EXTENSII ALE BAZELOR DE DATE DISTRIBUITE / SYSTEMS
... systems and considering them as a guaranteed solution, even if some cases prove this is not the most efficient approach. We will try to fight against to this preconceived idea trough reveal of some technologies as federated database systems, which are applicable in some categories of circumstances. ...
... systems and considering them as a guaranteed solution, even if some cases prove this is not the most efficient approach. We will try to fight against to this preconceived idea trough reveal of some technologies as federated database systems, which are applicable in some categories of circumstances. ...
MCA 304 DATABASE MANAGEMENT SYSTEMS
... Decomposition, Normal Forms: First Normal Form, Second Normal Form, Third Normal Form, Boyce Codd Normal Form, Fourth Normal Form,Fifth Normal Form MODULE V Transaction Management, Concurrency Control, Distributed System and Database Administration The ACID Properties,Transactions and Schedules, Con ...
... Decomposition, Normal Forms: First Normal Form, Second Normal Form, Third Normal Form, Boyce Codd Normal Form, Fourth Normal Form,Fifth Normal Form MODULE V Transaction Management, Concurrency Control, Distributed System and Database Administration The ACID Properties,Transactions and Schedules, Con ...
Distributed DBMS Security
... How to guarantee database consistency ? A database is said to be consistent if it satisfies the set of integrity constraints. Concurrency control techniques ...
... How to guarantee database consistency ? A database is said to be consistent if it satisfies the set of integrity constraints. Concurrency control techniques ...
slides01
... – E-commerce companies, banks, airlines, transportation companies, corporate databases, government agencies, … – Anyone you can think of! ...
... – E-commerce companies, banks, airlines, transportation companies, corporate databases, government agencies, … – Anyone you can think of! ...
Object Composition and Reuse in a Distributed Multimedia
... implementation of our system. The database supports an easy to reuse mechanism. Objects in the two layered database hierarchy can be grouped and declared as a class, which serve as a reusable multimedia presentation subject. In the hierarchy, we use four type of links to group presentation windows a ...
... implementation of our system. The database supports an easy to reuse mechanism. Objects in the two layered database hierarchy can be grouped and declared as a class, which serve as a reusable multimedia presentation subject. In the hierarchy, we use four type of links to group presentation windows a ...
CSC 3110 Database Management Systems II
... are to be extensively addressed. Internal operations of database management systems like indexing, query processing and transactions are to be covered. These are to create a strong basis for future advanced studies/research. (b) Aims The aim of the course is to equip students with fundamental knowle ...
... are to be extensively addressed. Internal operations of database management systems like indexing, query processing and transactions are to be covered. These are to create a strong basis for future advanced studies/research. (b) Aims The aim of the course is to equip students with fundamental knowle ...
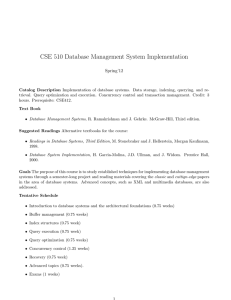
CSE 510 Database Management System Implementation
... in the area of database systems. Advanced concepts, such as XML and multimedia databases, are also addressed. Tentative Schedule • Introduction to database systems and the architectural foundations (0.75 weeks) • Buffer management (0.75 weeks) • Index structures (0.75 week) • Query execution (0.75 w ...
... in the area of database systems. Advanced concepts, such as XML and multimedia databases, are also addressed. Tentative Schedule • Introduction to database systems and the architectural foundations (0.75 weeks) • Buffer management (0.75 weeks) • Index structures (0.75 week) • Query execution (0.75 w ...
Database Management issues from Hoffer - Moodle
... simultaneous access to data can result in interference and data loss (lost update problem) Solution–Concurrency Control The process of managing simultaneous operations against a database so that data integrity is maintained and the operations do not interfere with each other in a multi-user enviro ...
... simultaneous access to data can result in interference and data loss (lost update problem) Solution–Concurrency Control The process of managing simultaneous operations against a database so that data integrity is maintained and the operations do not interfere with each other in a multi-user enviro ...
DBMS Functions Data, Storage, Retrieval, and Update
... • Provides users with the ability to store, retrieve, and update the data that are in the database. ...
... • Provides users with the ability to store, retrieve, and update the data that are in the database. ...
MTH101: Calculus I
... Information Systems Engineering (Bilişim Sistemleri Mühendisliği) Program Course Information Document ...
... Information Systems Engineering (Bilişim Sistemleri Mühendisliği) Program Course Information Document ...
Download
... Recovery and atomicity – failures classification and types – Transaction model and Log based recovery, schedules – serial and non-serial types – Serialization of schedules and views – testing for seriability – lock based protocols – time based protocols – validation techniques – multiple Granularity ...
... Recovery and atomicity – failures classification and types – Transaction model and Log based recovery, schedules – serial and non-serial types – Serialization of schedules and views – testing for seriability – lock based protocols – time based protocols – validation techniques – multiple Granularity ...
presentation source
... Finishing the Transaction • If the transaction goes successfully then the COMMIT command will commit the changes to the database. • However, if an error occurs the ROLLBACK command can be used to restore the database to its state prior to the transaction. ...
... Finishing the Transaction • If the transaction goes successfully then the COMMIT command will commit the changes to the database. • However, if an error occurs the ROLLBACK command can be used to restore the database to its state prior to the transaction. ...
Sylabus-CEng553-2010-2.prog
... Database Management Systems, Raghu Ramakrishnan, Johannes Gehrke, McGraw Hill, Third Edition , 2003. Fundamentals of Database Systems by R. Elmasri and S.B. Navathe, Addison-Wesley, Fourth Edition, 2003. Database System and Concepts, A.Silberschatz, H.F. Korth, S.Sudarshan, McGraw Hill, Fourth ...
... Database Management Systems, Raghu Ramakrishnan, Johannes Gehrke, McGraw Hill, Third Edition , 2003. Fundamentals of Database Systems by R. Elmasri and S.B. Navathe, Addison-Wesley, Fourth Edition, 2003. Database System and Concepts, A.Silberschatz, H.F. Korth, S.Sudarshan, McGraw Hill, Fourth ...
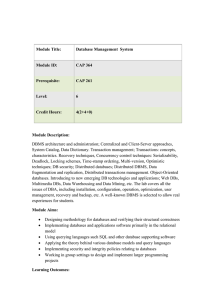
Database Management System Module Title: CAP 364 Module ID
... characteristics. Recovery techniques, Concurrency control techniques: Serializability, Deadlock, Locking schemes, Time-stamp ordering, Multi-version, Optimistic techniques; DB security; Distributed databases; Distributed DBMS, Data fragmentation and replication, Distributed transactions management. ...
... characteristics. Recovery techniques, Concurrency control techniques: Serializability, Deadlock, Locking schemes, Time-stamp ordering, Multi-version, Optimistic techniques; DB security; Distributed databases; Distributed DBMS, Data fragmentation and replication, Distributed transactions management. ...
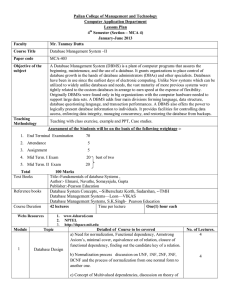
Database System Concepts, --Silberschatz Korth, Sudarshan, -
... have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to widely unlike databases and needs, the vast maturity of more previous systems were tightly related to the custom databases in arrange to earn speed at the expense of flexibility. Originally ...
... have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to widely unlike databases and needs, the vast maturity of more previous systems were tightly related to the custom databases in arrange to earn speed at the expense of flexibility. Originally ...
Slides 01 - University of California, Irvine
... – Shadowing, logging, multilevel recovery, ARIES, Checkpointing ...
... – Shadowing, logging, multilevel recovery, ARIES, Checkpointing ...
Concurrency Control - High Point University
... The movement of transaction data from private workspace to stored database 1. First Phase – try writing private workspace to a secure storage (not the stored DB). If OK then go to 2nd phase, otherwise lose changes but no harm done to DB. 2. Second Phase – data is moved from private workspace to stor ...
... The movement of transaction data from private workspace to stored database 1. First Phase – try writing private workspace to a secure storage (not the stored DB). If OK then go to 2nd phase, otherwise lose changes but no harm done to DB. 2. Second Phase – data is moved from private workspace to stor ...
CMP 206: Principles of Database Management System
... UNIT4: Transaction processing concepts: Transaction processing system, schedule and recoverability, Testing of serializability, Serializability of schedules, conflict & view serializable schedule ,Transaction processing in distributed database fragmentation, locking, Protocols for distributed databa ...
... UNIT4: Transaction processing concepts: Transaction processing system, schedule and recoverability, Testing of serializability, Serializability of schedules, conflict & view serializable schedule ,Transaction processing in distributed database fragmentation, locking, Protocols for distributed databa ...
Diapositive 1
... management; Transactions: concepts, characteristics. Recovery techniques, Concurrency control techniques: Serializability, Deadlock, Locking schemes, Time-stamp ordering, Multi-version, Optimistic techniques; DB security; Distributed databases; Distributed DBMS, Data fragmentation and replication, D ...
... management; Transactions: concepts, characteristics. Recovery techniques, Concurrency control techniques: Serializability, Deadlock, Locking schemes, Time-stamp ordering, Multi-version, Optimistic techniques; DB security; Distributed databases; Distributed DBMS, Data fragmentation and replication, D ...