HP Intelligent Management Center v7.1 Basic Getting Started Guide
... delivered by HP. Focusing on service management, IMC Basic manages the resources, users, and services of a network to provide you with a total solution for end-to-end resource management, user management, and service management. ...
... delivered by HP. Focusing on service management, IMC Basic manages the resources, users, and services of a network to provide you with a total solution for end-to-end resource management, user management, and service management. ...
EE579T-Class 4
... Curious Public Key Properties • The encryption function is one-way • The encryption process is fungible – Can encrypt with public key and decrypt with private key, and vice versa ...
... Curious Public Key Properties • The encryption function is one-way • The encryption process is fungible – Can encrypt with public key and decrypt with private key, and vice versa ...
Attestation
... Why can’t attacker disable TPM until after boot, then extend PCRs with whatever he wants? Root of trust: BIOS boot block. Gaping hole: role-back attack on encrypted blobs e.g. undo security patches without being noticed. Can be mitigated using Data Integrity Regs (DIR) ...
... Why can’t attacker disable TPM until after boot, then extend PCRs with whatever he wants? Root of trust: BIOS boot block. Gaping hole: role-back attack on encrypted blobs e.g. undo security patches without being noticed. Can be mitigated using Data Integrity Regs (DIR) ...
feb05_eap_usage
... – Problem to solve is “bootstrapping” – This is about how to (a) find a home agent and (b) set up a security association with it so that the mobile node can use the home agent’s services – Want to avoid deployment problem of yet another configuration and secret just because you want to be mobile – O ...
... – Problem to solve is “bootstrapping” – This is about how to (a) find a home agent and (b) set up a security association with it so that the mobile node can use the home agent’s services – Want to avoid deployment problem of yet another configuration and secret just because you want to be mobile – O ...
slides [pdf]
... 1. “Security: The ideal TC only attests certified platform configurations.” 2. “Accountability: Although the TTP has to be trusted by all participants, it is desirable to be able to detect TTP's misbehavior.” 3. “Revokeability: The TTP should be able to selectively revoke TCG versions and TCG realiz ...
... 1. “Security: The ideal TC only attests certified platform configurations.” 2. “Accountability: Although the TTP has to be trusted by all participants, it is desirable to be able to detect TTP's misbehavior.” 3. “Revokeability: The TTP should be able to selectively revoke TCG versions and TCG realiz ...
LogMeIn Security – an In-Depth Look
... installing a remote access product. Remote access products are perceived as high risk factors, but mainly for psychological reasons. When a user first sees a remote access solution in action, their first negative reaction is usually with regard to the security implications. This is perfectly normal, ...
... installing a remote access product. Remote access products are perceived as high risk factors, but mainly for psychological reasons. When a user first sees a remote access solution in action, their first negative reaction is usually with regard to the security implications. This is perfectly normal, ...
Chapter 10
... – E-mail message attachment (program) embedded in Web page – Verifies sender or Web site – Contains a means to send encrypted message – Signed message or code • Provides proof that holder is person identified by the certificate ...
... – E-mail message attachment (program) embedded in Web page – Verifies sender or Web site – Contains a means to send encrypted message – Signed message or code • Provides proof that holder is person identified by the certificate ...
Introduction (cont.)
... autonomously and automatically. The term is most commonly associated with malicious software. Main motivation: recognition and financial gain. Bot controller can ‘rent’ services of the botnet to third parties (Botnet as service) ...
... autonomously and automatically. The term is most commonly associated with malicious software. Main motivation: recognition and financial gain. Bot controller can ‘rent’ services of the botnet to third parties (Botnet as service) ...
CH10
... – Number: usually long binary number • Used with encryption algorithm • “Lock” message characters being protected ...
... – Number: usually long binary number • Used with encryption algorithm • “Lock” message characters being protected ...
Slide 1
... • Domain and forest functional levels are new features of Windows Server 2008. – The levels defined for each of these are based on the type of server operating systems that are required by the Active Directory design. – The Windows Server 2003 forest functional level is the highest functional level ...
... • Domain and forest functional levels are new features of Windows Server 2008. – The levels defined for each of these are based on the type of server operating systems that are required by the Active Directory design. – The Windows Server 2003 forest functional level is the highest functional level ...
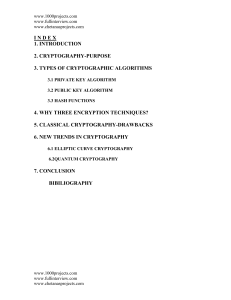
6.1. Elliptic Curve Cryptography
... end uses the receiver to measure the polarisation. According to the laws of quantum mechanics, the receiver can distinguish between rectilinear polarisations (0 and 90), or it can quickly be reconfigured to discriminate between diagonal polarisations (45 and 135); it can never, however, distinguish ...
... end uses the receiver to measure the polarisation. According to the laws of quantum mechanics, the receiver can distinguish between rectilinear polarisations (0 and 90), or it can quickly be reconfigured to discriminate between diagonal polarisations (45 and 135); it can never, however, distinguish ...
Guidance on the Use of E-Mail when Sending Person
... Guidance on the Use of E-Mail when Sending Person Identifiable or Confidential Information This guidance supplements the Email Policy; all NUH staff should be familiar with the provisions of the Email Policy and should not take this guidance in isolation. ...
... Guidance on the Use of E-Mail when Sending Person Identifiable or Confidential Information This guidance supplements the Email Policy; all NUH staff should be familiar with the provisions of the Email Policy and should not take this guidance in isolation. ...
CN 2015 5 - SNGCE DIGITAL LIBRARY
... In case of the steal of a user’s private key, only the msgs sent to that user are involved Better authentication mechanisms than symmetric systems ...
... In case of the steal of a user’s private key, only the msgs sent to that user are involved Better authentication mechanisms than symmetric systems ...
CGI Programming: Part 2 Robert M. Dondero, Ph.D. Princeton University 1
... Doesn't know previous author ...
... Doesn't know previous author ...
Security Analysis of a Single Sign
... The malicious and then mount the above attack. On the one hand, the Chang–Lee SSO scheme specifies that is the trusted party. So, this implies that service providers are not trusted parties and that they could be malicious. By agreeing with, when they said that “the Wu–Hsu’s modified version cold no ...
... The malicious and then mount the above attack. On the one hand, the Chang–Lee SSO scheme specifies that is the trusted party. So, this implies that service providers are not trusted parties and that they could be malicious. By agreeing with, when they said that “the Wu–Hsu’s modified version cold no ...
InfoSec Acceptable Use Policy. (nd). SANS Institute. Retrieved from
... “IBM Lotus Notes Traveler before 8.5.1.3, when a multidomain environment is used, does not properly apply policy documents to mobile users from a different Domino domain than the Traveler server, which allows remote authenticated users to bypass intended access restrictions by using credentials from ...
... “IBM Lotus Notes Traveler before 8.5.1.3, when a multidomain environment is used, does not properly apply policy documents to mobile users from a different Domino domain than the Traveler server, which allows remote authenticated users to bypass intended access restrictions by using credentials from ...
Using Digital Signature with DNS
... resource record set with its private keys • Resouce record set: The set of resource records of the same type. • Public KEYs can be used to verify the SIGs • The authenticity of public KEYs is established by a SIGnature over the keys with the parent’s private key • In the ideal case, only one public ...
... resource record set with its private keys • Resouce record set: The set of resource records of the same type. • Public KEYs can be used to verify the SIGs • The authenticity of public KEYs is established by a SIGnature over the keys with the parent’s private key • In the ideal case, only one public ...
EAP
... Was supposed to provide authentication and privacy Secret 40 bit keys, but unsafe at any length Static-manually-configured keys Weakness due to long life of keys and they are shared among many users ...
... Was supposed to provide authentication and privacy Secret 40 bit keys, but unsafe at any length Static-manually-configured keys Weakness due to long life of keys and they are shared among many users ...
Apply encryption to network and system security
... Encryption may be used to protect the confidentiality, integrity and authenticity of data in storage, such as that on a hard disk drive or tape. Encryption methods as discussed previously may be used but careful consideration must be given to the consequence of this. Encrypting and decrypting data c ...
... Encryption may be used to protect the confidentiality, integrity and authenticity of data in storage, such as that on a hard disk drive or tape. Encryption methods as discussed previously may be used but careful consideration must be given to the consequence of this. Encrypting and decrypting data c ...
Chapter 15
... – The name of the holder and other identification information, such as e-mail address – A public key, which can be used to verify the digital signature of a message sender previously signed with the matching mathematically unique private key – The name of the issuer, or Certificate Authority – The c ...
... – The name of the holder and other identification information, such as e-mail address – A public key, which can be used to verify the digital signature of a message sender previously signed with the matching mathematically unique private key – The name of the issuer, or Certificate Authority – The c ...
Liberty Games
... Symantec Norton Secured Seal also increased e-commerce conversion rate by 22.7 percent and grew the number of unique purchases by over 20 percent. Liberty Games also ran tests on the sites with the Norton Secured Seal, and has seen increased conversion rates since it was added. Also, Liberty Games r ...
... Symantec Norton Secured Seal also increased e-commerce conversion rate by 22.7 percent and grew the number of unique purchases by over 20 percent. Liberty Games also ran tests on the sites with the Norton Secured Seal, and has seen increased conversion rates since it was added. Also, Liberty Games r ...
document
... that to provide remote access service, VPN clients need only call into the nearest service provider's access point. In some cases this may require a long distance call, but in many cases a local call will suffice. ...
... that to provide remote access service, VPN clients need only call into the nearest service provider's access point. In some cases this may require a long distance call, but in many cases a local call will suffice. ...
![slides [pdf]](http://s1.studyres.com/store/data/003737230_1-2696b7865b4160afff3b6862ae017bef-300x300.png)