Presentation Title
... to prepare for major risks; suggesting such measures to President and Corporate ...
... to prepare for major risks; suggesting such measures to President and Corporate ...
Confidentiality
... The five main phases of an information security plan are as follows; 2.1 Inspection - The most important tasks in developing an Information Security Plan are identifying the key corporate functions, the capabilities they need, when they need those capabilities, and how they interact with other funct ...
... The five main phases of an information security plan are as follows; 2.1 Inspection - The most important tasks in developing an Information Security Plan are identifying the key corporate functions, the capabilities they need, when they need those capabilities, and how they interact with other funct ...
Event Title - Microsoft Center
... © 2010 Microsoft Corporation. All rights reserved. Microsoft, Windows, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries. The information herein is for informational purposes only and represents the current view of Micros ...
... © 2010 Microsoft Corporation. All rights reserved. Microsoft, Windows, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries. The information herein is for informational purposes only and represents the current view of Micros ...
ICT Security
... emails, protects against phishing and provides a firewall. Organisations will need to decide how much of this protection is done centrally or on each individual PC. Laptops that are used outside of the organisation’s premises should have the highest level of protection installed. Again, these issues ...
... emails, protects against phishing and provides a firewall. Organisations will need to decide how much of this protection is done centrally or on each individual PC. Laptops that are used outside of the organisation’s premises should have the highest level of protection installed. Again, these issues ...
Chapter 2 - Department of Accounting and Information Systems
... of requests is launched against target from many ...
... of requests is launched against target from many ...
Discovering Computers 2008
... How can you protect your system from a macro virus? Set macro security level in applications that allow you to write macros Set security level so that warning displays that document contains macro ...
... How can you protect your system from a macro virus? Set macro security level in applications that allow you to write macros Set security level so that warning displays that document contains macro ...
Internet and Network Attacks
... How can you protect your system from a macro virus? Set macro security level in applications that allow you to write macros Set security level so that warning displays that document contains macro ...
... How can you protect your system from a macro virus? Set macro security level in applications that allow you to write macros Set security level so that warning displays that document contains macro ...
Hyundai Department Store Group
... Reducing Potential Data Security Risks by 70 Percent with Solutions from Symantec Hyundai Department Store Group needed to comply with the South Korean Personal Information Protection Act and put customers at ease that their personal information would be protected. It turned to a data loss preventio ...
... Reducing Potential Data Security Risks by 70 Percent with Solutions from Symantec Hyundai Department Store Group needed to comply with the South Korean Personal Information Protection Act and put customers at ease that their personal information would be protected. It turned to a data loss preventio ...
Lecture 1 - The University of Texas at Dallas
... data has to be fused, aggregated and perhaps mined in real-time Research on secure dependable information management for sensor ...
... data has to be fused, aggregated and perhaps mined in real-time Research on secure dependable information management for sensor ...
Guidelines at a Glance - American Bankers Association
... establish an information security program. These guidelines are separate and apart from the privacy regulations and notice requirements contained in Section 501 of GLBA. A bank’s information security program must be designed to ensure the security and confidentiality of customer information, protect ...
... establish an information security program. These guidelines are separate and apart from the privacy regulations and notice requirements contained in Section 501 of GLBA. A bank’s information security program must be designed to ensure the security and confidentiality of customer information, protect ...
Introduction to Healthcare Information Technology
... • Asymmetric cryptography uses two keys: a public and a private key • Cryptography can be applied through hardware or software • Encryption can protect data that is stored or being transmitted across a network Introduction to Healthcare Information Technology ...
... • Asymmetric cryptography uses two keys: a public and a private key • Cryptography can be applied through hardware or software • Encryption can protect data that is stored or being transmitted across a network Introduction to Healthcare Information Technology ...
PowerPoint Slides
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts computer access to an Internet service such as the Web or e-mail ...
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts computer access to an Internet service such as the Web or e-mail ...
MYDIGIPASS for Healthcare
... aXsGUARD®, DIGIPASS ® and logo are registered or unregistered trademarks of VASCO Data Security, Inc. and/or VASCO Data Security International GmbH in the U.S. and other countries. VASCO Data Security, Inc. and/or VASCO Data Security International GmbH own or are licensed under all title, rights and ...
... aXsGUARD®, DIGIPASS ® and logo are registered or unregistered trademarks of VASCO Data Security, Inc. and/or VASCO Data Security International GmbH in the U.S. and other countries. VASCO Data Security, Inc. and/or VASCO Data Security International GmbH own or are licensed under all title, rights and ...
Privacy Policy - Dickey`s Barbecue Pit
... transactions completed using cookies and tags. Additionally, this information is used to better serve you with appropriate and relevant marketing offers. Cookies are small files that your Web browser places on your computer’s hard drive. Cookies are not used to access information entered on the sec ...
... transactions completed using cookies and tags. Additionally, this information is used to better serve you with appropriate and relevant marketing offers. Cookies are small files that your Web browser places on your computer’s hard drive. Cookies are not used to access information entered on the sec ...
Introduction to Information Security
... Security professionals: Dedicated, trained, and well-educated specialists in all aspects of information security, both technical and nontechnical. Systems, networks, and storage administrators: Individuals with the primary responsibility for administering the systems, storage, and networks that hous ...
... Security professionals: Dedicated, trained, and well-educated specialists in all aspects of information security, both technical and nontechnical. Systems, networks, and storage administrators: Individuals with the primary responsibility for administering the systems, storage, and networks that hous ...
data extraction from medical records
... The SEASCALE HEALTH CENTRE Practice & its Doctors & Staff, working as part of the NHS, need and want to share data in various ways but we also want to protect your confidential and personal information. Data about health can be used for various reasons, both internally within the practice, and exter ...
... The SEASCALE HEALTH CENTRE Practice & its Doctors & Staff, working as part of the NHS, need and want to share data in various ways but we also want to protect your confidential and personal information. Data about health can be used for various reasons, both internally within the practice, and exter ...
What is Trusted Computing and Digital Rights Management
... today. TC hardware can be useful to governments by guaranteeing that their machines have not been tampered with or to prevent unauthorised access to stolen machines. Digital Rights Management (DRM) software provides a way for information providers to control access to information while making it ava ...
... today. TC hardware can be useful to governments by guaranteeing that their machines have not been tampered with or to prevent unauthorised access to stolen machines. Digital Rights Management (DRM) software provides a way for information providers to control access to information while making it ava ...
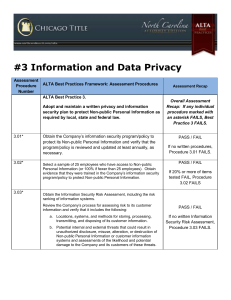
ALTA Assessment Procedures
... Obtain and review written policies and procedures to verify logical access to information systems (i.e., network, data base, and application layers) containing Non-public Personal Information is restricted to authorized persons only. a. For the sample of employees tested in Assessment Procedure 3.02 ...
... Obtain and review written policies and procedures to verify logical access to information systems (i.e., network, data base, and application layers) containing Non-public Personal Information is restricted to authorized persons only. a. For the sample of employees tested in Assessment Procedure 3.02 ...
Threats and Attacks
... § Forces of nature are among the most dangerous threats § Disrupt not only individual lives, but also storage, transmission, and use of information § Organizations must implement controls to limit damage and prepare contingency plans for continued operations ...
... § Forces of nature are among the most dangerous threats § Disrupt not only individual lives, but also storage, transmission, and use of information § Organizations must implement controls to limit damage and prepare contingency plans for continued operations ...
Data Governance Policy
... on a case-by-case basis, permissions may be added in to those already held by individual users in the student management system, again on a need-to-know basis and only in order to fulfill specific job responsibilities, with approval of the Data Governance Committee. ...
... on a case-by-case basis, permissions may be added in to those already held by individual users in the student management system, again on a need-to-know basis and only in order to fulfill specific job responsibilities, with approval of the Data Governance Committee. ...
US SAFE WEB Act - Higher Education Compliance Alliance
... powers. The main benefit was adding language which allows the FTC to collaborate with foreign agencies. Although there may be examples of where the FTC has collaborated with foreign agencies, this report is limited to the FTC’s use of existing laws (FTC Act and US SAFE WEB Act) to begin exerting aut ...
... powers. The main benefit was adding language which allows the FTC to collaborate with foreign agencies. Although there may be examples of where the FTC has collaborated with foreign agencies, this report is limited to the FTC’s use of existing laws (FTC Act and US SAFE WEB Act) to begin exerting aut ...
What Is Needed for True Population Health
... Most organizations face similar issues around data management, data quality, and timeliness of data. The first challenge might simply be getting access to the data, whether it’s because of data silos, protected health information (PHI) concerns, or the EHR is more like a locked bank vault when it co ...
... Most organizations face similar issues around data management, data quality, and timeliness of data. The first challenge might simply be getting access to the data, whether it’s because of data silos, protected health information (PHI) concerns, or the EHR is more like a locked bank vault when it co ...
Information Privacy What is information privacy?
... Internet and Network Attacks What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
... Internet and Network Attacks What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
Medical privacy

Medical privacy or health privacy is the practice of keeping information about a patient confidential. This involves both conversational discretion on the part of health care providers, and the security of medical records. The terms can also refer to the physical privacy of patients from other patients and providers while in a medical facility. Modern concerns include the degree of disclosure to insurance companies, employers, and other third parties. The advent of electronic medical records has raised new concerns about privacy, balanced with efforts to reduce duplication of services and medical errors.