Appendix C - Windows 2000
... device drivers. One advantage of this approach is that only a single version of each device driver is needed— it can run on all hardware platforms without porting the driver code. HAL also provides the support for symmetric multiprocessing. For performance reasons, I/O drivers (and graphics drivers ...
... device drivers. One advantage of this approach is that only a single version of each device driver is needed— it can run on all hardware platforms without porting the driver code. HAL also provides the support for symmetric multiprocessing. For performance reasons, I/O drivers (and graphics drivers ...
The init process cont. - Workshops
... You can run multiple command line windows (shells) at the same time. To use a GUI you must install the X Windows system and a desktop environment such as Gnome or KDE. ...
... You can run multiple command line windows (shells) at the same time. To use a GUI you must install the X Windows system and a desktop environment such as Gnome or KDE. ...
Operating Systems and File Management 4 Operating System
... To designate a file’s location, you must first specify the device where the file is stored The main hard disk usually is referred to as drive C ...
... To designate a file’s location, you must first specify the device where the file is stored The main hard disk usually is referred to as drive C ...
ch11file_system_implementation
... File system resides on secondary storage (disks) To the operating: large 1-D array of “blocks” ...
... File system resides on secondary storage (disks) To the operating: large 1-D array of “blocks” ...
No Slide Title
... Whenever a process opens a handle to an object, the security reference monitor checks the process’s security token and the object’s access control list to see whether the process has the necessary rights. ...
... Whenever a process opens a handle to an object, the security reference monitor checks the process’s security token and the object’s access control list to see whether the process has the necessary rights. ...
Slides
... likelihood of human error when entering command lines, i.e. typos and missing file names. ...
... likelihood of human error when entering command lines, i.e. typos and missing file names. ...
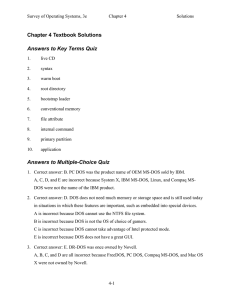
Solution to Lab Project 2.1
... 4. Correct answer: C. Real mode is the only processor mode used by MS-DOS. A is incorrect because there is no Intel processor mode officially named "advanced." B is incorrect because MS-DOS cannot use the Intel processors' protected mode. D is incorrect because MS-DOS cannot use the Intel processors ...
... 4. Correct answer: C. Real mode is the only processor mode used by MS-DOS. A is incorrect because there is no Intel processor mode officially named "advanced." B is incorrect because MS-DOS cannot use the Intel processors' protected mode. D is incorrect because MS-DOS cannot use the Intel processors ...
Windows 2000 System Architecture
... Included to meet US Government requirements Windows 2000 implements POSIX 1003.1 Provides limited set of services • Can’t create threads, windows or use sockets! – Executables linked against POSIX subsystem library (Psxdll.dll) – Commercial Unix-to-Win32 library better approach for porting UNIX appl ...
... Included to meet US Government requirements Windows 2000 implements POSIX 1003.1 Provides limited set of services • Can’t create threads, windows or use sockets! – Executables linked against POSIX subsystem library (Psxdll.dll) – Commercial Unix-to-Win32 library better approach for porting UNIX appl ...
Operating Systems
... O_RDONLY open for reading only, O_WRONLY open for writing only, O_RDWR open for reading and writing Optional constants include: O_APPEND append to the end of file on each write O_CREAT create the file if it doesn’t exist O_EXCL gives an error if O_CREAT is specified and the file exists ...
... O_RDONLY open for reading only, O_WRONLY open for writing only, O_RDWR open for reading and writing Optional constants include: O_APPEND append to the end of file on each write O_CREAT create the file if it doesn’t exist O_EXCL gives an error if O_CREAT is specified and the file exists ...
Chapter 8 - Operating Systems And Utility Programs - Elearning-KL
... Play printers, you can select type of printer you want to install. An on-screen prompt may ask you to insert floppy disk, CD-ROM or DVD-ROM that contains necessary driver files to complete the installation of printer. ...
... Play printers, you can select type of printer you want to install. An on-screen prompt may ask you to insert floppy disk, CD-ROM or DVD-ROM that contains necessary driver files to complete the installation of printer. ...
ch16.ppt
... services to enable Windows to run programs developed for other operating system. Windows 7 uses the Win32 subsystem as the main operating ...
... services to enable Windows to run programs developed for other operating system. Windows 7 uses the Win32 subsystem as the main operating ...
ch16
... services to enable Windows to run programs developed for other operating system. Windows 7 uses the Win32 subsystem as the main operating ...
... services to enable Windows to run programs developed for other operating system. Windows 7 uses the Win32 subsystem as the main operating ...
Chapter 16: Windows 7
... standard can be complied to run on Windows without changing the source code. Applications created for previous versions of Windows run using various virtual machine techniques! Performance —Windows subsystems can communicate with one ...
... standard can be complied to run on Windows without changing the source code. Applications created for previous versions of Windows run using various virtual machine techniques! Performance —Windows subsystems can communicate with one ...
PPT - Defcon
... Problems with HIPS Design • Required to be on the execution path of the attacker to allow/deny actions • Looks just like the hooks rootkits use (dual technology) ...
... Problems with HIPS Design • Required to be on the execution path of the attacker to allow/deny actions • Looks just like the hooks rootkits use (dual technology) ...
Operating System Security (II)
... information describing the file on-disk i-node (file system dependent) • persistent accounting information: user & group ownership, time stamps, etc. • information to locate the disk blocks holding the file’s data in-core i-node (file system independent) • transient management information: acces ...
... information describing the file on-disk i-node (file system dependent) • persistent accounting information: user & group ownership, time stamps, etc. • information to locate the disk blocks holding the file’s data in-core i-node (file system independent) • transient management information: acces ...
[slides] Case study: Windows
... services to enable Windows to run programs developed for other operating system. Windows 7 uses the Win32 subsystem as the main operating ...
... services to enable Windows to run programs developed for other operating system. Windows 7 uses the Win32 subsystem as the main operating ...
The Macintosh File System (continued)
... • OS typically groups disk sectors in some logical way, creates a record of this structure, and builds a directory to track the type of data stored in each file ...
... • OS typically groups disk sectors in some logical way, creates a record of this structure, and builds a directory to track the type of data stored in each file ...
Windows Server 2008
... • When a partition is created, information about that partition is stored in a special area of the disk known as the partition table (in MS-DOS, Mac OS, and Windows) and disk label (in UNIX/Linux) • Another piece of disk that is reserved is known as the boot block in UNIX/Linux and Mac OS X, or the ...
... • When a partition is created, information about that partition is stored in a special area of the disk known as the partition table (in MS-DOS, Mac OS, and Windows) and disk label (in UNIX/Linux) • Another piece of disk that is reserved is known as the boot block in UNIX/Linux and Mac OS X, or the ...
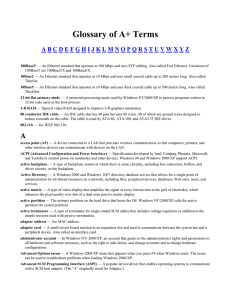
Glossary of A+ Terms
... Briefcase — A system folder in Windows 9x that is used to synchronize files between two computers. broadband — A transmission technique that carries more than one type of transmission on the same medium, such as cable modem or DSL. broadcast — Process by which a message is sent from a single host to ...
... Briefcase — A system folder in Windows 9x that is used to synchronize files between two computers. broadband — A transmission technique that carries more than one type of transmission on the same medium, such as cable modem or DSL. broadcast — Process by which a message is sent from a single host to ...
The Architecture of a Reliable Operating System,
... RS then forks a new process, assigns all needed privileges, and, finally, executes the given path in the child process (not shown in the figure). Information about the new system process is published in the data store (DS), which allows parts of the operating system to subscribe to updates in the sy ...
... RS then forks a new process, assigns all needed privileges, and, finally, executes the given path in the child process (not shown in the figure). Information about the new system process is published in the data store (DS), which allows parts of the operating system to subscribe to updates in the sy ...



![[slides] Case study: Windows](http://s1.studyres.com/store/data/008424774_1-87b89c613bf8233f6d9038041cfe401c-300x300.png)