Tables
... Structures Dominate that of Real Data Often this information is not “just random pointers” How do we encode a combinatorial object (e.g. a tree) of specialized information … even a static one in a small amount of space & still perform queries in constant time ??? May 09 ...
... Structures Dominate that of Real Data Often this information is not “just random pointers” How do we encode a combinatorial object (e.g. a tree) of specialized information … even a static one in a small amount of space & still perform queries in constant time ??? May 09 ...
word - Courses
... This function will be used to compute the array index into which a pair with key k is to be stored. The header file for this project is identical to that found in lab5, and also to the header file for the Binary Search Tree based Dictionary posted on the website. There is however one ADT operation ...
... This function will be used to compute the array index into which a pair with key k is to be stored. The header file for this project is identical to that found in lab5, and also to the header file for the Binary Search Tree based Dictionary posted on the website. There is however one ADT operation ...
slides
... • Decompose key x into r+1 bytes, so that x = {x0, x1, …, xr} – Only requirement is that max value of byte < m – Let a = {a0, a1, …, ar} denote a sequence of r+1 elements chosen randomly from {0, 1, …, m - 1} – Define corresponding hash function ha G: r ...
... • Decompose key x into r+1 bytes, so that x = {x0, x1, …, xr} – Only requirement is that max value of byte < m – Let a = {a0, a1, …, ar} denote a sequence of r+1 elements chosen randomly from {0, 1, …, m - 1} – Define corresponding hash function ha G: r ...
Hashing
... Chaining • Advantages to linked storage – with a good hash function, the linked lists will be short – clustering is not a problem -- records with different keys are on different chains – The size of the table is of less concern – Deletions are easy and efficient – [The chains could be binary search ...
... Chaining • Advantages to linked storage – with a good hash function, the linked lists will be short – clustering is not a problem -- records with different keys are on different chains – The size of the table is of less concern – Deletions are easy and efficient – [The chains could be binary search ...
SigMatch*Fast and Scalable Multi
... To ascertain whether an element belongs to a set, the same set of k hash functions are applied to the element to obtain k values. ...
... To ascertain whether an element belongs to a set, the same set of k hash functions are applied to the element to obtain k values. ...
Document
... – Compiler: All possible identifiers allowed by the language vs. those used in some file of one program – Database: All possible student names vs. students enrolled – AI: All possible chess-board configurations vs. those considered by the current player Edition 2016 ...
... – Compiler: All possible identifiers allowed by the language vs. those used in some file of one program – Database: All possible student names vs. students enrolled – AI: All possible chess-board configurations vs. those considered by the current player Edition 2016 ...
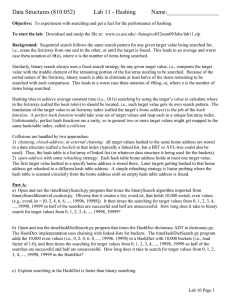
Data Structures (810:052) Lab 11 - Hashing Name:_________________
... Background: Sequential search follows the same search pattern for any given target value being searched for, i.e., scans the list/array from one end to the other, or until the target is found. This leads to an average and worst case theta notation of Θ(n), where n is the number of items being search ...
... Background: Sequential search follows the same search pattern for any given target value being searched for, i.e., scans the list/array from one end to the other, or until the target is found. This leads to an average and worst case theta notation of Θ(n), where n is the number of items being search ...
Cryptography for IoT
... Hardware implementation of PRESENT has much higher throughput and requires a half of gates compared to the implementation of AES with similar key size. ...
... Hardware implementation of PRESENT has much higher throughput and requires a half of gates compared to the implementation of AES with similar key size. ...
Network Applications of Bloom Filters: A Survey
... a Bloom lter to several other servers over a network. Can we gain anything by compressing the resulting Bloom lter? If we choose the optimal value for k to minimize the false probability as calculated above, then p = 1=2. Under our assumption of good random hash functions, the bit array is essenti ...
... a Bloom lter to several other servers over a network. Can we gain anything by compressing the resulting Bloom lter? If we choose the optimal value for k to minimize the false probability as calculated above, then p = 1=2. Under our assumption of good random hash functions, the bit array is essenti ...
Oracle`s Business Strategy: Maximizing Your Sales Leverage
... • Trie’s (Text retRieval data structure) can be used deterministically to find the closest match in a dictionary of words. Unsuccessful searches terminate quickly. Searches are usually tolerant and allows ...
... • Trie’s (Text retRieval data structure) can be used deterministically to find the closest match in a dictionary of words. Unsuccessful searches terminate quickly. Searches are usually tolerant and allows ...
y-fast Trees
... We can define correspondences u ∈ U ←→ bit string ←→ path in a balanced binary search tree. For all x in our set, we will store a dynamic perfect hash table of all prefixes of these strings. Unfortunately, this structure requires O(n lg u) space, because there are n elements, each of which have lg u ...
... We can define correspondences u ∈ U ←→ bit string ←→ path in a balanced binary search tree. For all x in our set, we will store a dynamic perfect hash table of all prefixes of these strings. Unfortunately, this structure requires O(n lg u) space, because there are n elements, each of which have lg u ...
The NDN Forwarding Plane
... Decides what to do for each incoming packet. Can be divided into multiple layers based on the functions: 1. The strategy layer Selects forwarding strategies and impacts the forwarding decisions. 2. The data forwarding layer Packet forwarding, pending Interest management and temporary content sto ...
... Decides what to do for each incoming packet. Can be divided into multiple layers based on the functions: 1. The strategy layer Selects forwarding strategies and impacts the forwarding decisions. 2. The data forwarding layer Packet forwarding, pending Interest management and temporary content sto ...
CS 61B Data Structures and Programming Methodology
... long (according to the Oxford Dictionary "a facticious word alleged to mean 'a lung disease caused by the inhalation of very fine silica dust causing inflammation in the lungs. Occurring chiefly as an instance of a very long word.) – Unfortunately, declaring an array of length 2645 is out of the que ...
... long (according to the Oxford Dictionary "a facticious word alleged to mean 'a lung disease caused by the inhalation of very fine silica dust causing inflammation in the lungs. Occurring chiefly as an instance of a very long word.) – Unfortunately, declaring an array of length 2645 is out of the que ...
Bloom filter
A Bloom filter is a space-efficient probabilistic data structure, conceived by Burton Howard Bloom in 1970, that is used to test whether an element is a member of a set. False positive matches are possible, but false negatives are not, thus a Bloom filter has a 100% recall rate. In other words, a query returns either ""possibly in set"" or ""definitely not in set"". Elements can be added to the set, but not removed (though this can be addressed with a ""counting"" filter). The more elements that are added to the set, the larger the probability of false positives.Bloom proposed the technique for applications where the amount of source data would require an impractically large amount of memory if ""conventional"" error-free hashing techniques were applied. He gave the example of a hyphenation algorithm for a dictionary of 500,000 words, out of which 90% follow simple hyphenation rules, but the remaining 10% require expensive disk accesses to retrieve specific hyphenation patterns. With sufficient core memory, an error-free hash could be used to eliminate all unnecessary disk accesses; on the other hand, with limited core memory, Bloom's technique uses a smaller hash area but still eliminates most unnecessary accesses. For example, a hash area only 15% of the size needed by an ideal error-free hash still eliminates 85% of the disk accesses, an 85–15 form of the Pareto principle (Bloom (1970)).More generally, fewer than 10 bits per element are required for a 1% false positive probability, independent of the size or number of elements in the set (Bonomi et al. (2006)).





![[Sets] [Hello. This is Rachel Cardell](http://s1.studyres.com/store/data/000219922_1-85acba46f3035809e6b6362c02e31e32-300x300.png)