DataStage DB2 Parallel Configuration
... 1) Perform the following on ALL members of the cluster BEFORE installing DataStage on the ETL server: a. Create the primary group to which the DataStage users will belong (in this document, this group is the recommended default dstage) and ensure that this group has the same UNIX group id (like 127) ...
... 1) Perform the following on ALL members of the cluster BEFORE installing DataStage on the ETL server: a. Create the primary group to which the DataStage users will belong (in this document, this group is the recommended default dstage) and ensure that this group has the same UNIX group id (like 127) ...
Installation and Setup Guide
... This Installation and Setup Guide will help you install and test GFI LanGuard 2011 and is structured as follows: ...
... This Installation and Setup Guide will help you install and test GFI LanGuard 2011 and is structured as follows: ...
SQL Server Transaction Log Management
... model according to the business requirements for the database, and then establish maintenance procedures appropriate to that mode. We cover this in Chapter 3, Transaction Logs, Backup and Recovery. • Perform transaction log backup and restore – Unless working in SIMPLE model, it is vital that the D ...
... model according to the business requirements for the database, and then establish maintenance procedures appropriate to that mode. We cover this in Chapter 3, Transaction Logs, Backup and Recovery. • Perform transaction log backup and restore – Unless working in SIMPLE model, it is vital that the D ...
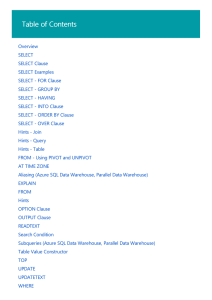
Transact-SQL
... The order of the clauses in the SELECT statement is significant. Any one of the optional clauses can be omitted, but when the optional clauses are used, they must appear in the appropriate order. SELECT statements are permitted in user-defined functions only if the select lists of these statements c ...
... The order of the clauses in the SELECT statement is significant. Any one of the optional clauses can be omitted, but when the optional clauses are used, they must appear in the appropriate order. SELECT statements are permitted in user-defined functions only if the select lists of these statements c ...
Install SQL Server on Linux
... Resolution: Change the name in /etc/hostname to something 15 characters long or less. Do not run the command ALTER SERVICE MASTER KEY REGENERATE . There is a known bug that will cause SQL Server to become unstable. If you need to regenerate the Service Master Key, you should back up your database fi ...
... Resolution: Change the name in /etc/hostname to something 15 characters long or less. Do not run the command ALTER SERVICE MASTER KEY REGENERATE . There is a known bug that will cause SQL Server to become unstable. If you need to regenerate the Service Master Key, you should back up your database fi ...
Oracle Data Warehousing Guide
... The Programs are not intended for use in any nuclear, aviation, mass transit, medical, or other inherently dangerous applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Pro ...
... The Programs are not intended for use in any nuclear, aviation, mass transit, medical, or other inherently dangerous applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Pro ...
Using Explicit Cursors
... last_name columns for those employees working in the department with a department_id of 30. The dept_cursor cursor is declared to retrieve all the details for the department with the location_id 1700. Note that a variable is used while declaring the cursor. These variables are considered bind variab ...
... last_name columns for those employees working in the department with a department_id of 30. The dept_cursor cursor is declared to retrieve all the details for the department with the location_id 1700. Note that a variable is used while declaring the cursor. These variables are considered bind variab ...
Hyperion Workspace User`s Guide
... applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Programs are used for such purposes, and we disclaim liability for any damages caused by such use of the Programs. Oracl ...
... applications. It shall be the licensee's responsibility to take all appropriate fail-safe, backup, redundancy and other measures to ensure the safe use of such applications if the Programs are used for such purposes, and we disclaim liability for any damages caused by such use of the Programs. Oracl ...
Database Compatibility for Oracle® Developer`s Guide
... Sample Database ....................................................................................................................30 2.1.1.1 Sample Database Installation ............................................................................................30 2.1.1.2 Sample Database Descripti ...
... Sample Database ....................................................................................................................30 2.1.1.1 Sample Database Installation ............................................................................................30 2.1.1.2 Sample Database Descripti ...
Active Record
... of the full power of your database engine from within your Ruby programs and Rails applications. Active Record is the object relational mapping library used for database access from the popular Ruby on Rails framework. We show you how to get Active Record, install it, work with legacy schema, and us ...
... of the full power of your database engine from within your Ruby programs and Rails applications. Active Record is the object relational mapping library used for database access from the popular Ruby on Rails framework. We show you how to get Active Record, install it, work with legacy schema, and us ...
IBM Informix Developer’s Handbook Front cover
... Note: Before using this information and the product it supports, read the information in “Notices” on page ix. ...
... Note: Before using this information and the product it supports, read the information in “Notices” on page ix. ...
Oracle Data Warehousing Guide
... license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without ...
... license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without ...
Web 2.0 samples for accessing DB2 on February 2009
... System administrators who read this document are familiar with, how to set up YUM to include the Red Hat Enterprise Linux 5.2 DVD image and the related supplementary ISO image as software repositories. Also, the latest available security updates must have been applied to the system. As required by a ...
... System administrators who read this document are familiar with, how to set up YUM to include the Red Hat Enterprise Linux 5.2 DVD image and the related supplementary ISO image as software repositories. Also, the latest available security updates must have been applied to the system. As required by a ...
Web 2.0 samples for accessing DB2 on February 2009
... The number of programming languages that are used for Web 2.0 applications is challenging system administrators to select the right programming language, which offers support for all requirements. Since Web 2.0 applications make use of databases that serve the user supplied information, connecting t ...
... The number of programming languages that are used for Web 2.0 applications is challenging system administrators to select the right programming language, which offers support for all requirements. Since Web 2.0 applications make use of databases that serve the user supplied information, connecting t ...
iSQL*Plus User`s Guide and Reference Release 9.0.1
... The Programs (which include both the software and documentation) contain proprietary information of Oracle Corporation; they are provided under a license agreement containing restrictions on use and disclosure and are also protected by copyright, patent, and other intellectual and industrial propert ...
... The Programs (which include both the software and documentation) contain proprietary information of Oracle Corporation; they are provided under a license agreement containing restrictions on use and disclosure and are also protected by copyright, patent, and other intellectual and industrial propert ...