NBBD Overview Presentation
... Once the account validation steps are complete, a repository record and a Direct account are provisioned for the registrant’s organization and an invoice is presented to complete activation (this is for demonstration purposes only – many sustainability models may be supported). ...
... Once the account validation steps are complete, a repository record and a Direct account are provisioned for the registrant’s organization and an invoice is presented to complete activation (this is for demonstration purposes only – many sustainability models may be supported). ...
Principals of Information Security, Fourth Edition
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
AISE PoIS4E_PP_ch02_48
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
Data mining tools - Cal State LA
... DBMS engine - accepts logical requests from the various other DBMS subsystems, converts them into their physical equivalent, and actually accesses the database and data dictionary as they exist on a storage device. ...
... DBMS engine - accepts logical requests from the various other DBMS subsystems, converts them into their physical equivalent, and actually accesses the database and data dictionary as they exist on a storage device. ...
Chapter 2
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
Chapter 2
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
Deleting POM Campaign Cause Report Data Associated with this
... When user deletes a POM campaign, all data records associated with this campaign would be removed from POM tables. They are no longer available in any POM report. In current POM design, when user deletes POM campaign, a popup box will display the message “Are you sure you want to delete this Campaig ...
... When user deletes a POM campaign, all data records associated with this campaign would be removed from POM tables. They are no longer available in any POM report. In current POM design, when user deletes POM campaign, a popup box will display the message “Are you sure you want to delete this Campaig ...
nar vow policy - The Globe and Mail
... What records must be kept? Members must maintain a record of the consumer’s name, email address, username and password for at least 180 days after password expiry, and maintain an audit trail of consumer activity on the VOW. These may be requested by TREB if a security breach or violation of MLS® an ...
... What records must be kept? Members must maintain a record of the consumer’s name, email address, username and password for at least 180 days after password expiry, and maintain an audit trail of consumer activity on the VOW. These may be requested by TREB if a security breach or violation of MLS® an ...
HIPAA Training - University of South Florida
... HIPAA stands for the Health Insurance Portability and Accountability Act. Congress passed HIPAA in 1996 to make health insurance eligibility “portable” from one employer to the next when employees change jobs or have a change in family status. Congress passed HITECH in 2005 significantly affec ...
... HIPAA stands for the Health Insurance Portability and Accountability Act. Congress passed HIPAA in 1996 to make health insurance eligibility “portable” from one employer to the next when employees change jobs or have a change in family status. Congress passed HITECH in 2005 significantly affec ...
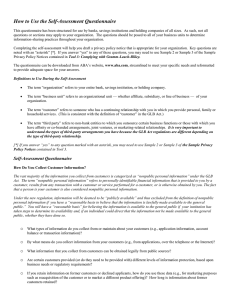
Self-Assessment Questionnaire
... There are important exceptions to this general rule, such as if the third party is performing services or functions on your behalf, including marketing your own products or services or products and services offered pursuant to a joint marketing agreement (see Tool 3’s Exceptions to the Opt Out Provi ...
... There are important exceptions to this general rule, such as if the third party is performing services or functions on your behalf, including marketing your own products or services or products and services offered pursuant to a joint marketing agreement (see Tool 3’s Exceptions to the Opt Out Provi ...
ch02
... Organizations must have secure infrastructure services based on size and scope of enterprise Additional security services may be needed as organization expands More robust solutions may be needed to replace security programs the organization has outgrown ...
... Organizations must have secure infrastructure services based on size and scope of enterprise Additional security services may be needed as organization expands More robust solutions may be needed to replace security programs the organization has outgrown ...
evesecures9
... Health providers is subject to civil & criminal penalties if they violate the patients’ rights under HIPAA. Up to $25,000 for multiple violations for the same standard in a calendar year. Up to $250,000 and/or 10 years in jail, if knowing any misuse of patients’ information. ...
... Health providers is subject to civil & criminal penalties if they violate the patients’ rights under HIPAA. Up to $25,000 for multiple violations for the same standard in a calendar year. Up to $250,000 and/or 10 years in jail, if knowing any misuse of patients’ information. ...
Introduction to Information Security Chapter N
... Broad category of activities that breach confidentiality – Unauthorized accessing of information – Competitive intelligence (the legal and ethical collection and analysis of information regarding the capabilities, vulnerabilities, and intentions of business competitors) vs. espionage – Shoulder su ...
... Broad category of activities that breach confidentiality – Unauthorized accessing of information – Competitive intelligence (the legal and ethical collection and analysis of information regarding the capabilities, vulnerabilities, and intentions of business competitors) vs. espionage – Shoulder su ...
Computer Security, Ethics, and Privacy
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts computer access to an Internet service such as the Web or e-mail ...
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts computer access to an Internet service such as the Web or e-mail ...
Text S1.
... The ELISA system developed in Visual Basic 6.0 consists of the automatization of the ELISA techniques in the Virology Laboratory. Each user is validated using passwords, and the system permits the use of multiple readers. In the ELISA system, the technician uses a 2D barcode scanner to generate the ...
... The ELISA system developed in Visual Basic 6.0 consists of the automatization of the ELISA techniques in the Virology Laboratory. Each user is validated using passwords, and the system permits the use of multiple readers. In the ELISA system, the technician uses a 2D barcode scanner to generate the ...
Principals of Information Security, Fourth Edition
... information not determined to be matter of national security • U.S. government agencies are required to disclose any requested information upon receipt of written request. • Some information is protected from disclosure; this act does not apply to state/local government agencies or private businesse ...
... information not determined to be matter of national security • U.S. government agencies are required to disclose any requested information upon receipt of written request. • Some information is protected from disclosure; this act does not apply to state/local government agencies or private businesse ...
Don`t Wait for the Breach to Plan Your Reaction
... Sector-specific federal privacy and data protection laws. Most states require that “reasonable information security measures” be used. – Protect information from unauthorized access, destruction, use, modification and disclosure. – Use reasonable records retention/destruction procedures. ...
... Sector-specific federal privacy and data protection laws. Most states require that “reasonable information security measures” be used. – Protect information from unauthorized access, destruction, use, modification and disclosure. – Use reasonable records retention/destruction procedures. ...
Presentation
... •What actuators does the robot possess? •What communication protocols does the robot support? •Who are the intended users of the robot? •What is the robot’s intended operational environment? •Besides the intended users of the robot, what other people (and animals) will be in the robot’s environment? ...
... •What actuators does the robot possess? •What communication protocols does the robot support? •Who are the intended users of the robot? •What is the robot’s intended operational environment? •Besides the intended users of the robot, what other people (and animals) will be in the robot’s environment? ...
ch02kc
... Protecting Data that Organizations Collect and Use Organization, without data, loses its record of transactions and/or ability to deliver value to customers Protecting data in motion and data at rest both critical aspects of information security ...
... Protecting Data that Organizations Collect and Use Organization, without data, loses its record of transactions and/or ability to deliver value to customers Protecting data in motion and data at rest both critical aspects of information security ...
Arizona Education Technology Standards
... A privacy policy is a written statement detailing how an entity handles personal information gathered. Purpose: Federal laws such as FERPA and COPPA (www.ed.gov/policy/gen/guid/fpco/ferpa and http://www.ftc.gov/kidzprivacy) are in place to regulate the use of private information in schools. As new t ...
... A privacy policy is a written statement detailing how an entity handles personal information gathered. Purpose: Federal laws such as FERPA and COPPA (www.ed.gov/policy/gen/guid/fpco/ferpa and http://www.ftc.gov/kidzprivacy) are in place to regulate the use of private information in schools. As new t ...
Introduction
... resources, the purpose of which is to 1 achieve and sustain a known secure system state at all times, and 2 prevent accidental or intentional theft, release, destruction, alteration, misuse, or sabotage of system resources.” Are these domains purely defensive, or might they be offensive? Compare and ...
... resources, the purpose of which is to 1 achieve and sustain a known secure system state at all times, and 2 prevent accidental or intentional theft, release, destruction, alteration, misuse, or sabotage of system resources.” Are these domains purely defensive, or might they be offensive? Compare and ...
Development of Tools for Medical Teleconsultations
... this alternative marketing and distribution channel. Health related e-commerce encompasses other products, including health insurance and business-to-business services. The article concentrates on the second segment of telemedicine – connectivity and communications – presenting its evolution from si ...
... this alternative marketing and distribution channel. Health related e-commerce encompasses other products, including health insurance and business-to-business services. The article concentrates on the second segment of telemedicine – connectivity and communications – presenting its evolution from si ...
MLT-1109 - Epcc.edu
... A to Z [Ebsco | Off-campus access] Alphabetical and subject listing of online periodical titles. Indicates what databases have full-text coverage. Academic Search Complete [Full Text | Ebsco | Off-campus access] Provides full-text for 4,600 scholarly publications covering academic areas of study inc ...
... A to Z [Ebsco | Off-campus access] Alphabetical and subject listing of online periodical titles. Indicates what databases have full-text coverage. Academic Search Complete [Full Text | Ebsco | Off-campus access] Provides full-text for 4,600 scholarly publications covering academic areas of study inc ...
Information Security Policy
... document in its entirety and sign the form confirming they have read and understand this policy fully. This document will be reviewed and updated by Management on an annual basis or when relevant to include newly developed security standards into the policy and distribute it all employees and contra ...
... document in its entirety and sign the form confirming they have read and understand this policy fully. This document will be reviewed and updated by Management on an annual basis or when relevant to include newly developed security standards into the policy and distribute it all employees and contra ...
The Need for Information Loss Metrics in Visualization
... and validation of the established techniques. While we have seen a steadily increasing amount of interest in the real-world about the applicability of different visualization techniques, there is a dearth of metrics that would help in creating a baseline that can be used for comparison among them. T ...
... and validation of the established techniques. While we have seen a steadily increasing amount of interest in the real-world about the applicability of different visualization techniques, there is a dearth of metrics that would help in creating a baseline that can be used for comparison among them. T ...
Medical privacy

Medical privacy or health privacy is the practice of keeping information about a patient confidential. This involves both conversational discretion on the part of health care providers, and the security of medical records. The terms can also refer to the physical privacy of patients from other patients and providers while in a medical facility. Modern concerns include the degree of disclosure to insurance companies, employers, and other third parties. The advent of electronic medical records has raised new concerns about privacy, balanced with efforts to reduce duplication of services and medical errors.