symmetric encryption with a shared secret key defined by Handshake Protocol AES, IDEA, RC2-40, DES-40, DES, 3DES, Fortezza, RC4-40, RC4-128 message is compressed before encryption SSL Record Protocol Operation SSL Change Cipher Spec Protocol one of 3 SSL specific protocols which use the SSL Record protocol a single message causes pending state to become current hence updating the cipher suite in use SSL Alert Protocol conveys SSL-related alerts to peer entity severity • warning or fatal specific alert • fatal: unexpected message, bad record mac, decompression failure, handshake failure, illegal parameter • warning: close notify, no certificate, bad certificate, unsupported certificate, certificate revoked, certificate expired, certificate unknown compressed & encrypted like all SSL data SSL Handshake Protocol allows server & client to: authenticate each other to negotiate encryption & MAC algorithms to negotiate cryptographic keys to be used comprises a series of messages in phases 1. 2. 3. 4. Establish Security Capabilities Server Authentication and Key Exchange Client Authentication and Key Exchange Finish SSL Handshake Protocol First 3 phases: Handshake Protocol Phase 4: Change Cipher Spec Public Key Infrastructure (PKI) 7. Tom confirms Sue’s DS 5. Tom requests Sue’s DC 6. CA sends Sue’s DC Tom 4. Sue sends Tom message signed with Digital Signature Digital Certificate User: Sue Public Key: 2456 Certificate Authority (CA) 3. Send approved Digital Certificates 1. Sue registers with CA through RA Sue Register(Owner, Public Key) 2. Registration Authority (RA) verifies owners IP Security various application security mechanisms exist eg. S/MIME, PGP, Kerberos, SSL/HTTPS security concerns cross protocol layers hence would like security implemented by the network for all applications authentication & encryption security features included in next-generation IPv6 also usable in existing IPv4 IPSec general IP Security mechanisms provides authentication confidentiality key management applicable to use over LANs, across public & private WANs, & for the Internet IPSec Uses Tunnel vs. Transport Mode Encrypted: Transport Mode: End-to-End Encryption Host D Host A IP=D | ESP | Data Internet Gtwy B Gtwy C IP=D | ESP | Data IP=D | ESP | Data Host D Host A IP=D | Data Internet Gtwy B Gtwy C IP=D | Data IP=C | ESP | IP=D | Data Tunnel Mode: Encryption between two gateways: Virtual Private Network (A form of link encryption) Benefits of IPSec in a firewall/router provides strong security to all traffic crossing the perimeter in a firewall/router is resistant to bypass is below transport layer, hence transparent to applications can be transparent to end users can provide security for individual users secures routing architecture IP Security Architecture mandatory in IPv6, optional in IPv4 have two security header extensions: Authentication Header (AH) Encapsulating Security Payload (ESP) Key Exchange function VPNs want both authentication/encryption hence usually use ESP specification is quite complex numerous RFC’s 2401/2402/2406/2408 Two Modes (From Network Security Essentials 2nd Ed., W. Stallings, Prentice Hall) Authentication Header (AH) Encapsulated Security Payload (ESP encryption & authentication) Access control X X Connectionless integrity X X (AH opt.) Data Origin Authentication X X (AH opt.) Rejection of Replayed Packets X X Confidentiality X Limited Traffic Flow Confidentiality X Security Associations a one-way relationship between sender & receiver that affords security for traffic flow defined by 3 parameters: Security Parameters Index (SPI): SA IP Destination Address: Unicast Security Protocol Identifier: AH or EH has a number of other parameters seq no, AH & EH info, lifetime etc have a database of Security Associations Holds data for each SA Authentication Header (AH) provides support for data integrity & authentication of IP packets end system/router can authenticate user/app prevents address spoofing attacks by tracking sequence numbers based on use of a MAC HMAC-MD5-96 or HMAC-SHA-1-96 parties must share a secret key Authentication Header SPI = Security Association # Authentication Data = Message Authentication Code Encapsulating Security Payload (ESP) Key Management handles key generation & distribution typically need 2 pairs of keys 2 per direction for AH & ESP manual key management sysadmin manually configures every system automated key management automated system for on demand creation of keys for SA’s in large systems has Oakley & ISAKMP elements S/MIME (Secure/Multipurpose Internet Mail Extensions) security original Internet RFC822 email was text only MIME provided support for varying content types and multi-part messages with encoding of binary data to textual form S/MIME added security enhancements have enhancement to MIME email S/MIME support in many mail agents eg MS Outlook, Mozilla, Mac Mail etc S/MIME Process S/MIME Cryptographic Algorithms digital signatures: DSS & RSA hash functions: SHA-1 & MD5 session key encryption: ElGamal & RSA message encryption: AES, 3DES, etc MAC: HMAC with SHA-1 must map binary values to printable ASCII use radix-64 or base64 mapping S/MIME Public Key Certificates S/MIME has effective encryption and signature services but also need to manage public-keys S/MIME uses X.509 v3 certificates each client has a list of trusted CA’s certs and own public/private key pairs & certs certificates must be signed by trusted CA’s Summary Secure Sockets Layer (SSL) / Transport Layer Security (TLS) IPsec: IPv4 and IPv6 Security S/MIME (Secure/Multipurpose Internet Mail Extension)