HashTables - University of Arizona
... Most often the data stored in a hash table includes both a key field and a data field (e.g., social security number and student information). The key field determines where to store the value. A lookup on that key will then return the value associated with that key (if it is mapped in the ...
... Most often the data stored in a hash table includes both a key field and a data field (e.g., social security number and student information). The key field determines where to store the value. A lookup on that key will then return the value associated with that key (if it is mapped in the ...
CSE 331. Computer Organization
... designed for translating attribute values into TID, or into other types of internal addresses of tuples having those attribute values, is called access ...
... designed for translating attribute values into TID, or into other types of internal addresses of tuples having those attribute values, is called access ...
Sequential Search Search Algorithms
... – We can choose m to make the implementation easy and/or fast. ...
... – We can choose m to make the implementation easy and/or fast. ...
types of searchings - SSC Recruitment Results
... sorted and unsorted arrays. However, these are not the only data types that are useful for searching. ...
... sorted and unsorted arrays. However, these are not the only data types that are useful for searching. ...
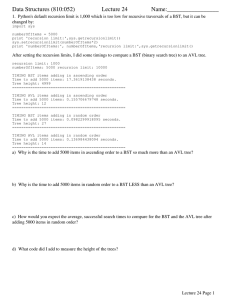
Data Structures (810:052) Lecture 24 Name:_________________
... b) Similarly, binary search of a sorted array or AVL tree always uses a fixed search strategy for any given target value. For example, binary search always compares the target value with the middle element of the remaining portion of the array needing to be searched. If n is the number of items bein ...
... b) Similarly, binary search of a sorted array or AVL tree always uses a fixed search strategy for any given target value. For example, binary search always compares the target value with the middle element of the remaining portion of the array needing to be searched. If n is the number of items bein ...
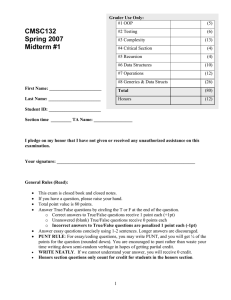
Midterm Solutions
... There are two main approaches. (Note that we excluded 0 and −263 since these are the only two long integers x such that x + −x = 0.) • Hashing. Insert each integer x into a hash table (linear probing or separate chaining). When inserting x, check if −x is already in the hash table. If so, you’ve fou ...
... There are two main approaches. (Note that we excluded 0 and −263 since these are the only two long integers x such that x + −x = 0.) • Hashing. Insert each integer x into a hash table (linear probing or separate chaining). When inserting x, check if −x is already in the hash table. If so, you’ve fou ...
Longest Prefix Matching using Bloom Filters
... parallel. Some algorithms allow dependent memory accesses to be masked via pipelining, with each stage accessing an independent memory bank or port; however, this quickly becomes an expensive option. We provide an overview of the prominent LPM algorithmic developments and a comparison of TCAM and SR ...
... parallel. Some algorithms allow dependent memory accesses to be masked via pipelining, with each stage accessing an independent memory bank or port; however, this quickly becomes an expensive option. We provide an overview of the prominent LPM algorithmic developments and a comparison of TCAM and SR ...
ppt
... • Splaying can be done top-down; better because: – only one pass – no recursion or parent pointers necessary ...
... • Splaying can be done top-down; better because: – only one pass – no recursion or parent pointers necessary ...
k - Current students
... We use the heap with the largest element on top. During the execution, left part of S (S[0:i-1]) is used to store the elements of the heap, and the right portion (S[i+1,n]). In the heap part of S, the element at the position k is greater or equal to its children at the positions 2k+1 and 2k+2. In th ...
... We use the heap with the largest element on top. During the execution, left part of S (S[0:i-1]) is used to store the elements of the heap, and the right portion (S[i+1,n]). In the heap part of S, the element at the position k is greater or equal to its children at the positions 2k+1 and 2k+2. In th ...
printer-friendly
... • We now have several implementations of data structures in which we can store and search for objects ...
... • We now have several implementations of data structures in which we can store and search for objects ...
Notes 33 Royden
... •Index functions are not always simple functions that compute an integer value from integer inputs. ...
... •Index functions are not always simple functions that compute an integer value from integer inputs. ...
Hashing 1
... development of hashing schemes while there already are other techniques that can be used to realize the same functionality provided by hashing methods? 2. How many storage cells will be wasted in an array implementation with O(1) access for records of 10,000 students each with a 7-digit ID number? 3 ...
... development of hashing schemes while there already are other techniques that can be used to realize the same functionality provided by hashing methods? 2. How many storage cells will be wasted in an array implementation with O(1) access for records of 10,000 students each with a 7-digit ID number? 3 ...
Hash Tables
... development of hashing schemes while there already are other techniques that can be used to realize the same functionality provided by hashing methods? 2. How many storage cells will be wasted in an array implementation with O(1) access for records of 10,000 students each with a 7-digit ID number? 3 ...
... development of hashing schemes while there already are other techniques that can be used to realize the same functionality provided by hashing methods? 2. How many storage cells will be wasted in an array implementation with O(1) access for records of 10,000 students each with a 7-digit ID number? 3 ...
PPT
... ○ Should distribute keys uniformly into slots ○ Should not depend on patterns in the data ...
... ○ Should distribute keys uniformly into slots ○ Should not depend on patterns in the data ...
The Pigeonhole Principle and Hashing
... Hashing and Association Tables (Maps, Dictionaries) A dictionary (or map or association table) is a collection of keyvalue pairs. In general, the objects in a table have no fixed order and each object is accessed by using the associated key. For example, we could have a table of motor vehicle drive ...
... Hashing and Association Tables (Maps, Dictionaries) A dictionary (or map or association table) is a collection of keyvalue pairs. In general, the objects in a table have no fixed order and each object is accessed by using the associated key. For example, we could have a table of motor vehicle drive ...
Power Point 2000
... Use all characters in the name Use the ordering information of each character Short names should not cluster in the table ...
... Use all characters in the name Use the ordering information of each character Short names should not cluster in the table ...
ppt
... history independent: if any two sequences of operations S1 and S2 that yield the same content induce the same probability distribution on memory representation strongly history independent: if given any two sets of breakpoints along S1 and S2 s.t. corresponding points have identical contents, S1 and ...
... history independent: if any two sequences of operations S1 and S2 that yield the same content induce the same probability distribution on memory representation strongly history independent: if given any two sets of breakpoints along S1 and S2 s.t. corresponding points have identical contents, S1 and ...
Bloom filter
A Bloom filter is a space-efficient probabilistic data structure, conceived by Burton Howard Bloom in 1970, that is used to test whether an element is a member of a set. False positive matches are possible, but false negatives are not, thus a Bloom filter has a 100% recall rate. In other words, a query returns either ""possibly in set"" or ""definitely not in set"". Elements can be added to the set, but not removed (though this can be addressed with a ""counting"" filter). The more elements that are added to the set, the larger the probability of false positives.Bloom proposed the technique for applications where the amount of source data would require an impractically large amount of memory if ""conventional"" error-free hashing techniques were applied. He gave the example of a hyphenation algorithm for a dictionary of 500,000 words, out of which 90% follow simple hyphenation rules, but the remaining 10% require expensive disk accesses to retrieve specific hyphenation patterns. With sufficient core memory, an error-free hash could be used to eliminate all unnecessary disk accesses; on the other hand, with limited core memory, Bloom's technique uses a smaller hash area but still eliminates most unnecessary accesses. For example, a hash area only 15% of the size needed by an ideal error-free hash still eliminates 85% of the disk accesses, an 85–15 form of the Pareto principle (Bloom (1970)).More generally, fewer than 10 bits per element are required for a 1% false positive probability, independent of the size or number of elements in the set (Bonomi et al. (2006)).