Hash Table Functions Redouan Lahmyed*, Parid Weasamae*, Said
... which is used when needing for quick processing for searching and input operations. This data structure uses hash function which convert input values into other values, index, in the table. When a collision is happened, it can be solved using ‘open addressing’ method or ‘separate chaining’. In case ...
... which is used when needing for quick processing for searching and input operations. This data structure uses hash function which convert input values into other values, index, in the table. When a collision is happened, it can be solved using ‘open addressing’ method or ‘separate chaining’. In case ...
csci 210: Data Structures Maps and Hash Tables
... • Best hashing method depends on application • Probing is the method of choice if n can be guessed • Linear probing is fastest if table is sparse • Double hashing makes most efficient use of memory as it allows the table to become more full, but requires extra time to to compute a second hash functi ...
... • Best hashing method depends on application • Probing is the method of choice if n can be guessed • Linear probing is fastest if table is sparse • Double hashing makes most efficient use of memory as it allows the table to become more full, but requires extra time to to compute a second hash functi ...
ch13hashing
... – Changes the structure of the hash table so that it can accommodate more than one item in the same location – Buckets • Each location in the hash table is itself an array called a bucket – Separate chaining • Each hash table location is a linked list ...
... – Changes the structure of the hash table so that it can accommodate more than one item in the same location – Buckets • Each location in the hash table is itself an array called a bucket – Separate chaining • Each hash table location is a linked list ...
Basic Data Structures
... • Good when new stuff will come in over time, rather than all read at beginning ...
... • Good when new stuff will come in over time, rather than all read at beginning ...
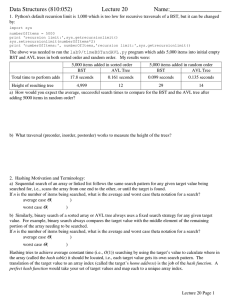
Data Structures (810:052) Lecture 20 Name:_________________
... then the record cannot be inserted even though the table is not full! A more realistic example is a table with 105 slots. The probe sequence starting from any given slot will only visit 23 other slots in the table. If all 24 of these slots should happen to be full, even if other slots in the table a ...
... then the record cannot be inserted even though the table is not full! A more realistic example is a table with 105 slots. The probe sequence starting from any given slot will only visit 23 other slots in the table. If all 24 of these slots should happen to be full, even if other slots in the table a ...
hash function
... Boyer-Moore string search algorithm 1. calculate the bad character and good suffix shift tables 2. while match not found and not off the edge a) ...
... Boyer-Moore string search algorithm 1. calculate the bad character and good suffix shift tables 2. while match not found and not off the edge a) ...
ppt - Dave Reed
... in practice, chaining is generally faster than probing cost of insertion is O(1) – simply map to index and add to list cost of search is proportional to number of items already mapped to same index e.g., using naïve "first letter" hash function, searching for "APPLE" might requires traversing a ...
... in practice, chaining is generally faster than probing cost of insertion is O(1) – simply map to index and add to list cost of search is proportional to number of items already mapped to same index e.g., using naïve "first letter" hash function, searching for "APPLE" might requires traversing a ...
Lecture 12 — March 21, 2007 1 Overview 2 Models of Computation
... or writes) and any additional computation is free. Memory cells have some size w, which is a parameter of the model. The model is non-uniform, and allows memory reads or writes to depend arbitrarily on past cell probes. Though not realistic to implement, it is good for proving lower bounds. Transdic ...
... or writes) and any additional computation is free. Memory cells have some size w, which is a parameter of the model. The model is non-uniform, and allows memory reads or writes to depend arbitrarily on past cell probes. Though not realistic to implement, it is good for proving lower bounds. Transdic ...
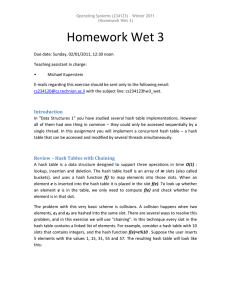
Review – Hash Tables with Chaining
... We only require you to submit the implementation of your hash table, but not any test programs that use the data structure. Of course, this does not mean you will not need a test program for debugging! Insertion and removal from a linked-list that has a lock for each element are not trivial to imple ...
... We only require you to submit the implementation of your hash table, but not any test programs that use the data structure. Of course, this does not mean you will not need a test program for debugging! Insertion and removal from a linked-list that has a lock for each element are not trivial to imple ...
INFOSYS 255 Lecture 16: Hash Tables
... Search: It is proportional to max linked list length Delete: Same as search ...
... Search: It is proportional to max linked list length Delete: Same as search ...
CS2007Ch12C
... All previous searching techniques require a specified amount of time (O(logn) or O(n)) Time usually depends on number of elements (n) stored in the table In some situations searching should be almost ...
... All previous searching techniques require a specified amount of time (O(logn) or O(n)) Time usually depends on number of elements (n) stored in the table In some situations searching should be almost ...
The Map ADT and Hash Tables
... social security number and student information). ♦ The key field determines where to store the value. ♦ A lookup on that key will then return the value associated with that key (if it is mapped in the ...
... social security number and student information). ♦ The key field determines where to store the value. ♦ A lookup on that key will then return the value associated with that key (if it is mapped in the ...
Engineering a Sorted List Data Structure for 32 Bit Keys
... 2.2 Variants: The data structure allows several in- by exploiting that IEEE floats keep their relative order when interpreted as integers. teresting variants: Saving Space: Our Stree data structure can consume considerably more space than comparison based search trees. This is particularly severe if ...
... 2.2 Variants: The data structure allows several in- by exploiting that IEEE floats keep their relative order when interpreted as integers. teresting variants: Saving Space: Our Stree data structure can consume considerably more space than comparison based search trees. This is particularly severe if ...
Picking a random element in an array or any other data structure is
... Picking a random element in an array or any other data structure is the easiest way to select a pivot element. Since the Quick Sort is a divide-and-conquer algorithm, the pivot element acts as the starting point upon which the array is divided in to two. This endeavors to achieve the O(N*logN) effic ...
... Picking a random element in an array or any other data structure is the easiest way to select a pivot element. Since the Quick Sort is a divide-and-conquer algorithm, the pivot element acts as the starting point upon which the array is divided in to two. This endeavors to achieve the O(N*logN) effic ...
hash function
... if the table becomes three-quarters full, then must resize create new table at least twice as big just copy over table entries to same locations??? NO! when you resize, you have to rehash existing entries new table size new hash function (+ different wraparound) ...
... if the table becomes three-quarters full, then must resize create new table at least twice as big just copy over table entries to same locations??? NO! when you resize, you have to rehash existing entries new table size new hash function (+ different wraparound) ...
Midterm1Spring07Key
... a. Data structures differ mainly in the amount of storage required b. A queue is a restricted version of a list c. Elements are removed from a stack in reverse order of insertion d. Sets may contain duplicate elements e. Maps may contain more keys than values f. A key may be used to retrieve multipl ...
... a. Data structures differ mainly in the amount of storage required b. A queue is a restricted version of a list c. Elements are removed from a stack in reverse order of insertion d. Sets may contain duplicate elements e. Maps may contain more keys than values f. A key may be used to retrieve multipl ...
Bloom filter
A Bloom filter is a space-efficient probabilistic data structure, conceived by Burton Howard Bloom in 1970, that is used to test whether an element is a member of a set. False positive matches are possible, but false negatives are not, thus a Bloom filter has a 100% recall rate. In other words, a query returns either ""possibly in set"" or ""definitely not in set"". Elements can be added to the set, but not removed (though this can be addressed with a ""counting"" filter). The more elements that are added to the set, the larger the probability of false positives.Bloom proposed the technique for applications where the amount of source data would require an impractically large amount of memory if ""conventional"" error-free hashing techniques were applied. He gave the example of a hyphenation algorithm for a dictionary of 500,000 words, out of which 90% follow simple hyphenation rules, but the remaining 10% require expensive disk accesses to retrieve specific hyphenation patterns. With sufficient core memory, an error-free hash could be used to eliminate all unnecessary disk accesses; on the other hand, with limited core memory, Bloom's technique uses a smaller hash area but still eliminates most unnecessary accesses. For example, a hash area only 15% of the size needed by an ideal error-free hash still eliminates 85% of the disk accesses, an 85–15 form of the Pareto principle (Bloom (1970)).More generally, fewer than 10 bits per element are required for a 1% false positive probability, independent of the size or number of elements in the set (Bonomi et al. (2006)).