Internet Applications - Guru Ghasidas Vishwavidyalaya
... Ans. The World Wide Web came into being in 1991, thanks to developer Tim BernersLee and others at the European Laboratory for Particle Physics, also known as Conseil European pour la Recherche Nucleure (CERN). The CERN team created the protocol based on hypertext that makes it possible to connect co ...
... Ans. The World Wide Web came into being in 1991, thanks to developer Tim BernersLee and others at the European Laboratory for Particle Physics, also known as Conseil European pour la Recherche Nucleure (CERN). The CERN team created the protocol based on hypertext that makes it possible to connect co ...
Internetworking : multicast and ATM network prerequisites for distance learning
... Tracey Emswiler used MBone tools to multicast Dr. Richard Hamming's course "Future of Science and Engineering: Learning to Learn" in real time over the global Internet during an entire quarter [Emswiler 95]. This was the first full academic course multicast globally. MBone has often been used for mu ...
... Tracey Emswiler used MBone tools to multicast Dr. Richard Hamming's course "Future of Science and Engineering: Learning to Learn" in real time over the global Internet during an entire quarter [Emswiler 95]. This was the first full academic course multicast globally. MBone has often been used for mu ...
The Quest for Artificial Intelligence
... All rights reserved. Please do not reproduce or cite. January 12, 2009 ...
... All rights reserved. Please do not reproduce or cite. January 12, 2009 ...
міністерство освіти і науки україни національний університет
... be a slow study Exercise 3. Read the text about Higher Education in Ukraine and translate it. Ukraine’s National Higher Education System In Ukraine, as in other developed countries, higher education is considered to be one of the main human values. Ukraine has inherited from the past a welldevelope ...
... be a slow study Exercise 3. Read the text about Higher Education in Ukraine and translate it. Ukraine’s National Higher Education System In Ukraine, as in other developed countries, higher education is considered to be one of the main human values. Ukraine has inherited from the past a welldevelope ...
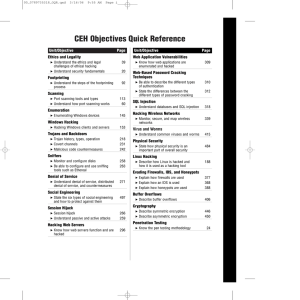
Exam Questions - Advanced Technology Support, Inc.
... All rights reserved. No part of this book shall be reproduced, stored in a retrieval system, or transmitted by any means, electronic, mechanical, photocopying, recording, or otherwise, without written permission from the publisher. No patent liability is assumed with respect to the use of the inform ...
... All rights reserved. No part of this book shall be reproduced, stored in a retrieval system, or transmitted by any means, electronic, mechanical, photocopying, recording, or otherwise, without written permission from the publisher. No patent liability is assumed with respect to the use of the inform ...
Dr.Halil ADAHAN NEAR EAST UNIVERSITY Faculty of
... Windows Server operating systems provide tools that you can use to manage servers from a remote location. These tools expand your flexibility because you can work as though you are physically present at each computer in your organization. The tools include the Remote Desktops nap-in, Active Director ...
... Windows Server operating systems provide tools that you can use to manage servers from a remote location. These tools expand your flexibility because you can work as though you are physically present at each computer in your organization. The tools include the Remote Desktops nap-in, Active Director ...
5th International Conference on Cyber Conflict Proceedings
... technological device or method that allowed us to increase the effectiveness and sophistication of cyber defensive and offensive actions, but also as a social factor which borders with the political, legal, moral and ethical framework of modern societies. All these factors remain in place as we move ...
... technological device or method that allowed us to increase the effectiveness and sophistication of cyber defensive and offensive actions, but also as a social factor which borders with the political, legal, moral and ethical framework of modern societies. All these factors remain in place as we move ...
Full book - NATO Cooperative Cyber Defence Centre of Excellence
... technological device or method that allowed us to increase the effectiveness and sophistication of cyber defensive and offensive actions, but also as a social factor which borders with the political, legal, moral and ethical framework of modern societies. All these factors remain in place as we move ...
... technological device or method that allowed us to increase the effectiveness and sophistication of cyber defensive and offensive actions, but also as a social factor which borders with the political, legal, moral and ethical framework of modern societies. All these factors remain in place as we move ...
Internet-Based Workflow Management
... the process; the other aspect covers the infrastructure for handling individual cases. The first problem is typically addressed by domain experts, individuals trained in business, science, engineering, health care, and so on. The second problem can only be handled by individuals who have some unders ...
... the process; the other aspect covers the infrastructure for handling individual cases. The first problem is typically addressed by domain experts, individuals trained in business, science, engineering, health care, and so on. The second problem can only be handled by individuals who have some unders ...
HOW TO BECOME THE WORLD`S NO .1 HACKER
... Every day, we hear and see in the news about constant cyber attacks, where hackers have stolen identities, taken millions of dollars, or even shut down websites and companies in their entirety. The reason why hacking will never die is because we hire IT-Managers, who are not hackers, to protect our ...
... Every day, we hear and see in the news about constant cyber attacks, where hackers have stolen identities, taken millions of dollars, or even shut down websites and companies in their entirety. The reason why hacking will never die is because we hire IT-Managers, who are not hackers, to protect our ...
Mastering Kali Linux for Advanced Penetration Testing
... on live and recorded streaming, how a hacker could break into almost any company with a fake LinkedIn request. You can view this video on his YouTube channel. Terry has been delivering Internet safety for children, parents, and law enforcement since 2006. He believes that prevention, street proofing ...
... on live and recorded streaming, how a hacker could break into almost any company with a fake LinkedIn request. You can view this video on his YouTube channel. Terry has been delivering Internet safety for children, parents, and law enforcement since 2006. He believes that prevention, street proofing ...
Windows Peer-to-Peer Network Configuration Guide
... pointers. Since these pointers reside on the server, they are the same for every workstation accessing Pathways on the network. Consequently, the installation of Pathways must be done to a commonly mapped network drive on the server. In a peer-to-peer network configuration, each workstation has the ...
... pointers. Since these pointers reside on the server, they are the same for every workstation accessing Pathways on the network. Consequently, the installation of Pathways must be done to a commonly mapped network drive on the server. In a peer-to-peer network configuration, each workstation has the ...
Lecture 16: TCP/IP Vulnerabilities and DoS Attacks
... • This 7-layer model of the protocols is referred to as the OSI (Open Systems Interconnection) model. In the literature on computer networks, you’ll also see an older 4-layer model in which the Application Layer is a combination of the top three layers of the OSI model. That is, the Application Laye ...
... • This 7-layer model of the protocols is referred to as the OSI (Open Systems Interconnection) model. In the literature on computer networks, you’ll also see an older 4-layer model in which the Application Layer is a combination of the top three layers of the OSI model. That is, the Application Laye ...
Security Warrior
... malicious code, unveiling corporate spyware, and extracting application vulnerabilities, but until this book it has received sparse coverage in the printed literature. This book is not married to a particular operating system, since many of you are responsible for protecting mixed networks. We have ...
... malicious code, unveiling corporate spyware, and extracting application vulnerabilities, but until this book it has received sparse coverage in the printed literature. This book is not married to a particular operating system, since many of you are responsible for protecting mixed networks. We have ...
Microsoft Computer Dictionary, Fifth Edition eBook
... $0.02 n. See my two cents. & n. 1. UNIX command suffix for running the preceding command as a background process. See also background1. 2. In UNIX, a root user command suffix for starting a daemon that is to remain running after logout. See also daemon. 3. The default character used to designate a c ...
... $0.02 n. See my two cents. & n. 1. UNIX command suffix for running the preceding command as a background process. See also background1. 2. In UNIX, a root user command suffix for starting a daemon that is to remain running after logout. See also daemon. 3. The default character used to designate a c ...
Contents - Norton Audio
... bond portfolios online, use the facilities of a price-comparison Web site prior to initiating a work-related purchase, check the latest results of their favorite sports team, examine weather predictions for a possible vacation getaway, and perhaps even book airfare, hotel, and a car rental online. A ...
... bond portfolios online, use the facilities of a price-comparison Web site prior to initiating a work-related purchase, check the latest results of their favorite sports team, examine weather predictions for a possible vacation getaway, and perhaps even book airfare, hotel, and a car rental online. A ...
McAfee Wireless Home Network Security Suite
... Cryptographic software written by Eric A. Young and software written by Tim J. Hudson. Some software programs that are licensed (or sublicensed) to the user under the GNU General Public License (GPL) or other similar Free Software licenses which, among other rights, permit the user to copy, modify a ...
... Cryptographic software written by Eric A. Young and software written by Tim J. Hudson. Some software programs that are licensed (or sublicensed) to the user under the GNU General Public License (GPL) or other similar Free Software licenses which, among other rights, permit the user to copy, modify a ...
INFORMATION TECHNOLOGY
... time they need to transfer data between main memory and the cache. This tends to improve the chance of a cache hit as most programs spend their time stepping through instructions stored sequentially in memory rather than jumping about from one area to another. The amount of data transferred each tim ...
... time they need to transfer data between main memory and the cache. This tends to improve the chance of a cache hit as most programs spend their time stepping through instructions stored sequentially in memory rather than jumping about from one area to another. The amount of data transferred each tim ...
Windows-2000 and system Administration
... condition of the line changes. This is equal to bits per second only if each signal corresponds to one bit of transmitted data. Modems must operate at the same baud rate in order to communicate with each other. If the baud rate of one modem is set higher than that of the other, the faster modem usua ...
... condition of the line changes. This is equal to bits per second only if each signal corresponds to one bit of transmitted data. Modems must operate at the same baud rate in order to communicate with each other. If the baud rate of one modem is set higher than that of the other, the faster modem usua ...
Windows 7 Advanced Training Manual
... The Control Panel contains an address bar and search box like many other folders. The different commands are categorized into eight groups: ...
... The Control Panel contains an address bar and search box like many other folders. The different commands are categorized into eight groups: ...
information security management – a new decade
... Wireless WANs use cellular networks for data transmission and examples of the cellular systems that are used are: CDMA, GSM, GPRS and CDPD. A portable computer with a wireless WAN modem connects to a base station on the wireless networks via radio waves. The radio tower then carries the signal to a ...
... Wireless WANs use cellular networks for data transmission and examples of the cellular systems that are used are: CDMA, GSM, GPRS and CDPD. A portable computer with a wireless WAN modem connects to a base station on the wireless networks via radio waves. The radio tower then carries the signal to a ...
I accidentally malware - NATO Cooperative Cyber Defence
... sources. Users are from public relations (PR), human resource management (HR) and from other posts exposed to public. It is assumed that devices used by such users are more likely to get infected at some point than devices used by normal employees, so additional protection techniques are required. T ...
... sources. Users are from public relations (PR), human resource management (HR) and from other posts exposed to public. It is assumed that devices used by such users are more likely to get infected at some point than devices used by normal employees, so additional protection techniques are required. T ...
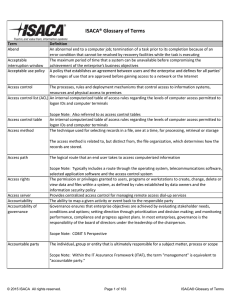
ISACA® Glossary of Terms
... Locations and infrastructures from which emergency or backup processes are executed, when the main premises are unavailable or destroyed Scope Note: Includes other buildings, offices or data processing centers Automatic or manual process designed and established to continue critical business proce ...
... Locations and infrastructures from which emergency or backup processes are executed, when the main premises are unavailable or destroyed Scope Note: Includes other buildings, offices or data processing centers Automatic or manual process designed and established to continue critical business proce ...
Diskeeper Administrator 9 User`s Manual
... tradition with even more innovative new features and approaches to solving fragmentation problems for everyone, from home users to the world’s largest enterprise IT departments. The Diskeeper family of products includes Diskeeper Administrator Edition. Diskeeper Administrator Edition is not a defrag ...
... tradition with even more innovative new features and approaches to solving fragmentation problems for everyone, from home users to the world’s largest enterprise IT departments. The Diskeeper family of products includes Diskeeper Administrator Edition. Diskeeper Administrator Edition is not a defrag ...