Click here to view PowerPoint slides
... • Perceptual modes in defensive I/W operations – Alerting is the primary mode • Known (components of) earlier attacks • Anomalous behavior – relative to standards on message protocols • Technologically easy to “prime for” many such alerts – NB a real attack may be a subtle one among many simultaneou ...
... • Perceptual modes in defensive I/W operations – Alerting is the primary mode • Known (components of) earlier attacks • Anomalous behavior – relative to standards on message protocols • Technologically easy to “prime for” many such alerts – NB a real attack may be a subtle one among many simultaneou ...
Synchronizing Guidelines - RangeMaster AM Transmitters
... the Master is operating disable the Master output by removing the coil tap select shunt J6. These jumpers are located near the large coil. This will disable the RF signal but still allow the sync signal to be sent to the Slave. Return this shunt to its original position after tuning slaves. Turn on ...
... the Master is operating disable the Master output by removing the coil tap select shunt J6. These jumpers are located near the large coil. This will disable the RF signal but still allow the sync signal to be sent to the Slave. Return this shunt to its original position after tuning slaves. Turn on ...
ber performance over fading channels diversity
... Fading is the term used to describe the rapid fluctuations in the amplitude of the received radio signal over a short period of time. Fading is a common phenomenon in Mobile Communication Channels, where it is caused due to the interference between two or more versions of the transmitted signals whi ...
... Fading is the term used to describe the rapid fluctuations in the amplitude of the received radio signal over a short period of time. Fading is a common phenomenon in Mobile Communication Channels, where it is caused due to the interference between two or more versions of the transmitted signals whi ...
Our Guidelines to Email and SMS Communications
... Opt-out: Remove permission to receive electronic communications. Phishing: Is an attempt to fraudulently acquire sensitive information, such as usernames, passwords and credit card details, by masquerading as a trustworthy entity in an electronic communication. SMS/Text message: The Short Message Se ...
... Opt-out: Remove permission to receive electronic communications. Phishing: Is an attempt to fraudulently acquire sensitive information, such as usernames, passwords and credit card details, by masquerading as a trustworthy entity in an electronic communication. SMS/Text message: The Short Message Se ...
Keysight Technologies DME Uses N6700 Power Supplies to Help
... subcomponents, to put it into the different modes required for testing. The only external equipment it currently uses is the N6700 low-profile modular power supply, which is connected via USB. Some radios require as many as five different voltages, in which case DME engineers pull four of them off t ...
... subcomponents, to put it into the different modes required for testing. The only external equipment it currently uses is the N6700 low-profile modular power supply, which is connected via USB. Some radios require as many as five different voltages, in which case DME engineers pull four of them off t ...
8th Symposium on Networking and Wireless
... Papers must be of high quality, unpublished, and currently not accepted or under review by another conference, workshop, or journal. All submissions must include author names and complete mailing addresses (including telephone number, fax number, and the email address). Extra charges will apply if f ...
... Papers must be of high quality, unpublished, and currently not accepted or under review by another conference, workshop, or journal. All submissions must include author names and complete mailing addresses (including telephone number, fax number, and the email address). Extra charges will apply if f ...
(13) 058
... telecommunication and ICT development and recognizes that radio spectrum is an essential natural resource for wireless connections and innovation. Given the the fact, that radio spectrum is a key resource for many essential services in society, including wireless and satellite communications, radio ...
... telecommunication and ICT development and recognizes that radio spectrum is an essential natural resource for wireless connections and innovation. Given the the fact, that radio spectrum is a key resource for many essential services in society, including wireless and satellite communications, radio ...
4.2 Digital Transmission
... □ Secure communication through the use of special modulation schemes of encryption. □ These advantages are obtained at the cost of more complexity and increased BT. □ With cost-effective implementations, the cost issue no longer a problem of concern. □ With the availability of wide-band communicatio ...
... □ Secure communication through the use of special modulation schemes of encryption. □ These advantages are obtained at the cost of more complexity and increased BT. □ With cost-effective implementations, the cost issue no longer a problem of concern. □ With the availability of wide-band communicatio ...
Bluetooth Controlled Robot
... The bluetooth app sends user defined signal to the BT module which inturn transmits it to the ATmega16. The micro controller employs USART communication to achieve the reception from the bluetooth module. The microcontroller process the received signal through programmed codes and logics to gi ...
... The bluetooth app sends user defined signal to the BT module which inturn transmits it to the ATmega16. The micro controller employs USART communication to achieve the reception from the bluetooth module. The microcontroller process the received signal through programmed codes and logics to gi ...
White Space Internet Device - Stevens Institute of Technology
... converts the analog signal received by the antenna into a digital signal which can be processed. This digital signal then passes through a digital signal processor, which will ultimately allow the signal to be broadcast through some internet protocol. A micro-controller will be used to handle the de ...
... converts the analog signal received by the antenna into a digital signal which can be processed. This digital signal then passes through a digital signal processor, which will ultimately allow the signal to be broadcast through some internet protocol. A micro-controller will be used to handle the de ...
Best-First Search
... When the children have been generated, alternative choices are evaluated using some type of heuristic function. The path that appears most promising is then chosen and no further reference to the parent or other children is retained. This process continues from node to node with previously expanded ...
... When the children have been generated, alternative choices are evaluated using some type of heuristic function. The path that appears most promising is then chosen and no further reference to the parent or other children is retained. This process continues from node to node with previously expanded ...
Document
... o Lumped / distributed systems: A lumped system’s physical dimensions are much smaller than the wavelength of the signal. A distributed system’s physical dimensions are comparable to the wavelength of the signal. o Continuous- / discrete-time systems: Time axis o Analog / digital systems: Vertical a ...
... o Lumped / distributed systems: A lumped system’s physical dimensions are much smaller than the wavelength of the signal. A distributed system’s physical dimensions are comparable to the wavelength of the signal. o Continuous- / discrete-time systems: Time axis o Analog / digital systems: Vertical a ...
The Multiphase Functional Cardiogram A Clinical
... along the left ventricular axis. The sampling rate is calculated to target frequency domain components that fall between 1 Hz (a 60 bpm heart rate) and 35 Hz6 . Multiple cardiac cycles for the two leads are sampled to provide a view of cardiac function over time, and mathematical models of the cardi ...
... along the left ventricular axis. The sampling rate is calculated to target frequency domain components that fall between 1 Hz (a 60 bpm heart rate) and 35 Hz6 . Multiple cardiac cycles for the two leads are sampled to provide a view of cardiac function over time, and mathematical models of the cardi ...
BME 373 – Biomedical Electronics II
... knowledge in more complicated circuit designs, field effect transistors, amplifiers, frequency response, signal generation, timers, and wave-shaping circuits. Apply knowledge of engineering and science to identify, formulate, and solve problems in these areas. 2. Data Interpretation: Learn to design ...
... knowledge in more complicated circuit designs, field effect transistors, amplifiers, frequency response, signal generation, timers, and wave-shaping circuits. Apply knowledge of engineering and science to identify, formulate, and solve problems in these areas. 2. Data Interpretation: Learn to design ...
FTAA Joint Public-Private Sector Committee of Experts
... Historically, cryptography has been used to encode information to conceal secret messages and to secure private communications using codes and ciphers. Cryptography is an important component of secure information and communication systems and an essential technology for enabling electronic commerce. ...
... Historically, cryptography has been used to encode information to conceal secret messages and to secure private communications using codes and ciphers. Cryptography is an important component of secure information and communication systems and an essential technology for enabling electronic commerce. ...
Contextually Supervised Source Separation with Application to
... From the applied point of view, algorithms for energy disaggregation have received growing interest in recently years [11, 22, 12, 16]. This is an important task since many studies have shown that consumers naturally adopt energy conserving behaviors when presented with a breakdown of their energy u ...
... From the applied point of view, algorithms for energy disaggregation have received growing interest in recently years [11, 22, 12, 16]. This is an important task since many studies have shown that consumers naturally adopt energy conserving behaviors when presented with a breakdown of their energy u ...
Professional Malware is a Pandemic
... A motivated & funded adversary will get in… it’s a just matter of time… New & Improved security diagnostics ARE needed to keep up with the bad guys: • Memory Forensics - better malware detection RAM today, E-Prom’s on motherboards & video card memory tomorrow ...
... A motivated & funded adversary will get in… it’s a just matter of time… New & Improved security diagnostics ARE needed to keep up with the bad guys: • Memory Forensics - better malware detection RAM today, E-Prom’s on motherboards & video card memory tomorrow ...
Conventional versus Broadband Radar™
... Conventional pulse radar uses a magnetron to generate a pulsed microwave signal that is transmitted from the rotating radar antenna. This burst of microwave energy is reflected off any target that it hits and returns to the radar, with the time it takes determining the range and bearing. This type o ...
... Conventional pulse radar uses a magnetron to generate a pulsed microwave signal that is transmitted from the rotating radar antenna. This burst of microwave energy is reflected off any target that it hits and returns to the radar, with the time it takes determining the range and bearing. This type o ...
Slides
... relaxed problem is an admissible heuristic for the original problem. – number-of-tiles-out-of-place heuristic: the rules of the 8-puzzle are relaxed so that a tile can move anywhere – Manhattan heuristic: the rules of the 8-puzzle are relaxed so that a tile can move to any adjacent square – minimal ...
... relaxed problem is an admissible heuristic for the original problem. – number-of-tiles-out-of-place heuristic: the rules of the 8-puzzle are relaxed so that a tile can move anywhere – Manhattan heuristic: the rules of the 8-puzzle are relaxed so that a tile can move to any adjacent square – minimal ...
EN 1414751
... In recent years, Power Quality (PQ) is a problem makes interest to both electric utilities & customers. The disturbance in power quality is primarily due to increase in using switching devices, unbalanced power system, nonlinear loads, computers and data processing. PQ disturbances such as sag, swel ...
... In recent years, Power Quality (PQ) is a problem makes interest to both electric utilities & customers. The disturbance in power quality is primarily due to increase in using switching devices, unbalanced power system, nonlinear loads, computers and data processing. PQ disturbances such as sag, swel ...
Network Interface Unit (NIU)
... where the interface is often bespoke and does not conform to any recognised international or national standards. Even where compatibility is claimed by equipment it is often only for part of a standard and the interface does not necessarily conform at all levels whether functional, electrical or phy ...
... where the interface is often bespoke and does not conform to any recognised international or national standards. Even where compatibility is claimed by equipment it is often only for part of a standard and the interface does not necessarily conform at all levels whether functional, electrical or phy ...
Sub Title Artificial Intelligence and Agent Technology
... reasoning tasks of a situated software agent. 4. To understand different logical systems for inference over formal domain representations, and trace how a particular inference algorithm works on a given problem specification. 5. To understand how to write a Prolog programs for Artificial Intelligenc ...
... reasoning tasks of a situated software agent. 4. To understand different logical systems for inference over formal domain representations, and trace how a particular inference algorithm works on a given problem specification. 5. To understand how to write a Prolog programs for Artificial Intelligenc ...
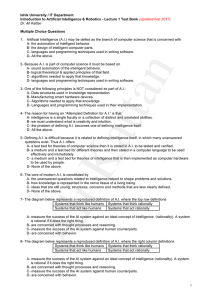
Test Bank #1
... A- measure the success of the AI system against an ideal concept of intelligence (rationality). A system is rational if it does the right thing. B- are concerned with thought processes and reasoning. C- measure the success of the AI system against human counterparts. D- are concerned with behavior. ...
... A- measure the success of the AI system against an ideal concept of intelligence (rationality). A system is rational if it does the right thing. B- are concerned with thought processes and reasoning. C- measure the success of the AI system against human counterparts. D- are concerned with behavior. ...
The Rhino Box TM - Metric Systems Corporation
... environment operating platform for commercial and industrial grade electronic equipment. • Facilitate a rapid and successful 1st time deployment process for complex communications, IT and sensor equipment suites. • Provide consistency in equipment performance by providing a controlled operating envi ...
... environment operating platform for commercial and industrial grade electronic equipment. • Facilitate a rapid and successful 1st time deployment process for complex communications, IT and sensor equipment suites. • Provide consistency in equipment performance by providing a controlled operating envi ...
Content Analytics for TIBCO Spotfire®, powered by
... the meaning in such content, locked up in emails, reports, etc. and merging this with information stored in perhaps a number of databases, a broader understanding can be lost. PerkinElmer Signals Perspectives, powered by Attivio®, unlocks the scientific value trapped in text-based sources of informa ...
... the meaning in such content, locked up in emails, reports, etc. and merging this with information stored in perhaps a number of databases, a broader understanding can be lost. PerkinElmer Signals Perspectives, powered by Attivio®, unlocks the scientific value trapped in text-based sources of informa ...
Signals intelligence

Signals intelligence (SIGINT) is intelligence-gathering by interception of signals, whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication (electronic intelligence—abbreviated to ELINT). Signals intelligence is a subset of intelligence collection management.As sensitive information is often encrypted, signals intelligence often involves the use of cryptanalysis to decipher the messages. Traffic analysis—the study of who is signaling whom and in what quantity—is also used to derive information.