Chapter 1. Introduction to Data Communications
... determined by user profiles assigned to each user account by the net manager. • The profile specifies access details such as what data and network resources a user can access and the type of access (e.g., read, write, create, delete). • Most access is still password based, that is, users gain access ...
... determined by user profiles assigned to each user account by the net manager. • The profile specifies access details such as what data and network resources a user can access and the type of access (e.g., read, write, create, delete). • Most access is still password based, that is, users gain access ...
PowerPoint-10b - Community College of Rhode Island
... • Cryptography: Science of transforming information so that it is secure while being transmitted or stored – scrambles” data • Encryption: Transforming plaintext to ciphertext • Decryption: Transforming ciphertext to plaintext • Cipher: An encryption algorithm – Given a key that is used to encrypt a ...
... • Cryptography: Science of transforming information so that it is secure while being transmitted or stored – scrambles” data • Encryption: Transforming plaintext to ciphertext • Decryption: Transforming ciphertext to plaintext • Cipher: An encryption algorithm – Given a key that is used to encrypt a ...
Untersuchungen zur MAC Address Translation (MAT)
... Hardware consists of a datapath and an evolution module ...
... Hardware consists of a datapath and an evolution module ...
Guide to Operating System Security
... Use strongest forms of authentication and encryption permitted by OS Use longest encryption keys possible Inventory encryption and authentication methods used by OS; close any holes ...
... Use strongest forms of authentication and encryption permitted by OS Use longest encryption keys possible Inventory encryption and authentication methods used by OS; close any holes ...
PK b
... set of size d , and let F {S1 ,..., Sk } be a family of subsets of G. We say that subset Si S j if S j cover Si . We say that family F is t -cover free over G if each subset in F is not covered by the union of t subsets in F . Moreover, we say that a family of subsets is q-uniform if all subsets ...
... set of size d , and let F {S1 ,..., Sk } be a family of subsets of G. We say that subset Si S j if S j cover Si . We say that family F is t -cover free over G if each subset in F is not covered by the union of t subsets in F . Moreover, we say that a family of subsets is q-uniform if all subsets ...
Insert Title Here
... Escrow mechanisms are a security hazard If required, perform at key generation, in the physical presence of humans Physically export Key Encryption Key and protect Export other keys encrypted with Key Encryption Key ...
... Escrow mechanisms are a security hazard If required, perform at key generation, in the physical presence of humans Physically export Key Encryption Key and protect Export other keys encrypted with Key Encryption Key ...
Course Name : INFORMATION SECURITY
... 2. (a) Compare and contrast between Cryptography and Cryptology. (b) Explain the various Key distribution methods. [8+8] 3. (a) Explain the procedure involved in RSA public-key encryption algorithm. (b) Explain what Kerberos is and give its requirements. [8+8] 4. Clearly explain in detail the Multip ...
... 2. (a) Compare and contrast between Cryptography and Cryptology. (b) Explain the various Key distribution methods. [8+8] 3. (a) Explain the procedure involved in RSA public-key encryption algorithm. (b) Explain what Kerberos is and give its requirements. [8+8] 4. Clearly explain in detail the Multip ...
CM109C2
... compliance with the ITU-T G.703 (2 Mbit/s) standard. The chassis is made of a light aluminium alloy with upper removable cover. The device comprises four main elements: the power supply, the control and encryption sections, the interfaces and the front panel. CM109C2 can store up to 60 crypto variab ...
... compliance with the ITU-T G.703 (2 Mbit/s) standard. The chassis is made of a light aluminium alloy with upper removable cover. The device comprises four main elements: the power supply, the control and encryption sections, the interfaces and the front panel. CM109C2 can store up to 60 crypto variab ...
IPSec
... IPSec is an abbreviation for IP security, which is used to transfer data securely over unprotected networks like “Internet”. It acts at the networks layer and is part of IPv6. The protocol/process is as follows : Sender encrypts packets before sending them on the network. Receiver authenti ...
... IPSec is an abbreviation for IP security, which is used to transfer data securely over unprotected networks like “Internet”. It acts at the networks layer and is part of IPv6. The protocol/process is as follows : Sender encrypts packets before sending them on the network. Receiver authenti ...
Hidden Markov Model Cryptanalysis
... Sequence of hidden, probabilistic states (S) Corresponding observable outputs (O) Each state is independent of every other (memoryless) P (S1 = x1) ...
... Sequence of hidden, probabilistic states (S) Corresponding observable outputs (O) Each state is independent of every other (memoryless) P (S1 = x1) ...
Blue Border - Courant Institute of Mathematical Sciences
... Have (u,v) where u=rA and v=+z(q/2)
Compute ( - v)
If - v is closer to 0 than to q/2, then decrypt to 0
If - v is closer to q/2 than to 0, then decrypt to 1
- v = rAs – r(As+e) -z(q/2)
= - z(q/2)
if all coefficients of e are < sqrt(q), || < m*sqrt(q)
So if q >> ...
... Have (u,v) where u=rA and v=
Security Risks
... – Data encrypted using two keys – Private key: user knows – Public key: anyone may request ...
... – Data encrypted using two keys – Private key: user knows – Public key: anyone may request ...
Chapter 19: Security
... the role of authentication in providing secure systems. access control models, policies and mechanisms. public-key/private-key cryptography. security and authentication protocols, such as SSL and Kerberos. digital signatures, digital certificates and certificate authorities. security threats, such a ...
... the role of authentication in providing secure systems. access control models, policies and mechanisms. public-key/private-key cryptography. security and authentication protocols, such as SSL and Kerberos. digital signatures, digital certificates and certificate authorities. security threats, such a ...
Chapter 19: Security
... the role of authentication in providing secure systems. access control models, policies and mechanisms. public-key/private-key cryptography. security and authentication protocols, such as SSL and Kerberos. digital signatures, digital certificates and certificate authorities. security threats, such a ...
... the role of authentication in providing secure systems. access control models, policies and mechanisms. public-key/private-key cryptography. security and authentication protocols, such as SSL and Kerberos. digital signatures, digital certificates and certificate authorities. security threats, such a ...
Chapter 19: Security - Murray State University
... the role of authentication in providing secure systems. access control models, policies and mechanisms. public-key/private-key cryptography. security and authentication protocols, such as SSL and Kerberos. digital signatures, digital certificates and certificate authorities. security threats, such a ...
... the role of authentication in providing secure systems. access control models, policies and mechanisms. public-key/private-key cryptography. security and authentication protocols, such as SSL and Kerberos. digital signatures, digital certificates and certificate authorities. security threats, such a ...
technology neutrality on electronic signatures
... measurements, no matter how they are collected and processed, they are collected and processed by computerized devices. Non-computable techniques have nothing to do with biometrics. By non-computable techniques I referred to some natural systems found for example on Quantum Mechanics that can be use ...
... measurements, no matter how they are collected and processed, they are collected and processed by computerized devices. Non-computable techniques have nothing to do with biometrics. By non-computable techniques I referred to some natural systems found for example on Quantum Mechanics that can be use ...
How to Encrypt with the LPN Problem
... Key words: symmetric encryption, LPN, error-correcting code. ...
... Key words: symmetric encryption, LPN, error-correcting code. ...
answer-sheet-7540-040-7630-345-b_
... you are the only person with your fingerprint or retina, therefore no one else will be able to get access into your computer or laptop. CCTV: CCTV are camera’s that will provide physical access control as it will protect against theft and vandalism, this is because if a PC has been damaged or stolen ...
... you are the only person with your fingerprint or retina, therefore no one else will be able to get access into your computer or laptop. CCTV: CCTV are camera’s that will provide physical access control as it will protect against theft and vandalism, this is because if a PC has been damaged or stolen ...
XML: Part - Houston Community College System
... Symmetric Cryptography Strengths and Weaknesses • Identical keys are used to both encrypt and decrypt the message • Popular symmetric cipher algorithms include Data Encryption Standard, Triple Data Encryption Standard, Advanced Encryption Standard, Rivest Cipher, International Data Encryption Algor ...
... Symmetric Cryptography Strengths and Weaknesses • Identical keys are used to both encrypt and decrypt the message • Popular symmetric cipher algorithms include Data Encryption Standard, Triple Data Encryption Standard, Advanced Encryption Standard, Rivest Cipher, International Data Encryption Algor ...
Lecture 10
... Alice receives t and y from Bob, and a 1 Calculates c (t ) mod p and y (t a ) 1 mod p x . Question: Why does it work? It works since: t a (s k ) a s ak mod p , so y (t a ) 1 ( x s ak ) (s ak ) 1 x mod p . ...
... Alice receives t and y from Bob, and a 1 Calculates c (t ) mod p and y (t a ) 1 mod p x . Question: Why does it work? It works since: t a (s k ) a s ak mod p , so y (t a ) 1 ( x s ak ) (s ak ) 1 x mod p . ...
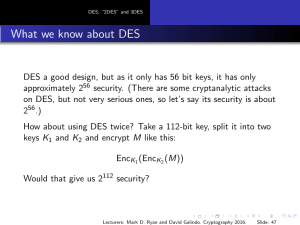
Slides
... “2DES” is not significantly more secure than DES Suppose we have a pair (M, C ) consisting of a valid plaintext-ciphertext pair. With approximately 257 work, we can find the 112-bit key K1 K2 used in 2DES. Here is how to do it. Try all 256 possible keys K2 , and store all the results EncK2 (M). Sort ...
... “2DES” is not significantly more secure than DES Suppose we have a pair (M, C ) consisting of a valid plaintext-ciphertext pair. With approximately 257 work, we can find the 112-bit key K1 K2 used in 2DES. Here is how to do it. Try all 256 possible keys K2 , and store all the results EncK2 (M). Sort ...
Net+ Chapter 1
... some of the higher-level protocols such as Hypertext Transfer Protocol (HTTP) and File Transfer Protocol (FTP). SSL uses a series of keys, public and private, to encrypt the data that is transported across the secure connection. ...
... some of the higher-level protocols such as Hypertext Transfer Protocol (HTTP) and File Transfer Protocol (FTP). SSL uses a series of keys, public and private, to encrypt the data that is transported across the secure connection. ...
Devireddy
... actively attacking from both ends. If the attacker guesses the headers of a packet, which includes destination IP address, he can flip relevant bits to make the destination system to send the packet to his own system and transmit it using some mobile station. attacking using table of appropriate i ...
... actively attacking from both ends. If the attacker guesses the headers of a packet, which includes destination IP address, he can flip relevant bits to make the destination system to send the packet to his own system and transmit it using some mobile station. attacking using table of appropriate i ...
Securing Distribution Automation
... The availability of an enterprise uplink can generally not be ensured at all times and a local authentication solution is still required. To fulfill this requirement, some vendors provide an innovative mechanism where a remote access server grants the user a limited duration “security ticket” that ...
... The availability of an enterprise uplink can generally not be ensured at all times and a local authentication solution is still required. To fulfill this requirement, some vendors provide an innovative mechanism where a remote access server grants the user a limited duration “security ticket” that ...
History of cryptography

Cryptography, the use of codes and ciphers to protect secrets, began thousands of years ago. Until recent decades, it has been the story of what might be called classic cryptography — that is, of methods of encryption that use pen and paper, or perhaps simple mechanical aids. In the early 20th century, the invention of complex mechanical and electromechanical machines, such as the Enigma rotor machine, provided more sophisticated and efficient means of encryption; and the subsequent introduction of electronics and computing has allowed elaborate schemes of still greater complexity, most of which are entirely unsuited to pen and paper.The development of cryptography has been paralleled by the development of cryptanalysis — the ""breaking"" of codes and ciphers. The discovery and application, early on, of frequency analysis to the reading of encrypted communications has, on occasion, altered the course of history. Thus the Zimmermann Telegram triggered the United States' entry into World War I; and Allied reading of Nazi Germany's ciphers shortened World War II, in some evaluations by as much as two years.Until the 1970s, secure cryptography was largely the preserve of governments. Two events have since brought it squarely into the public domain: the creation of a public encryption standard (DES), and the invention of public-key cryptography.