Ch 4 DSS Case study 6
... STC needed to identify the relevant metrics, properly visualize them, and provide them to the right people, often with time-sensitive information. But executives didn’t have the ability to see key performance indicators in a timely fashion. They would have to contact the technical teams to get statu ...
... STC needed to identify the relevant metrics, properly visualize them, and provide them to the right people, often with time-sensitive information. But executives didn’t have the ability to see key performance indicators in a timely fashion. They would have to contact the technical teams to get statu ...
Safety (MSDS) data for acid blue 9
... Stable. Incompatible with strong oxidizing agents. Toxicology May act as a skin, respiratory or eye irritant. Toxicity data (The meaning of any toxicological abbreviations which appear in this section is given here.) SCN-MUS LD50 4600 mg kg-1 Transport information Non-hazardous for air, sea and road ...
... Stable. Incompatible with strong oxidizing agents. Toxicology May act as a skin, respiratory or eye irritant. Toxicity data (The meaning of any toxicological abbreviations which appear in this section is given here.) SCN-MUS LD50 4600 mg kg-1 Transport information Non-hazardous for air, sea and road ...
BEST BEGINNINGS, LLC PRIVACY POLICY
... comply with our privacy policies and not use your personal data for any other purpose. Apart from this, we disclose personal information only when we have a good faith belief that access, use, preservation or disclosure of such information is reasonably necessary to (a) satisfy any applicable law, r ...
... comply with our privacy policies and not use your personal data for any other purpose. Apart from this, we disclose personal information only when we have a good faith belief that access, use, preservation or disclosure of such information is reasonably necessary to (a) satisfy any applicable law, r ...
Introduction - Personal Web Pages
... • Data mining attacks on public database – In Tenn, a newspaper generates a database about all residents that have CCW permits. – In CA, there is a webpage listing all people that donate to Proposition 8 ballot measure ...
... • Data mining attacks on public database – In Tenn, a newspaper generates a database about all residents that have CCW permits. – In CA, there is a webpage listing all people that donate to Proposition 8 ballot measure ...
Theme Paper none: Functions and Responsibilities
... to prevent prejudice to the supply of similar information, or information from the same source, and it is in the public interest that such information should continue to be supplied to protect information which is subject to an obligation of confidence or which any person has been or could be compel ...
... to prevent prejudice to the supply of similar information, or information from the same source, and it is in the public interest that such information should continue to be supplied to protect information which is subject to an obligation of confidence or which any person has been or could be compel ...
Slides Group 1 - Department of Information Technology
... • Normative privacy-protected by ethical, legal conventional norms • Normative privacy often natural as well ...
... • Normative privacy-protected by ethical, legal conventional norms • Normative privacy often natural as well ...
Acquire foundational knowledge of marketing
... Acquire foundational knowledge of marketing information management to understand its nature & scope ...
... Acquire foundational knowledge of marketing information management to understand its nature & scope ...
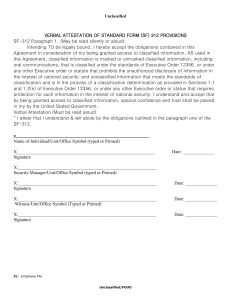
Verbal Attestation of Standard form SF
... SF-312 Paragraph 1. (May be read silently or aloud): Intending TO be legally bound, I hereby accept the obligations contained in this Agreement in consideration of my being granted access to classified information. AS used in this Agreement, classified information is marked or unmarked classified in ...
... SF-312 Paragraph 1. (May be read silently or aloud): Intending TO be legally bound, I hereby accept the obligations contained in this Agreement in consideration of my being granted access to classified information. AS used in this Agreement, classified information is marked or unmarked classified in ...
JRA1.4 AAs in eduGAIN
... ● Permit delegation of the management of user information in a clear and secure way. ● Provide new architectural elements that could seamlessly integrate with existing architectures (to simplify technical adoption of such a solution by all the participants to the federation). ● Leverage the existing ...
... ● Permit delegation of the management of user information in a clear and secure way. ● Provide new architectural elements that could seamlessly integrate with existing architectures (to simplify technical adoption of such a solution by all the participants to the federation). ● Leverage the existing ...
E-Surveillance and User Privacy
... • Balancing user privacy vs. the need for information • encryption – if it is too good then criminals can communicate with impunity ...
... • Balancing user privacy vs. the need for information • encryption – if it is too good then criminals can communicate with impunity ...
Data Analytics for Evidence-based Healthcare (DAEBH 2015)
... Victoria University, Australia Healthcare systems around the world are under great pressure to incorporate evidence-based practices due to the large bodies of medical evidence available and the problems related to determining how the clinical evidence applies to specific cases. These problems are co ...
... Victoria University, Australia Healthcare systems around the world are under great pressure to incorporate evidence-based practices due to the large bodies of medical evidence available and the problems related to determining how the clinical evidence applies to specific cases. These problems are co ...
Industry Landscape: Picture Archiving and Communications
... workflow and administrative processes. This approach has the added benefit of facilitating the creation of a seamless single-point-of-interaction with the entire collection of medical images and data types. However, this process is not without its challenges and risks. This presentation discusses se ...
... workflow and administrative processes. This approach has the added benefit of facilitating the creation of a seamless single-point-of-interaction with the entire collection of medical images and data types. However, this process is not without its challenges and risks. This presentation discusses se ...
USA PATRIOT Act - Landings Credit Union
... In order to prevent the use of the U.S. banking system in terrorist and other illegal activity, federal regulations require all financial institutions to obtain, verify, and record identification from all persons opening new accounts or being added as signatories to existing accounts. Effective Octo ...
... In order to prevent the use of the U.S. banking system in terrorist and other illegal activity, federal regulations require all financial institutions to obtain, verify, and record identification from all persons opening new accounts or being added as signatories to existing accounts. Effective Octo ...
BCS ASSIST Autumn Conference, Manchester 10 October 2012
... • The recent White Paper acknowledges the need to: – “…transform the way information is accessed, collected, analysed and used by the NHS… so that people are at the heart...” – move towards facilitating openness and transparency; to enable patients to be in control of and active participants in thei ...
... • The recent White Paper acknowledges the need to: – “…transform the way information is accessed, collected, analysed and used by the NHS… so that people are at the heart...” – move towards facilitating openness and transparency; to enable patients to be in control of and active participants in thei ...
security_6
... cyber-criminals who use email, popup messages or an imitation or copy of an existing legitimate webpage to trick users into providing sensitive personal information such as credit card numbers, bank account numbers, and passwords. ...
... cyber-criminals who use email, popup messages or an imitation or copy of an existing legitimate webpage to trick users into providing sensitive personal information such as credit card numbers, bank account numbers, and passwords. ...
Czech Republic
... Videosurveillance in the Czech Republic with special regard to privacy and data protection implications of the civil use of drones Jiří Maštalka Sarajevo, 11.5.2016 ...
... Videosurveillance in the Czech Republic with special regard to privacy and data protection implications of the civil use of drones Jiří Maštalka Sarajevo, 11.5.2016 ...
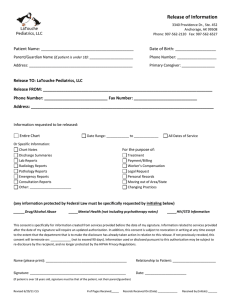
Patient - Snake River Pediatrics
... 1050 SW 3rd Ave, Suite 3200 • Ontario, OR 97914 • (541) 881-2380 • Fax (541)881-2389 Stephen Ames, MD, FAAP • Matthew Berria, PhD, PA-C • Sage Benintendi Stringer, MPAS, PA-C • Michelle DeVoe, DO, FAAP Mary James, MPAS, PA-C • Chelsie Lewis, FNP-C • Kailey Meskill, MPAS, PA-C ...
... 1050 SW 3rd Ave, Suite 3200 • Ontario, OR 97914 • (541) 881-2380 • Fax (541)881-2389 Stephen Ames, MD, FAAP • Matthew Berria, PhD, PA-C • Sage Benintendi Stringer, MPAS, PA-C • Michelle DeVoe, DO, FAAP Mary James, MPAS, PA-C • Chelsie Lewis, FNP-C • Kailey Meskill, MPAS, PA-C ...
Definition of Education Record
... • Student's identification code, • Social security number, • Picture or other information that would make it easy to identify or locate a student. Personal notes made by teachers and other school officials that are not shared with others are not considered education records. Additionally, law enforc ...
... • Student's identification code, • Social security number, • Picture or other information that would make it easy to identify or locate a student. Personal notes made by teachers and other school officials that are not shared with others are not considered education records. Additionally, law enforc ...
Medical privacy

Medical privacy or health privacy is the practice of keeping information about a patient confidential. This involves both conversational discretion on the part of health care providers, and the security of medical records. The terms can also refer to the physical privacy of patients from other patients and providers while in a medical facility. Modern concerns include the degree of disclosure to insurance companies, employers, and other third parties. The advent of electronic medical records has raised new concerns about privacy, balanced with efforts to reduce duplication of services and medical errors.