* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download Securing Information Transmission by Redundancy
Survey
Document related concepts
Transcript
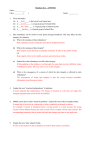
Securing Information Transmission by Redundancy Jun Li Peter Reiher Gerald Popek Computer Science Department UCLA NISS Conference October 21, 1999 1 Outline • Interruption threats are hard to counter • Redundant transmission makes interruptions harder • But redundant transmission is not as easy as using redundancy in other areas • Sample uses • Conclusion 2 Interruption Threats Source Destination An interruption attack occurs Result? No data flows to the destination 3 Problem • Many kinds of interruption threats – Corrupted routers drop packets – Transmitting over packets on shared media – Congesting links or routers • Conventional approaches won’t help – Encrypted/signed message can still be interrupted • Acknowledgement won’t help either – The acknowledgement itself is subject to interruption – Retransmission means possibly failing again • So? 4 Using Redundancy To Counter Interruptions • Don’t use a single path receiver – Any point on the single path is a point of failure • Use redundancy to secure transmission – Only parallel redundancy considered here • A node is expected to receive multiple copies of one message • Successful if at least one copy is authentically received • Redundancy has been widely used in other areas – High availability storage – Replicated execution – And many others 5 A Simple Example Source Normal delivery uses a default path What if a router is corrupted? Destination 6 How does redundant deliver help? The redundant copy gets through despite a bad router sender But . . . • Redundant transmission is tough – Discovering disjoint paths is difficult • Routing is transparent to applications – Using disjoint paths is difficult – They may not exist at all • Can try to be as disjoint as possible nevertheless – An attacker has to find a choke point or break multiple points • Scale can also cause big problems • And what about costs of sending multiple copies? 7 receiver Sample Uses of Redundancy • Revere – Secure delivery of security updates • General purpose redundant packet delivery service – Redundancy for every network user? 8 Revere - Goal: disseminate security updates to large number of machines - Assume a trusted dissemination center - Security updates - Small size but critical information - Examples: 9 New virus signature New intrusion detection signature CRL (certificate revocation lists) Offending characteristics for a firewall to monitor Revere Structure - Acks/Nacks inappropriate - Scaling, lack of complete trust, etc. - Use redundancy to send multiple copies to each node - Each node can also forward security updates to others - A node can contact multiple repository nodes for missed updates 10 General Redundant Packet Delivery Services • How could we add a redundant packet delivery service to the Internet? • What would be the best method of achieving redundancy? – Know a lot about the network? – Or rely on randomness and obscurity? • What are the costs of doing so? • How could it be easily deployable? – Proxy-based solutions? 11 Conclusion - Conventional security approaches and transmission primitives don’t adequately counter interruption threats - Redundancy is a promising tool - But effective use of redundancy is challenging - Are there other problems that redundancy can solve? - Does redundancy itself lead to new security threats? 12 Questions - Contact information - Peter Reiher: [email protected] - Jun Li: [email protected] - Gerald Popek: [email protected] 13