Logical attack advisory for U.S. and Canada
... Attacks Configuration and Implementation Guidelines Document. Physical Security: These attacks can occur on both front and rear access ATMs. Thus, it is important to consider the environment, and scale the physical security protecting the ATM accordingly. ATMs in unattended public locations are at h ...
... Attacks Configuration and Implementation Guidelines Document. Physical Security: These attacks can occur on both front and rear access ATMs. Thus, it is important to consider the environment, and scale the physical security protecting the ATM accordingly. ATMs in unattended public locations are at h ...
Chapter 10
... Electronic Evidence and Computer Forensics • Electronic Evidence: Computer data stored on disks and drives, e-mail, instant messages, and ecommerce transactions • Computer Forensics: Scientific collection, examination, authentication, preservation, and analysis of computer data for use as evidence i ...
... Electronic Evidence and Computer Forensics • Electronic Evidence: Computer data stored on disks and drives, e-mail, instant messages, and ecommerce transactions • Computer Forensics: Scientific collection, examination, authentication, preservation, and analysis of computer data for use as evidence i ...
Chapter 1
... The attacker attempts to breach a web application. Common attacks of this type are SQL injection and Cross Site Scripting. ...
... The attacker attempts to breach a web application. Common attacks of this type are SQL injection and Cross Site Scripting. ...
Key To Personal Information Security
... (LAN) or Internet run many services that listen at well-known and not so well known ports • By port scanning, the attacker finds which ports are available (i.e., what service might be listing to a port) • A port scan consists of sending a message to each port, one at a time • The kind of response re ...
... (LAN) or Internet run many services that listen at well-known and not so well known ports • By port scanning, the attacker finds which ports are available (i.e., what service might be listing to a port) • A port scan consists of sending a message to each port, one at a time • The kind of response re ...
SetNo11
... Instead, a security system must have layers, making it unlikely that an attacker has the tools and skills to break through all the layers of defenses ...
... Instead, a security system must have layers, making it unlikely that an attacker has the tools and skills to break through all the layers of defenses ...
Internet and Network Attacks
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? Hardware theft is act of stealing computer equipment ...
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? Hardware theft is act of stealing computer equipment ...
Discovering Computers 2008
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? Hardware theft is act of stealing computer equipment ...
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? Hardware theft is act of stealing computer equipment ...
darkhadoop - TutorialsPoint
... with the internet until the sinkhole is removed. A workaround could be that the target gets a different IP, but then you have to think about stuff like DNS TTL expiry and so on…. ...
... with the internet until the sinkhole is removed. A workaround could be that the target gets a different IP, but then you have to think about stuff like DNS TTL expiry and so on…. ...
Internal Networks and Physical Attacks
... Intrusion detection defines network or host monitoring and traffic analysis tools. These permit network operators and security specialists to protect their networks and hosts against unauthorized use. To accomplish this, a network device or software agent is placed on critical segments of the networ ...
... Intrusion detection defines network or host monitoring and traffic analysis tools. These permit network operators and security specialists to protect their networks and hosts against unauthorized use. To accomplish this, a network device or software agent is placed on critical segments of the networ ...
Ethics in Information Technology
... – Are updated with encrypted data every time the card is used – Used widely in Europe – Not widely used in the U.S. ...
... – Are updated with encrypted data every time the card is used – Used widely in Europe – Not widely used in the U.S. ...
Computer Security: Principles and Practice, 1/e
... • Document describes a data model to represent information exported by intrusion detection systems and explains the rationale for using this model • An implementation of the data model in the Extensible Markup Language (XML) is presented, and XML Document Type Definition is developed, and examples a ...
... • Document describes a data model to represent information exported by intrusion detection systems and explains the rationale for using this model • An implementation of the data model in the Extensible Markup Language (XML) is presented, and XML Document Type Definition is developed, and examples a ...
White Hat Hacking Tyler Schumacher Department of Computer
... hired by a company for the sole purpose of attempting to break into a system so that any vulnerabilities could be brought to light and hopefully fixed. White hats can be former black or grey hats, or they can simply be network security specialists. Black hats may become white hats for a number of re ...
... hired by a company for the sole purpose of attempting to break into a system so that any vulnerabilities could be brought to light and hopefully fixed. White hats can be former black or grey hats, or they can simply be network security specialists. Black hats may become white hats for a number of re ...
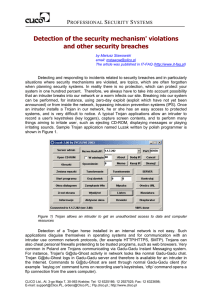
Detection of the security mechanism` violations and other
... log requires that a vendor of a security solution delivers relevant tools. The tools for viewing and sorting logs can help very little for this purpose. On the other hand, generating reports from historical logs usually takes long time, especially when an IPS/IDS system does not have its own databas ...
... log requires that a vendor of a security solution delivers relevant tools. The tools for viewing and sorting logs can help very little for this purpose. On the other hand, generating reports from historical logs usually takes long time, especially when an IPS/IDS system does not have its own databas ...
PowerPoint Slides
... Right to use software Single-user license agreement allows user to install software on one computer, make backup copy, and sell software after removing from computer ...
... Right to use software Single-user license agreement allows user to install software on one computer, make backup copy, and sell software after removing from computer ...
Getting Security Right in Wireless Sensor Networks
... different network to be a coordinator realignment message, which told them to change channels. There was no way for the ZigBee networks to determine that the messages were coming from a device that was not in their network! This disastrous behavior was not the result of an actual attack, but rather ...
... different network to be a coordinator realignment message, which told them to change channels. There was no way for the ZigBee networks to determine that the messages were coming from a device that was not in their network! This disastrous behavior was not the result of an actual attack, but rather ...
Evolve IP - Defense in Depth
... critical network assets, data, systems and users. These defenses are layered for two primary reasons: First, as one layer, device or mechanism fails, another will be there to mitigate, or at least track and notify the administrator, about the breach. Second, as detailed above, attacks can come from ...
... critical network assets, data, systems and users. These defenses are layered for two primary reasons: First, as one layer, device or mechanism fails, another will be there to mitigate, or at least track and notify the administrator, about the breach. Second, as detailed above, attacks can come from ...
Joint Information Environment (JIE)
... - Scalability and flexibility to provide new services - Use of common standards and operational techniques - Transition to a single security architecture • The DOD plans to achieve these goals via the following interrelated initiatives: - Implementation of Joint Regional Security Stack (JRSS) h ...
... - Scalability and flexibility to provide new services - Use of common standards and operational techniques - Transition to a single security architecture • The DOD plans to achieve these goals via the following interrelated initiatives: - Implementation of Joint Regional Security Stack (JRSS) h ...
The Stuxnet Worm: Just Another Computer Attack or a Game
... First, wired and open societies are target-rich environments for cyber-theft, espionage or attack, against which they must protect themselves. ...
... First, wired and open societies are target-rich environments for cyber-theft, espionage or attack, against which they must protect themselves. ...
What is Penetration Testing?
... a malicious source. • The process involves an active analysis of the system for any potential vulnerabilities that may result from poor or improper system configuration, known and/or unknown hardware or software flaws, or operational weaknesses in process or technical countermeasures. • The intent o ...
... a malicious source. • The process involves an active analysis of the system for any potential vulnerabilities that may result from poor or improper system configuration, known and/or unknown hardware or software flaws, or operational weaknesses in process or technical countermeasures. • The intent o ...
TLC_Requirements_TI+AlcatelLucent
... The application of these general requirements for MIT system should enhance overall resilience of all these complex communication Infrastructures. ...
... The application of these general requirements for MIT system should enhance overall resilience of all these complex communication Infrastructures. ...
5th Chapter - information systems and it audit
... • Creates false sense of security • Other entry points, connections direct though Modems • Mis-configuration ...
... • Creates false sense of security • Other entry points, connections direct though Modems • Mis-configuration ...
A Primer on Computer Security
... Corrupted files on victim’s machine – deleted mp3, jpg and other files Searched for active passwords in memory and emailed them to Web site in the ...
... Corrupted files on victim’s machine – deleted mp3, jpg and other files Searched for active passwords in memory and emailed them to Web site in the ...
The Importance of Cybersecurity
... Customers that need some additional guidance can contact a cybersecurity expert who can review their security report and recommend next steps in how to remediate and/or improve their security posture. Cybersecurity experts are available for consultation via phone and/or email for this personalized ...
... Customers that need some additional guidance can contact a cybersecurity expert who can review their security report and recommend next steps in how to remediate and/or improve their security posture. Cybersecurity experts are available for consultation via phone and/or email for this personalized ...
The AIG netAdvantage Suite® Coverage Highlights
... Crisis Communication Fund: Coverage provided up to $50,000 toward the fees and expenses for the insured's public relations crisis arising out of a computer attack. This coverage is provided with no applicable retention. Punitive, Exemplary and Multiple Damages: Coverage provided where permissible by ...
... Crisis Communication Fund: Coverage provided up to $50,000 toward the fees and expenses for the insured's public relations crisis arising out of a computer attack. This coverage is provided with no applicable retention. Punitive, Exemplary and Multiple Damages: Coverage provided where permissible by ...
Cutting Edge VoIP Security Issues Color
... VoIP systems rely heavily on supporting services such as DHCP, DNS, TFTP, etc. DHCP exhaustion is an example, where a hacker uses up all the IP addresses, denying service to VoIP phones DNS cache poisoning involves tricking a DNS server into using a fake DNS response ...
... VoIP systems rely heavily on supporting services such as DHCP, DNS, TFTP, etc. DHCP exhaustion is an example, where a hacker uses up all the IP addresses, denying service to VoIP phones DNS cache poisoning involves tricking a DNS server into using a fake DNS response ...