* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Network security
Computer network wikipedia , lookup
Airborne Networking wikipedia , lookup
Extensible Authentication Protocol wikipedia , lookup
Dynamic Host Configuration Protocol wikipedia , lookup
Parallel port wikipedia , lookup
Computer security wikipedia , lookup
Network tap wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Wake-on-LAN wikipedia , lookup
TCP congestion control wikipedia , lookup
SIP extensions for the IP Multimedia Subsystem wikipedia , lookup
Deep packet inspection wikipedia , lookup
Wireless security wikipedia , lookup
Remote Desktop Services wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Internet protocol suite wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Distributed firewall wikipedia , lookup
UniPro protocol stack wikipedia , lookup
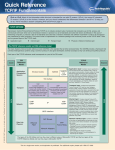
CHAPTERS 9-10 TJADEN Computer Network Security and Network Security Threats Dr. Suzanne Buchele (Most content borrowed from Ed Crowley at The University of Houston) OVERVIEW OF NETWORK SECURITY ISSUES Network security involves protecting a host (or a group of hosts) connected to a network Many of the same problems as with stand-alone computer systems apply and are more difficult: User authentication and authorization – determine the identity and privileges of users accessing the system Access control – policies that govern access privileges and mechanisms limiting what actions are permitted ADDITIONAL CHALLENGES OF NETWORK SECURITY Networking increases message vulnerability to: Interception Modification Destruction Delay Reordering Repetition Networking implies cooperation, sharing, and trust Networking also… Exposes a system to a larger pool of potential attackers Decreases the likelihood of intruders getting caught AUTHENTICATION AND AUTHORIZATION Issues: For the Server: Is the Client really who they say they are? Is the request from the Client fresh? Will an eavesdropper be able to read my response? For the Client: How do I know I’m really talking to the Server? Will an eavesdropper be able to read my request? Kerberos - Purpose Needed in environments in which: local distributed environment users on one computer can access services on other computers or servers in the network not all users have the authorization to access all other services or servers on the network users need to be authenticated for particular services users cannot be trusted to correctly identify themselves a user could pretend to be another user a user may alter the network address of their computer so that requests appear to be coming from a different computer a user may eavesdrop on exchanges and attempt attacks to gain unauthorized access to a service or server e.g. replay or man-in-the-middle attacks KERBEROS - OVERVIEW One approach – have a distributed authentication protocol, so that each server can self-authorize all attempted access from all users Kerberos approach: centralized authentication server on the local network authenticates users to servers and servers to users issues “tickets” uses symmetric key cryptography only reading says uses DES, latest version can use AES since local network, can physically distribute keys securely KERBEROS – HOW IT WORKS Central Authentication Server (AS) shares a secret key with each user Step 1: Step 2: User is authenticated to the Authentication Server (AS), is issued a ticket to be used to request access to services from the TGS User uses ticket from AS as authentication, so it can obtain tickets from the TGS for specific services it needs Step 3: User presents a ticket to a server and is granted the service KERBEROS - STEP 1: GETTING TICKET FOR TICKET GRANTING SERVICE (TGS) User enters username and password Requests ticket for TGS from the AS C => AS:(C, TGS) AS generates a ticket: Name of client; Name of TGS; IP address of client; time of issue; lifetime of ticket; session key for client and TGS All encrypted with secret key shared by AS and TGS client can’t read the ticket AS replies to client with ticket and session key for client and TGS, all encrypted with secret key shared by AS and client AS => C:(Encrypt((TicketAS, KC,TGS),KC,AS)) KERBEROS - STEP 2: GETTING A TICKET FOR A SERVER Client generates an authenticator for the TGS: AuthC,TGS = Encrypt((C, IPC, Timestamp), KC, TGS) Client contacts TGS and requests a ticket for Server, using the ticket from the AS and the authenticator: C => TGS:(S, TicketAS, AuthC,TGS) If ticket and authenticator are both valid, TGS generates random session key for Client and Server and embeds in a ticket issued to the client: TicketTGS: Encrypt((C, S, IPC, Time, Lifetime, KC,S),KS, TGS) TGS sends generated ticket and session key to Client, encrypted with key shared by Client and TGS TGS => C:(Encrypt((TicketTGS, KC,S), KC, TGS) KERBEROS – STEP 3: REQUESTING A SERVICE FROM A SERVER Client generates an authenticator for the server: AuthC,S = Encrypt((C, IPC, Timestamp), KC, S) Client contacts Server and requests a service using the ticket from the TGS and the authenticator it generated: C => S:(Request, TicketTGS, AuthC,S) Server decrypts the Ticket to learn the session key (KC,S), then uses the session key to decrypt the authenticator If the Client has requested that the Server authenticates itself to the Client, the Server returns to the Client the Timestamp+1, encrypted with the session key: S => C:(Encrypt((Timestamp+1),KC,S)) KERBEROS – OVERVIEW OF MESSAGES Step 1: a. Request for TGS ticket b. Ticket for TGS Step 2: c. Request for Server Ticket d. Ticket for Server Step 3: e. Request for service f. Server authentication (optional) TGS AS c b a d e Client Server f KERBEROS – SECURITY AND LIMITATIONS Adding Kerberos typically significantly strengthens security authenticates all parties involved uses cryptographic protocols no information transmitted that could be used maliciously Limitations: Scalability TGS could be a bottleneck Cross-realm authentication needed for large networks Single point of failure brings down system AS and TGS Prone to password-guessing attacks at initial authentication SESAME Used in Europe, whereas Kerberos more used in US Very similar to Kerberos TGS is PAS (Privilege Attribute Server) Tickets are Authentication Certificate (AC) or Privilege Attribute Certificate (PAC) AS PAS Server Client CORBA OVERVIEW Developed by the Object Management Group (OMG) Standard that allows distributed applications, running in heterogeneous distributed environments, to interoperate Objects are entities that provide services to requestors through well-defined encapsulating interfaces Hides “low-level” details from the objects Object Request Broker (ORB) mediates the requests between objects FUNCTIONS OF THE ORB Deliver A’s request to B and B’s reply to A Hide “low-level” details from calling objects: Location (local or remote) Implementation details (language and platform) Uses a universal Interface Definition Language (IDL) to communicate with the ORB Communication mechanisms (TCP/IP, shared memory, local method invocation) CORBA The Common Object Request Broker Architecture (CORBA) standard: Defined by OMG Allows different ORBs to interoperate The CORBA Security specification: Optional If implemented, the ORB provides basic security functionality to all objects: Authentication Communications security Access control Auditing Also used for secure interoperability between ORBS INTERACTION BETWEEN TWO SECURE ORBS ACCESS CONTROL FOR NETWORKS Problems: Enforce an access control policy Protect local internet from outsiders attempting to: Obtain information, modify information, disrupt communications Solution: firewall Allow trust relationships among machines Forms a barrier that protects one network from dangers of another A firewall can: Partition machines into those inside the organization and those outside the organization Enforce an access control policy about what types of traffic are allowed in and out IMPLEMENTING A FIREWALL WITH A SCREENING ROUTER Screening routers perform packet filtering: Examine some fields in the packet header: Source and destination IP address Protocol Source and destination port numbers Allow a packet to pass if it meets the screening criteria Filtering rules are stateless to increase speed Doesn’t take into account what happened just before or is happening right after E.g. C => S (Nonce) for authentication S => C (Nonce) - same one! can get C to do authentication for S FILTERING RULES Administrator can specify rules regarding which packets should not pass through the firewall Can block: Outgoing packets to certain addresses - restrict which outside sites local users can access Incoming packets from certain addresses – restrict access to specific external sites Incoming and outgoing requests to specific services Etc. SAMPLE FILTERING RULES Row 1: Block incoming packets from any source to any destination for the finger service (TCP port 79) Row 2: Block incoming packets bound for the TFTP service (UDP port 69) Row 3: Block outgoing packets bound for any machine on network 128.112 Incoming/ Source IP Destination Protocol Source Outgoing Address Address Port Destination Port Incoming * * TCP * 79 Incoming * * UDP * 69 Outgoing * 128.112.*.* * * * SCREENING ROUTERS Advantages: Relatively cheap Help improve security by blocking packets from/to dangerous sites and services Disadvantages: Still vulnerable to attacks on enabled services Potential services are large (and growing) requiring frequent maintenance Decisions must be made statelessly PROXY GATEWAY A Proxy gateway is more powerful than a screening router and can do more/better checking: Examine data (not just header) portion of packets Remember the past behavior of a connection Consider context – is this a response from the outside to a request that originated on the inside? Etc. Uses two barriers: Outer barrier: blocks all incoming/outgoing traffic not to/from the proxy gateway Inner barrier: blocks all incoming/outgoing traffic not from/to the proxy gateway PROXY GATEWAYS (CONT) Global Internet Bastion Host Organization’s Internet Each barrier is implemented by a screening router: Screening routers block all traffic not going to/from the proxy gateway on the Bastion Host Global Internet Screening Router Organization’s Internet Bastion Host Screening Router PROXY GATEWAYS (CONT) The bastion host runs a set of application gateway programs Act as middlemen between hosts inside and outside the firewall Internal hosts communicate with the application gateway program running on the proxy gateway Application gateway program relays request to the external host The external host’s reply is sent to the application gateway program Application gateway program performs some checking and then passes the reply on to the internal host PROXY GATEWAY - EXAMPLE An FTP server behind a proxy gateway firewall An external client issues commands to establish a connection and transfer files Proxy gateway acts as a middleman between the client and server The proxy can check incoming commands: Pass only valid FTP commands on to the server Protects the server from malformed or dangerous input If the external client attempts to upload a file to the server: The proxy may pass the file through virus-scanning software PROXY GATEWAYS – ADVANTAGES AND DISADVANTAGES Advantages: Provides better protection than a screening router Disadvantages: Additional cost Proxy gateway could be a: Bottleneck Single point of failure Tempting target for attackers But, also generally secure DYNAMIC FIREWALL TECHNIQUES Screening routers and proxy gateways enforce static security policies Dynamic filters allow administrators to set up triggers: Provides additional flexibility: Temporarily add, delete, or modify certain rules in response to particular events Permit or deny traffic in special circumstances Provides additional security: More stringent rules triggered when suspicious traffic is observed NETWORK ACCESS CONTROL - SUMMARY Access Control – need to protect local machines/networks from outsiders attempting to: Obtain information Modify information Disrupt communications Solution: firewalls (screening routers, proxy gateways, etc.) Form a barrier that protects one network from dangers on another Next… Chapter 10 NETWORK SECURITY THREATS - OVERVIEW Network communications exposes one to many different types of risks: Sniffers used to intercept and store network traffic for later analysis, or alter packets privacy, integrity, and authentication issues Traffic analysis - study communications patterns in order to guess the likely contents of the messages Who is communicating with whom How much How often Exploitation of the TCP/IP suite of network protocols Not originally designed with security in mind OVERVIEW OF THE INTERNET PROTOCOL (IP) The Internet Protocol (IP) provides an unreliable packet delivery service IP packets, called datagrams, contain a header and data portion: OVERVIEW OF THE INTERNET PROTOCOL (CONT) Important header fields: VERS (4 bits): version HLEN (4 bits): length of header in 32-bit words TOTAL LENGTH (16 bits): the length of the entire datagram (header and data) in 8-bit octets Max possible length of version 4 IP datagram is 65,536 bytes IDENTIFICATION, FLAGS, and FRAGMENT OFFSET: used to control datagram fragmentation A datagram may be too large to travel whole over a network IP specifies a way to divide a datagram into smaller pieces At the final destination, fragments are reassembled into the original datagram SOURCE and DESTINATION IP ADDRESSES (32 bits) ATTACKS ON THE INTERNET PROTOCOL TEARDROP The Teardrop tool enabled attackers to crash vulnerable remote systems by sending a certain type of fragmented IP datagram Normal datagram fragments do not overlap Teardrop created fragments that did overlap Some implementations of the TCP/IP IP fragmentation reassembly code do not properly handle overlapping IP fragments Windows and some Linux kernels Caused system crash Later fixed by software patches ATTACKS ON THE INTERNET PROTOCOL – IP SPOOFING DESTINATION ADDRESS field is used to route a datagram to its final destination SOURCE ADDRESS field identifies the sender so that the receiver knows where to send a reply IP spoofing – sender of a datagram inserts the address of another machine (or a nonexistent machine) in the source address field Prevent the receiver from determining the host from which an attack datagram originated Reply sent to a another (victim) host OVERVIEW OF THE INTERNET CONTROL MESSAGE PROTOCOL (ICMP) A sub protocol (part of IP) used to transmit error messages and report other unusual situations Different formats depending on type of error transmission Composed of a header and optional data portion and are encapsulated in the data portion of an IP datagram: OVERVIEW OF THE ICMP (CONT) Fields: TYPE (8 bits): identifies the type of the message e.g. 0 = echo reply e.g. 8 = echo request CODE (8 bits): identifies the subtype of the message e.g. 0 = echo reply/request CHECKSUM (16 bits): integrity check on header and data portion of ICMP message IDENTIFIER and SEQUENCE NUMBER: enable the sender to match each reply to the proper request DATA: any data included in an echo request is copied into the data portion of the reply message ATTACKS ON ICMP - PING OF DEATH Attacker constructs an ICMP echo request message containing 65,510 data octets and sends it to a victim host The total size of the resulting datagram (65,538 octets) is larger than the 65,536 limit specified by IP Several systems did not handle this oversized IP datagram properly hang the system crash the system Fixed by software patches ATTACKS ON ICMP - SMURF Attacker sends ICMP echo request messages to a broadcast address at an intermediate site Broadcast address: a copy of the datagram is delivered to every host connected to a specified network For some broadcast address, a single request could generate replies from dozens or hundreds of hosts The source address in each request packet is spoofed so that replies are sent to a victim machine Result: the victim’s machine/network is flooded by ICMP echo replies Solution: Many sites have reconfigured their machines so that their machines do not respond to ICMP echo requests sent to a broadcast address OVERVIEW OF THE USER DATAGRAM PROTOCOL (UDP) IP delivers data from one machine to another UDP runs on top of IP and delivers data from one application to another A port (represented by a positive integer) is a unique destination on a single machine Standard services run on reserved ports: ECHO (port 7) DISCARD (port 9) TIME (port 37) TFTP (port 69) NTP (port 123) Etc. Programs can request an unused (dynamic) port and receive messages that arrive on that port OVERVIEW OF UDP (CONT) The basic unit of communication in UDP is the user datagram: UDP header and UDP data Entire datagram is transported in the data portion of IP datagrams Header = 8 octets Maximum length of data portion = 65,536-8 = 65,528 octets ATTACKS ON UDP - FRAGGLE Similar to Smurf attack except uses UDP instead of ICMP UDP port seven is an echo service Attacker sends user datagrams to port seven of a broadcast address at an intermediate site Spoofed source addresses pointing to victim Random source ports (or port 7 for more effective attack) Each request generates replies from many machines Result: flood victim’s machine/network with UDP replies Solution: filtering out UDP echo requests (or anything else that might generate a response) sent to a broadcast addresses ATTACKS ON UDP - TRINOO Trinoo is a distributed denial of service attack tool that enables an attacker to inundate a victim with UDP traffic from many different hosts simultaneously Daemon program Setup: Search for machines and attempt to break into them using a number of different exploits Install the Trinoo daemon and root kit on as many of these hosts as possible, add to list of “owned” hosts Attack: When given a victim by a master server, sends a large number of UDP packets to random ports on the victim ATTACKS ON UDP – TRINOO (CONT) Master servers Each master server controls many daemons on different hosts An attacker normally controls a number of master servers (on different hosts) Commands (password protected): Start/stop it running Test that it is alive/listening Ask for a list of all the daemons that it controls Instruct it to order its daemons to attack a given victim Attacks: In August 1999 trinoo daemons from over 200 different machines flooded a Univ of Minnesota host for several days In February 2000 trinoo used to attack several major e-commerce sites on the Web OVERVIEW OF THE TRANSMISSION CONTROL PROTOCOL (TCP) TCP runs on top of IP and provides reliable delivery of a stream of data between two applications Like UDP, TCP messages are sent inside IP datagrams TCP: Divides a stream of data into chunks that will fit inside IP datagrams Insures that each datagram arrives at its destination Uses an acknowledgement and retransmission scheme as necessary Reassembles the stream at the destination OVERVIEW OF TCP (CONT) TCP messages that carry data and acknowledgements are called segments OVERVIEW OF TCP (CONT) Important fields: SOURCE and DESTINATION PORT (16 bits) = port identifiers SEQUENCE NUMBER (32 bits) = identifies the position of the data in the segment in the data stream ACKNOWLEDGEMENT (32 bits) = acknowledge the receipt of all data up to given point CODE BITS (6 bits) = URG, ACK, PSH, RST, SYN, and FIN OVERVIEW OF TCP (CONT) Establishing a TCP connection using the three-way handshake: Two parties exchange messages to ensure each is ready to communicate and to agree on initial sequence numbers for the conversation Message 1 (SYN + SEQ) Host A Message 2 (SYN + SEQ + ACK) Message 3 (ACK) Host B OVERVIEW OF TCP (CONT) Closing a TCP connection (one-way): Connection is closed from A to B B may continue sending data to A before fully closing the connection When B has sent all remaining data, then B performs the same closing protocol to close the connection from B to A Message 1 (FIN + SEQ) Host A Message 2 (ACK) Host B ATTACKS ON TCP – SYN FLOOD Recall the three-way handshake to establish a TCP connection After the second message has been sent but before the third message has been received the connection is half opened Most hosts store these half-opened connections in a fixedsize table while they await the third message Half-opened connections are timed out after after half a minute or so Message 1 (SYN + SEQ) Host A Message 2 (SYN + SEQ + ACK) Message 3 (ACK) Host B ATTACKS ON TCP – SYN FLOOD (CONT) Attacker attempts to fill up the half-opened connection table Attacker sends the victim machine a large number of SYN segments with spoofed source addresses Produces a large number of half-opened connections at the victim’s machine that will never become fully open The half-opened connection table fills and no new connections can be accepted until space is available Attacker attempts to keep it full Continue sending SYN segments to replace half-open connections as they time out Result: the victim host cannot accept any other, legitimate attempts to open a connection ATTACKS ON TCP - LAND Attack tool exploits a vulnerability in certain TCP implementations Attacker creates an invalid TCP SYN segment: Spoofed source address is identical to the destination address Source port is identical to the destination port Causes some TCP implementations to freeze or crash Fixed with software patches ATTACKS ON TCP – TRIBE FLOOD NETWORK Tribe Flood Network (TFN) is a distributed denial of service attack tool Used in February, 2000 to attack several major ecommerce sites on the Web Similar to trinoo: Daemon programs: listen for and execute commands from a master Master programs Control a number of daemons Communicate with an attacker and pass his/her commands on to daemons ATTACKS ON TCP – TFN “Improvements” over trinoo: Random protocol (TCP, UDP, or ICMP) for communication between master and daemons Can send out “decoy” packets to random IP addresses to obscure the true target of the attack Daemons spoof the source IP address in the attack packets they send Daemons can attack multiple targets Wider variety of attacks: UDP flood (like with trinoo) TCP SYN flood ICMP ping flood ICMP directed broadcast flood (smurf) All of the above SCANS AND PROBES Attackers typically engage in a variety of reconnaissance activities before attacking: To identify important/interesting hosts To identify potential vulnerabilities that could be exploited A port scanner is a program that tries to determine which ports have programs listening on them Example: Attempts to open a TCP connection to each port in order If a connection is made then immediately close it and record the fact that the port opened If the connection fails then the port is closed PORT SCANNING (CONT) Using fully-open connections to scan is likely to draw a lot of attention to the scan Most hosts log: Each attempt to connect to a closed port Each time a newly-opened connection is closed with little or no data having been sent Clandestine scanning methods: SYN scan: A SYN segment is sent to each port, and any port that responds with a SYN+ACK segment is opened Instead of completing the handshake, a RST (reset) segment is sent to close the connection before it fully opens Some hosts do not log half-opened connections PORT SCANNING (CONT) Clandestine scanning methods (cont): FIN scanning: A FIN segment is sent to each port opened ports will ignore (since no connection has been established) Closed ports are required to respond to a FIN with a RST segment so ports that do not answer are opened Again, many hosts do not log responses to FINs, so detection is less likely TRACEROUTE FOR NETWORK SCANNING The traceroute program discovers the path that an IP datagram follows to reach a target host Start by sending a probe message with a TTL value of 1 bound for the target host If the target host cannot be reached in one hop then: The datagram is dropped Machine that drops it returns an ICMP TTL-exceeded message Traceroute records the name and address of the machine and the round trip time The TTL value is incremented by 1, probe is sent again This process continues until the target is reached, and traceroute generates a report of its findings Can be used to gain info about the topology of a network REMOTE OPERATING SYSTEM FINGERPRINTING Certain attacks only work on certain operating systems (and certain versions of those operating systems) Techniques enable attackers to try to determine what operating system is running on a host Typically, specially crafted (and usually invalid) IP, ICMP, UDP, or TCP packets are sent to a host Different operating systems (and sometimes different versions of the same operating system) are known to respond to these packets in certain ways Examples: FIN segments for closed connections TCP options field SECURITY ASSESSMENT TOOLS Tools that allow system administrators to scrutinize their sites for vulnerabilities Examples: SAINT (http://www.wwdsi.com/saint) SARA (http://www-arc.com/sara) SATAN (http://www.fish.com/satan) Many others Some automate the fixing of vulnerabilities that are identified NETWORK SECURITY THREATS - SUMMARY Network communications exposes one to many different types of risks: Attacks on the privacy, integrity, or authenticity of messages Traffic analysis Exploitation of the TCP/IP suite of network protocols Attacks on IP (Teardrop, IP Spoofing) Attacks on ICMP (Ping of Death, Smurf) Attacks on UDP (Fraggle, Trinoo) Attacks on TCP (SYN Flood, Land, TFN) Probes and scans NEXT… 5 minute break, then Lab