`Quantum Cheshire Cat`as Simple Quantum Interference
... where the photon is measured in the left arm of the interferometer (the beam was displaced up by δy ) and, at the same time, there is positive angular momentum on the right arm of the interferometer (the beam was displaced sideways by δx ). However, as pointed out in our calculations, the probabilit ...
... where the photon is measured in the left arm of the interferometer (the beam was displaced up by δy ) and, at the same time, there is positive angular momentum on the right arm of the interferometer (the beam was displaced sideways by δx ). However, as pointed out in our calculations, the probabilit ...
Simulation programs for teaching quantum mechanics
... quantum phenomena students have problems to create any intuitive pictures or to make contact to their knowledge about “classical” systems. To remedy this situation several authors have produced tools to simulate and visualise quantum systems, among them two very comprehensive packages: Physlet Quant ...
... quantum phenomena students have problems to create any intuitive pictures or to make contact to their knowledge about “classical” systems. To remedy this situation several authors have produced tools to simulate and visualise quantum systems, among them two very comprehensive packages: Physlet Quant ...
Entanglement, Distillation and Quantum Repeaters
... have been introduced. They are often connected to an operational task and many are very hard or impossible to evaluate in general. As it turns out, entanglement can be view as a ressource, which can be transfered between systems. ...
... have been introduced. They are often connected to an operational task and many are very hard or impossible to evaluate in general. As it turns out, entanglement can be view as a ressource, which can be transfered between systems. ...
Incompatible results of quantum measurements
... an o p e r a t o r A d e p e n d s only on A and on the state o f the q u a n t u m system being measured (here, the word " s t a t e " includes not only the wave function ~u, but also any h i d d e n variables that theorists m a y invent). In particular, that result does not d e p e n d on the choi ...
... an o p e r a t o r A d e p e n d s only on A and on the state o f the q u a n t u m system being measured (here, the word " s t a t e " includes not only the wave function ~u, but also any h i d d e n variables that theorists m a y invent). In particular, that result does not d e p e n d on the choi ...
New Evidence that Quantum Mechanics is Hard to Simulate on
... Our Result: Take a system of n identical photons, with m=O(n2) modes (basis states) each. Put each photon in a known mode, then apply a random mm scattering matrix U: ...
... Our Result: Take a system of n identical photons, with m=O(n2) modes (basis states) each. Put each photon in a known mode, then apply a random mm scattering matrix U: ...
The Relativistic Quantum World
... they live a factor 5 longer • As seen from the muon particle the distance is a factor 5 shorter ...
... they live a factor 5 longer • As seen from the muon particle the distance is a factor 5 shorter ...
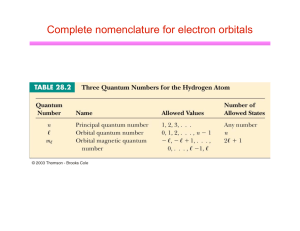
Complete nomenclature for electron orbitals
... little too classical, though l It pictures the electrons as orbiting the nucleus in circular (or elliptical orbitals) l But in fact the only reality is |y|2, the square of the wavefunction, which gives the probability of the electron to be in a given place at a given time l Electron is not confined ...
... little too classical, though l It pictures the electrons as orbiting the nucleus in circular (or elliptical orbitals) l But in fact the only reality is |y|2, the square of the wavefunction, which gives the probability of the electron to be in a given place at a given time l Electron is not confined ...
QUANTUM NUMBERS
... For an electron in an atom with l=0 is said to be in an s state. For an electron in an atom with l=1 is said to be in an p state. For an electron in an atom with l=2 is said to be in an d state. For an electron in an atom with l=3 is said to be in an e state. ...
... For an electron in an atom with l=0 is said to be in an s state. For an electron in an atom with l=1 is said to be in an p state. For an electron in an atom with l=2 is said to be in an d state. For an electron in an atom with l=3 is said to be in an e state. ...
relevance feedback algorithms inspired by quantum detection
... When a probability function is provided, each observable value and then each basis vector corresponds to a probability measure given by the function, thus obtaining a probability distribution. ...
... When a probability function is provided, each observable value and then each basis vector corresponds to a probability measure given by the function, thus obtaining a probability distribution. ...
Strings in the Quantum World. - Queen Mary University of London
... annihilation operators for electrons, positrons and photons. At the same time this new language captures thewave properties of electrons, photons. ...
... annihilation operators for electrons, positrons and photons. At the same time this new language captures thewave properties of electrons, photons. ...
The Quantum Model of the Atom
... Heisenberg Uncertainty Principle: it is impossible to determine simultaneously both the position and velocity of an electron or any other particle ...
... Heisenberg Uncertainty Principle: it is impossible to determine simultaneously both the position and velocity of an electron or any other particle ...
Chapter 4
... e- may have a wave-particle nature Would explain why e- only had certain orbits ...
... e- may have a wave-particle nature Would explain why e- only had certain orbits ...
quantum - Academia Sinica
... 1914, Bohr became famous after the success of his atomic model, and the Royal Danish Academy of Science gave him financial support to set up an Physics Institute. The fund was actually donated by Carlsberg ...
... 1914, Bohr became famous after the success of his atomic model, and the Royal Danish Academy of Science gave him financial support to set up an Physics Institute. The fund was actually donated by Carlsberg ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.