Introduction - Computer Science
... • Separation of user/kernel mode is used for: – Security: The OS calls in kernel mode make sure that the user has enough privileges to run that call. – Robustness: If a process that tries to write to an invalid memory location, the OS will kill the program, but the OS continues to run. A crash in th ...
... • Separation of user/kernel mode is used for: – Security: The OS calls in kernel mode make sure that the user has enough privileges to run that call. – Robustness: If a process that tries to write to an invalid memory location, the OS will kill the program, but the OS continues to run. A crash in th ...
What is an Operating System?
... One or more CPUs, device controllers connect through common bus providing access to shared memory ...
... One or more CPUs, device controllers connect through common bus providing access to shared memory ...
Paging
... Segments are visible to the programmer Usually different segments allocated to program and data There may be a number of program and data segments associated to a single ...
... Segments are visible to the programmer Usually different segments allocated to program and data There may be a number of program and data segments associated to a single ...
2.01
... among processes, users, and computer systems Allow users to send messages to one another’s screens, browse web pages, send electronic-mail messages, log in remotely, transfer files from one machine to another ...
... among processes, users, and computer systems Allow users to send messages to one another’s screens, browse web pages, send electronic-mail messages, log in remotely, transfer files from one machine to another ...
1. Introduction
... Interrupt transfers control to the interrupt service routine generally, through the interrupt vector, which contains the addresses of all the service routines Interrupt architecture must save the address of the interrupted instruction Incoming interrupts are disabled while another interrupt is b ...
... Interrupt transfers control to the interrupt service routine generally, through the interrupt vector, which contains the addresses of all the service routines Interrupt architecture must save the address of the interrupted instruction Incoming interrupts are disabled while another interrupt is b ...
Module 5: Buffer Overflow Attacks
... instructions executed by the computer processor are stored in either the processor’s registers or in memory. • It is the responsibility of the assembly language programmer to ensure that correct interpretation is placed on any saved data value. – Some machine language instructions will treat the byt ...
... instructions executed by the computer processor are stored in either the processor’s registers or in memory. • It is the responsibility of the assembly language programmer to ensure that correct interpretation is placed on any saved data value. – Some machine language instructions will treat the byt ...
TotalView Change Log, 8.0
... Critical performance improvements, and usability enhancements that cancel long running operations when processing delayed symbols and when creating certain types of breakpoints. ...
... Critical performance improvements, and usability enhancements that cancel long running operations when processing delayed symbols and when creating certain types of breakpoints. ...
THE USER VIEW OF OPERATING SYSTEMS
... In Chapter 15, we introduced you to two different views of the role of the operating system as part of the overall computer architecture. Specifically, we looked at the operating system both as a means of delivering services to the user and as a way of controlling and operating the system facilities ...
... In Chapter 15, we introduced you to two different views of the role of the operating system as part of the overall computer architecture. Specifically, we looked at the operating system both as a means of delivering services to the user and as a way of controlling and operating the system facilities ...
TOTALVIEW CHANGE LOG - Rogue Wave Software
... Critical performance improvements, and usability enhancements that cancel long running operations when processing delayed symbols and when creating certain types of breakpoints. ...
... Critical performance improvements, and usability enhancements that cancel long running operations when processing delayed symbols and when creating certain types of breakpoints. ...
BAB 8 SISTEM PENGOPERASIAN
... programs known as memory managers when PC main memories started to be routinely larger than 640 KB in the late 1980s. These move portions of the operating system outside their normal locations in order to increase the amount of conventional or quasi-conventional memory available to other applicati ...
... programs known as memory managers when PC main memories started to be routinely larger than 640 KB in the late 1980s. These move portions of the operating system outside their normal locations in order to increase the amount of conventional or quasi-conventional memory available to other applicati ...
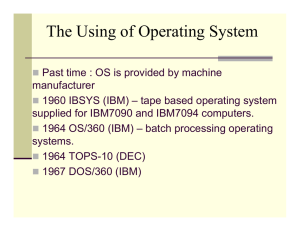
The Operating System
... Batch interface – commands are entered into files, and those files are executed ...
... Batch interface – commands are entered into files, and those files are executed ...
Machine and Operating System Organization
... What are components of traditional OSs? What are design issues that affect structures of OSs? How are components implemented? How are they stitched together? Major software engineering and design problem ...
... What are components of traditional OSs? What are design issues that affect structures of OSs? How are components implemented? How are they stitched together? Major software engineering and design problem ...
- JNTU World
... Computer System and Operating System Overview: Overview of computer operating systems functions , protection and security, distributed systems special purpose systems, operating systems structures-operating system services and systems calls, system programs, operating systems generation. Memory Mana ...
... Computer System and Operating System Overview: Overview of computer operating systems functions , protection and security, distributed systems special purpose systems, operating systems structures-operating system services and systems calls, system programs, operating systems generation. Memory Mana ...
Slide 1
... held in a queue and printed one at a time – the use of a queue also allows priorities to be set. • in a multi-user system, provides a method of keeping print-jobs separate – it means that printouts will not be muddled up. • Lets the processor get on with something else while the jobs are queued ...
... held in a queue and printed one at a time – the use of a queue also allows priorities to be set. • in a multi-user system, provides a method of keeping print-jobs separate – it means that printouts will not be muddled up. • Lets the processor get on with something else while the jobs are queued ...
3. Operating Systems - Informática Ingeniería en Electrónica y
... a virtual or extended machine with a much simpler use. It hides fine working details the user does not need to know (e.g. how to manage the read/write head of a magnetic disc) It provides an extra set of instructions, the System Calls They can be used by other programs or by the programmer working ...
... a virtual or extended machine with a much simpler use. It hides fine working details the user does not need to know (e.g. how to manage the read/write head of a magnetic disc) It provides an extra set of instructions, the System Calls They can be used by other programs or by the programmer working ...
CIS 721 - Lecture 1
... General Features of a Command • A UNIX command consists of a single word generally using alphabetic characters. • Commands are essentially files representing programs – mainly written in C. These files are stored in certain folders known as directories. • For instance, the ls command is also a prog ...
... General Features of a Command • A UNIX command consists of a single word generally using alphabetic characters. • Commands are essentially files representing programs – mainly written in C. These files are stored in certain folders known as directories. • For instance, the ls command is also a prog ...
A User Mode L4 Environment
... piler, and linker are available. For debugging, either kernel internal features such as single stepping or functions to dump the content and mapping of memory pages is available, or applications can be tested with a remote version of GDB. L4 Linux-applications have no different behavior than standar ...
... piler, and linker are available. For debugging, either kernel internal features such as single stepping or functions to dump the content and mapping of memory pages is available, or applications can be tested with a remote version of GDB. L4 Linux-applications have no different behavior than standar ...
1.01 - University of South Florida
... C program invoking printf() library call, which calls write() system call ...
... C program invoking printf() library call, which calls write() system call ...
Chapter 6 Operating Systems
... Users have much more control of their file system and operating system in a command line interface. For example, users can copy a specific file from one location to another with a one-line command. ...
... Users have much more control of their file system and operating system in a command line interface. For example, users can copy a specific file from one location to another with a one-line command. ...
ch02-OS-Structures
... Debugging facilities can greatly enhance the user’s and programmer’s abilities to efficiently use the system ...
... Debugging facilities can greatly enhance the user’s and programmer’s abilities to efficiently use the system ...
CIS 721 - Lecture 1
... the essential commands of UNIX . • UNIX was never designed for the world. There is a method to this madness. • Many Internet applications are powered by UNIX. ...
... the essential commands of UNIX . • UNIX was never designed for the world. There is a method to this madness. • Many Internet applications are powered by UNIX. ...
Appendix A-Linux_cs3
... Linux Environments The windows, menus, and dialog boxes most people think of as part of the operating system are actually separate layers, known as the windowing system and the desktop environment. These layers provide the human-oriented graphical user interface (GUI) that enables users to easily w ...
... Linux Environments The windows, menus, and dialog boxes most people think of as part of the operating system are actually separate layers, known as the windowing system and the desktop environment. These layers provide the human-oriented graphical user interface (GUI) that enables users to easily w ...
Acorn MOS

Acorn's Machine Operating System (MOS) or OS was a computer operating system used in the Acorn BBC computer range. It included support for four-channel sound and graphics, file system abstraction, and digital and analogue I/O including a daisy-chained fast expansion bus. The implementation was single-tasking, monolithic and non-reentrant.Versions 0.10 to 1.20 were used on the BBC Micro, version 1.00 on the Electron, version 2 was used on the B+, and versions 3 to 5 were used in the BBC Master Series range.The final BBC computer, the BBC A3000, was 32-bit and ran RISC OS. Its operating system used portions of the Acorn MOS architecture and shared a number of characteristics (commands, VDU system) with the earlier 8-bit MOS.Versions 0 and 1 of the MOS were 16KiB in size, written in 6502 machine code, and held in ROM on the motherboard. The upper quarter of the 16-bit address space (0xC000 to 0xFFFF) is reserved for its ROM code and I/O space.Versions 2 to 5 were still restricted to a 16KiB address space but managed to hold more code and hence more complex routines, partly because of the alternative 65C102 CPU with its denser instruction set plus the careful use of paging.