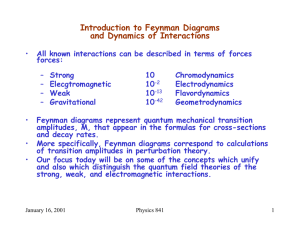
Introduction to Feynman Diagrams and Dynamics of Interactions
... perturbation theory in nonrelativistic quantum mechanics, we have second order perturbation theory in quantum field theories. ...
... perturbation theory in nonrelativistic quantum mechanics, we have second order perturbation theory in quantum field theories. ...
Open Quantum Physics and Environmental Heat Conversion into Usable Energy Brochure
... A Quantum system can be viewed as a larger closed system comprising of two components: an open quantum system and its surrounding environment. These two components interact with each other, and in the realm of theoretical physics, this interaction cannot be neglected. This eBook explains mathematica ...
... A Quantum system can be viewed as a larger closed system comprising of two components: an open quantum system and its surrounding environment. These two components interact with each other, and in the realm of theoretical physics, this interaction cannot be neglected. This eBook explains mathematica ...
Electrons in Atoms - Effingham County Schools
... Electrons, like light waves, can be bent, or diffracted ...
... Electrons, like light waves, can be bent, or diffracted ...
Quantum computing with nanoscale infrastructure
... of atomic magnetic needles connected by springs, sitting like pearls on a string. The qubit needle can point up (0) or down (1), but also in any direction in between. A bit represented by a flip-flop circuit in a classical computer can only be in either of the states |0> or |1>. However, the quantum ...
... of atomic magnetic needles connected by springs, sitting like pearls on a string. The qubit needle can point up (0) or down (1), but also in any direction in between. A bit represented by a flip-flop circuit in a classical computer can only be in either of the states |0> or |1>. However, the quantum ...
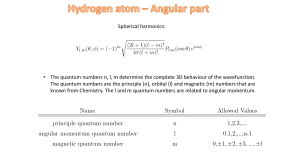
Spherical harmonics: • The quantum numbers n, l, m determine the
... • The quantum numbers n, l, m determine the complete 3D behaviour of the wavefunction. The quantum numbers are the principle (n), orbital (l) and magnetic (m) numbers that are known from Chemistry. The l and m quantum numbers are related to angular momentum. ...
... • The quantum numbers n, l, m determine the complete 3D behaviour of the wavefunction. The quantum numbers are the principle (n), orbital (l) and magnetic (m) numbers that are known from Chemistry. The l and m quantum numbers are related to angular momentum. ...
c - Greer Middle College
... The energy of a photon is proportional to its frequency. E: energy (J, joules) h: Planck’s constant (6.6262 10-34 J·s) ...
... The energy of a photon is proportional to its frequency. E: energy (J, joules) h: Planck’s constant (6.6262 10-34 J·s) ...
Quantum Lecture _08
... the nucleus of an atom exhibited wave behavior, acting at certain frequencies around the nucleus Further experiments proved more wavelike behavior such as a stream of electrons can be bent (diffracted), or that two electron beams can interfere with each other, just like water waves. ...
... the nucleus of an atom exhibited wave behavior, acting at certain frequencies around the nucleus Further experiments proved more wavelike behavior such as a stream of electrons can be bent (diffracted), or that two electron beams can interfere with each other, just like water waves. ...
The Computer Science Picture of Reality
... Quantum algorithms and complexity theory explore fundamental questions with profound implications: • Quantum resistant cryptography. • Probabilistic method <--> quantum method Quantum complexity <--> classical complexity • quantum complexity theory <--> condensed matter physics • Verifying quantum c ...
... Quantum algorithms and complexity theory explore fundamental questions with profound implications: • Quantum resistant cryptography. • Probabilistic method <--> quantum method Quantum complexity <--> classical complexity • quantum complexity theory <--> condensed matter physics • Verifying quantum c ...
AOW- Time Travel
... protons. Physicists believe fundamental particles are the smallest parts of matter. Now, they may be made of smaller parts or not, but we can't see that far. Deutsch came up with a theory to send these particles back in time. "It's intriguing that you've got general relativity predicting these parad ...
... protons. Physicists believe fundamental particles are the smallest parts of matter. Now, they may be made of smaller parts or not, but we can't see that far. Deutsch came up with a theory to send these particles back in time. "It's intriguing that you've got general relativity predicting these parad ...
SEPTEMBER 21, 2013 THESKEPTICARENA.COM QUANTUM
... each of them. If one atom were in two different places, the virtual particles would have to be the same. How is that possible at two different locations unless the quantum foam is also in superposition? If they were really one atom, any particle (for example, a neutrino) that interacted with one ato ...
... each of them. If one atom were in two different places, the virtual particles would have to be the same. How is that possible at two different locations unless the quantum foam is also in superposition? If they were really one atom, any particle (for example, a neutrino) that interacted with one ato ...
The Power of Quantum Advice
... The class of p(n)-qubit quantum states is Result of A.’06 on learnability of quantum infinitely large! And even if we discretize it, it’s states (building on Ambainis et al. 1999) still doubly-exponentially large Instead of Boolean functions f:{0,1}n{0,1}, now we have real functions f:{0,1}n[0,1] ...
... The class of p(n)-qubit quantum states is Result of A.’06 on learnability of quantum infinitely large! And even if we discretize it, it’s states (building on Ambainis et al. 1999) still doubly-exponentially large Instead of Boolean functions f:{0,1}n{0,1}, now we have real functions f:{0,1}n[0,1] ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.